Conver the following logic diagram into a boolean algebra representation.
Q: Question: What does it mean for a problem to be NP-complete?
A: Correct Answer : Option (a) : The Problem is in NP and every problem in NP can be reduced to this…
Q: To build a highly available distributed system, you must know what kinds of failures can occur. List…
A: Question- distributed computers are connected together by a central computer. Basically here Main…
Q: ogram creates a BitArray of five Byte values (1,2,3,4,5) and displays each byte in its proper bin
A: The idea is to try every permutations. For every positions, there are 2 options, either ‘0’ or ‘1’.…
Q: Question 17 Which of the following initializes a vector with a list initializer: vector integers{1,…
A: The correct way to initialize a vector <int> with a list initializer, will be:- (c)…
Q: Match the structures below with the kinds of languages that they are able to recognize. Not all…
A: In the Theory of computation, lots of languages are available there are various types, and it is…
Q: The CYK algorithm assumes that the given CFG is in CNF. True O False
A: Check next step for the explanation
Q: numbers between 1 to N. NOTE: YOU MAY ASSUME 1 and 2 AR
A: Dear Student, The source code, implementation and expected output of your asked program is given…
Q: Question 6 sm .True or False, BindingContext between two objects can be two-way. In that if either…
A: Various features of the XAML are listed below: Developers can prescribe the user interface by using…
Q: numbers = (38, 42, 15, 22, 46, 61, 88, 89, 64, 48) Partition(numbers, 5, 9) is called. Assume…
A: - We need to give the quick responses based on the function call for partition.
Q: Construct proofs to show that the following arguments are valid
A: Part A: ~P & R (premise)R v L (premise)R → ~M (premise)Assume L (for contradiction)L → ~N…
Q: I need help with this python code : Function PutGraph(integer array(?) dataRows) returns nothing…
A: The PYTHON Code for the algorithm is given in the below step with output screenshot
Q: Cadence1 is an archaeologist who is currently well-known for exploring the deepest crypts and tombs…
A: def getQuadrant(x, y): if x >= 0 and y >= 0: # first quadrant return 1 if x…
Q: Acceptance testing is normally done by O Developer Tester OSQA member Customer Jy
A: Answer: We have explain about Acceptance testing normally done by the which one . for more details…
Q: What are the features of a compiler based PL? Faster run time speed Good for quick prototyping…
A: We have to choose the features of a compiler based PL from the given options.
Q: 7.40 A digital control circuit has three inputs: Start, Stop and Clock, as well as an output signal…
A: Digital control is a branch of control theory that uses digital computers to act as system…
Q: at are the differences between relational and NOSQL data
A: Introduction: As per the bartleby guidelines we can solve only one question for you if you want to…
Q: Based on the function below, assume that the passed input parameter for x=4; What will be the…
A: The output of the given function is given below with explanatory comments.
Q: Consider two different machines with two different instruction sets, both of which have a clock rate…
A: Answer The answer will be an option 1) 50 ms Explanation => Rate = 800 MHz => Time =…
Q: Question 6 The product-of-sums expression for the function !A!B + BC is hint: use Karnaugh map) O…
A: Solution for given question, Boolean algebra laws: A.0=0 A.1=A A.A=A A.A'=0 A+A=A A+A'=1
Q: Explain why the time complexity of searching for an item in a list is not better than searching in a…
A: Dear Student, The answer to your question is given below -
Q: Consider the following relations in a Hotel database. Hotel (HotelNo, HotelName, Address, Capacity)…
A: Here is the explanation regarding the given database:
Q: 4 12 15 - If we have a list of numbers and we want to know what the biggest one is, we use the max…
A: Max algorithm or max function is better.
Q: Table name: DIRECTOR DIR_NUM DIR_LNAME 100 Broadway 101 Hollywoody 102 Goofy Table name: PLAY…
A: The queries for creating the tables and inserting data is given in the below steps along with OUTPUT…
Q: Write a program to find the solution to Maxone problem (You want to maximize the number of ones)…
A: Import the random module. Define the population size and chromosome length. Define the mutation and…
Q: Complete the DTD below so that the XML document would be valid according to the DTD. ]>…
A: The solution is given in the below step with proper explanation
Q: 1- A microservice is a web service that only responds to specific requests and cannot consume any…
A: Introduction SOAP: Data may be sent between apps created using various programming languages using…
Q: Linux systems. Write a script to do the following: Edit the file urname_file1 with the following…
A: Linux file system allows us to operate various operations on files like create, edit, rename,…
Q: Characters Decimal Binary C O d i n
A: Here in this question we have given some English character and we have asked to convert them in…
Q: Insert the following into a red-black tree. I do not need the code. Just a step by step of the…
A: A red-black tree is a self-balancing binary search tree in which each node has an extra bit, which…
Q: Sort the following functions in terms of asymptotic growth from smallest to largest. In particular,…
A: Given the following below function, we need to find their upper bound complexity (9/4)n = O(2.25n)…
Q: Describe the process of specifying a major piece of software: the main documents produced, their…
A: Please find the answer below :
Q: Write a function, called isSymmetric, which returns true if a directed graph is symmetric, false…
A: Dear student, the answer is provided below.
Q: C++,thanks! 10.Write a function to realize the binary search algorithm.
A: The C++ code is given below with output screenshot
Q: Question 24 Some portion of cache system B represented a 2-way set-associative mapping cache system.…
A: Answer 5. Total number of bits in Tag field = 14 bits Total number of bits in set field = 8 bits…
Q: 9. For the one-to-one function f(x) = 3x + 8, find a formula for the inverse function f-1(x).
A: Solution: Given, 9. For the one-to-one function f(x) = 3x + 8 , find a formula for the inverse…
Q: Q.1 For the following declaration, write the codes as asked. The pointer variable first points to…
A: I) Code to delete the node this is to the right of the node pointed to by b: Node *right…
Q: Which is not a component of Digital Forensics? a. Preparation b. Containment c. Eradication d.…
A: As per Bartleby's rules, we can answer only one question at a time As these 2 questions are…
Q: From the graph below, use the Ford-Fulkerson algorithm to determine the maximum flow obtained from…
A: Ford Fulkerson algorithm: Ford Fulkerson algorithm was developed by L. R. Ford and Dr. R. Fulkerson…
Q: Which of the following is NOT an example of instantiating an object. a.Keyboard k; k = new…
A: Please check the step 2 for solution .
Q: In the context of the ensemble methods, explain how you would use the following concepts within the…
A: Max-voting, which is generally used for classification problems, is one of the simplest ways of…
Q: Consider two different machines with two different instruction sets, both of which have a clock rate…
A: the solution is an given below :
Q: Consider three transactions T1, T2, T3 and two data iterns X, Y T1: R (X); R(Y); W (Y) T2: R (X); W…
A: “Since you have posted a question with multiple sub parts, we will provide the solution only to the…
Q: Reorder the following instructions to run faster by reducing pipeline stalls. N = L * M P = Q + N R…
A: To run faster by reducing pipeline stalls, the instructions should be reordered as : N = L * M Y =…
Q: Need the answer step by step with order of the node
A: START Insert the node using BST insertion. Calculate and check the balance factor of each node.…
Q: how many rows does the resultant of the relational algebra expression desc,acqcost (acqcost<1000…
A: Question- Here it will display desc and acqcost from table A that have acqcost less than 1000. So…
Q: Imagine I had a memory with 256 memory cells arranged in a grid 8 columns wide and 32 rows tall.…
A: decoder with an enable input can function as a demultiplexer.Network and returns a promise that is…
Q: 24. What is "kernel-trick" in the context of kernel methods for learning? (a) Mapping input data to…
A: What is the kernel-trick in the context of kernel methods for learning? We have to choose the…
Q: You are requested to create an algorithm analyzer for a sorting program. You are tasked to meet the…
A: As the programming language is not mentioned we are using JAVA The JAVA code is given below with…
Q: Write the language denoted by the following regular expressions:
A: (i) The language denoted by the regular expression (?∗?∗)∗ is the set of all strings that consist of…
Q: What is an SSL tunnel and what does it mean for a “tunnel” to be made between sites such as Render &…
A: proxy opens the connection between the client and the backend service and copies.
Conver the following logic diagram into a boolean algebra representation.
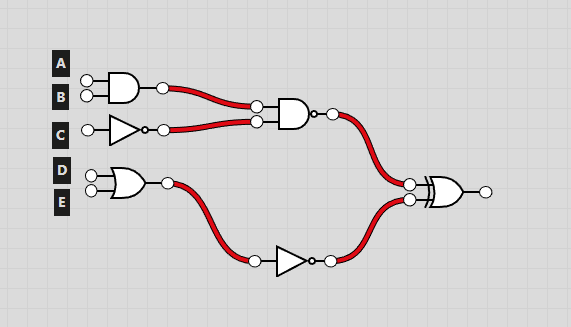
Step by step
Solved in 2 steps with 2 images


