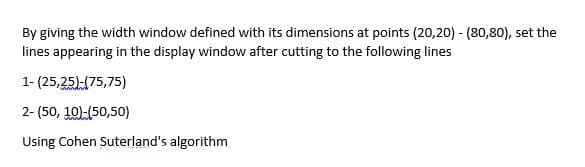
By giving the width window defined with its dimensions at points (20,20) -(80,80), set the lines appearing in the display window after cutting to the following lines
Q: What are the names of the three operations that are considered to be the most basic in the subject…
A: Cryptography Cryptography is a technique for securing digital data. It is a computer science…
Q: When learning academic material that will be kept in semantic memory, what kind of memory processing…
A: The term "storage" refers to the process of retaining data through time. The encoded data is…
Q: Give an introduction of object-oriented analysis by focusing on the role prototypes play in the…
A: Start: Object-oriented analysis will be the topic of our conversation on the provided challenge.
Q: In symmetric encryption, what are the downsides of having a key management system?
A: The solution to the given question is: INTRODUCTION Symmetric encryption uses a single key for…
Q: What is the most essential approach a database designer can utilise to influence database…
A: Introduction: Database design refers to the organisation of data in accordance with a database…
Q: Why should we put in the effort to become proficient in a variety of programming languages? Which…
A: Introduction: The question asks why we need to learn programming languages and which level is…
Q: Design and algorithm that does AND gate with two inputs based on perceptron algorithm.
A: Hey there, I hope you find my solution helpful.
Q: The application development process was improved by the use of debugging. Make a coding standard…
A: Given: Debugging is the act of detecting and removing any problems in software code that might cause…
Q: pop_most_recent_value doesn't work correctly for Make sure pop_most_recent_value() works correctly…
A: We need to write Python code for the given scenario.
Q: Why do we call something that we intend to call "storage" memory instead of storage?
A: The following is a definition of the term "memory," which refers to the structures and processes…
Q: Is it a computer's function? Then describe computer parts
A: let us see the answer:- Introduction:- Taking data, processing it, giving results, and storing it…
Q: What about open source software for word processing or presentations? Email and web browsers…
A: A database management system (DBMS) is software that facilitates the storage, modification,…
Q: Describe the difference. moug $0x8000, % rax movq between i 0x8000, rax
A: We need to answer questions related to given assembly code. *As per the guidelines only 1st question…
Q: What are the advantages of putting in place systems for transaction processing, customer…
A: Beginning: Transaction processing systems are used to balance and govern the purchases of goods and…
Q: What steps are included in the process of computer programming? What considerations need to be made…
A: Introduction: Computer programmers create code that governs how a computer, application, or software…
Q: IT What browsers do you use for school besides canvas, and what are the benefits?
A: The Canvas Learning Management System is an excellent tool that enables students and teachers to…
Q: Identify and provide a high-level overview of the six fundamental transaction processing processes…
A: Required: Identify the six core transaction processing procedures that all transaction processing…
Q: Write a C++ function that returns the sum of elements that are greater than 5 and divisible by 3 of…
A: Function :- int sum(int arr[], int n ) { int sum = 0; // initialize sum // Iterate through all…
Q: Calculate the time of executing the circuit below, where the time of executing each MU MUX= 2…
A: It is defined as a combinational circuit that has maximum of 2n data inputs, ‘n’ selection lines and…
Q: String is an array of characters with null character as the last element of array Select one: O True…
A: The given question is true.String is an array of characters with null character as the last element…
Q: What sets a solid-state drive from from a hard disk drive (HDD) is the lack of moving parts in the…
A: Given: We must define the distinction between a hard disc drive and a solid-state drive based on the…
Q: An overview of some of the more recent developments that have taken place in the field of…
A: The following are recent advancements in the area of nonvolatile solid-state memory: The term…
Q: Which memory would you enhance and why? Semantic, episodic, procedural
A: The answer is given in the below step
Q: What exactly is computer science, and how does it differentiate itself from other areas of study? In…
A: Computer science is the study of computers. Computer science is an area of study that focuses on the…
Q: What are some of the ideas that come to mind when you hear the term "software"? Is there any…
A: Application Software: A computer program that performs a particular personal, educational, or…
Q: How to define the Transaction Processing Cycle (TPS) and offer two business case examples of when…
A: TPS stands for transaction processing system. An information processing system that deals with data…
Q: What are the steps involved in acquiring Application Software? Please provide a detailed description…
A: 1. How much does it cost and what is its worth? Pricing is a crucial factor to consider when…
Q: Jump to level 1 Hash table valsTable is shown below. The hash function is key % 5. Assume items are…
A: A function used to group a value set of N size to some value set of fixed size given that it falls…
Q: What are the four factors that may be used to evaluate the impact of poor data quality in a…
A: Introduction: Data must be of high quality in order to be useful. The higher the quality of your…
Q: The object-oriented design techniques that are implemented should be structured in such a way that…
A: Object-oriented design techniques: The process of designing a computer system or application using…
Q: Watch how individuals behave when they have problems with computers or mobile applications. If a…
A: Problematic piece of software: In general, individuals will respond to troubles with computers and…
Q: Consider the following functions. 5.7 5.8 In which of the following classes is f4 located? (Minimum…
A:
Q: 1. The students' goal of EFL cla to............. O a. progress in the studies b. speak English
A: 1 ANSWER: B (SPEAK ENGLISH) EFL involves studying english in a country where english is not the…
Q: Please design and configure IP address for this office using CIDR (classless inter domain routing)/…
A: The central office is named UWG. It has four branches as mentioned in the diagram Engineering…
Q: When someone says "programming a computer," what precisely do they mean by that phrase? In order to…
A: Start: A programming language is a set of rules for translating text to machine code, or graphical…
Q: Which aspects of computer science have not been sufficiently covered? explain?
A: Machine learning conflicting models I'm interested in anti-grain models, contentious machine…
Q: hand written plz Analyze the decision tree below to answer the following question: Don't Enter $1…
A: According to the information given:- We have to choose the correct option to satisfy the outcome for…
Q: How does the ever-increasing usage of mobile devices, such as smartphones and tablets, which have…
A: Introduction: The rise of the smartphone/small screen: A smartphone's screen is smaller than that of…
Q: 9. To download files between your computer and the server: 10. You can manipulate HTML elements…
A: Note: As per bartleby policy, I can answer only first question in case of multiple questions.
Q: What does it mean to not be "in band" with something? Why is it necessary to do key exchanges…
A: Given: 1) A question is posed in the message on the meaning of the phrase "Out of Band." 2) The…
Q: Develop a State Table with all Inputs and Outputs for a vending machine that sales "Chip", "Water".…
A: State | Coin | Item | Total | Refund -------------------------------------- 0 | | | 0 | 1 | 5 | |…
Q: Why do people use the terms "computer science" and "computer engineering?"
A: The answer is given in the below step
Q: EXERCISE NAME: Using 2D char Array Given the following source code: #include int…
A: Code: #include <stdio.h> int count_digits(char* text); int main(void){char* test[] ={"H3ll0",…
Q: The Internet has affected our society. The Internet offers perks and downsides. What are the…
A: Introduction: One of the most powerful innovations is the Internet, which provides people with…
Q: What's the difference between main and secondary storage in terms of performance and price?
A: Main and Secondary storage: when you save a Word document, the information about the file is…
Q: An examination of wearable computing devices like the Apple Watch and Android Wear, as well as the…
A: Start: Body-worn computersWearable computing and AI refers to computer-powered gadgets that a user…
Q: Question - 3) Using Visual studio demonstrate types of Errors in C#: (Submission Instruction: Take…
A: Here we have given the code to explain the three types of errors with screenshots in step 2.
Q: How do transaction processing, customer relationship management, and supply chain management work?
A: Systems for transaction processing include: The transaction processing system (TPS) is a computer…
Q: Please create a class ArrayUtils in JAVA and write two static methods in it as described below:…
A: Define class ArrayUtils. Define fillarray() method fill the array. Define countMultiples() method to…
Q: The difference between an actual data flow diagram and a conceptual data flow diagram is that the…
A: Given: In the context of data flow diagrams, the phrase "conceptual data flow diagram" refers to a…
Step by step
Solved in 2 steps

- Let W be the rectangular window whose lower left corner is (-3, 1) and upper right corner is at (2, 6). Apply the Cohen-Sutherland clipping algorithm to clip the line segment AB whose endpoints are A (3, 2) and B (-1, 7). Write down all steps.Q3) Use the following rule in mathematical morphology to fill the holes inside the image A to be black. Let the first pixel in the hole is P=Xo.Then, proceed by finding Xk until Xi=X.1. Xc= (X1 @B) N A, K123, Origin Image A Structural element BUsing Incremental Line algorithm, perform the iterations for calculating the pixels for the following points: Initial Point: ( x0, y0 ) = ( 4, 3 ) Final Pont: ( xn, yn ) = ( 13, 11 )
- Start by trying out the moveVertical and slowMoveVertical techniques. Learn how to shift the circle 70 pixels to the left using moveHorizontal.Write an algorithm that outline how to calculate the room area for the image belowGiven the following texture on the left side that mapped onto two tringles on the right as follows: For each of 4 rendered images given below. Give the texture coordinates associated with the vertices of each triangle. Hint: to write the texture coordinates associated with the vertix, you can write for example: V(0,0) with T(0,0), where V represents the vertix and T represents the texture coordinate. Your answer should be like the following example: a) V(0,0) with T(0,0), ..... , .... , ... etc. Follow the same format for b, c, and d
- Computer Science apply sobel horizontal edge detection kernel to the image below using zero padding at edges. The result should be normalized to remove any negative values 9 10 2 10 11 0 8 10 2Question is in the image, Give a detailed explanation for the answerRefer to the image and provide the correct answer with short explanation!
- The attatched image is the 2D profile of an image, showing I(x,y). True or False: The spatial frequency in the x direction (kx) is π; the spatial frequency in the y direction (ky) is π; and the inital phase is π. To create this 2D intensity, we need to add together multiple 2D sine waves. The Fourier transformation of this image will contain a single peak at a single frequency (not counting peaks at zero and the overtones) The wave in the 2D profile is plotted for 3 wavelengthsLet B be a structuring element containing a single point, valued 1, and let A be a set of foreground pixels. a. What do you think would happen if we errode A by B. b. What do you think would happen if we dilate A by B.Take the police-car program and have the car move not side-ways but in a figure 8. For full-credit, Take our Allegro Dev C++ police car code and have the car go in a figure-8 (use the middle point of the 800-by-800 window, namely the point < 400,400 > as the center of the figure-8 (AKA Leminiscate, the radius is 200 pixels, and have the car move in a figure-8 path around the center. The path is a lemniscate (but, if problematic, then approximate a lemniscate).



