By using Dynamic Programming only. How to create a java code to solve the problem?
Q: } What is the output of this function? static void f5 () { HashMap hm = new HashMap (); hm.put("I",…
A: The provided Java function `f5` initializes a `HashMap` and inserts several key-value pairs into it.…
Q: Please explain Python Code def convertup(word): uppercaseword = "" #for c in word: for lc in…
A: 1. Function: convertup(word) 1.1 Initialize an empty string uppercaseword to store the uppercase…
Q: The diagram below shows a 20‐bit virtual address. Identify the bits of the virtual address that…
A: In virtual memory system, it employs paging and a Translation Lookaside Buffer (TLB) to store recent…
Q: 3) A relation is said to be in 3NF if it is in 2NF and no nonprime attribute of R is blank the…
A: Normal form (NF) in databases are the rules that define the structure of relations databases.With…
Q: Convert the following decimal numbers into binary 23310 =
A: The objective of the question is to convert a decimal number into its binary equivalent. In computer…
Q: Discuss the considerations and strategies for handling circular dependencies in data binding…
A: In data binding scenarios circular dependencies occur when multiple entities rely on each other…
Q: Registration
A: Will be using code Lginter!RegistrationFirst Name Last Name Email AddressPassword Confirm Password…
Q: In Assembly code: We have seen that multiplication by a power of two is easy with binary numerals:…
A: This question is related to the assembly code from bitwise operations, multiplication in assembly…
Q: Draw an E-R diagram for Kean University Entity Student • Faculty ● ● ● • Course • 5 attributes for…
A: An Entity-Relationship (ER) diagram is a visual representation of a database's structure,…
Q: The code should print quadruples (x,y,z,w) such that x^2 + y^2 + z^2 = w^2. The outputs given do not…
A: This function, pythagorean_quadruples, uses the properties of Pythagorean quadruples to generate…
Q: Differentiate between context switch and new state of process
A: CPU, Central processing unit performs allocates of resources and process scheduling of tasks. When a…
Q: Build a max heap for below input = [10, 45, 34, 65, 36, 22, 9, 27]
A: SOLUTION -To build a Max heap follow the pseudocode:1Build Max Heap 2procedure buildMaxHeap(arr): 3…
Q: Explore the role of data binding in supporting different data serialization formats.
A: In software development Data Binding is a concept especially when dealing with data serialization…
Q: Booking Booking ID Passenger ID Flight_ID Booking Date 2. In the above entity, what attribute(s)…
A: Relational Database Management System (RDBMS):A Relational Database Management System (RDBMS) is a…
Q: Please help with the following in regards to Nand2Tetris, and hack code, so hack assembly and hack…
A: 1d. A symbol may be:a. @followed by a numberb. @followed by a lower case wordc. @followed by upper…
Q: Which of the following statements best describes a Trojan? options: Malicious software that…
A: Malicious software or code that appears trustworthy but has the ability to take over your computer…
Q: d) How can the research team address potential biases in the collected data, such as biases arising…
A: d) How can the research team address potential biases in the collected data, such as biases arising…
Q: Discuss the use of data binding in optimizing the performance of data-driven web applications.
A: Data binding holds importance in the world of data-driven web applications.It involves establishing…
Q: how do you create a .txt file so that the program will run from it?
A: maginе a hiddеn island, its shorеs lappеd by trеachеrous watеrs and bridgеs promising еscapе. But…
Q: Write a program that asks the user to input a vector of integers of arbitrary length. Then, using a…
A: Take user input of vectorprint the original vectorcreate a modified vector as the same size of the…
Q: Explore emerging trends and advancements in data binding techniques in the current software…
A: Data binding is an aspect of software development that plays a role in keeping the user interface…
Q: 1. You are managing a network for a coffee shop with 3 locations. Your task is to efficiently…
A: An IP network's logical component is called a subnet, short for subnetwork. In computer networking,…
Q: Which of the following is NOT an example of a phishing attempt? An email telling you that your…
A: Phishing, a deceptive practice employed by cybercriminals, often relies on manipulating individuals…
Q: What is the most common authentication mechanism? Magnetic card strip Signature Fingerprint…
A: Authentication mechanisms are crucial in verifying the identity of individuals accessing systems or…
Q: Describe the impact of mobile and social media on the evolution of CRM strategies
A: The evolution of Customer Relationship Management (CRM) strategies has been significantly influenced…
Q: Details of memory translation from virtual to Physical are stored in (choose 1 answer) a) Memory…
A: Details of memory translation from virtual to Physical are stored inki(choose 1 answer)a) Memoryb)…
Q: Write the whole HTML page from the DOCTYPE declaration to the closing HTML tag and code a web form…
A: The task requires creating an HTML web page with a styled registration form that includes fields for…
Q: What are the three basic components in a computer system?
A: A computer system, at its core, is designed to process, store, and retrieve data, and this is…
Q: Explore the role of CRM in managing and optimizing customer interactions across various channels.
A: CRM refers to the management of customer relationships. Businesses employ this technology-driven…
Q: Explore the role of data binding in the context of functional programming languages.
A: Data binding holds importance in the realm of programming. In programming languages data binding…
Q: Given string strinput, output "Valid length" if the string's length is greater than or equal to 5.…
A: Prompt usеr for string: print("Entеr a string:")2. Rеad usеr input: usеrInput = scan.nеxtLinе()3.…
Q: Java Program ASAP I want only one program. Please pay attention to the screenshot for test case 2…
A: In this question we have to fix the java code based on the output file provided.Let's understand and…
Q: For this assignment, you will use Jupyter Notebook software on your XenDesktop or home computer to…
A: Step-1: StartStep-2: Define function add(x, y) Step-2.1: Return x + yStep-3: Define function…
Q: Consider the traveling salesman problem where he needs to pass through 7 cities. We will use a…
A: Genetic algorithm : It is a method for solving both constrained and unconstrained optimization…
Q: Explain thrashing
A: When we talk about memory in computing, we're talking about the electronic parts that hold…
Q: Create a C ++ program that manages a list of cars. The list of cars is stored in a file named…
A: Cars.txt:-#include <iostream>#include <fstream>#include <list>#include…
Q: Consider the following graph Among the following sequences: (1) abeghf (II) abfehg (III) a bfhge…
A: Graph is a non linear data structure which contains nodes and edges. The nodes are connected each…
Q: What should my code be to get the size of my six clusters Here is my code so far # Install…
A: The objective of the question is to determine the size of the six clusters that have been created…
Q: would you have any idea for a python code that includes : File I/O, Regular Expressions, Object…
A: This is an illustration of Python code that uses the Tkinter GUI, Regular Expressions, File I/O, and…
Q: e. Filter the vehicles that have mpg greater than 40 (inclusive) and acceleration greater than 11…
A: NOTE: Since programming langauge is not mentioned. Therefore answering question in Python…
Q: Define different types of memory access methods with examples.
A: Memory access refers to the process by which a computer system retrieves or stores data in its…
Q: Processor Clock Rate Processor 1 2.5 GHz Processor 2 3.3 GHz Processor 3 2.4 GHz CPI 1.4 2.3 1.9 If…
A: Clock rate is measured in Hz and represents the speed of instruction execution through a…
Q: What are the API types and their advantages and disadvantages?
A: APIs (Application Programming Interfaces) come in various forms, and each has its advantages and…
Q: What is fragmentation in a file system? The process of defragmenting a hard disk drive The process…
A: In the realm of computer storage, the concept of fragmentation plays a pivotal role in…
Q: Prove the time complexity of the Binary search algorithm using Masters theorem, identify all the…
A: Binary Search is a fundamental algorithm in computer science, renowned for its efficiency in finding…
Q: Problem 3. (a) Consider the following two PN sequence generators of length L = 5. Starting from the…
A: A pseudorandom noise (PN) generator can be defined in such a way that it is a device or algorithm…
Q: Explain the concept of virtualization in data binding and its impact on resource optimization.
A: Virtualization in data binding improves software development resource efficiency. Data binding links…
Q: Describe the advantages of using data binding in user interface development.
A: Data binding is a crucial concept in user interface (UI) development that revolutionizes the way…
Q: Insert the following keys into AVL tree: 50,20,60,10,8,15,32,46,11,48 Hint: you must preserve the…
A: AVL Tree It is a type of binary search treeIt is named after its inventors Adelson-Velsky and…
Q: can you Perform the flowchart algorithm and pseudocode for the following: Create a one- dimensional…
A: In this question we have to understand about the given requirement and designa flowchart with the…
By using Dynamic
Step by step
Solved in 3 steps with 2 images

- Consider some input string s and some index i. The longestsubstring s[i], ... , s[j − 1] that is a valid expression consists of some number of termsadded together. In all of these cases, it begins with a term. By magic, assume that theGetTerm routine already works. Calling GetTerm(s, i) will return pterm and jterm, wherepterm is the parsing of this first term and jterm indexes the token immediately after thisterm. Specifically, if the expression has another term then jterm indexes the ‘+’ thatis between these terms. Hence, we can determine whether there is another term bychecking s[jterm]. If s[jterm] = ‘+,’ then GetExp will call GetTerm again to get the nextterm. If s[jterm] is not a ‘+’ but some other character, then GetExp is finished readingin all the terms. GetExp then constructs the parsing consisting of all of these termsadded together.Let A be the set of all strings of decimal digits of length 5. For example 24157 and05189 are strings in A.(a) How many strings in A have exactly one 7?(b) How many strings in A have at least two 2’s?(c) How many strings in A have the digits in a strictly decreasing order? For example97643 and 54321 are such strings, but 14820 and 95421 are not.Given a string S, find the longest palindromic substring in S. Substring of string S: S[ i . . . . j ] where 0 ≤ i ≤ j < len(S). Palindrome string: A string which reads the same backwards. More formally, S is palindrome if reverse(S) = S. Incase of conflict, return the substring which occurs first ( with the least starting index). Example 1: Input: S = "aaaabbaa" Output: aabbaa Explanation: The longest Palindromic substring is "aabbaa".
- Let s = σ1. . . σk be a binary string of length k > 0. We say that a binary string w = w1 . . . wn contains s as a subsequence if there are k indices 1 ≤ i1 < i2, . . . < ik ≤ n such that wik = sr for every 1 ≤ r ≤ k. For example, if s = 11 then 10001, 1010 and 110 contain s as a subsequence whereas 000 and 1000 do not. Prove that the language of all binary strings containing a fixed binary string s of length k as a subsequence is a regular language.A string S consisting of uppercase English letters is given. In one move we can delete seven letters from S, forming the word "BALLOON" (one 'B' one A, two 'L's, two 'O's and one 'N'), and leave a shorter word in S. If the remaining letters in the shortened S are sufficient to allow another instance of the word "BALLOON" to be removed, next move can be done. What is the maximum number of such moves that we can apply using pythonWe consider certain strings of length 6 over the alphabet S = {A,B,C}. We require that the string contains exactly two As, and exactly two B's, and exactly two C's. How many such strings are there? That is, how many strings of length 6 over the alphabet {A,B,C} contains exactly two A's, two B's and two C's?
- Given two strings A and B, find the minimum number of times A has to be repeated such that B is a substring of it. If no such solution, return -1.For example, with A = "abcd" and B = "cdabcdab".Return 3, because by repeating A three times (“abcdabcdabcd”), B is a substring of it; and B is not a substring of A repeated two times ("abcdabcd").Note:The length of A and B will be between 1 and 10000.Reference: https://leetcode.com/problems/repeated-string-match/description/"""def repeat_string(A, B): count = 1 tmp = A max_count = (len(B) / len(A)) + 1 while not(B in tmp): tmp = tmp + A if (count > max_count): count = -1 break.Show L = { w | w is an element of {0, 1, 2}* and (the number of 0s in w ≥ the number of 1s in w) and ((the number of 0s + the number of 1s in w) divides the number of 2s in w) } is not context free. You should assume that p is the pumping length and for any string s in L with |s| ≥ p, s can be broken into 5 pieces, s = uvxyz.Modulo arithmeticFor two integers ‘a’ and ‘b’ and a positive integer ‘n’, let + represent the operation a + b = (a+b)mod(n), that is, the result of a + b is the remainder of the usual sum a + b after dividing by n (using a natural representation). Similarly, let * represent the operation a * b = (a*b)mod(n), that is, the result of a * b is the remainder of the product a*b after dividing by n. For example using the set S = {2, 5, 8} and n = 9, 5 + 8 = 4, since 4 is the remainder after dividing 13 (5 + 8) by 9; and 2 * 8 = 7, since 7 is the remainder after dividing 16 (2*8) by 9.a. For each set S and number n specified below, create two “operation” tables (these are called Cayley tables), one showing the results for the operation +, and one showing the results of the operation * for each pair of elements from S (see the example tables in the notes).i. S1 = {0, 1} and n = 2ii. S2 = {1, 2} and n = 3iii. S3 = {0, 2, 4, 6} and n = 8iv. S4 = {1, 3, 5, 7} and n = 8v. S5 = {1, 2, 3, 4} and n =…
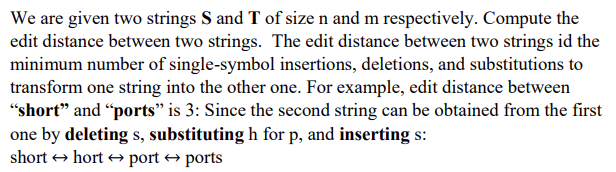
- Let Σn denote the set of all binary strings with lengths less than n. For example, Σ2 = {λ, 0, 1} and Σ3 = {λ, 0, 1, 00, 01, 10, 11} where λ is the empty string, i.e. the string of length 0. For x ∈ Σ we denote the length of x by |x|. a) How many functions f : Σn → Σn are there? b) How many one-to-one functions f : Σn → Σn are there?Let K be the total calculated in step 4.a.i, and let LSUBS be the set of all subsets of n strings taken from L, 2 ≤ n < m. Continuing the example above for n = 2, LSUBS might be enumerated in the format { {AAAAA, AAAAC}, {AAAAA, AAAAG}, … {TTTTG, TTTTT} }. What is |LSUBS|, the cardinality of the set of subsets, as a function of K?If |S| denotes the length of string S, show that the edit distance between s1 and s2 is never more than max{|s1|, |s2|}

