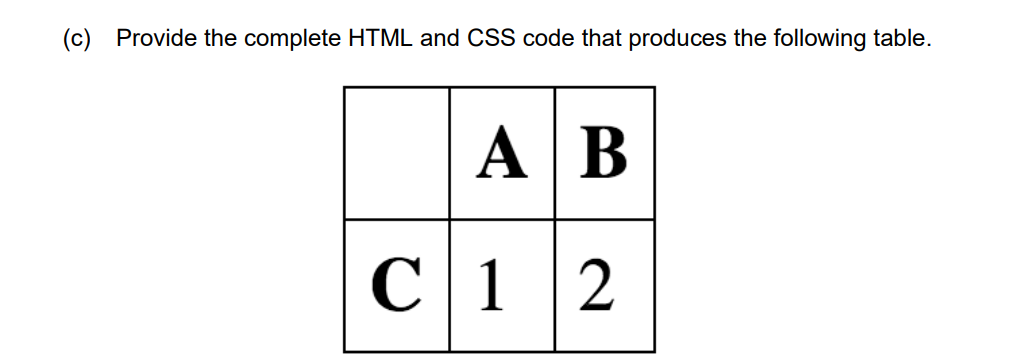
(c) Provide the complete HTML and CSS code that produces the following table. A B C12
Q: Computer Science Information about the handling of processes and threads in the operating system "VM…
A: Intro Computer Science Process and thread handling information from the operating system "VM / CMS".
Q: how ofted do you have to microblog ...once ot twice a day or once or twice a week?
A: Microblogging can be denoted as a certain type of blogging which provides information in a brief…
Q: What are some of the ways that SSH may be put to use? Create a list of acronyms associated with SSH…
A: Answer: The acronym SSH refers to the secure shell protocol, which is used for communication across…
Q: 10) Functions in high-level languages often declare local variables just below the return address on…
A: According to the information given:- We have to write a function in high level language on the basis…
Q: In what ways does a distributed database work? Do you know what a DDBMS stands for?
A: Given: A distributed database management system (DDBMS) is a centralized software system that…
Q: Where can I get a list of general and common duplicated data criteria?
A: The Correct Response Is: For duplicated data, two broad and common requirements must be met.…
Q: Share what you've learned about the ARP protocol with a friend. Please specify the operating layer…
A: The Address Resolution Technique (ARP) is a technique or method used in a local-area network to…
Q: Please identify the three methods for recording WORM discs.
A: Introduction: There are three options for recording WORM discs available to users:
Q: Compare the performance of a 32-bit and 64-bit computer when the same resources, such as RAM and…
A: Intro We need to compare the performance of a 32-bit and 64-bit computer when the size is same
Q: The answer to this inquiry is "How does Apache Spark carry out lazy transformations on RDDs?"
A: Introduction: Apache Spark is a high-performance unified analytics engine for big data and machine…
Q: Topics Covered: Double-subscripted Array Objectives: To understand the concept and use of…
A: Pascal triangle: The coefficients in the expansion of any binomial expression, such as (x + y)n, are…
Q: Language-defined assertions offer what advantages over ifthen constructs?
A: Solution: When the condition is untrue, an if statement does not throw an exception. When the…
Q: Explain the concept of a challenge–response authentication system. What makes it more safe than a…
A: A challenge-response authentication system is a group of protocols that is used to: present…
Q: What is information management function? Which software performs this function in computer?
A: I will explain both answers in details,
Q: What are the benefits of learning a variety of programming languages? This programming language has…
A: Programming languages: Programming languages boost pupils' logical thinking and problem-solving…
Q: How important is it to be familiar with the many programming paradigms that a language supports? To…
A: Introduction If you are interested in developing code in a particular programming language, it is…
Q: Explain why, in the first place, a web server should be considered an end system.
A: Intro Outline two or three unquestionable sorts of end frameworks. All through this substance, the…
Q: Q4 write a program that accepts a day, month and year then calculate the day of year corresponding…
A: Given requirement, Write a program that accepts a day, month and year then calculate the day of the…
Q: Is the security architecture of Open Systems Interconnection (OSI) equipped with cutting-edge…
A: Non-repudiation: When neither the sender nor the recipient of a communication may refute the…
Q: Note: 1- you do not need (and should not) to import any additional package/class. 2- We do not need…
A: Input n and m from the user. Iterate the loop from 1 to m. Determine whether number is divisible by…
Q: In DHCP. How does a client machine seeking an IP address determine whether or not a DHCP offer…
A: Introduction: After receiving the DHCP Offer message, the client is aware that there is a DHCP…
Q: Describe briefly five techniques for lowering the risk of an information security compromise.
A: Intro Launch: Risk Control Strategies are used by IT and Info Sec departments to limit…
Q: What would the components of a business case for moving to the cloud look like?
A: Inspection: When we develop a business case, we are ultimately driving a representation of ROE.…
Q: Share information about the ARP protocol with a coworker. Include information about the layer it…
A: Inspection: Tell a coworker about the ARP protocol. Mention the layer it works at, as well as the…
Q: Is there a possibility of a security breach occurring inside cloud computing platforms with regard…
A: The above question is solved in step 2 :-
Q: The study of computers
A: The answer to the following questions:-
Q: Is there a significant difference in the degree of unreliability between IP and UDP? Is there a…
A: Given: Both UDP and IP provide unstable service to their users. The acronym UDP stands for User…
Q: Exists a difference between traditional on-premises data centers and cloud settings with regard to…
A: Introduction: There is, indeed, a distinction between traditional on-premises data centres and…
Q: Give some instances of how two-tier and three-tier application architectures differ and how they are…
A: Introduction: The end-user and the organisation both stand to gain from the use of a web…
Q: Describe how a challenge–response system is used to verify someone. In what respects is it more safe…
A: The above question is solved in step 2 :-
Q: Conduct research about the advantages and disadvantages of using cloud computing services. What are…
A: Start: Recent years have seen a rise in cloud-based information technology infrastructure adoption…
Q: ble for an application to receive a reliable data transmission while it is simultaneously operating…
A: Introduction: UDP is more appealing in applications like as streaming and VOIP, which can tolerate…
Q: What are the most important considerations when choosing a portable computer? What are the…
A: Intro Consider the following factors: When purchasing a mobile computer, the following elements…
Q: When it comes to cloud security, what exactly do you mean when you refer to the shared…
A: Launch: A shared responsibility paradigm is a cloud security perspective that establishes the…
Q: Is there a common methodology for presenting business cases that include moving to the cloud?
A: According to the information given:- We have to define the common methodology for presenting…
Q: What is the size of the following array? (Don't add an empty space before and after your answer) int…
A: Question- An Array can hold any value of same data type. Index of an Array Starts from 0 Given…
Q: why it could be preferable for an application developer to execute the program using the UDP…
A: Task: Advantages of UDP protocol over TCP for application developer.
Q: In what ways does a distributed database work? Do you know what a DDBMS stands for?
A: DDBMS is widely used in data warehousing, where huge volumes of data are processed and accessed by…
Q: In the following instruction sequence, show the resulting value of AL where indicated, in binary:…
A: The Answer is
Q: Justify why authentication is an issue in today's cyber society
A: According to the information given:- We have to justify authentication is an issue in today's cyber…
Q: What would the components of a business case for moving to the cloud look like?
A: Considering: What's a cloud migration business case? second Business cases are driven by ROE. This…
Q: What is the value in count if input sel=10 after the third rising edge of clock based on the…
A: I will explain it in details,
Q: Task 5: Use the EXISTS operator to find the ID, first name, and last name of each customer for which…
A: Introduction Task 5: Use the EXISTS operator to find the ID, first name, and last name of each…
Q: Please explain the significance of the "Work Breakdown Structure" in your response. Do you have to…
A: Work Breakdown Structure (WBS) is a sequence of tasks required to complete a project. WBS “breaks…
Q: What are three applications of computers and information systems that you use in your day-to-day…
A: Introduction: A computer information system is a network of people and computers that cycles or…
Q: Why is it necessary to learn about the interactive system development framework ?
A: Introduction: When designing a website, we need to make sure that we use a high-quality interactive…
Q: Wireless networks have less bandwidth than traditional networks.
A: The above question is solved in step 2 :-
Q: ential search algorithm and the binary search algorithm have their own set of benefits, but what are…
A: Introduction: Performing a search in a certain sequence. The existence of a sorted list is not…
Q: Was the algorithm used to erase files affecting the performance of the Symbian, Android, and iPhone…
A: Introduction: The algorithm impacted Symbian, Android, and iPhone. Android was affected by Detection…
Q: How vulnerable are cloud-based security solutions to data breaches? Is there anything that can be…
A: Answer: Is it conceivable that a data breach will have a substantial impact on cloud security? Is…
Step by step
Solved in 3 steps with 1 images

- Python -- Find some websites that give RSS feeds, noting that some use the XML given in the ATOM specification. Then choose one and use urllib.request to get the document. Use ElementTree to parse the document and choose some tags to obtain. You can do something simple like get the title tags. Please submit your code and your output, but please print only a small amount, for example the first 10 tags. Or you may choose to find some other content from the xml document. Once you have submitted your code and results, look at those of two or three of your fellow classmates to see what they didcreate this using anchor tag in htmlSegmentation errors and page design flaws are cited. Give a quick summary of the main differences between a segmentation fault and a page fault.

