(c) Using the smallest data size possible, either a byte (8 bits), a halfword (16 bits), or a word (32 bits), convert the following values into two's complement representations: (11) -128 (iv) -129
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: Introduction: Apex is one of the programming languages which is utilized to make the salesforce…
Q: #function read file and display report def displayAverage(fileName): #open the file infile =…
A: I have provided PYTHON CODE, CODE SCREENSHOT , TXT FILE SCREENSHOT and OUTPUT…
Q: Please do it with regular expression. Don't use loops please. Do fast, I have no time left Write a…
A: Required:- Please do it with regular expression. Don't use loops, please. Do fast, I have no time…
Q: Do fast, I have no time left Write a java program to check if a string contains the vowels or not
A: import java.util.Scanner;import java.util.regex.Matcher;import java.util.regex.Pattern;public class…
Q: Give some details of how you might augment the sliding window protocol with flow control by having…
A: We assume ACKs carry an additional variable k, which indicates the available buffer space of the…
Q: . Suppose A is connected to B via an intermediate router R, as in the previous problem. The A-R link…
A: Consider the situation wherein there are two computers, A and B as shown below, with a router R in…
Q: Do it in intelij IDE other wise will give down vote Write python program to give whether a number…
A: Here I have created a function named checkIsPrime(). Inside the function, I have used a conditional…
Q: > Let L = {a"b":n>0} a. Show that L² is a context-free language. b. Show that L' is a context-free…
A: Context free language is the language that is generated by the context free grammar or according to…
Q: What security flaws are exploited and how may these issues be addressed in the future in the case of…
A: Introduction: Information or gear damage that was accidental yet at the same time happens is alluded…
Q: and a bandwidth of 12000 KHz. What is the
A: The answer is
Q: have learned from the class "history of computing.
A: The history of computing is longer than the history of computing hardware and modern computing…
Q: I am having an error in the following java method. pipeline <- javaMethod('createCoreNLP',…
A: Sys.setenv(JAVA_HOME='C:\\Program Files\\Java\\jdk-18.0.1.1')library(rJava) library(coreNLP)options(…
Q: Construct a Binary tree using following information Inorder sequence - 1,2,3,4,5,6,7,8 Pre-order…
A: The tree in which every parent node has at most two child nodes is known as a Binary tree.
Q: In C program, Implement intArray_remove( intArray_t* ia, unsigned int indexToBeRemoved ) and…
A: The answer is given below.
Q: I need help in this C program. Assume a list of integers stored in a text file named…
A: ALGORITHM:- 1. Declare a file and insert the integer elements in it. 2. Read the integers from the…
Q: You are hired to design a reliable byte-stream protocol that uses a sliding window (like TCP). This…
A: Given, Bandwidth = 1 Gbps = 109 bps = (109 /8) bytes per second Round Trip Time = RTT= 100ms = 0.1…
Q: 1. Consider the network shown in Figure 4.28, in which horizontal lines represent transit providers…
A: Below is the answer to above question. I hope this will be helpful for you..
Q: One of the benefits of a honey pot is that it affords a person the opportunity to commit crimes…
A: The above question is solved in step 2 :-
Q: What form of Denial of Service attack is well known for spoofing the source and destination address…
A:
Q: I need help in this question in C program. Assume the following declarations: struct EmployeeTag {…
A: The question is to write C code for the given problem.
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: The Salesforce Backend was built using the programming language Apex, and most of the functionality…
Q: Path MTU is the smallest MTU of any link on the current path (route) between two hosts. Assume we…
A: The term MTU also called as Maximum Transmission Unit defines the greatest size of a packet which…
Q: (i) A sequence diagram can describe the architecture elements of a software application. (ii) Both…
A:
Q: . Suppose A is connected to B via an intermediate router R, as in the previous problem. The A-R link…
A:
Q: Given a code snippet in C++, write the equivalent codes in MIPS. Note: You may use any register that…
A: Snippet1.asm main: push rbp mov rbp, rsp mov DWORD PTR [rbp-4], 3 mov DWORD PTR [rbp-8], 5 mov DWORD…
Q: A conveyor system is a mechanical handling equipment that moves materials from one location to…
A: Please refer below for your reference
Q: C CODE: ------------------------ int i, n, j; printf( "Feed Me:" ); scanf( "%d", &n ); for (i=1;…
A: Answer is given below.
Q: stakeholder register for a Greek restaurant
A: Stakeholder Register Stakeholder Type Level of interaction Importance Vendor Primary Recurring…
Q: until now, we have not puts should follow a p fines and calls a text va
A: Solution: text_validator.py def text_validator(): """ function to validate full name """…
Q: BitDefender Antivirus provides real time protection against all viruses and ransomware. It also…
A: The above question is solved in step 2 :-
Q: c-2. Figure below shows a code written in C to run on a Linux-based operating system. (a) What are…
A: steps needed to compile and run this code.
Q: Your task is to create a program that could be used to calculate the cost of purchasing several…
A: Program Plan: Create a class ShoppingCart as follows: Initialize variables to store TAX, index, and…
Q: Internal control being one of the major determinants of an organization’s success requires the…
A: advantages and five disadvantages/limitations of internal controls.
Q: An online warehouse provides features for their customers to browse and search products and to place…
A: Solution:: Package diagram, a kind of (related to what holds something together and makes it…
Q: Give some details of how you might augment the sliding window protocol with flow control by having…
A:
Q: When closin timeout not CLOSED?
A: Answer is given below.
Q: . Let A and B be two stations attempting to transmit on an Ethernet. Each has a steady queue of…
A: Ethernet:- Ethernet is a method to interconnect multiple computers in a small area, this is one of…
Q: Encrypt your memory stick using BitLocker. Save the newly generated recovery key on your Desktop.…
A: Below is the complete steps with explanation in detail for the given question regarding encrypting…
Q: X435: Generics - Comparable Cage Modify the Cage class to implement Comparable. The definition of…
A: Java Comparable interface is used to order the objects of the user-defined class. The interface is…
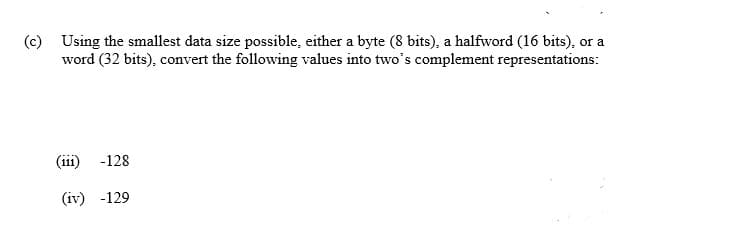
Q: (c) Using the smallest data size possible, either a byte (8 bits), a halfword (16 bits), or a word…
A:
Q: Write a program that converts distances measured in kilometers to miles.One kilometer is…
A: Kilometers must be entered by the user. The kilometres variable holds this value. Since 1 kilometre…
Q: Suppose that we run the sliding window algorithm with SWS = 5 and RWS = 3, and no out-of-order…
A: The question is related to sliding window protocol.
Q: Write a program that will read the contents of "integers.dat". The output of the program is the…
A: Program Plan : 1.Declare header files. 2. Declare the variables to store the values .…
Q: An online warehouse provides features for their customers to browse and search products and to place…
A: Solution:: Package diagram, a kind of (related to what holds something together and makes it…
Q: Considering the local banks here in the Philippines. Identify what are the data mining task that can…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Arrangement,…
Q: . Suppose a 10-Mbps Ethernet hub (repeater) is replaced by a 10-Mbps switch, in an environment where…
A: Ethernet hubs are multiport repeaters that help expand the physical medium and give network devices…
Q: When it comes to cloud security, what is the "shared responsibility" paradigm like?
A: Shared Responsibility for cloud security is discussed below
Q: 1. Write a JavaScript statement to accomplish each of the following tasks: a) Declare variables…
A: JavaScript:- Java Script can be both server side and client side. Client-side javascript is the…
Q: I need help in this C program. Assume two lists of integers both in ascending order. The first list…
A: The C program is given below with code and output screenshots Happy Coding ?
Q: In C program. implement list_find( list_t* list, int targetElement ) function /* * dataStructure.h *…
A: The answer is given below.
Step by step
Solved in 3 steps

- Computer Science Draw Table X based on the logical and physical memory including valid invalid bit based on the above Figure 1.0.3. a Design a (7, 4) CRC code word for the data bits 1011 assuming the generatorpolynomial of 1011. b. Calculate the syndrome for the received code word 1000110 using the generatorpolynomial 1011.Assume that an 8-bit data word stored in memory is 11101010. Using the Hamming algorithm, determine what check bits would be stored in memory with the data word. Consider if data bit 4 sustains an error and calculate syndrome word.
- Assignment for Computer Architecture! this is about hamming codes write the code IN MIPS ASSEMBLY LANGUAGE calculating hamming codes; The key to the Hamming Code is the use of extra parity bits to allow the identification of a single error. Create the code word as follows: Mark all bit positions that are powers of two as parity bits. (positions 1, 2, 4, 8, 16, 32, 64, etc.) All other bit positions are for the data to be encoded. (positions 3, 5, 6, 7, 9, 10, 11, 12, 13, 14, 15, 17, etc.) Each parity bit calculates the parity for some of the bits in the code word. The position of the parity bit determines the sequence of bits that it alternately checks and skips.Position 1: check 1 bit, skip 1 bit, check 1 bit, skip 1 bit, etc. (1,3,5,7,9,11,13,15,...)Position 2: check 2 bits, skip 2 bits, check 2 bits, skip 2 bits, etc. (2,3,6,7,10,11,14,15,...)Position 4: check 4 bits, skip 4 bits, check 4 bits, skip 4 bits, etc. (4,5,6,7,12,13,14,15,20,21,22,23,...)Position 8: check 8 bits,…Select the correct condition for block size in RSA. a. Must be Greater than log2 ( n ) + 1 b. Must be Greater than or equal to log2 ( n ) + 1 c. Must be Less than or equal to log 2( n ) +1 d. Must be Less than log2 ( n ) +1a) Consider the (7,4) hamming code with data word 1111 and evaluate the 7-bt composite code word (use even parity). b) Assume the stored composite code from memory is 1010001. Evaluate the parity bits of the stored code, find the bit position in error, and correct it if it is correctable (use even parity).
- Please please don't copy Computer Science for BCH (16,12). when input is (0, 4, 14, 14, 4, 4, 15, 2, 4, 2, 15, 13), what are the check digits?Work on the following questions: 1. Convert the following decimal numbers into binary (show the steps): i) 75, ii) 64, iii) 1023Show Steps Please 21. Suppose we want an error-correcting code that will allow all single-bit errors to be corrected for memory words of length 10. a) How many parity bits are necessary? b) Assuming we are using the Hamming algorithm presented in this chapter to design our error-correcting code, find the code word to represent the 10-bit information word: 1001100110. 22. Using the CRC polynomial 1101, compute the CRC code word for the information word, 01001101. Check the division performed at the receiver.
- 32) Let a = 1.0 × 29, b = − 1.0 × 29 and c = 1.0 × 21. Using the floating-point model described in the text (the representation uses a 14-bit format, 5 bits for the exponent with a bias of 15, a normalized mantissa of 8 bits, and a single sign bit for the number), perform the following calculations, paying close attention to the order of operations. What can you say about the algebraic properties of floating-point arithmetic in our finite model? Do you think this algebraic anomaly holds under multiplication as well as addition? b + (a + c) = (b + a) + c = Show Steps PleasePLEASE USE MATLAB (Linear Block Code) Design a (5, 1) code that can correct 2 error bits in each codeword.a. Please write down the generator matrix G, the standard table, and thesyndrome look-up table.b. Please also use an example received word with 2 error bits to demonstrate thedecoding procedureKindly answer the following questions. b. Verify. that the 6-3-1-1 code is a weighted code. Note that for some decimal digits, two different code combinations could have been used. For example, either 0101 or 0110 could represent 4. In each case the combination with the smaller binary value has been used.

