c. The set of all strings consisting of one or more as. d. The set of all strings consisting of one or more digits. (Each digit is one of the characters 0 through 9.) e. The set of all strings consisting of zero or more as one. with ice. a semicolon after each
c. The set of all strings consisting of one or more as. d. The set of all strings consisting of one or more digits. (Each digit is one of the characters 0 through 9.) e. The set of all strings consisting of zero or more as one. with ice. a semicolon after each
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter4: Selection Structures
Section4.3: Nested If Statements
Problem 7E
Related questions
Question
Give a BNF and an EBNF grammar for each of the languages:
Please do parts c,d,e
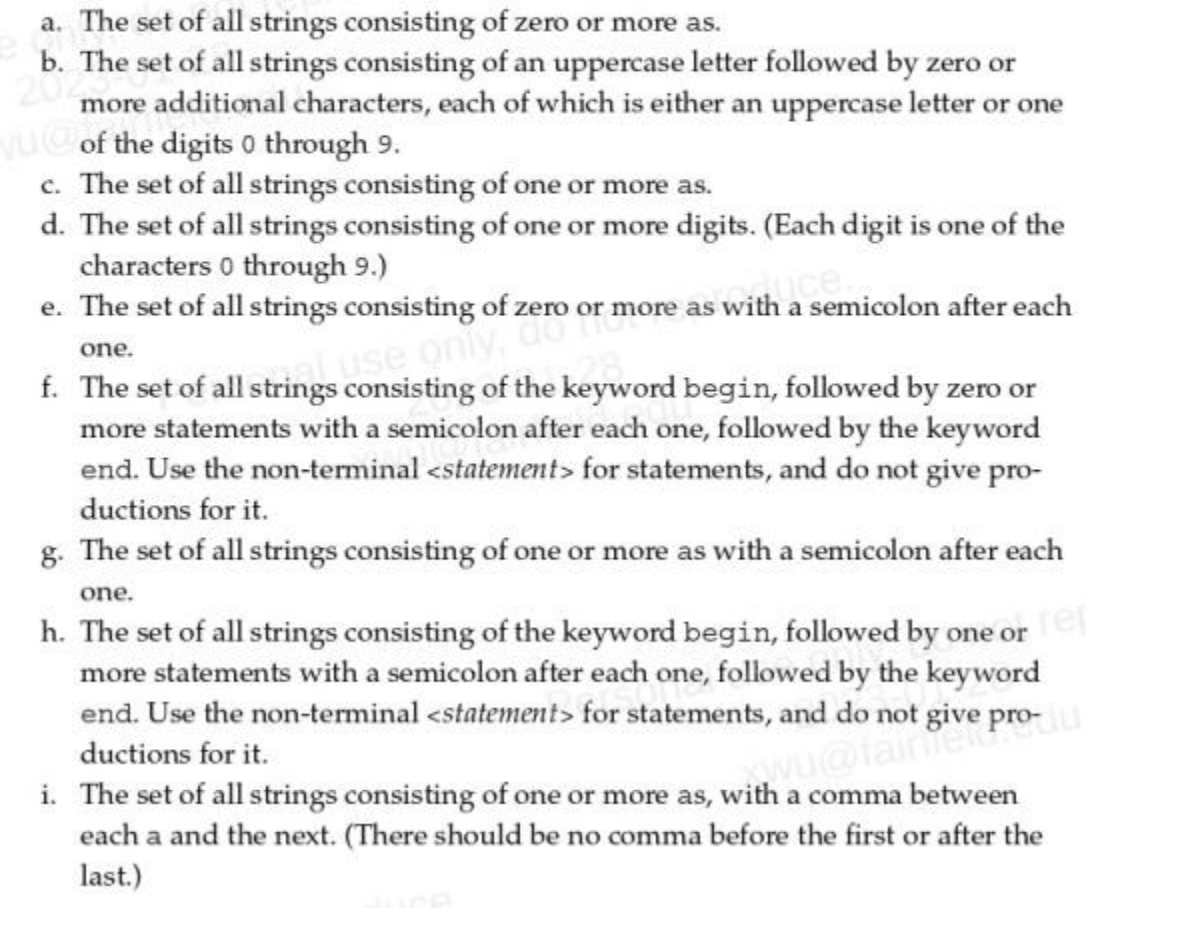
Transcribed Image Text:a. The set of all strings consisting of zero or more as.
b. The set of all strings consisting of an uppercase letter followed by zero or
more additional characters, each of which is either an uppercase letter or one
of the digits 0 through 9.
c. The set of all strings consisting of one or more as.
d. The set of all strings consisting of one or more digits. (Each digit is one of the
characters 0 through 9.)
e. The set of all strings consisting of zero or more as with a semicolon after each
one.
f.
use only
The set of all strings consisting of the keyword begin, followed by zero or
more statements with a semicolon after each one, followed by the keyword
end. Use the non-terminal <statement> for statements, and do not give pro-
ductions for it.
g. The set of all strings consisting of one or more as with a semicolon after each
one.
h. The set of all strings consisting of the keyword begin, followed by one or ref
more statements with a semicolon after each one, followed by the keyword
end. Use the non-terminal <statement> for statements, and do not give pro-
ductions for it.
wu@fainiert
i. The set of all strings consisting of one or more as, with a comma between
each a and the next. (There should be no comma before the first or after the
last.)
Expert Solution
Overview
In this question we have to provide a BNF and a EBNF Grammar for the langauge given
C. The set of all strings consisting of one or more as.
D. The set of all strings consisting of one or more digits. (Each digit is one of the characters 0 through 9.)
E. The set of all strings consisting of zero or more as with a semicolon after each one.
Let's answer, hope this helps you if you have queries on the solution, utilize threaded question feature.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning