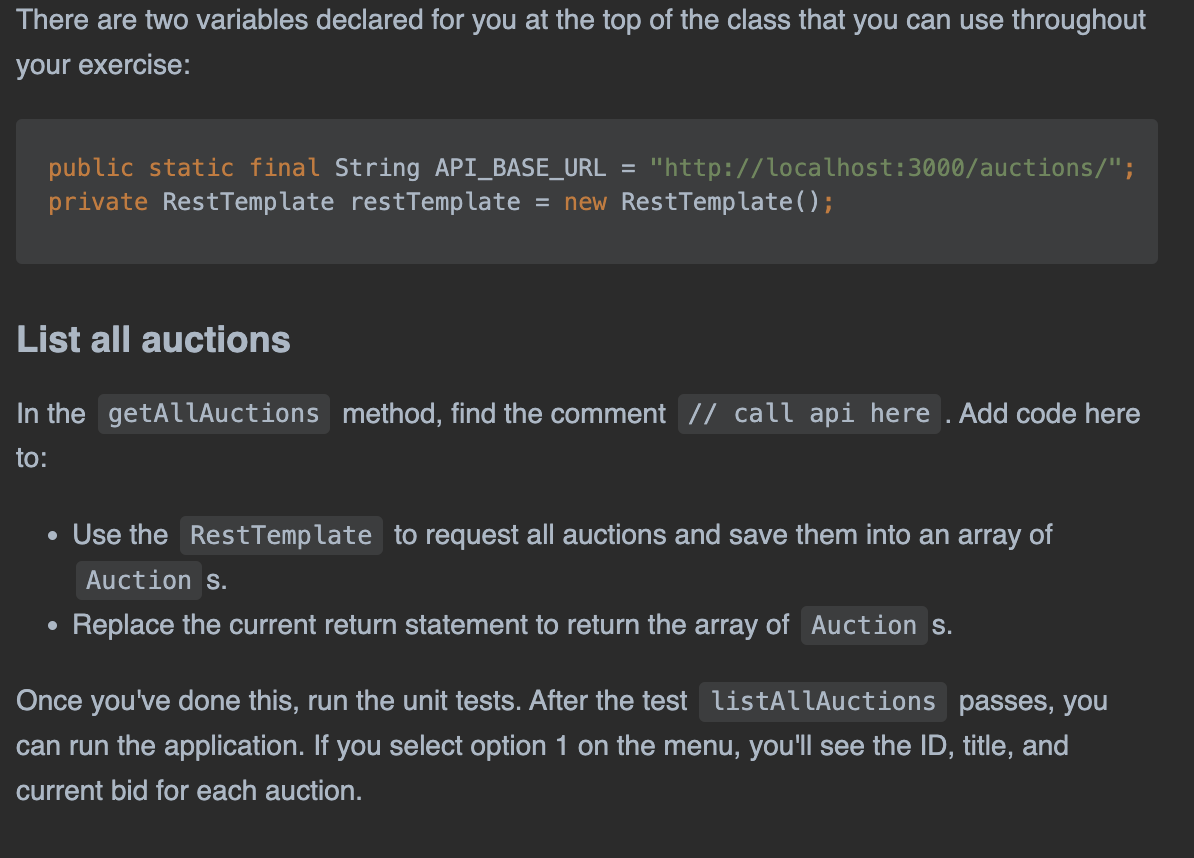
There are two variables declared for you at the top of the class that you can use throughout your exercise: public static final String API_BASE_URL = "http://localhost:3000/auctions/"; private RestTemplate restTemplate = new RestTemplate(); List all auctions In the getAllAuctions method, find the comment // call api here . Add code here to: • Use the RestTemplate to request all auctions and save them into an array of Auction s. Replace the current return statement to return the array of Auction s. ● Once you've done this, run the unit tests. After the test listAllAuctions passes, you can run the application. If you select option 1 on the menu, you'll see the ID, title, and current bid for each auction.
There are two variables declared for you at the top of the class that you can use throughout your exercise: public static final String API_BASE_URL = "http://localhost:3000/auctions/"; private RestTemplate restTemplate = new RestTemplate(); List all auctions In the getAllAuctions method, find the comment // call api here . Add code here to: • Use the RestTemplate to request all auctions and save them into an array of Auction s. Replace the current return statement to return the array of Auction s. ● Once you've done this, run the unit tests. After the test listAllAuctions passes, you can run the application. If you select option 1 on the menu, you'll see the ID, title, and current bid for each auction.
Chapter8: Advanced Method Concepts
Section: Chapter Questions
Problem 3E
Related questions
Question
Please give the proper answer with an explanation and step-by-step solution.
![8 usages Josh Tucholski
public class Auction Service {
J
3
3 usages
public static String API_BASE_URL = "http://localhost:3000/auctions/";
no usages
private RestTemplate restTemplate = new RestTemplate();
3 usages Josh Tucholski *
public Auction[] getAllAuctions() {
}
// call api here
public static final String API_BASE_URL = "http://localhost:3000/auctions/";
private RestTemplate restTemplate = new RestTemplate();|
return null;](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2Fef3e1da9-efa9-41bf-8766-d612578816c8%2F8c09d473-4dbf-4c1c-a5e5-3f3059971028%2Fxohb89g_processed.png&w=3840&q=75)
Transcribed Image Text:8 usages Josh Tucholski
public class Auction Service {
J
3
3 usages
public static String API_BASE_URL = "http://localhost:3000/auctions/";
no usages
private RestTemplate restTemplate = new RestTemplate();
3 usages Josh Tucholski *
public Auction[] getAllAuctions() {
}
// call api here
public static final String API_BASE_URL = "http://localhost:3000/auctions/";
private RestTemplate restTemplate = new RestTemplate();|
return null;
Transcribed Image Text:There are two variables declared for you at the top of the class that you can use throughout
your exercise:
public static final String API_BASE_URL = "http://localhost:3000/auctions/";
private RestTemplate restTemplate = new Rest Template();
List all auctions
In the getAllAuctions method, find the comment // call api here . Add code here
to:
• Use the Rest Template to request all auctions and save them into an array of
Auction s.
Replace the current return statement to return the array of Auction s.
●
Once you've done this, run the unit tests. After the test listAllAuctions passes, you
can run the application. If you select option 1 on the menu, you'll see the ID, title, and
current bid for each auction.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,