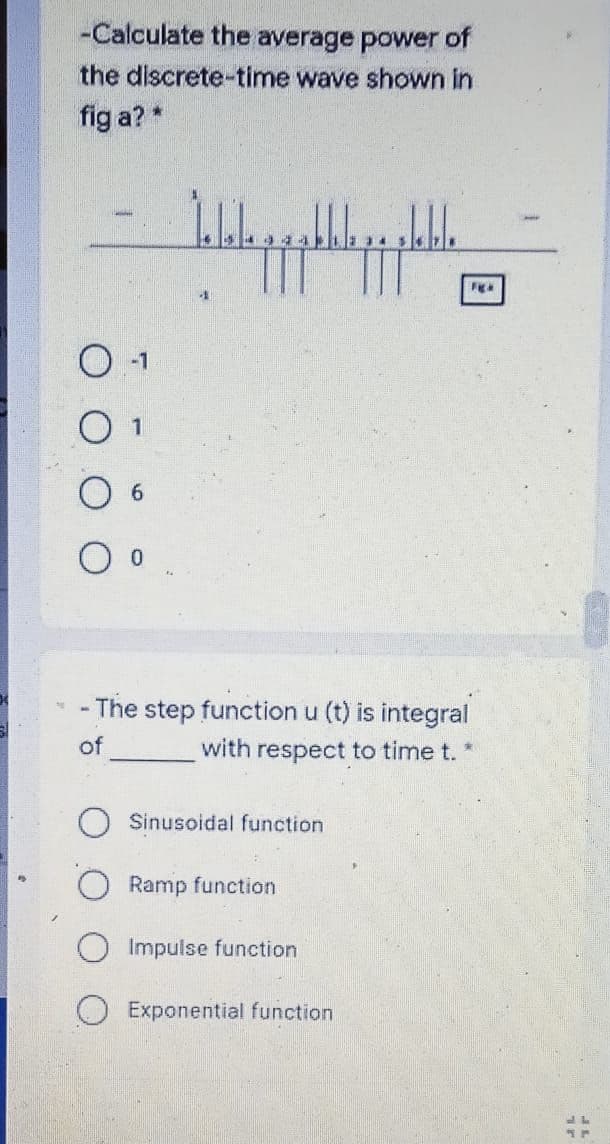
-Calculate the average power of the discrete-time wave shown in fig a?
Q: What is Enumerated Integer providing an example to illustrate your point? Assure uniqueness, qua...
A: The solution to the given problem is below.
Q: Examine the advantages and disadvantages of various system models.
A: There are various methods of developing software models which depends on the projects objective and ...
Q: What type of possible error messages you can get when you try to login with the ssh-i option?
A: answer is
Q: the function returns the result as a string if the expression is legal. the expression returns an em...
A: Python is one of the most widely used programming language which has been used to create different ...
Q: Compute the edit distance (using insertion cost 1, deletion cost 1, substitution cost 1) of "beat" t...
A: The edit distance is a way of measuring of how related two strings are. This is defined as the small...
Q: Suppose memory access takes 100 ns and register access takes 1 ns (or less), calculate and compare t...
A:
Q: There are 4 paths as follows: Path 1: Start → 1 → 4 → 5 → 6 → 7 → 8 → 9 → 10 → End ...
A: SOLUTION:- 1.1 Activity/event a c b Mean Variance Start 1 5 15 30 16.6666667 158.333333 2 5...
Q: RAnswer the following questions by circling either true (T) or false (F) 1. T F Every database has m...
A:
Q: True or false? An organization should periodically conduct an inspection of its systems and practice...
A: Hello student, hope you are doing good. This is an objective question and the answer is provided bel...
Q: sk user to enter 10 grade and determine the average of grades. first you have to validate grade and ...
A: The valid grades lies between 0-100 and this validation is done using a while loop and the outer loo...
Q: write c++ program to input a year and to check whether it is a leap year or not
A: The above question that is leap year pogram in c++ is written below
Q: Look into one intriguing data or text mining application and explain it.
A: Text mining: Text mining, also known as text data mining, is the technique of extracting high-qualit...
Q: What is the operation of SETI?
A: Introduction The Search for Extraterrestrial Intelligence (SETI) is a general abbreviation for the s...
Q: Examine the benefits and drawbacks of various system models.
A: answer is
Q: write c++ program to input a year and to check whether it is a leap year or not
A: I have provided C++ CODE along with CODE SCREENSHOT and also provided TWO OUTPUT SCREENSH...
Q: write a c# program A parking garage charges a $3.50 minimum fee to park for up to three hours. The ...
A: #include<iostream>#include<conio.h>#include<iomanip>using namespace std; float cha...
Q: Examine the advantages and disadvantages of various system models.
A: System Models are mainly divided into 5 types: -> Minicomputer model -> Workstation model -...
Q: List 10 merits and demerits of ict
A: ICT is abbreviated for information and communications technology and in today’s world called as IT(I...
Q: In this lesson, we spoke about several rewriting and editing strategies. What is your go-to editing ...
A: Introduction: Editing or revising is making changes to the structure, format, and content. Rewriting...
Q: Let's try to add dynamically property of an object and the property must be function and variable in...
A: Required:- Let's try to add dynamically property of an object and the property must be function and ...
Q: Basic data types, keyboard input and conditional statements The front tires of a car should both hav...
A: As there is no programming language mentioned so program is attempted in java language Start in...
Q: What is the difference between using +/- versus = when setting file permissions? Is there any benefi...
A:
Q: Explain the phrase "balanced scorecard" in just a few words. What role does it play in the operation...
A: Operation of the Business: The everyday actions of a firm that help it build its worth and earn prof...
Q: Give two examples of when NOT to use a use case and explain why not.
A: Use Case Diagram: A UML use case diagram is the primary form of gadget/software requirements for a b...
Q: Countermeasures come in a variety of sizes, shapes, and levels of complexity. This document endeavor...
A: Network Security Countermeasures :The following countermeasures address network security concerns th...
Q: Decide whether the given set of sentences are Con Inconsistent. 1. SM -~ C & [U v (- C & B)] C 2. SM...
A: Lets see the solution in the next steps
Q: Explain what the memory addressing capacity of the 20-bit address bus will be.
A: given- Explain what the memory addressing capacity of the 20-bit address bus will be.
Q: Describe why web application security is critical. What may go wrong with an unsecured application? ...
A: Introduction: In this question, we will explore why web application security is important for every ...
Q: her given grammar is SLR(1) or not? Explain step by step. S->Aa/bAc/dc/dba A->d
A: we obtain the state diagram as follows:
Q: What happens when an exception occurs in a method but it is not caught inside the method? The met...
A: Your answer is here given below.
Q: Problem Definition: Create and design a program that will accept employee’s information such as empl...
A: S:: In this particular program we need to print an ASCII art. For that, we need to install a library...
Q: What happens to two truly-redundant features (i.e., one is literally a copy of the other) if we use ...
A: What happens to two truly-redundant features (i.e., one is literally a copy of the other) if we use ...
Q: A. What is the ciphertext of M=9 if Alice chooses the random integer k=4? B. If Alice uses the same ...
A: The answer is
Q: Assume, r1= 0XA2FF0010, r2= 0×5D00FFF0 What is the ARM statement which correspond to the each follow...
A: Answer 1: ========================================================================= figure 1:
Q: (Using C++) Define a base class vehicle and its two derived classes :Car and Scooter. Write a progra...
A: Here is your C++ code with an output.
Q: Artificial intelligence Without using any python libraries or built in python functions: Show you ca...
A: Finding Mode without Python Libraries: from collections import Counter # list of elements to calcu...
Q: n successful project vision includes what are known as the "components." gnificance?
A: Lets see the solution.
Q: ead a name from the user( assume the user enters first, middle and last names. The name pai eparated...
A: CODE - JAVA : import java.util.*;public class Main{ public static void main(String[] args) { ...
Q: Identify three kinds of software that are necessary to support a company's operations and explain ho...
A: These software tools are mainly needed for small businesses, where the management of individual busi...
Q: What are whole disc encryption (WDE) solutions and when do they need to be used?
A: INTRODUCTION: Whole disc encryption is a method of protecting data by turning it into unreadable co...
Q: Suppose the implementation of an instruction set architecture uses three classes of instructions, wh...
A:
Q: What is the difference between using +/- versus = when setting file permissions? Is there any benefi...
A: Basically +/- is used to add or delete permissions for the file. = is used to specify the new set of...
Q: Complete the code provided to add the appropriate amount to totalDeposit. 5290 2416604.qx3zqy7 1 #in...
A: Introduction:
Q: Question:: What's the difference between Stored Procedures and Scripts? What is the purpose of each?...
A: Difference between Stored Procedure and Scripts: Both stored manner and SQL script template are "bat...
Q: Suppose the implementation of an instruction set architecture uses three classes of instructions, wh...
A: The answer is
Q: [rdt3.0] Now suppose that the network with a data rate of R b/s can deliver out of order and that th...
A: Reliable data transfer 3.0---------Channels with Errors and Loss Approach: sender waits “reasonabl...
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a messag...
A: We have a total of N layers.. The message generated at the top layer is M bytes So the message have ...
Q: 1. Write a program (WAP) to create an undirected graph using adjacency matrix representation. Number...
A: c++ program for undirected graph -------------------------------------------------------------------...
Q: List five of the records and information manager's duties.
A: Manager of Records: Each firm must organise and store all of its data in order to optimize its proce...
Q: Show that the language {amb n | m ≠ n} is context-free.
A: Here in this question we have given a grammer and we have asked to show that the language is context...
Step by step
Solved in 3 steps

- 5. We can find all the Trigonometric functions in C++ as a built-in function. a) True b) FalseFind the simplest form of the function F=A'B'C'+A'B'C'D'+BD.Hello. I need help in converting temperature for the fahrenheit to celsius equation: C = 5/9 (fahrenheit - 32) in C++. I need to use setw, setprecision, and fixed functions.
- -----If you pass n=2 to your function your 2nd term of Fibonacci series is 1 and (n-1)th= 1" term of Fibonacci series is 0 and (n+1)th= 3rd term of Fibonacci series is 1.----.Write down the complement of the following function, f. f=ab՛(c+d՛e)+a՛bc79. To find the decimal value of 1111, that is 15, we can use the function: a. int(1111,10) b. int(‘1111’,10) c. int(1111,2) d. int(‘1111’,2)
- (Automotive) a. An automobile engine’s performance can be determined by monitoring its rotations per minute (rpm). Determine the conversion factors that can be used to convert rpm to frequency in hertz (Hz), given that 1rotation=1cycle,1minute=60seconds,and1Hz=1cycle/sec. b. Using the conversion factors you determined in Exercise 7a, convert 2000 rpm into hertz.(Practice) Determine names for functions that do the following: a. Find the average of a set of numbers. b. Find the area of a rectangle. c. Find the minimum value in a set of numbers. d. Find the density of a steel door. e. Sort a set of numbers from lowest to highest(Statics) An annulus is a cylindrical rod with a hollow center, as shown in Figure 6.7. Its second moment of inertia is given by this formula: I4(r24r14) I is the second moment of inertia (m4). r2 is the outer radius (m). r1 is the inner radius (m). a. Using this formula, write a function called annulusMoment ( ) that accepts two double-precision numbers as parameters (one for the outer radius and one for the inner radius), calculates the corresponding second moment of inertia, and displays the result. b. Include the function written in Exercise 5a in a working program. Make sure your function is called from main(). Test the function by passing various data to it.
- (Practice) The volume, v, and side surface area, s, of a cylinder are given by these formulas: v=r2ls=2rl r is the cylinder’s radius, and l is its length. Using these formulas, write and test a function named cylinder() that accepts a cylinder’s radius and length and returns its volume and side surface area.Graph the following functions and determine whether the functions are even, odd or neither: (a) y = sin x (b) y = sec xR programming question 181. The corresponding R function for teh PMF is __________.

