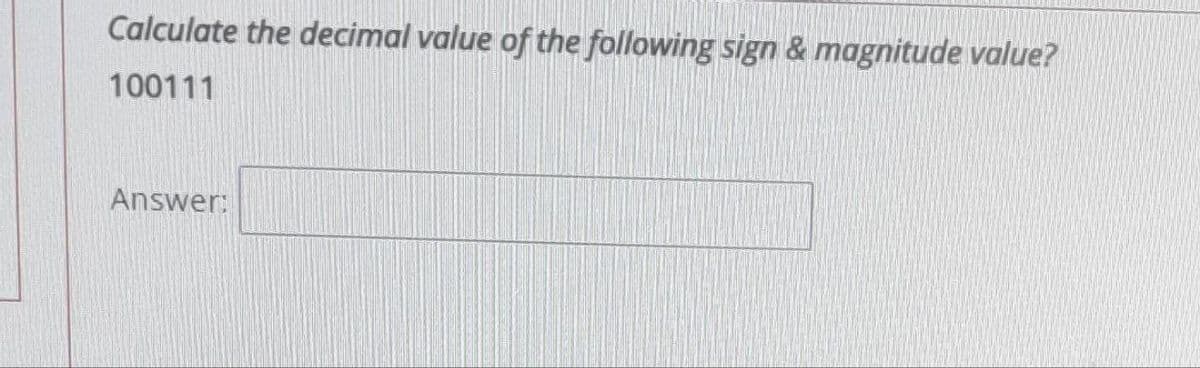
Calculate the decimal value of the following sign & magnitude value? 100111
Q: A computer is an electrical device that can swiftly and correctly store, retrieve, and analyse both…
A: Introduction: A computer is a piece of electronic equipment that can be used to manage information…
Q: 8. Number Pattern 4 by Jemar Jude Maranga Print the pattern below given the value of n Input A…
A: The complete C code is given below with code and output screenshots
Q: What should small businesses do to prevent themselves from becoming the victims of a well-organised…
A: Answer:
Q: How many different methods are there to get into a file, and what are they? What are the benefits of…
A: Given that the existing global system supports both index and direct file access, It is additionally…
Q: Question 8 Which if the following properties does the {(x,y) 1 x % y = 0} for x, y in 1, 2, 3, 4…
A: Answer to the given question: The given relation is reflexive as x%x =0 and antisymmetric because…
Q: A positive integer is entered through the keyboard, write a function by using C language to find the…
A: Answer:
Q: ? How long is an IPv4 address • 32 bits O • 128 bytes O • 64 bits O • 128 bits O .
A: 32-bit IPv4 addresses are 32-bit numbers that are typically displayed in dotted decimal…
Q: What is the difference between sequential and random file organisation ?
A: Sequential access-linear order and Random
Q: Describe the differences between a NoSQL database and a relational database. Identify and discuss…
A: Introduction: Constraints have been placed on relationships inside the system, which helps to ensure…
Q: List and explain the challenges that may develop as a consequence of big data's vast volumes of…
A: Data mining for fresh insights is critical to company success, but the test should not be…
Q: What perspectives should be taken into account while constructing models of software systems?
A: A software system can be denoted as a group of programs that are utilized to solve a specific…
Q: In the context of network diagrams, what are some of the characteristics that are most often seen
A: Network diagram serves as a road map to allow professionals to perform tasks such as understanding…
Q: 25 An example of SOP expression is A+B(C+D) A'B+ AC + AB'C (A+B+C)(A + B' + C) All of the answers…
A:
Q: While developing software system models, how should different views be taken into consideration?
A: let us see the answer:- Introduction:- The practice of creating abstract models of a system, each of…
Q: explain the positive and negative impact of the Information and Communication Technology in our…
A: Positive impact of the Information and Communication Technology 1. Access to information: The…
Q: Because of this, it is necessary to deal with each interrupt class in its own unique manner. It is…
A: Overview: An interrupt is the processor's reaction to an occurrence that demands software attention…
Q: Draw the tree corresponding to the following Prüfer codes (2,7,6,2,2) (3,1,2,3,3)
A: As per the question statement, It is asked to only to draw the tree for the given Priifer codes.
Q: Could you could explain it to me using your own words so that I can have a better grasp on the idea…
A: Given: Client-server systems employ password-based authentication. This approach isn't safe since…
Q: The last question I have is this: what exactly is the point of artificial intelligence? Are there…
A: Artificial intelligence (AI) is a wide-ranging branch of computer science concerned with building…
Q: Would it be possible for you to supply me with a more in-depth look at the metrics that were used…
A: "Software measure" refers to a percentage of quantifiable or countable programming attributes. The…
Q: In what way does a Binary Search Tree work?
A: Binary Search Tree is a binary tree with a spin: the scanned input moves to either the left or right…
Q: is a step-by-step process for solving a problem. Process Program Pseudocode Algorithm includes…
A: Please refer below for your reference: According to company guidelines we are restricted to answer…
Q: Discuss the future of AI in light of its current evolution.
A: Introduction: The future is going to look significantly different for practically every industry and…
Q: Which kinds of network topologies are really doable to create, and which kinds do you think are the…
A: A Network Topology is the interconnection of computer systems or network devices. Physical and…
Q: Explain the outcomes of Information and Communications Technology (ICT) in relation to their…
A: Introduction: In order to communicate, generate, bar, store, and manage data, schools use a wide…
Q: Explain the distinction between a hub and a switch.
A: Introduction: The distinction between a hub and a switch are :
Q: What exactly does it imply when applied to a particular thing for the word "operating system" to be…
A: Introduction System of Operation: An operating system (OS) is a piece of software that manages the…
Q: * ? How long is an IPv4 address • 32 bits O • 128 bytes O • 64 bits O • 128 bits * Which layer of…
A: We need to find the correct option regarding the OSI model.
Q: Network diagrams generally incorporate a variety of features. How can you characterise some of these…
A: The answer is given below
Q: Consider the following typed relational schema describing books and borrowers in a library:…
A: A query is command that requests a set of data from the database. SQL is a structured type query…
Q: Explain how to utilise network access control (NAC) and what the term "remediation" means in the…
A: Introduction: The corrective action within the framework of NAC.
Q: Let G be a directed weighted graph with n vertices and m edges such that the edges in G have…
A: So, the Dijkstra Algorithm may be used to do this. The vertex name, I presume, may be changed to…
Q: Q4/ Write functions to plot y = 0.1cos(x) in the interval 0≤x≤ 2л with yellow color, * symbol and…
A: syms x fplot(sin(x),[-2*pi 2*pi]) grid on title('sin(x) from -2\pi to 2\pi') xlabel('x') ylabel('y')…
Q: When it comes to an Interrupt Service Routine, which step is more important for the programmer to…
A: Solution: ISRs are the heart of any microprocessor-based system. They handle external service…
Q: Scripts and stored procedures vary in the following ways: What's the point of each of these? Are…
A: A Stored Procedure could properly be called a script.
Q: In the process of building models for software system architecture, which perspectives have to be…
A: What perspectives should be taken into consideration while building software system models? As we…
Q: Explain the importance of firewalls in terms of the security offered by networks and the internet.…
A: Fencing your property protects your house and keeps trespassers at bay; similarly, firewalls are…
Q: In today's world, every company has integrated big data into its information technology platforms.…
A: Introduction: Every firm in the modern world has integrated big data into its information…
Q: As technology advances, what is the notion of digital privacy? What examples can you provide of…
A: Introduction: What is emerging technology's notion of digital privacy? Cybersecurity examples?
Q: What are the fundamental components of an Android application? Explain each one.
A: Which software is used to run emulator or an android device, called android application. This…
Q: A battery-powered power protection device that offers a few minutes of electricity. What is UPS's…
A: Introduction: Nickel-cadmium, lead-acid, and lithium-ion batteries are the principal types used in a…
Q: Solve the system by using linsolve in Matlab -x-5y+6z=-24
A: here in given question solve the equation using linsolve in matlab.
Q: Explain in detail the operating system's kernel, starting with the most basic components and working…
A: The answer is as follows
Q: nct types of computer software are th
A: Introduction: Below the describe distinct types of computer software
Q: 10. Inverted Number-Triangle by Julian Semblante Write a C program that will ask for a positive…
A: Answer: C Source Code: #include <stdio.h> int main() { for (int i = 5; i >= 1; i--) {…
Q: What exactly does it imply when applied to a particular thing for the word "operating system" to be…
A: System of Operation: An operating system (OS) is a piece of software that manages the hardware and…
Q: Provide a synopsis in a single phrase of the components of the kernel that are shared by the…
A: Introduction The kernel is the computer's main operating system (OS) processor. As the core of the…
Q: computer science -What are some of the methods for recording data flows?
A: Introduction: The recording of data flows or the creation of a data flow diagram
Q: What are the fundamental components of an Android mobile application ?
A: Introduction: Android applications (apps) are a type of software that may either be installed on a…
Q: The definition of a real-time operating system might be accomplished via the use of examples. What…
A: Introduction: Real-time operating system: This type of operating system is frequently applied in…
Step by step
Solved in 2 steps

- ((xy)'+xy')' evaluates to waht the correct answer a.y b.x c.0 d.1Convert the following base 2 numeral to a base 10 numeral and enter your answer in the box.111110(Remember, the above number is in Base 2!)Base 10 numeralWhich binary number represents the decimal number 133? Do not include the base number when you write your answers. Group of answer choices A. 10000101 B. 10001011 C. 11000001 D. 10000111
- What is the decimal value of octal number 143? Do not include the base number when you write your answers. Group of answer choices A. 217 B. 8F C. 99Subtract in the indicated base (base eight). The answer is [1]-base eight. (Just type the numerica value only). 462-base eight - 177-base eightWhat is the lowest base in which the number 1C7 could be a valid number? Question 11 options: A. base 12 B. base 10 C. octal D. base 13 E. hexadecimal
- Convert the following base 2 number to base 10. You must show the steps on how you reach the final result. (1011 1101)2 (1101 1011)2In MASM Prompt the user for coefficients a, b, and c of a polynomial in the form ax2 + bx + c = 0. Calculate and display the real roots of the polynomial using the quadratic formula, using functions. If any root is imaginary, display an appropriate message.Evaluate the following arithmetic expressions 1. 5 / 2 + 4 - 2 * 7 % 3 2. 5.0 / 2 + 4 - 2 * 7 % 3 3. 17 - 5 * 4 / 10 * 5 / 2





