Predict with Fuzzy Logic if: Age 45, IMT 26 and Alcohol Variable 2!
Principles of Information Systems (MindTap Course List)
12th Edition
ISBN:9781285867168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter10: Information And Decision Support Systems
Section: Chapter Questions
Problem 4SAT
Related questions
Question
100%
Fuzzy Logic :
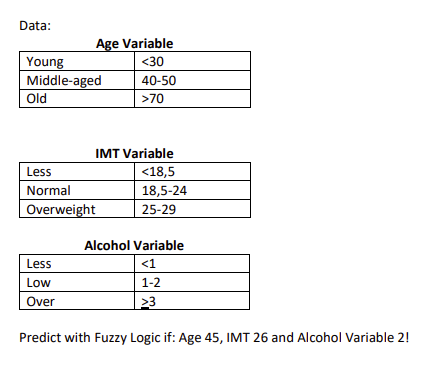
Transcribed Image Text:Data:
Young
Middle-aged
Old
Age Variable
<30
40-50
>70
Less
Low
Over
IMT Variable
<18,5
18,5-24
25-29
Less
Normal
Overweight
Alcohol Variable
<1
1-2
23
Predict with Fuzzy Logic if: Age 45, IMT 26 and Alcohol Variable 2!
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 3 images

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
Can you please calculate how this would be if those parameters are put into the cancer parameters a patient can get with the fuzzy set given ?
| Parameter | |
| Desc | interval % |
| Very little | < 20 |
| little | 20 - <40 |
| normal | 40 - <60 |
| high | 60-70 |
| very high | > 70 |
Solution
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning