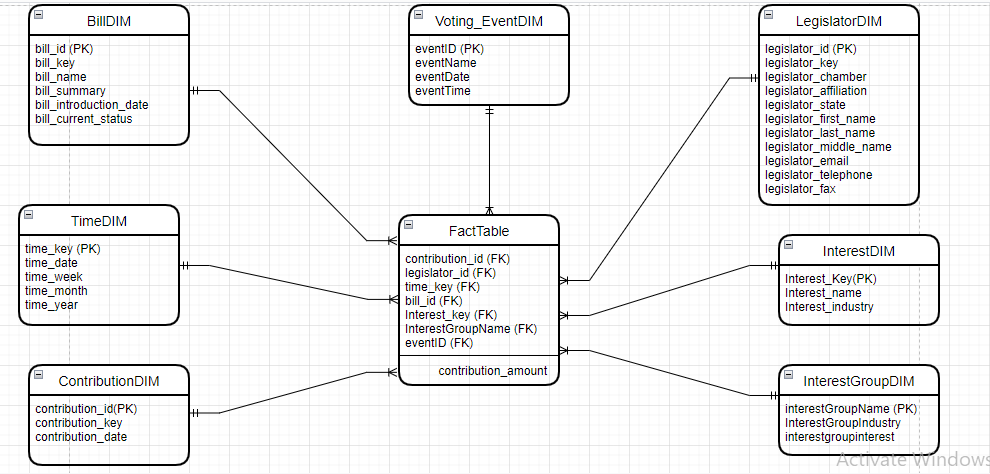
Explain what principles of dimensional modeling this fact table violates
Q: class Student: students = 0 # this is a class attribute def _init__(self, name, staff): self.name =…
A: Code: class Student: students =0 def __init__(self,name,staff): self.name=name…
Q: List, BST (binary search trees), and AVL each have their own unique search time challenges; please…
A: Binary Search tree and AVL tree distinctions Because AVL trees likewise have a maximum of two…
Q: Is there anything that distinguishes hacktivism from other forms of cybercrime and terrorist…
A: hacktivism Derived from combining the words 'Hack' and 'Activism', hacktivism is the act of…
Q: Suppose you have the following graph, what is the correct representation of its edges? D O E=…
A: correct ans:- D- E= {(A,B), (B,A),(B,C),(C,B),(B,D),(D,B),(C,E),(E,C),(D,E),(E,D),(E,F),(F,E)…
Q: of incorrectly transmitting a single bit. Let w 10100011 be a wor which is transmitted over the…
A: The answer is
Q: Although it is difficult to pinpoint exactly what it is about the inclusion of technology into the…
A: When it comes to education and training, the process may be thought of as the method through which…
Q: If you own a large landscaping business in your area, you may have hundreds of customers. Determine…
A: Intro: If you own a large landscaping business in your area, you may have hundreds of customers.…
Q: Each of the following backup types: full, differential, incremental, selected, CPD, and cloud,…
A: Introduction: Indicate the benefits and drawbacks of full, differential, incremental, selective,…
Q: What attracts some people to the world of cybercrime?
A: Introduction: Cybercriminals use the internet and computer technology, among other things, to get…
Q: How may the actions of a user who is attempting to add data to the database lead to the creation of…
A: Answer:
Q: what are the differences between the enormous data and the big data
A: Data is a set of quality or quantity variables - either edible or random, machine-readable or…
Q: ✓ Out of the following class declarations which one is/are invalid? (i) Class A { int x; }; (ii)…
A: Classes are an important concept of object-oriented programming. They are the way using which other…
Q: When it comes to computer chips, what is the difference between microprocessors and…
A: Microprocessor and microcontroller.
Q: Consider a system with 256Mbytes of main memory with page size of 4Kbytes. It has a logical address…
A: Below is the answer to above questions.
Q: C. BINARY CODE (Questions #25 & #26) How many bits are required to store an image of 25. 1MB? 26. 2…
A: Dear student, As per guidelines, I can answer only first three questions. Please repost your pending…
Q: Those individuals whose processes have been found to include a deadlock will be granted access to…
A: A deadlock in the operating system happens when a process or thread enters a waiting state because a…
Q: The phrase "third tier" refers to the layer that is located in the middle of a three-tier…
A:
Q: In database systems, the file-based method has two major drawbacks. explain them in a few sentences
A: EXPLANATION: In the file-based method, data is saved on a computer in one or more separate files…
Q: What role does the operating system play in processor management?
A: Introduction: Process management in operating systems comprises tasks associated with processing…
Q: What value of R^2 (coefficient of determination) indicates that the model performed worst? Answer:
A: Here is the explanation:
Q: What is the significance of computer programming?
A: Introduction: A computer programme is a set of instructions that a computer may use to do a certain…
Q: Static variables can't be declared inside a local class.
A: A static variable is one that has been "statically" allocated, which means that its lifespan (or…
Q: What is the use of TLD server in DNS?
A: Given that the the question needs use of TLD server in DNS.
Q: What does "cloud computing" mean in the context of e-commerce?
A: Introduction: Cloud computing is the hosting and distribution of information and on-demand computer…
Q: compose a paragraph comparing and contrasting the pros and disadvantages of time-sharing and…
A: Operating System: An Operating System is a software that provides a user interface for computer…
Q: In Pakistan, Google has lately opened an office. There, you're being scouted. You were asked during…
A: The microprocessor is an electronic device which is having the asthmatic and logic circuit to…
Q: A compound Boolean expression that will evaluate to True if and only if both of its subexpressions…
A: Answer: and Explanation: A compound boolean expression is nothing but a logical operator which…
Q: The phrase "third tier" refers to the layer that is located in the middle of a three-tier…
A: Answer:
Q: In what ways are the Whetstone, Dhrystone, and Linpack benchmarks lacking, and how do the SPEC CPU…
A: In what ways are the Whetstone, Dhrystone, and Linpack benchmarks lacking, and how do the SPEC CPU…
Q: Discuss why you believe patch management remains a challenge for some organisations and businesses.…
A: Introduction: Patch control is a mechanism for distributing and using software upgrades. These…
Q: consider the following model: y = b_0+ b_1*x what is the parameter b_0? O a. the slope coefficient.…
A: To find what is the parameter for b_0.
Q: Questions 1. What is prime objective of software engineering? Define software engineering paradigm?…
A: Below is the answer to above questions. I hope this will be helpful for you...
Q: necessary to provide an explanation for the connection that exists between object-oriented…
A: Object Oriented Paradigm: The term "object oriented paradigm" refers not to a specific programming…
Q: You are given the arrival and departure times of trains reaching to a particular station. You need…
A: An algorithm is the special rules or the produces that are used for the solving a well defined…
Q: What is more harder to implement for compilers, the VLIW algorithm or the superscalar algorithm?…
A: Answer:
Q: The attributes field of objects is a potential storage location for data. The qualities of the class…
A:
Q: List, BST (binary search trees), and AVL all have different search time issues; please explain how…
A: Binary Search tree and AVL tree distinctions Because AVL trees likewise have a maximum of two…
Q: When the value 17 is removed from the following Binary Search Tree, the value a (2) 12 O23 14 19 12…
A: A binary search tree arranges the components in a certain order. The left node's value in a binary…
Q: the five most important pieces of hardware in a comp
A: Lets see the solution.
Q: For a report to focus on the needs of typical business readers today, it needs to be trustworthy,…
A: Here is the explanation about the report:
Q: Develop/create a Decision Table and Decision Tree that represents the registration system at your…
A: I will explain it in details,
Q: Explain the methods used by List, BST (binary search trees), and AVL to arrive at their conclusions.
A: BST All of the nodes in a tree that is a binary search tree (BST) adhere to the following…
Q: Indicate where the language below fits into the complexity hierarchy. All strings of Os and 1s that…
A: Answer:
Q: Defintion: What is internet addiction?
A: In general terms, addiction is the behavior which is shown by the people, where they completely…
Q: How challenging is it to get either the VLIW or the superscalar architecture into production? Which…
A: Compilers are devices used to change over programs written in undeniable level dialects to low-even…
Q: A pipelined CPU has a longer clock cycle time than a non-pipelined CPU.
A: The answer to the given question is in next step.
Q: There are numerous instructions that must flow through the CPU at the same time. In what ways does…
A: A multiprocessor is a type of operation which is running more than two processors in a computer to…
Q: What are the differences between time-sharing and distributed operating systems? What are the…
A: ANSWER:-
Q: What is more harder to implement for compilers, the VLIW algorithm or the superscalar algorithm?…
A: Implement for Compilers: A high-level source program is transformed formally into a low-level target…
Q: Defintion: What is internet addiction?
A: A condition in which a person: Is confused is referred to as a disorder. It is primarily…
Explain what principles of dimensional modeling this fact table violates
Step by step
Solved in 2 steps with 1 images

- <!DOCTYPE html><html><head><title>Name information creater</title><script src="1.js"></script></head><body><h1>create name and gender</h1><table></tr><tr><td> </td><td><input type="submit" value="Submit" id="Submit"></tr></table><p id="msgField"> </p></body></html> function name() {var male firstName = ["James""Joe" "John" "Juan" "Robert" "Jack" "Michael" "Albert" "William " "Jonathan" "David" "Justin" "Richard" "Terry" "Charles" "Gerald" "Joseph" Keith "Thomas" "Samuel" "Christopher" "Willie" "Daniel"];var femail firstName = ["Mary""Alice" "Patricia" "Julie" "Linda" "Heather" "Barbara" "Teresa" "Elizabeth" "Doris" "Jennifer " "Gloria" "Maria" "Evelyn"…Data Exchange assignment. Create an Excel Spreadsheet with Column names: LastName FirstName City State Age Major Enter 10 rows of data to populate your spreadsheet with test data. Save this file as an XLSX (standard Excel Format); base spreadsheet. Save and view the data in its ‘raw’ format Save this file as Windows Comma Separated .CSV Close Excel Open this .CSV file using a text editor (e.g. Notepad) Take a screen shot of this and include it in your writeup document What you notice that’s different about this format vs the standard XLSX format? XML Using your TEXT editor, create a file called ‘studentdata.xml’ Enter the studentdata.xml below as the XML schema and save it Open your original .XLSX file On the Developer tab, open the ‘XML Source’ task pane If you don't see the Developer tab, do the following to display it: Click File > Options. In the pane on the left, click the Customize Ribbon category. Under Main Tabs, check the Developer box, then click OK. Click XML Maps…PHP According to table the in the image and code program 1 <?php include ('config.php'); $ matrixnum = $_POST['matrixnum']; $ subject_code = $_POST['subject_code ']; $ quiz = $_POST['quiz']; $ assignment = $_POST['assignment']; $ project = $_POST['project']; $ total_marks= $_POST['total_marks']; $ grade = $_POST['grade']; Code program 1 (Based on the program section (Code Program 1), assume that the data wants to be updated by the user. Build program code to provide instructions for updating the data to the assessments table. In addition, build a link to view the updated data.)
- I have a project I need assistance with using javascript. I am needing to reverese the view order in which the suppliers are when a user clicks on the Supplier field. For example please see image 1. Now I found the code that pulls in that table in on that page: See image 2. The variable: var supplierField = form.addField('custpage_supplier', 'select', 'Supplier', 'customrecord_reorder_suppliers').setLayoutType('startrow'); This is the code and in particular this id: 'customrecord_reorder_suppliers' is pulling in the field values for screen shot 1. However, I am not sure how to change the order view. Currently the order view is: Number Supplier Name => (12344 Walmart) My goal is to change it to: Supplier Name Number => (Walmart 12344) I have tried using the built in JS methods like so: 'customrecord_reorder_suppliers'.split(' ').reverse().join(' ') but to no avail. I also created a new variable and reassigned the initial variable and called the same methods on the new variable…Can someone help me create a Crows foot erd using these entities? I need to put in the appropriate relationships and cardinality symbols. PLEASE HELP Table restaurant Camis - String DBA - String Boro - String Building - String Street - String Zipcode - String Phone - String Cusine Description - String Latitude - Int Longitude - Int Table inspection. inspection date - String Action - String Score - Int Grade - String Grade date - String Record Date. - String Inspection date. - String Community Board - String 9.council district - String Table violation Violation Code - String violation description - String critical flag - TextSomeone please help me,Basec on the image given ( Loan and Loan output). How to Use the JAVA , HTML and JSP code given to create or change something and make the output ( Loan output) can store in database (Create a database named " bookingcourtdb" and "jdbc / bookingcourtds") File : ComputeLoan.html <!-- View component: ComputeLoan.html --><html> <head> <title>Compute Loan</title> </head> <body> <form method="post" action="ComputeLoan"> Compute Loan Payment <br /> Loan Amount<input type="text" name="loanAmount"/><br /> Annual Interest Rate<input type="text" name="annualInterestRate"/><br /> Number of Years<input type="text" name="numberOfYears" size="3" /><br /> <p><input type="submit" name="Submit" value="Compute Loan Payment" /> <input type="reset" value="Reset" /></p>…
- ###Important variables below # gauteng ebp data as a listgauteng = ebp_df['Gauteng'].astype(float).to_list() # dates for twitter tweetsdates = twitter_df['Date'].to_list() # dictionary mapping official municipality twitter handles to the municipality namemun_dict = { '@CityofCTAlerts' : 'Cape Town', '@CityPowerJhb' : 'Johannesburg', '@eThekwiniM' : 'eThekwini' , '@EMMInfo' : 'Ekurhuleni', '@centlecutility' : 'Mangaung', '@NMBmunicipality' : 'Nelson Mandela Bay', '@CityTshwane' : 'Tshwane'} # dictionary of english stopwordsstop_words_dict = { 'stopwords':[ 'where', 'done', 'if', 'before', 'll', 'very', 'keep', 'something', 'nothing', 'thereupon', 'may', 'why', '’s', 'therefore', 'you', 'with', 'towards', 'make', 'really', 'few', 'former', 'during', 'mine', 'do', 'would', 'of', 'off', 'six', 'yourself', 'becoming', 'through', 'seeming', 'hence', 'us', 'anywhere', 'regarding', 'whole', 'down', 'seem', 'whereas', 'to', 'their',…C2 Extend Your Knowledge: Updating a Webpage with Semantic Elements <!DOCTYPE html> <!-- Student Name: File Name: index.html Date: 04/14/2022 --> <html lang="en"> <head> <title>CH 2 Extend Your Knowledge</title> <meta charset="utf-8"> </head> <body> <div id="header"> <h1>Accessibility Guidelines</> </header> <div id="nav"> <p>Perceivable Operable Understandable Robust</p> </nav> <div id="main"> <p>Guidelines for Principle 1: Perceivable</p> <p>Guideline 1.1 provides an overview of text alternatives for non-text content, such as images, media, or controls.</p> <p>Guideline 1.2 provides an overview of alternatives for time-based media, such as providing captions or an audio description.</p> <p>Guideline 1.3 provides an overview for creating…CREATE TABLE ARTISTS( artist_id CHAR(30), artist_name CHAR(30), artist_pop INT(5), PRIMARY KEY (artist_id)); CREATE TABLE TRACKS( track_id CHAR(30), track_name CHAR(30), duration INTL(10), tempo REAL, PRIMARY KEY (track_id)); CREATE TABLE USERS( user_id CHAR(30), user_name CHAR(30), age INT(5), nationality CHAR(30), num_track_listened INT(10), PRIMARY KEY (user_id)); CREATE TABLE RECORD( artist_id CHAR(30), track_id CHAR(30), PRIMARY KEY (artist_id, track_id), FOREIGN KEY (artist_id) REFERENCES ARTISTS, FOREIGN KEY (track_id) REFERENCES TRACKS); CREATE TABLE LISTEN( user_id CHAR(30), track_id CHAR(30), PRIMARY KEY (user_id, track_id), FOREIGN KEY (user_id) REFERENCES USERS, FOREIGN KEY (track_id) REFERENCES TRACKS); CREATE TABLE FOLLOW( user_id CHAR(30), artist_id CHAR(30), follow_date datetime, PRIMARY KEY (user_id, artist_id) FOREIGN KEY (user_id) REFERENCES USERS, FOREIGN KEY (artist_id) REFERENCES ARTISTS); According to the six table, write a single SQL…
- CREATE TABLE ARTISTS( artist_id CHAR(30), artist_name CHAR(30), artist_pop INT(5), PRIMARY KEY (artist_id)); CREATE TABLE TRACKS( track_id CHAR(30), track_name CHAR(30), duration INTL(10), tempo REAL, PRIMARY KEY (track_id)); CREATE TABLE USERS( user_id CHAR(30), user_name CHAR(30), age INT(5), nationality CHAR(30), num_track_listened INT(10), PRIMARY KEY (user_id)); CREATE TABLE RECORD( artist_id CHAR(30), track_id CHAR(30), PRIMARY KEY (artist_id, track_id), FOREIGN KEY (artist_id) REFERENCES ARTISTS, FOREIGN KEY (track_id) REFERENCES TRACKS); CREATE TABLE LISTEN( user_id CHAR(30), track_id CHAR(30), PRIMARY KEY (user_id, track_id), FOREIGN KEY (user_id) REFERENCES USERS, FOREIGN KEY (track_id) REFERENCES TRACKS); CREATE TABLE FOLLOW( user_id CHAR(30), artist_id CHAR(30), follow_date datetime, PRIMARY KEY (user_id, artist_id) FOREIGN KEY (user_id) REFERENCES USERS, FOREIGN KEY (artist_id) REFERENCES ARTISTS); According to the six table, write a single SQL…CREATE TABLE ARTISTS( artist_id CHAR(30), artist_name CHAR(30), artist_pop INT(5), PRIMARY KEY (artist_id)); CREATE TABLE TRACKS( track_id CHAR(30), track_name CHAR(30), duration INTL(10), tempo REAL, PRIMARY KEY (track_id)); CREATE TABLE USERS( user_id CHAR(30), user_name CHAR(30), age INT(5), nationality CHAR(30), num_track_listened INT(10), PRIMARY KEY (user_id)); CREATE TABLE RECORD( artist_id CHAR(30), track_id CHAR(30), PRIMARY KEY (artist_id, track_id), FOREIGN KEY (artist_id) REFERENCES ARTISTS, FOREIGN KEY (track_id) REFERENCES TRACKS); CREATE TABLE LISTEN( user_id CHAR(30), track_id CHAR(30), PRIMARY KEY (user_id, track_id), FOREIGN KEY (user_id) REFERENCES USERS, FOREIGN KEY (track_id) REFERENCES TRACKS); CREATE TABLE FOLLOW( user_id CHAR(30), artist_id CHAR(30), follow_date datetime, PRIMARY KEY (user_id, artist_id) FOREIGN KEY (user_id) REFERENCES USERS, FOREIGN KEY (artist_id) REFERENCES ARTISTS); Based on the six tables above, write a single SQL…CREATE TABLE ARTISTS( artist_id CHAR(30), artist_name CHAR(30), artist_pop INT(5), PRIMARY KEY (artist_id)); CREATE TABLE TRACKS( track_id CHAR(30), track_name CHAR(30), duration INTL(10), tempo REAL, PRIMARY KEY (track_id)); CREATE TABLE USERS( user_id CHAR(30), user_name CHAR(30), age INT(5), nationality CHAR(30), num_track_listened INT(10), PRIMARY KEY (user_id)); CREATE TABLE RECORD( artist_id CHAR(30), track_id CHAR(30), PRIMARY KEY (artist_id, track_id), FOREIGN KEY (artist_id) REFERENCES ARTISTS, FOREIGN KEY (track_id) REFERENCES TRACKS); CREATE TABLE LISTEN( user_id CHAR(30), track_id CHAR(30), PRIMARY KEY (user_id, track_id), FOREIGN KEY (user_id) REFERENCES USERS, FOREIGN KEY (track_id) REFERENCES TRACKS); CREATE TABLE FOLLOW( user_id CHAR(30), artist_id CHAR(30), follow_date datetime, PRIMARY KEY (user_id, artist_id) FOREIGN KEY (user_id) REFERENCES USERS, FOREIGN KEY (artist_id) REFERENCES ARTISTS); According to the six table, write a single SQL…

