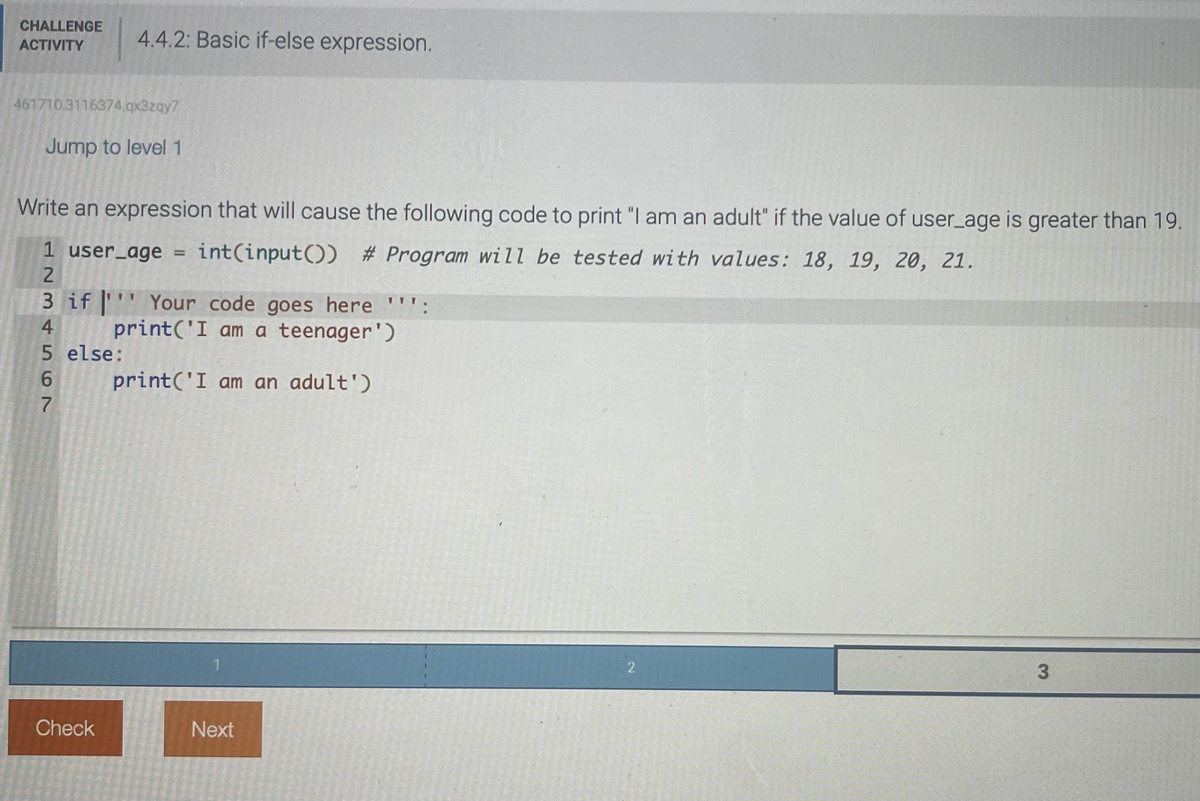
CHALLENGE ACTIVITY 4.4.2: Basic if-else expression. 461710.3116374.qx3zqy7 Jump to level 1 Write an expression that will cause the following code to print "I am an adult" if the value of user_age is greater than 19. 1 user_age = int(input()) # Program will be tested with values: 18, 19, 20, 21. 2 3 if Your code goes here "'': 4 print('I am a teenager') 5 else: 6 print('I am an adult') 7 11
Q: Firewalls are an important part of keeping networks safe, therefore it's crucial to explain what…
A: A firewall is a network security system that monitors and controls the incoming and outgoing network…
Q: Algorithm 6.1 Flocking algorithm. Flock(B,A) in: set B of boids in a flock; set A of avoidable…
A: Introduction: - The Flocking algorithm is a simulation of the collective behavior of birds, where a…
Q: Which two technologies account for the bulk of wireless network deployments?
A: Wireless network: It is a method by which homes, telecommunications networks and business…
Q: prove the follwing by using Boolean Identites 1. (( X Y ) Z ) + ( Y Z ) = YZ 2. X' Y = X' Y + X'…
A: Given Data:- 1. (( X Y ) Z ) + ( Y Z ) = YZ 2. X' Y = X' Y + X' Y Z prove the above following by…
Q: How is a still image translated into discrete data? How precisely is the source code for a video…
A: 1. A Database Management system (or DBMS). 2. It is essentially nothing more than a computer-based…
Q: How exactly does the routing function? Provide some context on distance vector routing.
A: Distance-Vector Routing Algorithm: With the Distance-Vector Routing Algorithm, each router…
Q: A pointer can be initialized to an address. Choose all the answers that apply. a floating value.…
A: 1) A pointer in computer programming can be initialized to a memory address that stores a specific…
Q: What are the two types of services that may be received via the usage of Internet applications? What…
A: Describe two distinct categories of services that may be accessed by Internet users via the use of…
Q: First, evaluate the similarities and differences between the threats and attacks in information…
A: INFORMATION SECURITY 1. Contrast assaults and threats. A threat is a prospective security breach…
Q: Examples of programming environments and user contexts are taught.
A: Programming settings: A particular kind of programming environment is environment programming.…
Q: Does a hash table of size m always have the same number of linked lists? I've been trying to…
A: In order to distinguish one item from another that may look quite similar, hashing is employed. Hash…
Q: The following is a list of resources accessible via cloud computing, followed by an explanation of…
A: Cloud Technology It is defined as a distributed network for the concurrent sharing and execution of…
Q: be stopped and started? Is it necessary to restart it after changing configuration files, or may…
A: Depending on what you want to achieve, there are several different ways to stop and start Asterisk.…
Q: What are your opinions in light of the parallels between network sniffing and wiretapping? Why are…
A: Discussion of similarities between network sniffing and wiretapping includes the following: Sniffing…
Q: In general, descriptive models are preferable than prescriptive models, but which one is superior?
A: Given this data, we need to determine if descriptive or prescriptive models are more appropriate…
Q: An in-depth examination of how the various security technologies operate
A: Answer : Various security technologies are : 1) Firewalls : It is a device which is used to filter…
Q: The Rational Unified model and the Classical Waterfall model will be contrasted and compared in this…
A: Answer: We need to do the compare and contrast between the Rational Unified model and the Classical…
Q: What is the role of the Transport layer in the OSI model and what are its key functions?
A: Introduction : The transport layer is a layer of the Internet Protocol Suite that is responsible for…
Q: What distinguishes computer and telephone networks from the countless other kinds of networks now on…
A: Definition: The telephone network, which links two or more people to make phone calls and utilise…
Q: There are two methods for terminating processes and escaping deadlocks:
A: The answer for the above question is given in the following step for your reference.
Q: Whoever has the capacity to inspire and excite technical specialists to perform at their highest…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: tween possessing the copyri
A: Introduction: Two further queries pertain especially to licencing and copyright.I get the impression…
Q: includes iterative searches as well as one-time searches, authoritative and root servers, and DNS…
A: DNS is sometimes referred to as the yellow pages of the internet. When you wanted to discover the…
Q: What are some of the goals the LOCAL directive seeks to accomplish?
A: The LOCAL directive in programming is used to declare local variables within a function or…
Q: We believe it would be advantageous to add a level to Flynn's taxonomy. What distinguishes high-end…
A: Solution: Flynn's well-established taxonomy takes into consideration two different factors. The…
Q: The Internet's transport layer ensures that data may be sent from one network to another. This layer…
A: Introduction: The fourth layer of the OSI model of network connections is the transport layer. As…
Q: What sorts of Tor network limitations exist?
A: Tor network The Tor network (short for The Onion Router) is a free, open-source software and…
Q: The following issues arise while utilizing a disjointed information system, and are experienced by…
A: Introduction: Major computer concerns include losses and malfunctions, which result in inflated…
Q: Define a file manager. Define the Windows Explorer program. Include areas for storing items and…
A: As per our guidelines we are supposed to answer only ? 3 sub- parts ( if there are multiple sub-…
Q: How can a Cyber Security educator benefit the world at large?
A: A cyber security educator can benefit the world by raising awareness and providing education on how…
Q: ompare and contrast the Waterfall methodology with the more modern Rational Unified approach
A: Waterfall methodology is a traditional, sequential model of software development that is structured…
Q: How are system models defined and what do they entail? What elements must be considered while…
A: System models are defined as representations of a system that can be used to study the system's…
Q: There are a lot of parallels between the iterative-and-incremental approach and the waterfall…
A: Using a Waterfall Model:- The waterfall model is a common and straightforward approach to software…
Q: Describe the complications in wireless networking that exist when one station is invisible and…
A: The term "wireless networking" refers to a kind of network in which the transfer of data from one…
Q: how implementing network and IT risk rules may be crucial in keeping staff members from disregarding…
A: Introduction: Implementing network and IT risk rules is an important aspect of ensuring that staff…
Q: Concerning normalization, database administrators must be vigilant. It's helpful whether you're a…
A: The answer is given below step.
Q: Write a C program that implements a hash table with chaining for collision resolution. The program…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: What information must an instruction set contain? Provide a summary of the SRC.
A: Details in the instruction set The component of the computer that is most related to programming is…
Q: Provide a description of the many ways that may be used while designing applications in an ordered,…
A: The reuse of software components is encouraged by object-oriented methodology (OOM) in the creation…
Q: Explain what you mean by the term "application security."
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Make a clear delineation between users and their assigned functions in the context of computer…
A: Given: When it comes to the computer's access control security, what are the key distinctions…
Q: It is possible to describe a challenge-response authentication system in your own words. What…
A: Authentication procedures known as challenge-response are used in computer security to safeguard…
Q: Discover how technology and data may be used to solve the problems faced by data systems.
A: Introduction: - Technology and data have become integral components in various platform have…
Q: What is the difference between MPLS (Multiprotocol Label Switching) and VPN (Virtual Private…
A: HI THEREI AM ADDING ASNWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: What are some best practices for firewall configuration, and why are they essential?
A: When operating a firewall, it is advised that you follow the practises outlined in the following…
Q: These factors should be taken into account while designing a fully working open hash table:
A: The hash table A hash table in hashing represents data in array form, with each element containing…
Q: 1. Name the stages of the software development lifecycle (SDLC) - Give a short description for each…
A: Introduction:- SDLC(System development life cycle) is a systematic and user friendly technique or…
Q: What are a few of the most essential considerations when it comes to data backup and recovery?
A: The introductory phrase: Throughout the data backup and recovery process, planning is conducted to…
Q: lectures we only had one root and everywhere i look on the internet there is at least 2 values in…
A: Summary A (2,3) tree is a type of B-tree where each node can have 2 or 3 children and each internal…
Q: When it comes to BC/DR preparation, why is testing so important? In how many ways can one be tested?
A: BC/DR Preparation: Business continuity and disaster preparation aid an organization's ability to…
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

- Write a VB program to ask user to assign a value to “i” to find the answer for the following three cases. 1. Case 1. Assume i = 1 and HowMuch = 0IF i < 5 THENHowMuch = HowMuch + 1ELSEIF i = 5 THENHowMuch = HowMuch - 5ELSEHowMuch = HowMuch + 3END IFDISPLAY HowMuch2. Case 2. Assume i = 5 and HowMuch = 0IF i < 5 THENHowMuch = HowMuch + 1ELSEIF i = 5 THENHowMuch = HowMuch - 5ELSEHowMuch = HowMuch + 3END IFDISPLAY HowMuch3. Case 3. Assume i = 6 and HowMuch = 0IF i < 5 THENHowMuch = HowMuch + 1ELSEIF i = 5 THENHowMuch = HowMuch - 5ELSEHowMuch = HowMuch + 3END IFDISPLAY HowMuch2.2.2: If-else statements. 422784.2543518.qx3zqy7 Jump to level 1 Write multiple if statements: If carYear is before 1967, print "Probably has few safety features." (without quotes). If after 1969, print "Probably has seat belts.". If after 1990, print "Probably has anti-lock brakes.". If after 2000, print "Probably has airbags.". End each phrase with period and newline. Ex: carYear = 1995 prints: Probably has seat belts. Probably has anti-lock brakes.4. A) What will be the value of x after the following code is executed? int x, y = 4, z = 6; x = (y++) * (++z); B) Suppose a = 1. What is the value of a after the following code executes? Show the procedure to reach your answer if(a > 0) { switch(a) { case 1: a = a + 3; case 3: a++; case 6: a = a * 2; break; case 8: a--; break; default a++; } else a = a + 2; C) What would be the value of x after the following statements were executed? int x = 10; switch (x) { case 10: x += 15; case 12: x -= 5; break; default: x *= 3; }
- Please Help Solve, Thank You! 3.25.2: Basic if-else. Write an if-else statement for the following: If userTickets is not equal to 6, execute awardPoints = 10. Else, execute awardPoints = userTickets. Ex: If userTickets is 14, then awardPoints = 10. import java.util.Scanner; public class TicketCounter { public static void main (String [] args) { int awardPoints; int userTickets; Scanner scnr = new Scanner(System.in); userTickets = scnr.nextInt(); // Program will be tested with values: 5, 6, 7, 8. /* Your code goes here */ System.out.println(awardPoints); }}Write a program that calculates and displays a person’s body mass index (BMI). A person’s BMI is calculated with the following formula: BMI = weight × 703/height2 where weight is measured in pounds and height is measured in inches. The program should display a welcome message, and ask for the weight (in pounds) and the height (in inches) from the user. The program should display a message indicating whether the person has optimal weight, is underweight, or is overweight. A sedentary person’s weight is considered to be optimal if his or her BMI is between 18.5 and 25 (including 18.5 and 25). If the BMI is less than 18.5, the person is considered to be underweight. If the BMI value is greater than 25, the person is considered to be overweight.Develop a program that allows the user to enter a start value of 1 to 4, a stop value of 5 to 12 and a multiplier of 2 to 8. The program must display a multiplication table with results using these values. For example, if the user enters a start value of 3, a stop value of 7 and a multiplier value of 3, the table should be displayed as follows: Multiplication Table 3 x 3 = 9 3 x 4 = 12 3 x 5 = 15 3 x 6 = 18 3 x 7 = 21 additionally Each multiplication problem must be displayed with a problem number. The program must prompt the user to enter an answer to each of the multiplication problems. The correct answer should be displayed after the user enters an answer. A message should be displayed informing the user that the answer entered was correct or incorrect followed by an appropriate motivating comment. A running record of the number of correct and incorrect responses must be kept. After all the problems have been presented the user must be informed of his/her performance; number of…
- Java code Ever wondered how change is disbursed to customers in certain stores? In country X the following notes exists 200,100,50,20,10 and following coins: 5, 1, 50c, 10c, 5c. For the sake of this exercises let us only consider change below 50 see below example: Sample run 1: Enter item name: Apples Enter QTY of Apples: 2 Enter price per item N$: 3.25 Amount tendered N$: 50 Your change is: N$ 43.50 Disbursed as follows: 2 x N$20; 0 x N$10; 0 x N$5; 3 x N$1; 1 x 50c; 0 x 10c; 0 x 5c [Hint: make use of % and / operators to determine the values needed]Write an application that prompts the user for two integers and then prompts the user to enter an option as follows: 1 to add the two integers, 2 to subtract the second integer from the first, 3 to multiply the integers, and 4 to divide the first integer by the second. Display an error message if the user enters an option other than 1 through 4 or if the user chooses the divide option but enters 0 for the second integer. Otherwise, display the results of the arithmetic.In java write a program that takes four int command-line arguments w, x, y, z,. define a boolean variable whose value is true if the four values are either in strictly acending order (w<x<y<z) or strictly descending order (w>x>y>z), and false otherwise, then display the boolean variable value. Note: Do not use if statements on the program Note: Assume that the inputs will always be integers
- Write a program using functions and the switch structure to determine the healthiest food store. Build a menu, exactly, like the following menu: Which fast food restaurant provides the healthiest food: 1. McDonalds 2. Jack in the Box 3. Chick-fil-A 4. Exit The user inputs a number 1 or 2 or 3 or 4. If the user types a 1 output to the monitor is "That's right, Mac y Dee! If the user types a 2 output to the monitor is "Yes, the guy with the big round head." If the user types a 3 output to the monitor is "The best chicken in town." If the user types a 4 output to the monitor is "Thank you for choosing!" c++ PROBLEM: I need to make an ATM program that allows the user to check his or her balance after entering his or her correct PIN and the maintaining balance is Php 8000. A message is shown when the balance is below PHP 8,000 for withdrawal and its remaining balance. Another message is shown when the balance is PHP 8,000 and above for deposit and its updated balance. The code: import random import sys class ATM(): def __init__(self, name, account_number, balance = 0): self.name = name self.account_number = account_number self.balance = balance def account_detail(self): print("\n----------ACCOUNT DETAIL----------") print(f"Account Holder: {self.name.upper()}") print(f"Account Number: {self.account_number}") print(f"Available balance: Nu.{self.balance}\n") def deposit(self, amount): self.amount = amount self.balance = self.balance + self.amount print("Current account…java Write a program that prompts the user to enter a point (x, y) and checks whether the point is within the rectangle centered at (0, 0) with width 10 and height 5. For example, (2, 2) is inside the rectangle and (6, 4) is outside the rectangle, as shown in the Figure. (Hint: A point is in the rectangle if its horizontal distance to (0, 0) is less than or equal to 10 / 2 and its vertical distance to (0, 0) is less than or equal to 5 / 2.) Here are sample runs of the program: Sample 1: Enter a point with two coordinates: 2 2 Point (2.0, 2.0) is in the rectangle Sample 2: Enter a point with two coordinates: 6 4 Point (6.0, 4.0) is not in the rectangle Analysis: (Describe the problem including input and output in your own words.) Design: (Describe the major steps for solving the problem.) Coding: (Go over your code step by step) Testing: (Describe how you test this program). In other words run your code with sample outputs.



