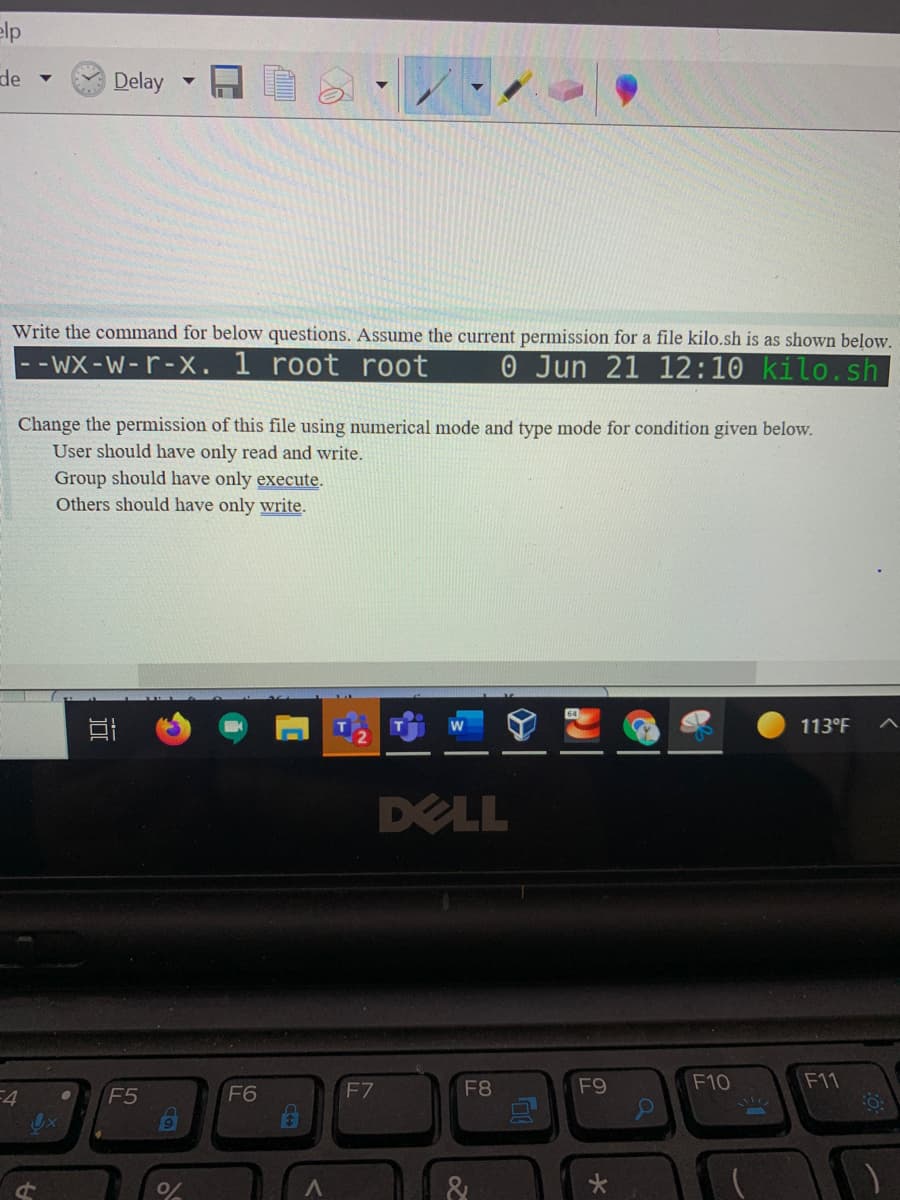
Change the permission of this file using numerical mode and type mode for condition given below. User should have only read and write. Group should have only execute. Others should have only write.
Q: The information of all students taking the programming course is kept in a random access file with…
A: Answer is given below .
Q: Local functions look just like ordinary functions, but they are only accessible to the other…
A: Let us see the answer below,
Q: State which is true and which is false. If false, explain why ? " Searching all records in a…
A: State which is true and which is false. If false, explain why ? " Searching all records in a…
Q: A temperature file consists of five records, each containing a temperature in degrees Fahrenheit. A…
A: Step-1: Start the program. Step-2: Open an input temperature file. Step-3: Print the column heading…
Q: When we use this command in a batch file, the user must pick from the available options because…
A: IF ELSE command in batch file is used to check condition i.e., IF condition is true then certain…
Q: Write a program that generates student records in a database file. Your program should be able to…
A: %sql def val db = { val sn = student_name; val si = student_id; } get 10 * db print(db)
Q: -Suppose that x=date of your birth and y is month of your birth. Use Matlab and calculate the…
A: Input : Value of x Value of y Output : Value of given expressions
Q: a. Write a python program that writes data to a file. The data consists of a series of records, each…
A: a) Create a file say 'file1.txt' to which program writes data. Python program that writes data to…
Q: q11) Choose the correct syntax to use the writelines() method with file object f. a. f.writelines()…
A: We need to choose correct option for the syntax to use the writelines() method with the file object…
Q: Hello, need the code for the below! Thanks. I am badly stuck with this one. This is for python.…
A: The python code and its explanation are given below: - Explanation: - Creating a text file txt that…
Q: In the input file, transfers are indicated by listing two account handles and an amount, like lines…
A: In this question, the coding language is not specified then we are doing this question in the CPP…
Q: Which file open flag forces all output to occur at the end of the file?
A: Given: Which file open flag forces all output to occur at the end of the file?
Q: a. Write a python program that writes data to a file. The data consists of a series of records, each…
A: the answer for above question is :
Q: Takes(studentid, courseCode, mark) Course(courseCode, title, credits,deptno) Student(studentld,…
A:
Q: Write a script file that enter and display the scores data in two exams as a table shown below:
A: The code for the script file using Matlab's table() method has been given in the next step.
Q: Exercise 1: Use vi to create a file with name "table1.txt" with following content. fruit amount…
A:
Q: If you don't know where the update.txt file is located on your computer, it's a good idea to print a…
A: Finding the File's Location: When you don't know where a file is located but know its name, you may…
Q: a python program that writes data to a file. The data consists of a series of records, each with…
A: chegg.py # Prompt user to enter the number of records to enter n = int(input("Enter the number of…
Q: You should use the Exit method to close a sequential access file as soon as you finished using the…
A: The Exit statement transfers the control from a procedure or a block immediately to the statement…
Q: Thank you, but the renaming needs to read from a list in a text file called (filenames.txt) . I…
A: Here's the solution:
Q: ___________ and _________ are two different ways to access data stored in a file.a. Sequence access,…
A: Given data is shown below: ___________ and _________ are two different ways to access data stored in…
Q: Extension of the program below with the following specifications Array of records with file I/O is…
A: Programming instructions: Create an array of structures. Open the file. Store the file data into…
Q: From most restrictive to least restrictive, the access modifiers are:
A: Access modifiers are used to maintain the scope of variables
Q: The information of all students taking the programming course is kept in a random access file with…
A: Actually, c is a easiest programming language. It is a high level language.
Q: If you don't know where the update.txt file is on your machine, you should print a duplicate.
A: Intro For Finding File Location: When you do not know the location of a file but know its name, you…
Q: Write the single line that will intercept EXIT then delete the file named /tmp/tmpfile. Be sure that…
A: Command to remove the file from the directory without prompt the user for confirmation
Q: The file that provides non-key ordering features is called as the, and it is contained in the
A: Introduction: The way files are named, saved, and retrieved from a storage medium is defined by a…
Q: It's hard to tell the difference between back-ups that are done in a certain order and ones that are…
A: Given: The sequential file approach consists of a set of data and a set of physical-restricted…
Q: use only include and fstream headerfiles and do according to question kindly.
A: Required:
Q: Create an extsort function to sort a list of files by extension?
A: Code in Python To sort A files: import os def extsort(files): return sorted(files,key=lambda x:…
Q: This function is used to create an user accounts dictionary and another login dictionary. The given…
A: Please find the complete code below: Commnet if you need any help # function valid to check for…
Q: Q1)write M-file to calculate integration of f(x) from xo-value to x₁=value? where, one can use…
A: Code: syms x str=input('Enter an equation in x: ','s'); f=str2sym(str); x0=input('Lower…
Q: Fill in the blank: Q. ________________ is used to change file owner and group information in redhat
A: chown command is used to change the owner and/or group for the file. Syntax: chown, followed by the…
Q: The file name is file1.txt How would you inclue this?
A: The answer is given below.
Q: Write program to generate digital signature using DSA private key for text “This is final exam of…
A: Calculation of Digital Signature Digital Signatures are often calculated using elliptical curve…
Q: Deadlock on File Requests happens if jobs are allowed to request and hold files for the duration of…
A: This question comes from Operating System which is a paper of computer science. Let's discuss it in…
Q: a. Write a python program that writes data to a file. The data consists of a series of records, each…
A: The Answer is
Q: The information of all students taking the programming course is kept in a random access file with…
A:
Q: WAP to read 4 student objects and write them into a file, then print total number of student number…
A: The code is written below: #include<iostream> #include<fstream> using namespace std;…
Q: Read all rows from a file. Test whether that row is palindrome or not. Write validation (true or…
A: You haven't asked in the specific programming language so I am answering in the python programming…
Q: Construct a batch file as "password1.bat" to check whether the password "5555" is valid or not. And…
A: @echo offREM: print new lineecho. echo -----------------------------------------echo *** Test…
Q: Using the python code below. Identify the Variabale, Conditional Statement,Operators,Loops and…
A: We need to identify the Variabale, Conditional Statement,Operators,Loops and Functions used in the…
Q: The information of all students taking the programming course is kept in a random access file with…
A: Code : #include <stdio.h>#include<string.h>struct student{int number;float midterm;char…
Q: The actions below are necessary if you delete a file accidently and desire to recover it.
A: Given: The steps to recover a deleted file on Windows 10 are shown below as an example.
Q: Which file open flag causes all output to take place at the end of the file?
A: Append Flag
Q: Create a batch file to check the following two numbers are equal or not using GOTO statement.
A: @echo offRem input bot numbers from userset /p num1="Enter Number1: "set /p num2="Enter Number2:…
Q: sequence access files?
A: Sequential Access files – It is the simplest access method. Information in the file is processed in…
Step by step
Solved in 2 steps

- Create a file named "YournameTask03.txt". Change its permission using absolute(numeric) mode. so that it has ONLY executed permission of owner and group ONLY. Solve this task by using shell scriptingAfter typing the ls –F command, you see the following line in the output:-rw-r-xr- - 1 user1 root 0 Apr 29 15:40 file1What does this mean?a. User1 has read and write, members of the root group have read and execute, and allothers have read permissions to the file.b. Members of the root group have read and write, user1 has read and execute, and allothers have read permissions to the file.c. All users have read and write, members of the root group have read and execute,and user1 has read permissions to the file.d. User1 has read and write, all others have read and execute, and members of theroot group have read permissions to the file.BELOW MCQ GIVEN ANSWER CAN BE MORE THAN ONE OPTION. PLEASE PROVIDE CORRECT ANSWERS. ------------------- Which of the following statements correctly describe execution of the highlighted command? $qrep ^root /etc/passwd root:qqed262w7tvxq:0:0:0000~admin(0000), ,258, :/:/bin/tcsh $su A) the current directory will be changed to '/' B) the environment will be the same as though root (super user ) had logged onto the system. C) the user will be prompted for a password and then /bin/tcsh will be executed . D) the system will execute /bin/sh . the current directory will not be changed. E) the user will be prompted for a password and then /bin/sh will be executed.
- After typing the ls –F command, you see the following line in the output: -rw-r-xr- - 1 user1 root 0 Apr 29 15:40 file1What does this mean?* a. User1 has read and write, members of the root group have read and execute, and all others have read permissions to the file. b. Members of the root group have read and write, user1 has read and execute, and all others have read permissions to the file. c. All users have read and write, members of the root group have read and execute, and user1 has read permissions to the file. d. User1 has read and write, all others have read and execute, and members of the root group have read permissions to the file.السؤال What does the following command do? $ chmod ugo -w file01.txt الاجابات remove write permission to users, group and others remove write permission to the user (owner) only assign write permission to group and others assign write permission to users, group and othersunix Using one or more of the wild card charaters *, ? and range (also called set) like [abx] and [1-3] in the file pathname, issue appropriate command(s) to do the following. Note: You must show the use of the above three wild card characters individually in one or more commands for part (6) to 11) below. list all files that begin with section using wildcard character List only the files section1, section2, and section3 using wildcard character List the intro files only using a wild card character List the files section1, section3, ref1 and ref3 using set/range Change the permission to all files that begin with section to rwxrw-rw-. Display the file attributes to show that file permissions changed Change working directory to the parent directory using relative path Display pathname of working directory Issue command to delete the directory you created for Q2 without using –r option Using echo command answer whether you are able to delete a non-empty directory Change working…
- Which of the following commands will change the user ownership and group ownershipof file1 to user1 and root, respectively?a. chown user1:root file1b. chown user1 : root file1c. This cannot be done because user and group ownership properties of a file must bemodified separately.d. chown root:user1file1e. chown root : user1file1Write commands to accomplish the following (use the manual or info pages if necessary):a. Create a user with a login name of bsmith, a UID of 733, a GECOS field entry of“accounting manager,” and a password of Gxj234b. Delete the user jdoe, but leave the home directory intactc. Change the properties of the existing user wjones such that the user has a newcomment field of “shipping” and an account expiry of March 23, 2022d. Lock the account of wjenkinse. Change the password of bsmith to We34Rtf. Change the properties of the existing user tbanks such that the user is a member ofthe managers group and has a login name of artbanksg. Create a user with the same UID and primary group as root and a login name ofwjonesh. Create a new user with a login name of jdoe who has a password of he789R andno home directoryi. Change the primary group of the user wsmith to rootj. Add the users tbanks and jdoe to the group acctgPlease help write a command that uses the output of git log to find all the unique contributors, case-insensitively, to the repository. A “contributor” should be all of the text that appears after “ Author: ” in the git log . Authors with the same name but different emails should be considered distinct. The output should be written to a file called contributors.txt: (will leave a like)
- Create a batch file Your batch file should include all required comments for creation and author information. Your batch file must include but is not limited to these commands: ECHO CD NET ICACLS MKDIR COPY Comment each line of your batch file as you create it. Don’t forget to include creation and author information. Create a batch file F:\bat that uses all the required commands and completes the following: Creates a folder named Scripts on the Root of C Add a local user named Aisha Bruce with the username ABruce and the password student Creates a directory in the “E:\CompanyInc\Management” folder named “ABruce_Files” Creates an ACE for “ABruce” to the “ABruce_Files” folder with these explicit permissions: Full Control Re-establishes inheritance to sub-folders and files Copies the application cmd.exe from the C:\Windows\System32 folder to the “ABruce_Files” folder Addes ABruce to your Management Group created in assignment 3 Produces an ICACLS Report for “ABruce_Files”…Write the command taht will locate all files that have the suffix/extension of ".py". For each file that is located, the command should append the suffix/extension of ".backup" to the file. So, if a file had the name "one.py", its new name would be"one.py.backup".Write the answer of the following commands below: a. Write a command to append the text “This is Assessment exam” into demo.txt file with save and exit. b. Write a command to print number of lines that match the word EEE in a file named is HCT. c. Write a command to display all the files of /Demo directory, whose name is ending with a character in between a to m.…





