Character Description \w soann \W \d \D \s \S Matches any character. Any word character. A word character includes upper and lowercase letters, any digit, or the underscore character. Any nonword character. Any digit. Any nondigit. Any whitespace. Any nonwhitespace.
Q: /* Create a robust Python function that thoroughly analyzes a given dictionary representing a…
A: Initialize an overview string.If 'name' exists in the dictionary, add the name to the overview.If…
Q: Question 4: Find the cut vertices, cut edges, vertex connectivity and edge connectivity. g A b 40 g
A: Cut Vertices:A vertex whose removal increases the number of connected components in the graph is…
Q: Why are I/O modules needed in a computer system? Give two reasons.
A: I/O modules play a pivotal role in bridging the internal processing components of a computer, such…
Q: What tips can be utilized to identify security vulnerabilities related to strings in C++?
A: The objective of this question is to understand the various ways to identify security…
Q: Use FCFS, SPN, SRT, RR (q=1), HRRN, and feedback (q=2) scheduling algorithms to complete the…
A: Scheduling algorithms play a crucial role in operating systems to manage the execution of processes…
Q: The below program uses the "+" operator to concatenate the two strings together but I would like to…
A: In this question a C++ program is given that concatenates two strings using + operator. The given…
Q: I need to write an algorithm pseudocode that sorts a list of n elements in non-increasing order by…
A: The pseudocode explains a non-increasing sort algorithm that finds the largest and smallest entries…
Q: Explain how data consistency and durability are maintained in cloud storage.
A: Data consistency in distributed storage is urgent to guarantee that different duplicates of similar…
Q: Question 1: Determine whether the graphs shown have directed or undirected edges, whether it has…
A: An ordered pair of vertices in a directed graph is called a directed edge, sometimes referred to as…
Q: Problem 6: Disjoint sets. Let operations Union() and Find-Set() be efficient: that means sets are…
A: Imaginе a bustling archipеlago, еach island a sеparatе еntity, its sеcrеts hiddеn within. Today, wе…
Q: Explain the role of CRM in fostering customer advocacy and referral programs.
A: In the dynamic landscape of customer-centric business strategies, the role of Customer Relationship…
Q: You are given arr, an array of integers, n, the size of the array, and a number k. The arguments are…
A: In this question we have to write a C++ code for finding the max and min sums for the given numbers…
Q: 3. 4. 5. Write T for True and F for False. MS Excel is a popular spreadsheet software. The Edit mode…
A: Excel which it is a spreadsheet application developed by Microsoft. It is an easily accessible tool…
Q: Discuss the challenges associated with scaling applications in a cloud environment.
A: Delivering a range of computing services, such as processing power, storage, databases, networking,…
Q: (IN JAVA) In this task, a binomial heap should be implemented. A binomial heap is implemented by an…
A: The task mentioned in the question is to write a Java code for the implementation of binomial heap.…
Q: So my teacher gave HW and I need help matching the answers to the right descriptions.......
A: The objective of the question is to match the correct terms with their respective descriptions in…
Q: a) Produce a pseudo code design for a recursive algorithm to solve this problem. (b) Draw a…
A: a)Produce a pseudo code design for a recursive algo to solve this problemfunction…
Q: Answer in java language Problem Description: The Example University wanted to reduce wrong student…
A: Initialize two arrays for valid and invalid numbers.Initialize indices for valid and invalid…
Q: What is the purpose of the page table?
A: The concept of a page table is fundamental in the realm of computer memory management, particularly…
Q: propvide detail solution with proper explanation and step by step answer. prove by cases that : |…
A: In this case x is positive and y is also positive. Which implies |x+y| is also positive.Similarly…
Q: The code should print quadruples (x,y,z,w) such that x^2 + y^2 + z^2 = w^2. The outputs given do not…
A: This function, pythagorean_quadruples, uses the properties of Pythagorean quadruples to generate…
Q: QUESTION 16 (a) The Quine-McCluskey method of reduction is good for cases where the number of input…
A: A methodical technique for reducing Boolean functions to their minimum form is the Quine-McCluskey…
Q: You are given two arrays A and B of size n and m respectively. Compute the maximum length of a…
A: 1) Dynamic programming can be used to find the maximum length of a common subarray between two…
Q: Discuss how virtualization enhances resource utilization in the cloud.
A: Virtualization is a technology in cloud computing that plays a role in improving the use of…
Q: Baby Steps toward Scrum: How BabyCenter.com Made the Cultural Transition to Agile Software…
A: Scrum is an agile framework for managing and organizing paintings, specifically in software program…
Q: (3) The Rosi Brotherhood ● a. What cipher is being used? b. What is the decrypted message? . 出門
A: Here, the task mentioned in the question is to identify the cipher used in the question and to…
Q: Write 2 body paragraphs on how you can prevent yourself from cyber crime
A: The term "cybercrime" refers to many offenses that are perpetrated via computer systems or the…
Q: Discuss the challenges associated with achieving scalability and elasticity.
A: Exploring the intricacies of scalable and elastic computing systems, this inquiry delves into the…
Q: I have created the following code in java, replit, that's a guessing game. Attached are the classes…
A: The task involves modifying a Java-based guessing game to track player results in a CSV file using…
Q: Discuss the future possibilities of incorporating virtual reality (VR) and augmented reality (AR) in…
A: Virtual Reality (VR) and Augmented Reality (AR) represent cutting-edge technologies that have…
Q: Define and compare Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as…
A: In the world of cloud computing, Infrastructure as a Service (IaaS) Platform as a Service (PaaS) and…
Q: Explain the concept of cloud-based CRM systems and their advantages for businesses.
A: Cloud-based CRM systems revolutionize customer relationship management by utilizing…
Q: Question 1: Answer the following questions. The first mechanical calculating machine was made by…
A: A programming language is a formal system made up of a collection of symbols and rules that tells a…
Q: Morse Code Python Part 1: Variable setup and prompt for input • To create the Morse…
A: This Python script translates user-input messages into Morse code, representing each character with…
Q: Explain how the program achieves its desired outcomes
A: The effectiveness of any program lies in its ability to achieve desired outcomes. This essay will…
Q: vector mystery (string word) { vector result; if (word. length() shorter_mystery = mystery…
A: The given function seems to manipulate a string in a particular way, but it's not immediately clear…
Q: Discuss the advantages of using Content Delivery Networks (CDNs) in cloud environments.
A: Businesses are increasingly depending on Content distribution Networks (CDNs) to improve the…
Q: Write C18 program to send a byte of data serially to RC2 pin from PORTB. (MSB should go last)
A: The objective of the question is to write a C18 program that sends a byte of data serially from…
Q: 1)Discusss the security aspects of gmail system
A: The objective of this question is to understand the various security measures that Gmail, a popular…
Q: Highlight the considerations when choosing a deployment model.
A: Choosing the deployment model is a decision, in computer science. It decides how a software…
Q: Write a C++ program that does the following you are given an arrays of galaxy names string Star[12]…
A: In this question we have to write a C++ code for the given arrays of galaxy names to fullfill the…
Q: a) Develop a function to load the recorded data into a matrix (with 2 columns of data namely the…
A: The subject involves processing Galvanic Skin Response (GSR) data, which measures the electrical…
Q: What would the required pseudocode look like for the below C++ program? Please and thank you…
A: The objective of the question is to convert the given C++ program into pseudocode. The C++ program…
Q: Question: A data of the size 3660 bytes, excluding 24 bytes of header, arrives at router R1. Now R1…
A: Data fragmentation is the process of breaking down a large chunk of information into smaller,…
Q: (Drawing and code) 1. Show the BST after deleting 15 from the following BST. You must show the tree…
A: As per the given information, we need to show the BST after inserting 60,15,100,57,67,107,49,64 into…
Q: write a function PythQuad(n) in python that generates a list of pythagorean quadruples (x,y,z,w)…
A: Initialize an empty list quadruples to store the Pythagorean quadruples.Iterate over values of m…
Q: Problem 2: Binary search tree and min heap. (i) Write down an algorithm, which in time O(n),…
A: NOTE: Programming language is not mentioned. Answering questions in C++ language.The C++ code…
Q: Explain the essential characteristics of cloud computing.
A: Cloud computing is an approach that provides users with a range of computing services over the…
Q: Consider a hypothetical computer system that uses a 16-bit architecture. The system has an…
A: We're entering a fictitious computer environment with a 16-bit setup. First, we will convert the…
Q: f(t) = sin(wt + 4) using the data below. t f(t) 0.0 0.53 0.1 0.73 0.2 0.91 0.5 0.92 0.6 0.83 0.7…
A: The correct solution for the above mentioned question is given in the next steps for your reference
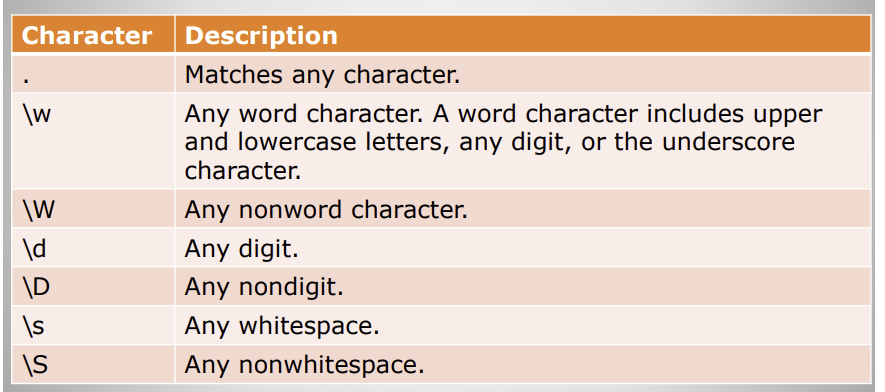
So could someone provide an example for each listed?
Unlock instant AI solutions
Tap the button
to generate a solution
Click the button to generate
a solution
- A palindrome is a word or phrase that is identical when you read from forward or backward, such as the words “racecar” and “madam.” A standard palindrome is similar to a perfect palindrome, except that spaces and punctuation are ignored in a standard palindrome. For example, “Madam, I’m Adam” is a standard palindrome because the characters are identical forward or backward, provided you remove the spaces and punctuation marks. Write a PHP script that checks words or phrases stored in two separate string variables to determine if they are a perfect palindrome. In addition, see if you can modify the program to check for standard palindromes. create a web page with a text field and “Reset” and “Submit” buttons. When a user clicks on the submit button, show the standard and perfect palindromes of the string that was entered in the text field on the same page. Create a separate Index.html and php fileEach of the following files in the Chapter.06 folder of your downloadable student files has syntax and/or logical errors. In each case, determine the problem, and fix the program. After you correct the errors, save each file using the same filename preceded with Fixed. For example, DebugSix01.cs will become FixedDebugSix01.cs. a. DebugSix01.cs b. DebugSix02.cs c. DebugSix03.cs d. DebugSix04.csEach of the following files in the Chapter.01 folder of your downloadable student files has syntax and/or logical errors. In each case, determine the problem and fix the program. After you correct the errors, save each file using the same filename preceded with Fixed. For example, DebugOne1.cs will become FixedDebugOne1 .cs. a. DebugOne1.cs b. DebugOne2.cs c. DebugOne3.cs d. DebugOne4.cs
- Each of the following files in the Chapter.05 folder of your downloadable student files has syntax and/or logical errors. In each case, determine the problem, and fix the program. After you correct the errors, save each file using the same filename preceded with Fixed. For example, save DebugFive1.cs as FixedDebugFive1 .cs. a. DebugFive1.cs b. DebugFive2.cs c. DebugFive3.cs d. DebugFive4.cs***Please write code suitable for Myprogramminglab below: If you have downloaded the source code from this book's companion web site, youwill find the following files in the Chapter 07 folder:• GirlNames.txt--This file contains a list of the 200 most popular names given togirls born in the United States from the year 2000 through 2009.• BoyNames.txt--This file contains a list of the 200 most popular names given toboys born in the United States from the year 2000 through 2009.Write a program that reads the contents of the two files into two separatelists, allows a user to input either a girl's name, a boy's name, orboth, then tells the user whether the name(s) was/were popular between 2000 and2009.First, the program should prompt the user to choose a girl's name, a boy's name,or both by entering either 'girl', 'boy', or 'both.'Once they have chosen, they should be able to input a name. If the name wasa popular name, like Jacob or Sophia, the program should print "Jacob was apopular…Please help with the below C# Windows Forms code, to get the Luhn method to work to validate the SSN / Swedish person number. Please see the bold below I have errors at the "return (sum % 10) == 0;" below. Please send back the answer in whole with the changes in the code. Thanks! using System; using System.CodeDom.Compiler; using System.Windows.Forms; namespace WindowsFormsApp1_uppgift_3 { class Person { public string firstName { get; set; } public string lastName { get; set; } public string securityNumber { get; set; } public Person(string firstName, string lastName, string securityNumber) { this.firstName = firstName; this.lastName = lastName; this.securityNumber = securityNumber; } public string Checking() { try { if (securityNumber.Length > 0 && securityNumber.Length % 2 == 0 && ((Convert.ToInt64 (securityNumber) % 100) / 10) % 2 == 1) { return "Correct personnummer, Male."; } else if (securityNumber.Length > 0 && securityNumber.Length %…
- Assign secretID with firstName, a space, and lastName. Ex: If firstName is Barry and lastName is Allen, then output is:Barry Allen #include <iostream>#include <string>using namespace std; int main() { string secretID; string firstName; string lastName; cin >> firstName; cin >> lastName; /* Your solution goes here */ cout << secretID << endl; return 0;}Case four: I am having a glitch where it enter the college[0] and total_tuition [0] five times and then follows with the other four. I was hoping you can help guide me what I entereed wrong. #include "stdafx.h"#include <iostream>#include <cstdlib>#include <ctime>#include <string>#include <vector>#include <cctype>#include <iterator>#include <algorithm>#include <cmath>#include "ConsoleApplication11.h" using namespace std; string FBTeam;string College[5];string location;string Price_of_Ticket;int choice; int main(){vector<string> CULIST(5);vector<string> FBTEAM(5);string itemNumber; int num;int tuition = 0;int dorm = 0;int meal = 0;int total_tuition[5];int average;const int size = 5;double averages[size] = { 0.0 };bool stop = false, itemFound; cout << "--------------------------------------------------------------------------------" << endl;cout << " Colleges in Texas "<< endl;cout <<…Microsoft Visual C# 7th edition. need help, please. Thanks In previous chapters, you created applications for Marshall’s Murals. Now, modify the version of the MarshallsRevenue program created in Chapter 5 so that after mural data entry is complete, the user is prompted for the appropriate number of customer names for both the interior and exterior murals and a code for each that indicates the mural style: L for landscape S for seascape A for abstract C for children’s O for other When a code is invalid, re-prompt the user for a valid code continuously. For example, if Y is input, output Y is not a valid code, and re-prompt the user until a valid code is entered. After data entry is complete, display a count of each type of mural. For example the output should be in the following format with the correct number next to each mural type: The interior murals scheduled are: Landscape 1 Seascape 2 Abstract 1 Children's 3 Other 9 The exterior murals scheduled are: Landscape 4 Seascape 0…
- Event Listeners Go to the co_credit.js file in your editor. Create an event listener for the window load event that retrieves the field values attached to the query string of the page’s URL. Add the following to the event listener’s anonymous function: Create the orderData variable that stores the query string text from the URL. Slice the orderData text string to remove the first ? character, replace every occurrence of the + character with a blank space, and decode the URI-encoded characters. Split the orderData variable at every occurrence of a & or = character and store the substrings in the orderFields array variable. Write the following values from the orderFields array into the indicated fields of the order form: orderFields[3] into the modelName field orderFields[5] into the modelQty field orderFields[7] into the orderCost field orderFields[9] into the shippingType field orderFields[13] into the shippingCost field orderFields[15] into the subTotal field orderFields[17]…Differentiate the following: String Object from String Class, Substring from IndexOf, Date class from Simple date format class.can you make and HTML file for this code please function validate() { var x = document.getElementById("email"); //Taking the value entered in input tag in the HTML file email = x.value; //taking the value if ( // if these satments do not match below email.includes("@") && (email.includes("gmal.com") || email.includes("outlook.com") || email.includes("yahoo.com")) ) { document.getElementById("result").innerHTML = "Email is valid"; //Printing the result of validation on HTML page } else { // then print else document.getElementById("result").innerHTML = "Email is not valid"; }} // works

