Check applicable statements that describes a typical network switch (L2 switch) and its usage:
Q: Analyze the below code and fill in the blanks to complete the code #include int main() { int…
A: Solution: C Program: #include <stdio.h> int main() { int Array1[2][3] = {{10, 20, 30},…
Q: Write a code sequence that enables the input change notification interrupt for changes on inputs RA4…
A: The Answer is Provided in the next step:
Q: The words subnet, prefix, and BGP route should be defined and contrasted with one another.
A: Subnet: A subnetwork, often known as a segmented piece of a more extensive network, is a network…
Q: Subnetting (Subnetting) Fill in the blanks. (If possible show your solution) Number of needed…
A: Address Class is : B Default subnet mask is : 255.255.0.0 Custom subnet mask is : 255.255.255.224…
Q: Which of the following is a method of the Object class? O a. super) O b. encrypt( O c. equals) O d.…
A: Which of the following is a method of the Object class? a.) super() b.) encrypt c.) equals() d.)…
Q: 5. Prove that the following language is decidable: L = {0i1j 0k | i,j,k > 0 ∧ i < j < k}
A: A language is called Decidable or Recursive if there is a Turing machine which accepts and halts on…
Q: What exactly does application partitioning entail?
A: Introduction: Application partitioning is a word used to describe the process of developing…
Q: computer science- In the context of running a service firm, what exactly is scalability?
A: Introduction: Scalability, whether in a financial context or in the context of business strategy,…
Q: What is Standard Error, and what does it mean?
A: The standard error(SE) of a measurement is the exact standard deviation of a statistical sample…
Q: What is the value of JFK for the conversion below to be correct? (0100111JFK00)2 = (4FC)16 %3D…
A:
Q: Java
A:
Q: 3. The table below represents five lines from a cache that uses fully associative mapping with a…
A: Mapping Combinatorial: This indicates that perhaps the phrase id bits are being utilized to…
Q: 8. Consider the following Java code (Figure 7): O import java.util.Scanner; public class Q8 { public…
A: The solution to the given problem is below.
Q: Write a C program that will do the following: • Create an integer type 2D array with the number of…
A: The two-dimensional array can be defined as an array of arrays.
Q: Assume a program requires the execution of 75 x106 FP instructions, 112 x106 INT instructions, 88…
A: The answer as given below steps:
Q: Where do 5G's stated benefits stand in comparison to those of a 4G network?
A: 5G: Define 5G is the fifth-generation wireless technology that was implemented in 2019. The word…
Q: ays struct a Java class that includes the static methods described in the tab hod Return Formal…
A: The Java program to solve the given problem is below.
Q: Computer experts advise increasing the computer's Random Access Memory (RAM) if the processing speed…
A: The Answer is in step2
Q: What is a histogram? Write a scenario for a problem/situation, then draw a histogram which depicts…
A:
Q: What is the significance of the word Magnitude in the context of computer technology?
A: The signed-magnitude representation is used in computer science to describe how a number's magnitude…
Q: Assume that list1 is an object of class type ArrayList of Java (similar to KWArrayList class) and it…
A: This question comes under the collection of List in Java Initially "H", "E", "L", "L", "O" is in the…
Q: Write a script that will find the sum of the array elements using pointers. Conditions a) The user…
A: The Answer is in step-2.
Q: Is there a reason for typing "namespace std" in the middle of a C++ programme
A: There was a reason behind every statement that was written in a program and similarly there was…
Q: How to proceed the data in each excel entry box into separate txt files and upload them to the SAS…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. More often…
Q: What methods can you employ to identify fraudulent information on social media?
A: Introduction: Fake news is anything that is false or misleading while posing as legitimate news.
Q: Create table "STUDENT" with attributes "STUDENT_ID", "STUDENT_NAME", "STUDENT GPA". Use appropriate…
A: NOTE : There is a policy from bartleby to solve only first 3 subparts of a question.
Q: Derive the windows to viewpoint transformation coefficient matrix. Explain the application of this…
A: We need to derive the windows to viewpoint transformation coefficient matrix and explain the…
Q: Name the four types of I/O architectures. Where are each of these typically used and why are they…
A: Introduction Name the four types of I/O architectures. Where are each of these typically used…
Q: Concurrency control is a term used to describe the ability to manage many processes at the same…
A: Concurrency control: This is a database management system (DBMS) technique for addressing multi-user…
Q: Simplify the following Boolean Function using K-Map
A:
Q: There is Hash Table implemented with an array of 10 linked lists (shown below). Following 15 numbers…
A:
Q: Discuss, with necessary diagrams and mathematical analysis, the electrostatic deflection as occur in…
A:
Q: Is it possible to perform parallel processing of statements that are implicitly or explicitly…
A: Introduction: It is possible for multiple processes or programmes to execute simultaneously without…
Q: Q1. Write the Characteristics and Operations of Mode 0.
A: The internal machine cycles are counted in the timer mode. As a result, every machine cycle, this…
Q: Information technology In the.NET Framework, what is the difference between a DLL and an EXE?
A: Introduction: NET is a developer platform that consists of a number of tools, programming languages,…
Q: Practice by making a Ship class with the following members: A field for the name of the…
A: The above code is solved in Java below:
Q: 1. Which of the following show the interactive 2. UX for website design includes: A. Visual design…
A: As i have read guidelines i can provide answer of only first 3 sub part of questions in case of…
Q: 3. Make a directory by checking its existence using a shell script
A: A shell script is a list of commands in a computer program that is run by the Unix shell which is a…
Q: Hello edit the given JAVA code so that it prints the required output when we run it and follows…
A: Here I have defined the function named printPrime(). I have defined an array with a size one greater…
Q: 1) and let the löčál cost measure be defiñed by: =(x, y) = |x-yl, for x, y € R. Construct the cost…
A: Answer is in given below:-
Q: Computer science What types of information system 'Hardware' breaches are most common? Text on a…
A: Introduction: Through different system hardware tools, a hardware security threat can generate an…
Q: What is the name given to the data that has been transferred from RAM to virtual?
A: We are going to understand the terminology which is responsible for transferring data from RAM to…
Q: dure to control individual
A: Lets see the solution.
Q: What's the deal with the Web?
A: INTRODUCTION: Here we need to tell the deal with the Web.
Q: Q2) Consider the regular expression: (ablac)* a. Use Thompson's construction to construct a NFA
A: Given Regular Expression : (ab|ac)*
Q: Access Control Lists are used by firewalls (ACL). Explain what an ACL is and what typical contents…
A: Introduction: An Access Control List (ACL) is a set of rules used to filter network traffic. ACLs…
Q: Required: 1. Create a function with three output [ss, li,bas] which will determine whether the…
A: Suppose we are given a set of vectors { {V1, V2,...,Uk UK in 022, and we construct the Xu matrix A…
Q: Consider the following graph and find the minimum cost of this problem by using Prim's algorithm and…
A:
Q: In a row of seats, 1 represents a person sitting in that seat, and 0 represents that the seat is…
A: Let us see the answer:- Below I have provided code for the above answer and also I have written…
Q: 1. Write a program that creates an array with 100 randomly chosen integers. Your program should…
A: rand() is used to generate random numbers. CPP will not throw error for index out of bound so we…
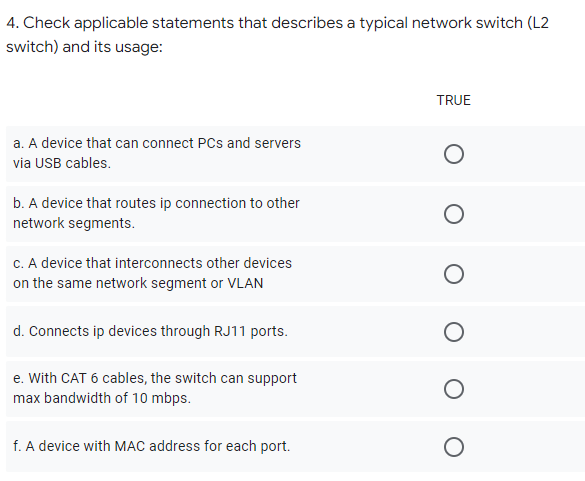
4. Check applicable statements that describes a typical network switch (L2 switch) and its usage:
Step by step
Solved in 2 steps with 1 images

- Write a code for VLSM calculator by c programming languageInput will be: 1) Enter IP address [sample- IP address - 192.168.1.0/22]2) How many LAN/Networks in your topology [number of 'n'. n can be any numbers]3) How namy Host/computers in each topology [number of 'n' in each topology. n can be any numbers] Output will be:1) Network address with subnet mask, first assignable address, last assignable address, broadcast address and gateway address for each LAN/Networks. Sample Input example for your understanding:- sample IP address - 192.168.1.0/24 ------------------------------------------ 1st LAN/Network : 258 Host/Computers2nd LAN/Network : 200 Host/Computers3rd LAN/Network : 120 Host/Computers4th LAN/Network : 20 Host/Computers5th LAN/Network : 56 Host/Computers...'n' times LAN/Network : 'n' Host/Computers Output example for your understanding:- ----------------------------------------- 1st LAN/Network : [Network address with subnet mask]1st LAN/Network : [first assignable…May someone please show me what should I input in the CLI in every task/ DIRECTION. Perform the following tasks and capture or copy the CLI commands for each indicated task. Task 1. Create VLAN’s, enable switchport mode, and assigning VLAN’s interfaces on each switch. Task 2. Configure sub-interfaces on a router with CME Task 3. Configuring a DHCP address scope on a Router Task 4. Configure Router’s Telephony Service for IP Phone Task 5. Create Directory Numbers Task 6. Verify Connectivity and Test IP Phone CommunicationAssume that the Ethernet Switch Forwarding table (MAC Address Table) starts out empty, and then Client #2 sends a packet to Client #3 and then Client #3 sends a reply packet back to Client #2. After these packet transmissions are done, show me the contents of the Forwarding Table of the Ethernet Switch. There are 3 switch ports, named Fa0, Fa1, Fa2. MAC Address: 1. 2. Switch Port: 1. 2.
- . Assume: Your laptop's Ethernet address is 0a:0b:0c:0d:0e:0f, DHCP server address is 131.111.7.3, your IPv4 address will be 131.111.7.121, the gateway's IP address is 131.111.7.1, and Ethernet address is 00:01:02:03:04:05, the network subnet mask is 255.255.255.0.Write the series of protocol/packet exchanges that occur on the wired Ethernet link, up until you can send a single packet to 128.232.0.20. You do not need to describe packets after this packet has left the link. Include ARP and DHCPWhich of the following statements is correct? a. characteristic of LAN is unlimited expansion b. characteristic of LAN is low cost access for low bandwidth channels c. characteristic of the hub architecture of ARC-net is alternative routing d. characteristic of the hub architecture of ARC-net is directionalized transmissionComputer Science Arriving at your university room, you plug into the wired Ethernet jack for the first time. The network admin has a record of your MAC address and your machine can join the network without further action on your part. Assume: Your laptop's Ethernet address is 0a:0b:0c:0d:0e:0f, DHCP server address is 131.111.7.3, your IPv4 address will be 131.111.7.121, the gateway's IP address is 131.111.7.1, and Ethernet address is 00:01:02:03:04:05, the network subnet mask is 255.255.255.0.Write the series of protocol/packet exchanges that occur on the wired Ethernet link, up until you can send a single packet to 128.232.0.20. You do not need to describe packets after this packet has left the link. Include ARP and DHCP.
- 1. Consider the network setup shown below. Assume that switch 3 has an empty switch table. Which of the following would be the entry on its switch table when it receives the packet from user 7? Select from the options below MAC Address of User 3 | Interface 3 | TTL of packet from User 1 MAC Address of User 7 | Interface 2 | TTL of packet from User 1 MAC Address of User 3 | Interface 1 | TTL of packet from User 7 MAC Address of User 7 | Interface 2 | TTL of packet from User 7 MAC Address of User 7 | Interface 1 | TTL of packet from User 1 2. Suppose user 1 transmits to user 7 and the switch tables of switch 1 and 2 are empty while the switch table of switch 3 contains information on user 7. How will switch 2 behave when it receives the packet? Broadcast the packet to user 4, user 5, switch 1, and switch 3. Send the packet to switch 3. Discard the packet since user 1 is not connected to any interfaces of switch 2. Send back the packet to…Assume that Computer A, which is connected through an Ethernet cable to the Switch S1, is just powered on. The user opens a browser and then types a website address to receive the website from the Server (as shown in Figure 1). Write down all the important protocols that come into play by the time the first frame containing HTTP request reaches R1. (Note: Before HTTP frame, other frames have already been sent by other protocol(s).) Write down all the protocols with reference to the TCP Model as follows? Application Layer: Transport Layer: Internet Layer: Link Layer:You need to send a document from one computer to another, and you want it to be encrypted. Because the target computer is on a different network, data must pass via one or more routers. Ethernet is the network technology on your network, while Wi-Fi is the network technology on the target network. Should this document transfer function based on what you've learnt about networking? Why do you think that is? In the italicized sections of this description, which levels of the OSI model are involved?
- Consider the following topology. iMac2 wants to send a file to iMac3. iMac2 knows the destination IP of iMac3. Assuming that the fully configured network has just been switched on, explain the exact process that occurs to send the file from source to destination (only one way). Since many things happen along the way, you only need to address the following in your answer: 1. The appropriate names of the PDU during different stages 2. The ARP table population 3. The MAC table population 4. The usage and role of the IP Routing table (assume that the router already knows all routes to different networks) Hint: This question does not require explanation of the OSI Reference Model or TCP/IP stack. Your answer should be strictly structured in a step-by-step number-point format.89. Consider the following statements :a. High speed Ethernet works on optic fiber.b. A point to point protocol over Ethernet is a network protocol for encapsulating PPP frames inside Ethernet frames.c. High speed Ethernet does not work on optic fiber.d. A point to point protocol over Ethernet is a network protocol for encapsulating Ethernet frames inside PPP frames.Which of the following is correct ? a. a and b are true; c and d are false b. a and b are false; c and d are true c. a, b, c and d are true d. a, b, c and d are false1 a) What layer of the OSI model does the ARP protocol best belong to? b) What command is used in the Windows Command Prompt to DELETE your ARP table? c) ARP protocol typically maintains a cache of IP-to-Ethernet address translation pairs on your network router?(t/f)

