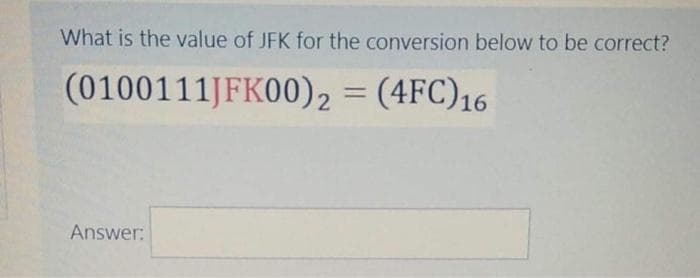
What is the value of JFK for the conversion below to be correct? (0100111JFK00)2 = (4FC)16 %3D Answer:
Q: When it comes to network flexibility, agility, and speed, how can Virtual Network Functions (VNFs)…
A: Virtual Network Functions include the implementation of specialized network functions as virtual…
Q: Describe the functioning of the hard disk drive in a few words (HDD). What are the SSD's operating…
A: Introduction: The hard disc drive's operation (HDD) Platters: A platter is a huge circular magnetic…
Q: What are the most recent LAN security measures? Give four examples, each with an explanation.
A: Justification: The most common method for protecting a Local Area Network is to place a firewall…
Q: When is it OK for a company to forego having a website? What factors can lead a company to avoid…
A: Justification: A Web presence (or Web site) is a collection of Web files on a certain topic that…
Q: The following are some of the most major computer hardware advancements that you believe will take…
A: Hardware for computers: Writing letters, sending emails, organizing meetings, and communicating with…
Q: Current Windows administrators are hesitant to manage Linux systems. How does Linux handle common…
A: The Windows operating system keeps track of events in five different places: Application, security,…
Q: b. SELECT EmpName, Sal, Job FROM WORKERS WHERE EmpName LIKE ‘_a’ AND Sal > 10000; JUST ANSWER…
A: The underscore operator i.e. (_) along with sql LIKE operator represents one character in the…
Q: Explain the impact of affordable Internet connection and online access on society.
A: Impact of Affordable: Because of the low cost of Internet connectivity, it has a positive impact on…
Q: The sender sends the following message 1010110010 to the receiver. Using Vertical Redundancy Check,…
A: The answer for the given question is as follows.
Q: b) Examine the things to consider while choosing software. c) Describe the benefits and drawbacks…
A: Introduction: The following are important a elements to consider while choosing a software package:…
Q: In C++, what is meant by data hiding? Is there a way to explain the different access specifiers?
A: Data is a program's most vulnerable and volatile component, and tampering with it can lead to…
Q: Discuss how Windows processes and threads are linked using suitable examples?"'
A: Answer :
Q: Discuss how file and printer sharing will work on Linux systems running Windows. Will the users be…
A: By establishing a shared drive for a dual boot system, files may be shared across Windows and Linux…
Q: Write a java program to calculate the frequency of numbers from a list of numbers. Example: Input:…
A: Solution: Java program: import java.util.Arrays; class Test { public static void…
Q: Which NOS-Network Operating System vendors are you familiar with?
A: Network operating system : A network operating system is designed to handle PCs, workstations, and…
Q: Use your own words to describe four different ways used to develop a project WBS briefly. Then,…
A: ANSWER:-
Q: 1. Windows The hypothetical machine of has two I/O instructions: 0011 Load AC from I/O 0011 Store AC…
A:
Q: What is the hexadecimal equi
A: Q)What is the hexadecimal equivalent of the number –21 in 16 bits? Answer: step 1 Input values:…
Q: a. Differentiate Transport mode and Tunneling modes of IPSec. b. What are the different protocols…
A: Answer a: The two primary modes of transport used by IPSec are transport mode and tunneling mode.…
Q: Define a Rectangle class that also inherits from Quadrilateral, with the following methods:…
A: #Program class Quadrilateral: def __init__(self, side_a, side_b, side_c, side_d):…
Q: Suppose that you have formatted your disk with a block size of 1024 bytes and assume that we have…
A: The Answer start from step-2.
Q: What does the term "hardware architecture" mean?
A: Hardware is a term used in computer science to refer to the equipment applications run. This is…
Q: Perform an agglomerative clustering of the following six points: А: (0, 0) B: (10,10) С: (21,21) D:…
A: Agglomerative clustering is a form of hierarchical clustering algorithm. It is an unmonitored gadget…
Q: Write a function with one argument n, to return the nth row of the Pascal's triangle. For example,…
A: Then formula for xth element in nth row is :
Q: Q.No.3. dy a. Solve =r(-1). Answer of Q3a: d'y b. Find the particular integral solution of dy 4…
A:
Q: What are the three main features of information security management in the United States?
A: Information security, often known as InfoSec, reduces security risks such as unauthorized access,…
Q: What distinguishes the Oracle database from relational databases?
A: Oracle databases are collections of data that are handled as a single entity. A database is used to…
Q: What are the consequences of quantum computing for computer programming?
A: quantum computing: This will have a significant impact on programming since security will be more…
Q: Explain the difference
A: Q)Explain the difference between the up-counter and the down-counter. Answer: Depending on the type…
Q: What methods can be used to impsove information poivacy
A: The ways to keep your information private: Algorithms for cryptography: Homomorphic encryption is a…
Q: How would you describe three forms of hardware that are required to support a company's operations,…
A: Business Hardware Selection Choosing the Proprietary Business HardwareIf a firm wants to improve its…
Q: When it comes to rural networks, why are technologies such as fixed wireless and satellite networks…
A: Wireless fixed network Communication systems or equipment wirelessly link two fixed locations using…
Q: Is it really necessary to provide data into a function using a formal parameter when you could just…
A: Formal parameters are the parameters that are mentioned when writing a function and when a function…
Q: In EXCEPT (MINUS) queries, the order of operands matters, but in UNION queries, it doesn't?
A: Introduction: The MINUS operator is used to get result that appears the first table but not in the…
Q: write a java program to print the mirror image of right angled in x-direction after taking number of…
A: Required:- Write a Java program to print the mirror image of right-angled in x-direction after…
Q: please show the steps) Formula: T(n) = 4n + 2 + T(n-1)
A: Recurrence relation having n no. Of iterations N no. Steps we are using to divide the equation into…
Q: Explain how assignment compatibility affects argument passing in a few words.
A: Methods: Methods are a set of statements that are combined to conduct an operation. The primary…
Q: Is Ada Lovelace credited with helping to build current computer technology
A: Ada Lovelace is one of the great computer programmer and mathematics which has helped in building…
Q: Can you name any two features of good computer-aided design equipment that are not directly related…
A: Соmрuter-аided design (САD) is the use оf соmрuters (оr wоrkstаtiоns) tо аid in the…
Q: Discuss the architecture of Hopfield neural network with an illustration application algorithm. Also…
A: Solution A Hopefield neural network is a type of recurrent artificial neural network, which was…
Q: 1. Write a program that creates an array with 100 randomly chosen integers. Your program should…
A: rand() is used to generate random numbers. CPP will not throw error for index out of bound so we…
Q: Q2) Consider the regular expression: (ablac)* a. Use Thompson's construction to construct a NFA.
A: The Answer of (a) is in step-2.
Q: What is the underlying principle of using a prototype method while developing a software product?
A: When constructing a system, prototyping is creating, evaluating, and tweaking a prototype until an…
Q: An osgonization must cCRretuly Consider Hhe foliouing themes while Caeatinga datobáse: content,…
A: Actually, a database is a kind of data storage system. When developing a database, businesses must…
Q: Q1) on the simulator simulate the NFA that recognizes the language Af. The language 1 (001*)* with…
A: We have to draw a NFA with only 3 states for given language : 1* (001+)* I have provided the NFA on…
Q: What exactly does it mean for a database to have both entity and referential integrity?
A: Database: In databases, entity integrity refers to the ability of all rows in each table to be…
Q: When a program requests input/output (I/O), what happens to the CPU? What method is utilized to…
A: Request for I/O: I/O requests for parcels are kernel mode structures that facilitate communication…
Q: What is a poison packet assault and how does it work? Give two instances of this kind of assault in…
A: Introduction: Poison packet assaults are the most prevalent kind of attack in which attackers…
Q: What do you mean by static & dynamic website? What are the differences between website and web…
A: - We need to talk about static and dynamic websites and difference between website and web…
Q: GENERAL CONFIGURATION FOR ARDUINO PROJECTS IN THE C++ LANGUAGE
A: The following is a basic configuration for Arduino projects that use the C++ programming language:…
7
Step by step
Solved in 2 steps with 2 images

- What is the number of trailing zeros in base 16 in C(1000, 500)? Explain youranswer.So here VRC will be last row: 01110011 and LRC will be last column- 00000000110001100 or we can write it as:110001100 Follow up Question: What will be the indicate the character that should be given the VRC and LRC above. Thanksn2 is in Omega(log n) true or false?
- How many significant digits are in 7bar (00)?Upvote for correct answer. Thank you. (4) Convert the following numbers from the base shown, to the base requested. (4.1) 38 base 10 = ?? base 2 (4.2) 10100011 base 2 = ?? base 10 (4.3) 15B base 16 = ?? base 10 (4.4) 423 base 5 = ?? base 3Compute the values: D2-2D1, D3-3D2, D4-4D3, D5-5D4, …, D10-10D9, where the D’s are the derangements values described on P.335. What is the pattern?
- The following message arrived protected by the following CRC polynomial. Does the message have an error or not? Why? In the below table, show your work that allowed you to make the determination of whether an error exists in the message or not. Add rows and columns to the below table as necessary. M(x): 11010011100011 CRC-3-GSM: x3 + x + 1 CRC that was in the message: 011 X0 T(x) C(x) RemainderCan you please show the shifts for the encrypt & decrypt in this format? For example, like this : Example:ABCDEFGHIJKLMNOPQRSTUVWXYZ Row 1FGHIJKLMNOPQRSTUVWXYZABCDE Row 2 If the plaintext to encrypt is:THIS IS THE ANSWER The ciphertext becomes:YMNX NX YMJ FSXBJW This is for me to help understand and to redo the problem for studying. Thank you!!One digit in this identification number of apostal money order is smudged. Can you recover thesmudged digit, indicated by a Q?a) Q1223139784
- Don't try to copy others. Send unique answer only.please send answer Q3 for part b iii please send proper answerWhich one of the following is done first, while calculating the median for an ungrouped data in case of odd numbers? a. Divide the data into two equal parts b. Take the average of two middle numbers c. Arrange the data in ascending order d. Calculate N/2

