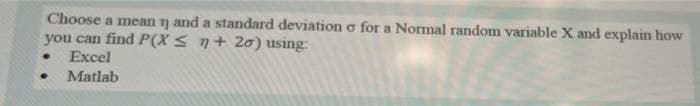
Choose a mean n and a standard deviation o for a Normal random variable X and explain how you can find P(X ≤ n+20) using: Excel ● Matlab
Q: What is CGI? Why was CGI introduced? What are the disadvantages of an architecture using CGI…
A: Introduction In this question we will write about the CGI.
Q: Problem 1. Construct a non-recursive procedure capable of reversing a single linked list of n…
A: Non-recursive procedure of Reversing a Single Linked List - Time Complexity O(n) struct RL{ int…
Q: Assuming the kid is connect www.google.com? (or any c in the correct sequence.
A: LAN: LAN stands for local area network. A network is a group of two or more connected computers, and…
Q: 2. Which command is used to list the attributes of a file? a) cp b) list c) Is d) attr
A: 2.Which command is used to list the attributes of a file? a) cp b) list c) Is d) attr Answer : c)…
Q: a) At what time will the statement S1 execute? b) At what time will L be updated? c) At what time…
A: Please check the step 2 for solution
Q: Three processes P1, P2 and P3 with related information are given in the following table: Process…
A: In Preemptive the process whose run time is shortest is taken irrespective of the arrival time For…
Q: Exercise 5.9 Discuss the strengths and weaknesses of the trigger mechanism. Con trast triggers with…
A: The trigger is a procedure that is automatically invoked in response to a specified change to the…
Q: What exactly is DHCP and what are its benefits?
A: Introduction: DHCP is a network Dynamic Host Configuration Protocol (DHCP) management protocol that…
Q: Why does the insertion sort outperform the sorted group in efficiency? Specify just one cause.
A: Answer: Insertion sort: In comparison to bigger items, this sorting method performs better on…
Q: What is the fundamental advantage of decoupling mechanism and policy in operating system…
A: Introduction: The terms policy and mechanism have diverse connotations. Mechanisms will regulate how…
Q: Show the results of the FIFO algorithm using the following page reference string with 3 available…
A: FIFO: Its abbreviation is First In First Out. This is the simplest page replacement algorithm. In…
Q: What might a cloud migration business case look like?
A: Introduction: When we develop a business case, we are ultimately driving a representation of ROE.…
Q: I need an operand and description of these JC, JNC, JZ, JNZ, JP conditions.
A: The operand and description of above JC, JNC, JZ, JNZ, JP conditions are given in next step.
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: Here we are expected to respond to the three inquiries posed to above about network foundation for…
Q: Problem 4: How many 3-to-8 decoders does it take to build a 5-to-32 decoder? Problem 5a: A decoder…
A:
Q: I need ideas for a Python programming project that includes the handling of an input file (data or…
A: Please check the step 2 for solution
Q: What are the advantages of retaining browsing history, and how long can it be kept?
A: Introduction: The following are some of the advantages of maintaining your browsing history:
Q: Draw the waveform for the data 1100111010 using the following encoding schemes: (i) Unipolar NRZ (i)…
A:
Q: The reason why you subscribed the internet plan (the download and upload speed) and from which ISP.
A: The upload and download are the two major task where someone can use internet. While we are…
Q: What Is A Symbol Table?
A: here is the solution. Symbol Table is an important data structure that is used in a Compiler.
Q: Develop an activity diagram of the following scenario The 2021 IEEE 23rd International Multitopic…
A: It is one of the UML diagrams under behavioral category. ⦁ It is used to explain the control flow…
Q: Consider the merits and cons of connectionless protocols as a potential substitute for…
A: Advantages of connectivity-based protocols: Very reliable.All piles follow the same pattern in…
Q: Describe the purpose of helper applications.
A: The helper applications are the external viewer programs launched to display content retrieved using…
Q: There are 6 x 10 small picture elements in a video each having 8 distinguishable 4 levels of…
A: Given Data : Number of picture elements = 60 Number of levels = 4 * 8 = 32 Rate of frames = 20 /s…
Q: Design a sequential detector that detects the code 1011 using T flip flops and any other gates. Show…
A:
Q: Write a program to draw a beautiful artboard
A: <!DOCTYPE html><html><body> <canvas id="myCanvas" width="200"…
Q: Compare TWO aspects of the IPv4 and IPv6 packet headers.
A: Answer: In the IPv4 header, the source and objective (destination) IPv4 addresses are 32-bit binary…
Q: Create a apex class called addition and then create a method to add the 2 integer and return the…
A: Apex is a program language which is used to create the salesforce Backend and mostly Salesforce…
Q: Write a java program to get the summation of unicode values of all the characters in a user entered…
A: Algorithm: Step-1: Start Step-2: Declare a variable str and take input from the user Step-3: Declare…
Q: What is Internet 2 exactly, and how does it work?
A: Introduction: Internet 2 is a set of high-performance networks that are connected to each other on a…
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: Apex is a program language which is used to create the salesforce Backend and mostly Salesforce…
Q: What does changing software configuration management policies imply?
A: Introduction: Software configuration management (SCM or S/W CM) is responsible for tracking and…
Q: The reason why you subscribed the internet plan (the download and upload speed) and from which ISP.
A: Plan details are : ISP - Airtel Upload speed - 50 mbps Download speed - 100 mbps
Q: What is the basis for considering the use of edge computing and cloud computing in the IoT system?
A: Introduction: It is preferable to locate computing resources at the "edge" of the network, which is…
Q: The problem states that there are five philosophers sitting around a circular table. The…
A: Problem statement: The problem states that there are five philosophers sitting around a circular…
Q: Authentication, authorization, and roles can be used to protect enterprise systems
A: Introduction: Enterprise systems may, in fact, be safeguarded by employing authentication,…
Q: Explain the phrase "cybersecurity" and why it is important Internet?
A: Introduction: Cybersecurity is the process of defending against cyber assaults on internet-connected…
Q: reate a new Java project/class called FamilyMembers. Ask user how many family members they have and…
A: The program is written in Java. Check the program screenshot for the correct indentation. Please…
Q: 6. Evaluate the determinant for the following matrix: O A. 8 OB.-2 O C.5 OD.-4 3 1 5
A: Here in this question we have given a matrix and we have asked to find the determinant of this…
Q: Write down the values of Carry, Overflow, Zero, Sign, Auxiliary Carry, Parity flag after each…
A: answer starts from step 2
Q: I need a C++ program that can write a program to show a greeting script the robot can use later. the…
A: cout is used to print on console cin is used to accept input \n is character literal used to print…
Q: What exactly are Database System Utilities?
A: Introduction: Database System Utilities are tools for managing the database system. It provides…
Q: What are some of the underappreciated fundamentals of software engineering?
A: Introduction: An executable piece of code is a component of a programmer performing a…
Q: Consider the following list: 63, 45, 32, 98, 46, 57, 28, 100 Using the sequential search as…
A: Hope you are doing fine. Please find the answers to the above question below: a. 90 - 8 comparisons…
Q: Question 1: Working with MARIE a) Write a MARIE Program that asks the user to input a number. The…
A: According to the Bartleby guideline, we are supposed to answer only one question at a time. Kindly…
Q: Consider a PUBLICATION COMPANY database in which data requirements are summarized as follows: Every…
A: Solution:- The entity list along with underlined primary keys are :- 1)…
Q: The text states that MIS is the most important class in the business school. Choose whether you…
A: MIS(MANAGEMENT INFORMATION SYSTEMS) is an essential discipline to be taught in a Business school,…
Q: hat distinctions should there be between the security of databases and the security of the rest of…
A: Introduction: System security protects a company's networks and resources from disruption,…
Q: I need ideas for a Python programming project that includes the handling of an input file (data or…
A: Python programming for handling input file
Q: a) Use the last six integer numbers from your UITM student ID as unsorted data. Then. determine the…
A: The bubble sort is the basic sorting algorithm in which the adjacent elements are compared and…
Step by step
Solved in 3 steps with 2 images

- Give an example of a random variable X : {b, c, d, e} → N (Natural Number) with expectation 2, where each of {b, c, d, e} has equal probability1. Write down an algorithm that can be used to evaluate whether a given sample isfrom a Poisson distribution or not using a Bayesian p-value and a discrepancymeasure T(y, θ)?For following observations, fit a line y= a+bx by the method of least squares. Estimate the coefficients, assume that the observations are gathered randomly and independent from populations of normal distributions with constant Variance: x 0.34. 1.38. -0.65. 0.68. 1.40 y. 0.27. 1.34. -0.53. 0.35. 1.28 Continue… x -0.88. -0.3. -1.18. 0.5. -1.75 y -0.98. 0.72. -0.81. 0.64. -1.59
- Hypergeometric distribution Given user defined numbers k and n, if n cards are drawn from a deck, find the probability that k cards are black. Find the probability that at least k cards are black. INPUT 11 7 OUTPUT 0.1628063397551007 0.24927823677714275Let X and Y be two binary, discrete random variables with the following joint probability mass functions. (a) Compute P(X = 0]Y = 1). (b) Show that X and Y are not statistically independent. P(X = 0, y = 1) = P(X = 1, Y = 0) = 3/8 P(X = 0, y = 0) = P(X = 1, Y = 1) = 1/8Solve in R programming language: Let the random variable X be defined on the support set (1,2) with pdf fX(x) = (4/15)x3. (a) Find p(X<1.25). (b) Find EX. (c) Find the variance of X.
- Using the MATLAB Histogram function, "hist.m", Illustrate the Central Limit Theorem by taking two different random variables and show how when appropriately scaled and summed, they converge to a Normal (Gaussian) distribution.Let X be discrete random variable. If P(Xshow that t ↔ ~q is logically equivalent to (t v ~q) → (~t ∧ q) without using a truth table.
- A random variable X with two-sided exponential distribution given by has moment generating function given by M X (t)= e^ t +e^ -t -2 t^ 2 . f x (x)= x+1,&-1\\ 1-x,&0<= x<=1 - 1 <= x <= 0 (a) Using M_{X}(t) or otherwise, find the mean and variance of X. (b) Use Chebychev inequality to estimate the tail probability, P(X > delta) , for delta > 0 and compare your result with the exact tail probability.If 3 numbers are randomly selected from the first 20 consecutive natural numbers without replacement, then the probability that their product is an odd number is.A polling company calls 100 random voters, finds that 53 of them support Donald Trump, and then concludes that 53% of the U.S. population supports him. This is an example of: Group of answer choices Maximum Likelihood Estimation Maximum A Posterior Estimation Bayesian Estimation Semi-supervised Learning

