Cite some examples of integrity constraints that you think can apply to the database.
Q: Bound the backward error in approximating the solution to 2 1 X1 [ ³ + ][ * ] - [ 25.35 ] by x = [ 3…
A:
Q: Encode oevopov with Huffman coding. a. List all symbols and their probabilities b. Find the Huffman…
A: ANSWER:
Q: Devise a strategy for connecting LANs for a single corporation with four geographically separate…
A: Common Carrier Networks are a very common setup. Each location would have a "Internet" circuit setup…
Q: Threats - Explore the classic ARP poisoning attack. What the mitigating strategies to defend…
A: Given: What are the mitigating strategies to defend against it? The solution is given below for…
Q: This is for C++ Design a Boolean function named isPrime(), which takes an integer as an argument…
A: Code is given below #include <iostream>using namespace std;//function isPrime()bool…
Q: Given main(), define a course base class with methods to set and get the courseNumber and…
A: Here I have deinfed the class Course. Inside the class I have created 2 variables of type String.…
Q: Following the development and testing of individual software modules, they must be combined and…
A: Introduction: Software development refers to computer programming, which is the process of writing…
Q: a. Bob claims that he can receive a complete copy of the file that is shared by the swarm. Is Bob's…
A: A. Yes. His first claim is possible, as long as there are enough peers staying in the swarm for a…
Q: Attributes item_name (string) item_price (int) item_quantity (int) Default constructor Initializes…
A: The complete JAVA program is given below with code and output screenshots Happy Coding?
Q: Protocols are fundamental to data transmission. Compare and contrast Transmission Control Protocol…
A: Protocols are a fundamental part of digital communication as they direct how to organize, transmit…
Q: The objective is to make sure we are able to set up their own GIT repository and are able to…
A: 1. Create a directory in any drive. For this example, a new directory named java_repo is created. 2.…
Q: Explain a practical scenario why split tunneling is used
A: It improves internet speeds by alleviating bottlenecks and conserving bandwidth because all your…
Q: IN JAVA PROgramming Write a function that swaps the first pair (1st and 2nd characters) with the…
A: We need to write a Java code for the given scenario.
Q: Java - class IntBTNode { private int data; private IntBTNode left;…
A: Answer
Q: Explain a practical scenario why split tunneling is used
A: Split tunnelling often enables you to pick which apps to safeguard and which to allow to connect…
Q: Consider the GBN protocol with a sender window size of 4 and a sequence number range of 1,024.…
A: INTRODUCTION It is Given that the window size is 4 and the sequence number is 1024.
Q: Write a php program to take the current room temperature from the user in degree celsius and try to…
A: Required:- Write a PHP program to take the current room temperature from the user in degree celsius…
Q: item_name (string) item_price (int) item_quantity (int) Default constructor Initializes item's…
A: Python is the programming languages and it is used to create the web applications and also used to…
Q: The BTNodeGen instance method search(T s) in the class above is intended to return the depth of the…
A: Here we have given appropriate output for the given code. you can find the solution in step 2. As…
Q: Suppose Bob joins a BitTorrent torrent, but he does not want to upload any data to any other peers…
A: Introduction: Free-riding: It is challenging to determine which peers hold what portions of the…
Q: A PC-relative mode branch instruction is 3 bytes long. The address of the instruction, in decimal,…
A:
Q: 0 2 A. 0 OB. 1 2 3 4 5 6 7 20 15 16 13 10 12 30 0 20 1 2 3 4 5 6 7 20 15 16 13 10 12 2 C. 1 2 3 4 5…
A: Given array of elements is: 30, 20, 15, 16, 13, 10, 12, 2 respectively. The address of the array…
Q: Briefly explain the two basic approaches used to minimize register-memory opera- tions on RISC…
A:
Q: Define a method named sortArray that takes an array of integers and the number of elements in the…
A: The JAVA code is given below with output screenshot
Q: On the entire gapminder data frame, compute the median of lifeExp for each year. For what years is…
A: According to the question , we have to write a query for compute the median of life expectancy for…
Q: What can I fix about this code to program it to display ONLY duplicates instead of with…
A: using System;using System.collections.Generic;using System.Linq;using System.Threading.Tasks. public…
Q: Ex: If the input is: 5 25 51 0 200 33 0 50 then the output is: 25,0,33, (the bounds are 0-50, so 51…
A: new_list = range (0,10) for i in range (0,10) print "numbers are", new_list [5:9]
Q: Given a base Plant class and a derived Flower class, complete main() to create an ArrayList called…
A: The ArrayList class is a resizable array that is present in Java. util package. While built-in…
Q: Read integers from input and store each integer into a vector until 0 is read. Do not store 0 into…
A: Algorithm: Start of the program Declare necessary variables Define a vector Print the message We…
Q: For the below code I need to add a history list with below conditions, Objectives Extend…
A: The answer is solved in python. first we create an empty array and call it calculation then we…
Q: Total = a + b + c; Average = Total / 6; B. C. D. Logic Errors Run-time Errors None of the above…
A: Syntax errors are the compile time which will not allows us for the execution of program Runtime…
Q: SOLVE STEP BY STEP IN DIGITAL FORMAT, Apply the principle of inclusion-exclusion Find the number of…
A: The question is to find the number of permutations of the 26 letters of the alphabet so that the…
Q: Note: Use Ruby language to write your code. Task Assigned: Write a program to read input two strings…
A: The solution is provided below
Q: The exercise of specialist knowledge and competencies is called a. data mining b. informatics c.…
A: The above question is solved in step 2 :-
Q: Write a function in python, cannot use isalpha or .get named count_letters that takes as a parameter…
A: I give the code in Python along with output and code screenshot
Q: What is the difference between an external iterator and an internal iterator? Describe an advantage…
A: what is difference between external and internal operator describe advantage of external iterator.
Q: IN JAVA SCRIPT Create a function that takes an integern and reverses it. Examples rev (5121) ➡…
A: Algorithm - Create a method with one integer as an argument. Now use the below logic while (rest…
Q: What are the practical benefits, if any, of importing a specific class rather than an entire package…
A:
Q: 1. In each row, four items are given: function to which runtime is proportional, original input…
A: The answer is below:-
Q: The x86 includes the following instruction: IMUL op1, op2, immediate This instruction multiplies…
A:
Q: Disk Parameters: Transfer size is 8K bytes, Advertised average seek is 6 ms, Disk spins at 3600 RPM,…
A: the answer is:-
Q: Consider the following AND/OR graph to describe a simple automobile diagnostic system using IF-THEN…
A: The answer is given in the below step
Q: Python.
A: NOTE :- PYTHON CODE
Q: Consider that only a single TCP (Reno) connection uses one 10Mbps link which does not buffer any…
A: Here we have given solution as per your requirement.You can find the solution in step 2.
Q: Exercise 2: in scilab Write a code to plot the 2 signals: y1 = sin(t); y2 = sin(2*t) and their sum…
A: Code is given below CODE IN SCILAB t = -10:0.1:10; y1 = sin(t);y2 = sin(2*t);y3 = y1 + y2;…
Q: What is meant by a control plane that is based on per- router control? In such cases, when we say…
A: What is meant by a control plane that is based on per router control? In such cases, when we say the…
Q: can u please send screenshot of code for the alignement/ indentation
A: - The code screenshot with indentation is requested here.
Q: Suppose Bob joins a BitTorrent torrent, but he does not want to upload any data to any other peers…
A: answer is
Q: Welcome and thank you for your interest in our workshop! Please enter the names of the participants…
A: Please refer below for your reference: Language used is Python:
Q: , describe the is-a and has-a relationship
A: Summary In Java, we can exercise our law using the Is- A relationship or using the Has- A…
Cite some examples of integrity constraints that you think can apply to the
Step by step
Solved in 2 steps

- Python Programming Problem: Simple Soccer Point TableThe programmer will design a simple point table lookup and update application. The table contains some basic information: team_name, match_played, win, draw, loss, point and rank. Design Solution:1. English Premier League is a prestigious soccer league. Here is the result of its one session. Man. City|38|32|2|4|98|1Liverpool|38|30|7|1|97|2Chelsea|38|21|9|8|72|3Tottenham|38|23|2|13|71|4Arsenal|38|21|7|10|70|5 2. Hypothetically, you have been assigned to design a simple lookup software for prestigious ‘English Premier League’ from a given point table. The point table contains team_name, match_played,win, draw, loss, points and rank. 3. The input file, ‘previous_result.txt’ has been provided to you above the top 5 teams in 2018-19 session. Your software needs to be able to search and update the point table based on user input. For example: The first time Chelsea played 38, the second time it changed (based on user input) to 40 and so…Subject : Data Structure Language : C Topic : Hash Table Sub Topic :- Pop- Push- Search Case : Bluejack Library is one of the popular libraries in the town. This library has more than 50.000 books. Sadly the senior librarian wants to resign and he doesn’t have time to teach the new librarian. Bluejack Library needs a simple program to help the new librarian so he can easily manage and search books. Bluejack Library hires you as a programmer to help them create a program that can help a new librarian find and manage books in this library easily using a C programming language and hashtable data structure. The criteria of the program are: The program consists of 4 menus, there are: View Book Insert Book Remove Book Exit If the user chooses View Book (Menu 1), then: * If there is no book, then show “There is no book(s) !” message * Otherwise, the program will show all the book data If the user chooses Insert Book (Menu 2), then: - The program will ask user to input the following…Subject : Data Structure Language : C Topic : Hash Table Sub Topic :- Pop- Push- Search Case : Bluejack Library is one of the popular libraries in the town. This library has more than 50.000 books. Sadly the senior librarian wants to resign and he doesn’t have time to teach the new librarian. Bluejack Library needs a simple program to help the new librarian so he can easily manage and search books. Bluejack Library hires you as a programmer to help them create a program that can help a new librarian find and manage books in this library easily using a C programming language and hashtable data structure. The criteria of the program are: The program consists of 4 menus, there are: View Book Insert Book Remove Book Exit If the user chooses View Book (Menu 1), then: * If there is no book, then show “There is no book(s) !” message * Otherwise, the program will show all the book data If the user chooses Insert Book (Menu 2), then: - The program will ask user to input the following…
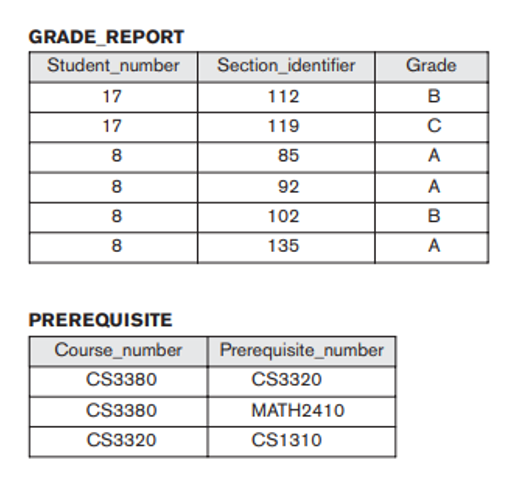
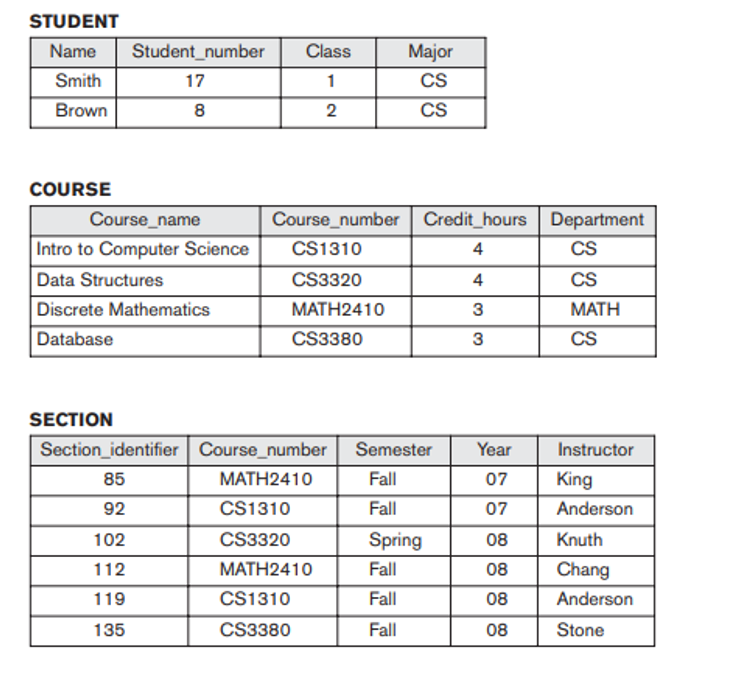
- Answer the following questions by referring to the tables below. COURSE Course_name Course_number Credit_hours Department Intro to Computer Science CS1310 4 CS Data Structures CS3320 4 CS Discrete Mathematics MATH2410 3 MATH Database CS3380 3 CS SECTION Section_ID Course_number Semester Year Instructor 85 MATH2410 Fall 07 King 92 CS1310 Fall 07 Anderson 102 CS3320 Spring 08 Knuth 112 MATH2410 Fall 08 Chang 119 CS1310 Fall 08 Anderson 135 CS3380 Fall 08 Stone Retrieve a list of all the courses under the "CS" department, listed alphabetically by course name. Retrieve the section ID, course name, course number, semester, year, and Instructor of the courses taught by Instructor "Anderson". Insert a tuple for a new COURSE with the following information: 4.The course name is Computer networks, and the course number is CS3480. It belongs to the CS…The PHP instruction: $name = $ REQUEST ["name"]; $surname = $_REQUEST ["sumame"]; echo "Welcome $name $surname, please visit the website!" (a) each parameter of the form becomes a field of the associative array $_REQUEST (b) it is correct only if the parameters are passed from the HTML form to the PHP program through POST (c) none of the answers are correct (d) it is correct only if the parameters are passed from the HTML form to the PHP program through GETPHP According to table the in the image (Assume that the following program section (Program Code 1) are variables that receives input from the user via a form. Build program code to provide instructions for entering the data into the assessments table. In addition, next build a link to view the data that has been entered.) <?php include ('config.php'); $ matrixnum = $_POST['matrixnum']; $ subject_code = $_POST['subject_code ']; $ quiz = $_POST['quiz']; $ assignment = $_POST['assignment']; $ project = $_POST['project']; $ total_marks= $_POST['total_marks']; $ grade = $_POST['grade']; Code program 1
- C++ Please explain the code below. It doesn't have to be long, as long as you explain what the important parts of the code do. You can also explain it line by line for best ratings. Thank you so much! The code is already correct, only explanation needed void addTail(int num) { node* newest = create_node(num); if (tail != NULL) { tail->next = newest; } tail = newest; if (head == NULL) { head = newest; } index++; } int add(int num) { addTail(num); return index; } int get(int pos) { node* currnode = head; int count = 0; while (currnode != NULL){ count++; if (count == pos){ return currnode -> element; }else{ currnode = currnode -> next; } } return -1; } int size() { return index; }…Write a PHP script to do the following: Create the following two dimensional array $students: ID Name Score 100 Ali 76 200 Khaleed 33 300 Fatema 89 400 Sumaya 45 Use foreach to display the array $students in an HTML table. Display the number of pass and fail students (pass if the score is greater than 50 and fail otherwise).Query Board Python or Java(Preferred Python please) Thank you! Programming challenge description: There is a board (matrix). Every cell of the board contains one integer, which is 0 initially.The following operations can be applied to the Query Board:SetRow i x: change all values in the cells on row "i" to value "x".SetCol j x: change all values in the cells on column "j" to value "x".QueryRow i: output the sum of values on row "i".QueryCol j: output the sum of values on column "j".The board's dimensions are 256x256."i" and "j" are integers from 0 to 255."x" is an integer from 0 to 31. Input: Your program should read lines from standard input. Each line contains one of the above operations. Output: For each query, output the result of the query. Test 1 Test InputDownload Test 1 Input SetCol 32 20 SetRow 15 7 SetRow 16 31 QueryCol 32 SetCol 2 14 QueryRow 10 Expected OutputDownload Test 1 Input 5118 34
- # Begin constantsCOLUMN_ID = 0COLUMN_NAME = 1COLUMN_HIGHWAY = 2COLUMN_LAT = 3COLUMN_LON = 4COLUMN_YEAR_BUILT = 5COLUMN_LAST_MAJOR_REHAB = 6COLUMN_LAST_MINOR_REHAB = 7COLUMN_NUM_SPANS = 8COLUMN_SPAN_DETAILS = 9COLUMN_DECK_LENGTH = 10COLUMN_LAST_INSPECTED = 11COLUMN_BCI = 12 INDEX_BCI_YEARS = 0INDEX_BCI_SCORES = 1MISSING_BCI = -1.0 EARTH_RADIUS = 6371 # Sample data for docstring examplesdef create_example_bridge_1() -> list:"""Return a bridge in our list-format to use for doctest examples. This bridge is the same as the bridge from row 3 of the dataset.""" return [1, 'Highway 24 Underpass at Highway 403','403', 43.167233, -80.275567, '1965', '2014', '2009', 4,[12.0, 19.0, 21.0, 12.0], 65.0, '04/13/2012',[['2013', '2012', '2011', '2010', '2009', '2008', '2007','2006', '2005', '2004', '2003', '2002', '2001', '2000'],[MISSING_BCI, 72.3, MISSING_BCI, 69.5, MISSING_BCI, 70.0, MISSING_BCI,70.3, MISSING_BCI, 70.5, MISSING_BCI, 70.7, 72.9, MISSING_BCI]]] def create_example_bridge_2() ->…A(n)______________is a collection of data fields that are all related to the same object, activity, or individual. a. attribute b. byte c. record d. columnC++ only. Do not copy. Correct code will upvoted else downvote. Monocarp is playing a PC game. Presently he needs to finish the principal level of this game. A level is a rectangular framework of 2 lines and n sections. Monocarp controls a character, what begins in cell (1,1) — at the convergence of the 1-st line and the 1-st segment. Monocarp's character can move starting with one cell then onto the next in one stage if the cells are nearby by side or potentially corner. Officially, it is feasible to move from cell (x1,y1) to cell (x2,y2) in one stage if |x1−x2|≤1 and |y1−y2|≤1. Clearly, it is denied to go external the matrix. There are traps in certain cells. In case Monocarp's character winds up in such a cell, he bites the dust, and the game closures. To finish a level, Monocarp's character should arrive at cell (2,n) — at the crossing point of line 2 and section n. Assist Monocarp with deciding whether it is feasible to finish the level. Input The principal…

