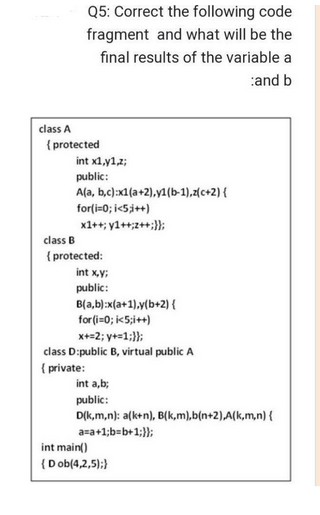
class A Q5: Correct the following code fragment and what will be the final results of the variable a and b {protected int x1,1,2; public: A(a, b,c):x1(a+2),yl(b-1),z(c+2) { for(i=0; i<5;j++) x1++;y1++++;)); class B {protected: int x,y; public: B(a,b):x(a+1),y(b+2) { for(i=0; i<5;i++) x+=2; y+=1;}); class D:public B, virtual public A { private: int a,b; public: D(k,m,n): a(k+n), B(k,m),b(n+2),A(k,m,n) { a=a+1;b=b+1;}); int main() (Dob(4,2,5):)
Q: List the several design models that we use throughout the software development lifecycle's analysis…
A: The Answer is in given below steps
Q: Some databases may only utilize the outside tracks of magnetic disks to store data, leaving the…
A: It is not unusual for us to come across hot spots when we are working with a database that has a…
Q: What are the advantages and disadvantages of using the cloud for your current online business, and…
A: Cloud Computing The delivery of various services through the Internet is referred to as cloud…
Q: The operating system places file blocks on hard drives in a sequential manner. What use does doing…
A: The answer is given in the below step.
Q: Operating systems make an effort to preserve successive blocks in the same position after reading a…
A: Magnetic Disk In order to write, rewrite, and access the data, a magnetic disc utilises a…
Q: What benefits and drawbacks come with using the cloud for data storage? There should be a directory…
A: Cloud storage is a cloud computing model that stores data on the Internet through a cloud computing…
Q: why is a work breakdown structure important? Do you need to use the software development lifecycle…
A: SOLUTION : The work breakdown structure is the visual representation of a hierarchical and…
Q: Consider these five moral guiding principles for computer systems.
A: Information system ethics are as follows: Rights and obligations in info This dimension displays…
Q: Define, Find x. Hint: use numpy.linalg.inv and the @operator for matrix multiplication. 35 1 5 A = 6…
A: Below I have provided Python Programming. Also, I have attached the screenshot of the code and…
Q: Provide at least five examples of how augmented reality has been or may be utilized in ways that the…
A: explain agumented reality and example of AR , benefits of AR and disadvantages of AR
Q: Study the many ways that information systems are being used in different industries.
A: Information system which refers to the system which is the an integrated the set of components which…
Q: What actions are taken in the forensic data recovery procedure from a solid-state drive?
A: The answer for the above question is given in the below steps for your reference.
Q: Which technological advancements in information systems, IT infrastructure, and information…
A: Artificial intelligence basically makes use of human intelligence in machines. Machine learning is…
Q: javascript
A: function edit() { var code = prompt("Enter the unique code"); if (code == user.random-generated…
Q: Include details on the communications, software, and hardware that comprise the basis of information…
A: Information technology (IT) is used by the computer to store, receive, transmit, and modify data.As…
Q: According to certain hypotheses, the growth of information technologies may be fueled by people and…
A: An information system, in technical terms, is a set of linked components that collect (or retrieve),…
Q: Which technological advancements in information systems, IT infrastructure, and information…
A: There are four methods for closing the gap between the processor and main memory. The only things…
Q: Make a list of all the many ways that a network may help companies save money. Along with other…
A: The answer for the above motioned question is given in the following steps for your reference.
Q: How do you feel about the idea of cloud computing? Do you believe it to be a good idea? Why?
A: Cloud computing is on-demand access to PC assets like data. storage and computing power, without…
Q: How precisely can you use netstat to check whether you've been infected?
A: Netstat is a command-line tool that displays approaching and active organisation associations, ports…
Q: Using python write a python program that reads from an imbedded XML file and retrieves elements and…
A: Below I have provided Python Programming. Also, I have attached the screenshot of the code and…
Q: Look at the various company sectors and the information management techniques used there.
A: Information technology may be advantageous for every business, whether it is a little corner store…
Q: Write a program that reads a list of words. Then, the program outputs those words and their…
A: Here is the c++ complete code of above problem. See below step for code and output.
Q: What distinguishes networked computers from other computers on a network?
A: Networking is the process of building, maintaining, securing, and troubleshooting networks, whereas…
Q: Where can I get information about the newest advancements in information systems, information…
A: e work bundle.These levels are included in each and every variation of the job breakdown structure.
Q: What are a few of the factors that lead many people to believe that the internet represents the apex…
A: introduction : The internet is the most potent tool now in use, and it has contributed to the…
Q: 1. [( q v p)-->r] [(p -->q) ^ p]
A: Note: there is no symbol between [( q v p)-->r] and [(p -->q) ^ p] . so we assume ^…
Q: I'm not familiar with routing or how it works. It's crucial to the differences between two common…
A: The answer is given in the below step.
Q: In order to become a skilled lightning web component designer, Mr. Sk is now attending LWC courses…
A: To access Salesforce data, Lightning web components use a reactive wire service.To clarify an Apex…
Q: What is the most effective way to backup user data? Your solution has to be proficient, quick, and…
A: It describes the process of digitally capturing information and documents and then putting those…
Q: There are several methods for achieving forensically sound data recovery from a solid-state disk.
A: By using bit stream imaging of hard drives as a criterion for admission into court, practitioners…
Q: Where would it be best to install an anti-virus application on a computer network with two servers…
A: First, three degrees of security are necessary. an effective firewall that can block viruses,…
Q: What actions are taken in the forensic data recovery procedure from a solid-state drive?
A: While the forensic recovery procedure differs from standard recovery methods, it may provide…
Q: Construct a class called Hypixel that will contain all information needed to describe and manipulate…
A: Construction of a class called Hypixel that will contain all information needed to describe and…
Q: escribe the downsides of cloud computing for students and teachers. Can we get out of this
A: Design:
Q: Are there issues with the many different information systems used at work? What choices do we have…
A: Given: In an organisation, the presence of several different kinds of information systems presents a…
Q: Do you believe that the production of the final product is the most crucial step in software…
A: No, As First For building software requirements are to be clearly understand and what and how that…
Q: Tom DeMarco asserts, "You can't control what you can't measure." His assertion makes it clear how…
A: Program MetricsA software metric is defined as a measurement of characteristics related to the…
Q: Which of the following is most likely to be removed at the conclusion of a line? What justifies the…
A: Programmers usually have to delete whitespaces in order to keep just the essential data and remove…
Q: What sets networked computers different from other computers connected to the same network?
A: Utilizing the cloudA firm may utilise software, hardware, and platforms as a service provided by a…
Q: By employing a firewall, your computer is shielded from possible outside attacks. It's crucial to…
A: Your answer is given below. Introduction :- Each batch of data that passes through a packet…
Q: There are several methods for achieving forensically sound data recovery from a solid-state disk.
A: By using bit stream imaging of hard drives as a criterion for admission into court, practitioners…
Q: Examine the numerous applications that various kinds of businesses employ information technology…
A: Information systems' foundations: Information technology may be advantageous to any business,…
Q: The operating system places file blocks on hard drives in a sequential manner. What use does doing…
A: Introduction Start: At the very bottom of the stack is where you will find all of the physical…
Q: What precisely does the phrase "cloud-based data storage" refer to, and what are some of the biggest…
A: What is cloud based data storage Cloud based data storage is a service which is given to the users.…
Q: What benefits and drawbacks come with using the cloud for data storage? There should be a directory…
A: Introduction When using a cloud computing provider who manages and maintains data storage as a…
Q: What warning signs point to the impending failure of a software project? Why elucidate?
A: The indicators indicate a software project is in trouble going to fail include the following: The…
Q: How can a software engineer arrive at a precise cost estimate for the application they are creating?
A: It is intrinsically difficult to calculate the cost of software, because the majority of efforts.…
Q: Please provide the names and short descriptions of 10 international organizations that are involved…
A: Write the names of 10 major international organisations in computer science and information…
Q: Using the cloud for computing What elements are required for handling SLAs?
A: SLA (Service level agreement):- Service Level Agreement (SLA) is an agreement between customer and…
Step by step
Solved in 2 steps with 1 images

- ### welcome_assignment_answers### Input - All nine questions given in the assignment.### Output - The right answer for the specific question. def welcome_assignment_answers(question): #Students do not have to follow the skeleton for this assignment. #Another way to implement is using a "case" statements similar to C. if question == "Are encoding and encryption the same? - Yes/No": answer = "The student should type the answer here" elif question == "Is it possible to decrypt a message without a key? - Yes/No": answer = "The student should type the answer here" else: ### you should understand why this else case should be included ### what happens if there is a typo in one of the questions? ### maybe put something here to flag an issue and catch errors answer = "This is not my beautiful wife! This is not my beautiful car! How did I get here?" return(answer)# Complete all the questions. if __name__ == "__main__": #use this…### welcome_assignment_answers### Input - All nine questions given in the assignment.### Output - The right answer for the specific question. def welcome_assignment_answers(question): #Students do not have to follow the skeleton for this assignment. #Another way to implement is using a "case" statements similar to C. if question == "Are encoding and encryption the same? - Yes/No": answer = "The student should type the answer here" elif question == "Is it possible to decrypt a message without a key? - Yes/No": answer = "The student should type the answer here" else: ### you should understand why this else case should be included ### what happens if there is a typo in one of the questions? ### maybe put something here to flag an issue and catch errors answer = "This is not my beautiful wife! This is not my beautiful car! How did I get here?" return(answer)# Complete all the questions. if __name__ == "__main__": #use this…### welcome_assignment_answers### Input - All nine questions given in the assignment.### Output - The right answer for the specific question. def welcome_assignment_answers(question): #Students do not have to follow the skeleton for this assignment. #Another way to implement is using a "case" statements similar to C. if question == "Are encoding and encryption the same? - Yes/No": answer = "The student should type the answer here" elif question == "Is it possible to decrypt a message without a key? - Yes/No": answer = "The student should type the answer here" else: ### you should understand why this else case should be included ### what happens if there is a typo in one of the questions? ### maybe put something here to flag an issue and catch errors answer = "This is not my beautiful wife! This is not my beautiful car! How did I get here?" return(answer)# Complete all the questions. if __name__ == "__main__": #use this…
- my code is displayed below, just need help with this question in c++. #include <iostream>using namespace std; class Vehicle{private: string *brand;public: Vehicle(){ brand = new string; *brand = "TBD"; } Vehicle(string b){ brand = new string; *brand = b; } void output(){ cout << "Brand: " << *brand << endl; } void setBrand(string b){ *brand = b; } string getBrand(){return *brand;}}; class Car:public Vehicle{private: int *weight;public: Car():Vehicle(){ weight = new int; *weight = 0; } Car(string b, int w):Vehicle(b){ weight = new int; *weight = w; } void output(){ cout << "Brand: " << getBrand() << " Weight: " << *weight << endl; } void setWeight(int w){ *weight = w; } int getWeight(){return *weight;}}; class Boat:public Vehicle{private: int *hullLength;public: Boat():Vehicle(){ hullLength = new int; *hullLength = 0; } Boat(string b, int h):Vehicle(b){ hullLength =…C++ Suppose we have the following declarations: struct Time { int hours; int minutes; int seconds; }; struct User { string username; string password; int userID; Time lastLogin; } newUser; User* userPtr = &newUser; Use the member selection arrow operator -> to show how you can set the lastLogin time of *userPtr to 16 hours, 43 minutes, and 39 seconds./ create the following functions: GetInteger - returns an integer DONE GetDouble - returns a double CheckInteger (called from GetInteger) - checks the range of an integer CheckDouble(called from GetDouble) - checks the range of a doubleCalculateSum - overloaded for integers and doubles as parameters DONE CalculateProduct - overloaded for integers and doubles as parameters DONE ShowSums - shows the sums of integers and the sum of doubles ShowProducts - shows the products of integers and the product of doubles. if you can create a function ShowInstructions that passes the type (integer or double) as a string. ShowInstructionsIntegers and ShowInstructionsDoubles
- Overload the following operators. > < <=When I am putting - getline(cin, name); getline(cin, name); an error comes up underneath the first getline saying "Identifier not found"Write assignment statements for the following: Assign a value of 1 to between if n is in the range -k through +k, inclusive; otherwise assign a value of 0 Assign a value of 1 to uppercase if ch is an uppercase letter; otherwise, assign a value of 0. Assign a value of 1 to divisor if m is a divisor of n; otherwise, assign a value of 0.
- # Write python codes here.print("Total E-Customer:", ECustomer.count)c1 = ECustomer("James")c1.setProductDetails("TV",35000,"Air Cooler", 9000)c2 = ECustomer("Mike")c2.setProductDetails("Mobile",20000,"Headphone",1200,"Fridge", 45000)c3 = ECustomer("Sarah")c3.setProductDetails("Headphone", 1200)print("=========================")c1.printDetail()print("=========================")c2.printDetail()print("=========================")c3.printDetail()print("=========================")print("Total E-Customer:", ECustomer.count)Output:Total E-Customer: 0=========================Name: JamesProducts: TV, Air CoolerTotal cost: 44000=========================Name: MikeProducts: Mobile, Headphone, FridgeTotal cost: 66200=========================Name: SarahProducts: HeadphoneTotal cost: 1200=========================Total E-Customer: 3Please answer the question in the code using ubunto the code : #include <stdio.h>#include <unistd.h>#include <stdlib.h>#include <sys/wait.h>int main ( ) {int pid ;pid = fork(); /* Duplicate. Child and parent continue fromhere *//* pid is non-zero, so I must be the parent *//* Never terminate and never execute a wait ( )*/ /* stop executing for 100 seconds */if ( pid != 0 ){while (1)sleep (100) ;}else /* pid is zero, so I must be the child */{exit (42) ; /* exit with any number */}}Assign courseStudent's name with Smith, age with 20, and ID with 9999. Use the printAll() member method and a separate println() statement to output courseStudents's data. Sample output from the given program: Name: Smith, Age: 20, ID: 9999 // ===== Code from file PersonData.java =====public class PersonData {private int ageYears;private String lastName; public void setName(String userName) {lastName = userName;} public void setAge(int numYears) {ageYears = numYears;} // Other parts omitted public void printAll() {System.out.print("Name: " + lastName);System.out.print(", Age: " + ageYears);}}// ===== end ===== // ===== Code from file StudentData.java =====public class StudentData extends PersonData {private int idNum; public void setID(int studentId) {idNum = studentId;} public int getID() {return idNum;}}// ===== end ===== // ===== Code from file StudentDerivationFromPerson.java =====public class StudentDerivationFromPerson {public static void main(String[] args) {StudentData…

