class People(): def _init_(self, name): self.name = name def namePrint(self): print(self.name) person1 = People("Sally") person2 = People("Louise") person1.namePrint()
Q: Wi-Fi offers both benefits and disadvantages. In light of the security concerns, should wireless…
A: Introduction: Here we are require to explain is wireless network a better option that can be used as…
Q: Prepare and submit an in-depth report, complete with references. The six layers of our computer…
A: TCS is a branch of computer science and mathematics that focuses: mathematical aspects of the field,…
Q: how they are related and how they differ; (2) how each affects the development of a system; (3) how…
A: Defining and discussing the terms methodology and technique. Including all of the following answer:…
Q: relationship among HCI and SDLC with the help of diagram
A: Life Cycle of Software Development The Software Development Life Cycle (SDLC) is a technique used by…
Q: What are the differences between Common Lisp and Scheme?
A: According to the information given:- We have to differences between Common Lisp and Scheme.
Q: How can an interactive system be designed to be user-friendly? Give an example to ilustrate your…
A: Usability is a property of any system: that allows the user to define the system's efficacy,…
Q: Explain what a network operating system's fundamental functions are.
A: Start: A network operating system is a kind of operating system that is specifically built to handle…
Q: What are the benefits of arrays? The maximum number of dimensions for an array is. What…
A: THE ARRAY - An array is a collection of contiguous memory allocations that contain similar types of…
Q: Question 5 Translate the following pseudo code to MIPS code: A = B +C
A: # load value at memory B into $t0 lw $t0, 0($s4) # load value at memory C into $t1 lw $t1, 0($s5) #…
Q: 2. Consider the following operation: Z = AB · BC а. Write out the truth table for the given…
A:
Q: What are the performance advantages of vectors over arrays?
A: INTRODUCTION: Here we need to tell the performance advantages of vectors over arrays.
Q: To what extent does the idea of "interdependence" vary from other phrases used to describe the same…
A: Interdependent objects are those that are mutually dependent on one another. Plants and animals,…
Q: how many 8 bit strings begin with 2 0’s
A: The question is how many 8 bit strings begin with two 0’s.
Q: The importance of verification over validation cannot be overstated. Whether it is true or false
A: It is critical to verify whether the system meets standards and produces accurate outputs. This is…
Q: what is Geometrical Transformations
A: Geometric transformations are needed to give an entity the needed position, orientation, or shape…
Q: What is the full name of FCS and HAL in computer science?
A: FCS and HAL: A frame check sequence (FCS) is a protocol error-detecting code added to a frame.…
Q: What exactly is a socket and what does it do? What is the difference between ports and sockets?
A: What exactly is a Socket and what does it do? A socket allows two processes on the same computer or…
Q: Assembly language instructions may be optimized by writing compilers and assemblers that rearrange…
A: The solution to the given question is: PIPELINE/RISKS - Pipeline is an execution technique in which…
Q: What are the four different sorts of primtives used in standards to specify the interaction between…
A: PRIMITIVES: The service primitives are utilized for each protocol in the OSI reference model. Each…
Q: What does it mean to develop an operating system in layers? What are the benefits and drawbacks of…
A: Introduction: It is possible to divide the operating system into layers. Several levels of…
Q: A logic programming language like Prolog might be used to address computer issues.
A: Prolog has been used largely for logic programming: Prolog, for example, is a logical collection of…
Q: Explain THREE (3) basic elements of access control.
A: ANSWER:-
Q: Is it necessary to understand the fundamental principles of web design? What is the reason for this…
A: In web design, pages are created; anyone with access to the internet can view that. Rather than…
Q: Because of their inherent features, wireless networks face a broad variety of challenges. Three of…
A: Explanation: In order to operate efficiently and successfully, industrial companies now rely on…
Q: Using unconditional jumps complete the following scenario: ⦁ Take a character from the user in…
A: C program to convert the case of the character using unconditional jump statements: #include…
Q: The tree pointer is the first node of the binary tree and has both data and two reference links.…
A: The first node of the tree is called the root.
Q: Sort the arrays according on where they store their data. Does allocating memory during compilation…
A: Means the compiler resolves at compile-time where certain things: Arrays are divided into two…
Q: IO devices play what function in the process execution? What causes a process to exit the running…
A: Given: Input and output devices are also referred to as I/O devices. An input unit is a general term…
Q: It's important to weigh the benefits and drawbacks of wireless networking before using it. Should…
A: Wireless local area networks (Lawns) transmit: We need to discuss whether or not wireless networking…
Q: How do you keep track of data in a half filled array?
A: The Answer is in step2
Q: Dynamic programming is a term that means something different to different people.
A: Dynamic programming is a term that means something different to different people.
Q: What are the differences between SpecC and SystemC?
A: Design and specification of digital embedded systems: Unlike Hols like Verily and HDTV, it is used…
Q: Do vectors have any benefits over an array?
A: Given: Vectors are better for frequent insertion and deletion, but Arrays are much better for…
Q: A 50 ml of 0.10 M NHa is being titrated by 0.10 M HCI. (Kb(NH3)) = 1.8 x 104) a. What is the pH at…
A: Answer
Q: Write a Java program that print its own source code.
A: This type of program is called Quine. The quine is program which takes no input and produce a copy…
Q: What is the role of Human mind in HCI. write detailed note on cognitive elements. (Subject: Human…
A: Human computer interaction are also called as HCI.It is the study of how people interact with…
Q: In computer science, what does it mean to "widen conversion" mean?
A: Given Question: What does "widen conversion" mean in the field of computer science?
Q: s shown in the Figure. (Hint: A point is in the rectangle if its horizontal distance to (0, 0) is…
A: Analysis of the problem: There is a rectangle with vertices a,b,c,d(let). The position of the…
Q: What language does the following regular expression represent? Assume the alphabet is {0,1}. a. R3 =…
A: We will generate language here step by step-1. (0+1) - Either 0 or 1 generated strings are either-…
Q: What is the significance of Bitcoin Block Integrity, and how does it relate to data integrity and…
A: Given: Data saved in Blockchain is immutable and cannot be edited or destroyed, therefore meeting…
Q: In what way does a code of ethics for software engineers serve a practical purpose?
A: The Answer is in step2
Q: lifference between block cipher and strea
A: Below the difference between block cipher and stream cipher.
Q: The link between processes and threads and how a process is formed in Windows may be shown by using…
A: Process: A process is the execution of a programme that enables you to carry out the specified…
Q: How can an interactive system be designed to be user-friendly? Give an example to illustrate your…
A: Interactive system can be designed to be user- friendly
Q: What are the criteria for selecting an appropriate SPI approach for the company and project context?…
A: ADVANTAGE OF SPI: The most significant benefit of employing the SPI is its ease of usage and…
Q: Is Scheme's define primitive an imperative language feature, or is it only a convenience? What's the…
A: Define the term "primitive": It has the primitive type of special form, with the Define is the…
Q: Create 2-3 catchy hashtag on responsible use of media.
A: Introduction: Coming up with a hashtag that can quickly go viral is the most important component of…
Q: Write a program using do-while loop that: Asks the user to enter a number between 0 and 99…
A: I give the code in Java along with output and code screenshot
Q: hello i want the compare between namshi and noon app please. thank you
A: Namshi and noon these are two apps developed by soudi Arabia.
Q: What is the best way for a computer to store the following information? What is the difference…
A: Binary data is primarily stored on the hard disk: All of information is kept on computers in digital…
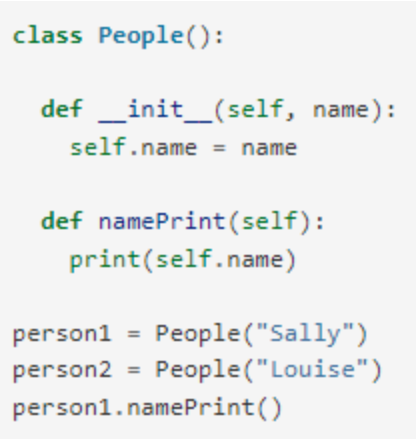
QUESTION 5
-
What does the following code output?
A. person1
B. Sally
C. Sally Louise
D. Louise
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Complete the Kennel class by implementing the following methods: addDog(Dog dog) findYoungestDog() method, which returns the Dog object with the lowest age in the kennel. Assume that no two dogs have the same age. Given classes: Class LabProgram contains the main method for testing the program. Class Kennel represents a kennel, which contains an array of Dog objects as a dog list. (Type your code in here.) Class Dog represents a dog, which has three fields: name, breed, and age. (Hint: getAge() returns a dog's age.) For testing purposes, different dog values will be used. Ex. For the following dogs: Rex Labrador 3.5 Fido Healer 2.0 Snoopy Beagle 3.2 Benji Spaniel 3.9 the output is: Youngest Dog: Fido (Healer) (Age: 2.0)# Coding - Simulate a robot Write a program that simulates the movements of a robot. The robot can have three possible movements: turn right turn left advance The robot is placed on a hypothetical infinite grid, facing a particular direction (north, east, south, or west) at a set of `{x,y}` coordinates,e.g., `{3,8}`, with coordinates increasing to the north and east. Create a Class `Robot` that contains a method `execute` which given a number of instructions will calculate the robot's new position, and the the direction in which it is pointing. ## Example The letter-string "RAALAL" means: Turn right Advance twice Turn left Advance once Turn left yet again Say a robot starts at `{7, 3}` facing north. Running this stream of instructions should leave it at `{9, 4}` facing west. ## Inputs and Outputs The argument of the `execute` is `string` in the format `X Y BEARING COMMANDS`. The method should return a one-liner `string` in the format `X Y BEARING`. In the…java Create a Storage<T> abstract class. The class has abstract methods void print() which prints the object of the storage. The class has a non-abstract method add(T element) which adds the not-null element in the storage if the element is not already present. Create a class MyStorage which is a subclass of Storage.
- Class: Square Create a class called "Square", which is inherited from“TwoDimensionShape” class. The "Square" class is used to calculate theArea and the Perimeter of square shapes when their side-length is given, or in contrast,finding the side-length of the square when the Area or the Perimeter of the square is given.The specifications of this class are below. Data Members (Attributes): All are private. sideLength: the sidelight (L) of the square. Methods/Operations/Getters/Setters: Default Constructor: when creating an object this constructor must set the side-length of the square by calling the method setSideLength(). Also, this constructor willcall the findArea() and the findPerimeter() in addition to summaryPrint() to calculateand print all needed information. User-Defined Constructor: when creating an object this constructor shouldfind the side-length of the square by calling the method findSquareSideLength()and pass the Area or the…Programming Language= PYTHON 3. Personal Information Class Design a class that holds the following personal data: name, address, age, and phone number. Write appropriate accessor and mutator methods. Also, write a program that creates three instances of the class. One instance should hold your information, and the other two should hold your friends’ or family members’ information. My information: Name: John Doe Address: 111 My Street Age: 22 Phone Number: 555-555-1281 Mom's information: Name: Mom Address: 222 Any Street Age: 52 Phone Number: 555-555-1234 Sis's infomation: Name: Jane Doe Address: 333 Her Street Age: 20 Phone Number: 555-555-4444 Dad's information: Name: Dad Address: 222 Any Street Age: 56 Phone Number: 555-254-5611java programming Robot Class : a robot has a name , located at a point with integer coordinates , faces north , east , south , or west and keeps a record of all its movements positions . The class has the following methods : A default constructor that initializes robot's name to " Unknown ” , location to ( 0,0 ) , direction to North , and travelled distance to 0 , and simulated movements to null . A constructor that given robot's name , starting location , and facing direction , Accessor methods to access all the instance variables and the simulated movements of the robot Mutator methods that change the instance variables to given values and they made the change for only suitable values . tumLeft and turn Right methods that change the direction of the robot but not the location move method that moves the robot by one unit in the direction it is facing . get Travelled Distance method that retums how many units has the robot moved .
- True or False A class can implement more than one interface./** Represents a car.*/public class Car // TODO: Inherit from Vehicle{ // Do NOT add any instance variables public Car(double purchasePrice) { // TODO: Complete } // TODO: Override the getValue methodWrite a Java class Student inherited from Person class. Your class must have the following features: Student - major: String + Student() + Student(name: String, id: int, major: String) + getMajor(): String + Override toString() method: you have to return needed data Fields values. Note: major data members can take only CS for Computer Science, CIS for Computer and Information Systems, CPE for Computer Engineering, SE for Software Engineering, and NES for Network Engineering and Security.
- Create a class Animal Create a class Cat, and a class Dog, and a class Bearded Dragon which extend Animal. Add to your Animal class: Member: name Methods: Public Animal (String name) //constructor public void makes Sound () with the implementation printing out a generic animal sound. Next, override (add) the makes Sound() method to your Cat and Dog class, with the implementation specific to each animal (i.e, cat says purr..). Do not override the makesSound() for your Dragon (bearded dragons don't make sounds!) Note, you'll also need a constructor in each of your subclasses which calls super(name) to initialize the common 'name' member of Animal. Next (in your test harness) create a List of different Animals ( a couple cats, a dog, a dragon... ) and add these Animals to your list. Iterate through your list & call makeSound on each. (you should observe the makeSound method called will be: cat -> from Cat class, dog-> from Dog class, bearded Dragon -> from Animal class ) EC:…The class "Student" has the following attributes: studentId (int), name (String), surname (String), deptCode (String).Write a constructor method for the "Student" class that takes values as parameters for all these attributes.package lab1; /** * A utility class containing several recursive methods * * <pre> * * For all methods in this API, you are forbidden to use any loops, * String or List based methods such as "contains", or methods that use regular expressions * </pre> * * */ public final class Lab1 { /** * This is empty by design, Lab class cannot be instantiated */ privateLab1(){ // empty by design } /** * Returns the product of a consecutive set of numbers from <code> start </code> * to <code> end </code>. * * @param start is an integer number * @param end is an integer number * @return the product of start * (start + 1) * ..*. + end * @pre. * <code> start </code> and <code> end </code> are small enough to let * this method return an int. This means the return value at most * requires 4 bytes and no overflow would happen. */ publicstaticintproduct(ints,inte){ if(s==e){ returne; }else{ returns*product(s+1,e); } }…

