Code in Java. Instructions attached
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter4: Selection Structures
Section4.3: Nested If Statements
Problem 7E
Related questions
Topic Video
Question
100%
Code in Java. Instructions attached
Transcribed Image Text:ction 4.24 - CMP 167: Program X
zy Section 3.5 - CMP 167: Programn X +
kMnlnB-KsSu5s3Mg/edit
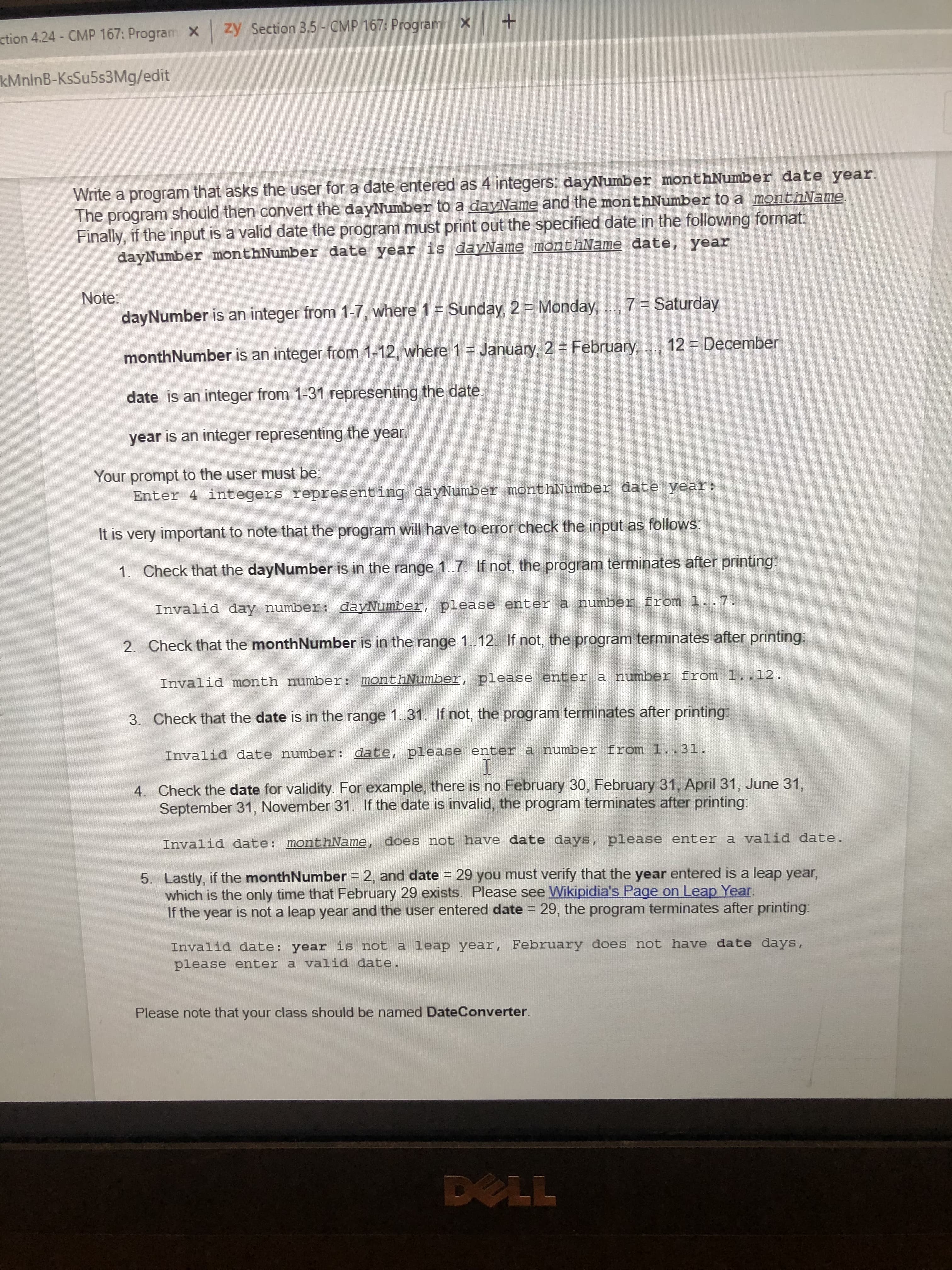
Write a program that asks the user for a date entered as 4 integers: dayNumber monthNumber date year.
The program should then convert the dayNumber to a dayName and the monthNumber to a monthName.
Finally, if the input is a valid date the program must print out the specified date in the following format
dayNumber monthNumber date year is dayName monthName date, year
Note:
dayNumber is an integer from 1-7, where 1 = Sunday, 2 = Monday,
7 = Saturday
monthNumber is an integer from 1-12, where 1 = January, 2 = February,
12 December
date is an integer from 1-31 representing the date.
year is an integer representing the year.
Your prompt to the user must be:
Enter 4 integers representing dayNumber monthNumber date year:
It is very important to note that the program will have to error check the input as follows
1. Check that the dayNumber is in the range 1.7. If not, the program terminates after printing:
Invalid day number: dayNumber, please enter a number from 1..7.
2. Check that the monthNumber is in the range 1..12. If not, the program terminates after printing:
Invalid month number: monthNumber, please enter a number from 1..12.
3. Check that the date is in the range 1..31, If not, the program terminates after printing
Invalid date number: date, please enter a number from 1..31.
4. Check the date for validity. For example, there is no February 30, February 31, April 31, June 31,
September 31, November 31. If the date is invalid, the program terminates after printing:
Invalid date: monthName, does not have date days, please enter a valid date.
5. Lastly, if the monthNumber = 2, and date = 29 you must verify that the year entered is a leap year,
which is the only time that February 29 exists. Please see Wikipidia's Page on Leap Year.
If the year is not a leap year and the user entered date = 29, the program terminates after printing:
Invalid date: year is not a leap year, February does not have date days,
please enter a valid date.
Please note that your class should be named DateConverter.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning