Computer science Cs 102
Q: Python
A: Introduction of the Program: The Python program takes the price of the pasties and tip % that you…
Q: Computer Science Engineering:
A: The above question is coded in C language, according to the given requirements.
Q: Why are programmers not developing machine translation software?
A: Machine language Machine language is a low-level language comprised of binary numbers or pieces…
Q: elop software
A: In systems engineering, data systems and software designing, the systems development life cycle…
Q: Define technological flexibility in computer science.
A: Introduction: Flexibility in technology- The creation, development, and implementation of new…
Q: c in computer scienc
A: ARC Advanced RISC Computing (ARC) is a definition of computer production that has never led to the…
Q: Translate assembly language into machine language: BCF STATUS, Z
A: BCF STATUS Z means Clear the Set to Z times.
Q: List Python Speech Recognition Packages.
A: A handful of packages for speech recognition exist on PyPI. A few of them include: apiai assemblyai…
Q: Computer science WHAT IS SCIENTIFIC RESEARCH METHOD (SRM)?
A: Introduction: The SRM discipline aids in determining the value that each supplier delivers, as well…
Q: Explain rounding in as few words as possible. Computer science
A: Estimation and rounding Rounding is a method of simplifying numbers to make them simpler to…
Q: Software engineering
A: Agile is a project development methodology that uses an iterative approach to deliver a project…
Q: Father of computer science
A: Alan Turing is known as the father of computer science.
Q: What is computer science engineering
A: The answer is as following:-
Q: C programming Topic: Stacks
A: program
Q: . Fragments, Creating Fragments with java Code explain detailed
A: Overview:A fragment is a reusable class executing a part of a movement. A Fragment ordinarily…
Q: python
A: write a python program to compute the average value mean
Q: omputer science...
A: We need to find the create the program to find the angle between the sides of a triangle.
Q: Computer science 1.Discuss three duties of the Sysadmin.
A: Definition of Sysadmin and three Duties Sysadmin is System Administrator responsible for management…
Q: language
A: According to the question we need to tell the correct way to check if the linked list is empty. a.…
Q: Python code
A: May this help you...... Python Source Code: # 1. import pandas as pd import matplotlib.pyplot as plt…
Q: Using C program
A: The first program will be answered only. C code: #include <stdio.h> int main(int argc, char…
Q: mputer Science
A:
Q: Programming language C++
A: Can you please share bigger pics?
Q: Research in computer science
A: Areas of Research in Computer Science: Assistive Technologies and Learning with disabilities…
Q: Digital ele, computer science!.
A: given : F(W,X,Y,Z)=(Y'+X)(W+X)
Q: omputer Science Question
A: Given:
Q: In computer programming... 10 % 3 * 3 – (1 + 2) =
A: Explanation:-The priority of the operators present in the given equation is as follows:- () > %…
Q: C PROGRAMMING LANGUAGE
A: As per the requirement program is completed. Algorithm: Step 1: Write the main() method Step 2: Call…
Q: Computer science
A: System 1 Mar=16 bits it can hold address up to 216 given each address of size 16 bits Memory…
Q: Acme java code
A: Digital certificate management is complex and can be challenging to manage effectively without the…
Q: COMPUTER ORGANIZATION
A: The first three parts will be answered a) The boolean equation for SOP form : Y = A¯ B¯ C¯D+A¯ B¯CD…
Q: # Python Natural Language Processing
A: Here there is no image provided i think question is , what is NLP? Like about NLP. Answer is…
Q: What are some applications of natural language processing
A: Lets see some the applications of natural language processing
Q: computer Architecture
A: Sorry, we are not allowed to provide the references links but we will provide you with enough best…
Q: Computer science Short answer What is Data control language (DcL)?
A: Introduction: What is Data control language (DCL)?
Q: Computer science Short answer Explain puplic and secret key
A: Introduction: A public key and a private key are the two most common forms of keys. Both are used…
Q: PYTHON.....
A: The code is below:
Q: When was the first photocopier introduced? Computer science
A: Introduction: Photo Illustration: The photocopier is a piece of technology that allows individuals…
Q: ming
A: For part 1: Define function remove_duplicate_sorted with t as parameter Define empty list str Use…
Q: c++ programmin
A: Given Code: int main(){ int x=5, y=3; string s = "Hi", r="There";…
Q: gramming lang
A: High-Level programming language.
Q: what is debicated computers
A: A dedicated computers is designed which is assigned one and only one task.In this a dedicated server…
Q: Python: 2048 games
A: The following are the steps to building a Python 2048 game: 1. Install the pygame module. 2. Module…
Q: c program
A: I have answered this question in step 2.
Q: Computer Engineering C++ Programming
A: #include<bits/stdc++.h> #define ll long long #define ull unsigned ll #define uint unsigned…
Q: C++ Language
A: In GetData Function ,its not clear what are the arguments we should pass.So,In that case I passed…
Q: Python language
A: Objective: This program receives two numbers from the user and displays "YES" if exactly one of the…
Computer science Cs 102
Step by step
Solved in 2 steps with 1 images

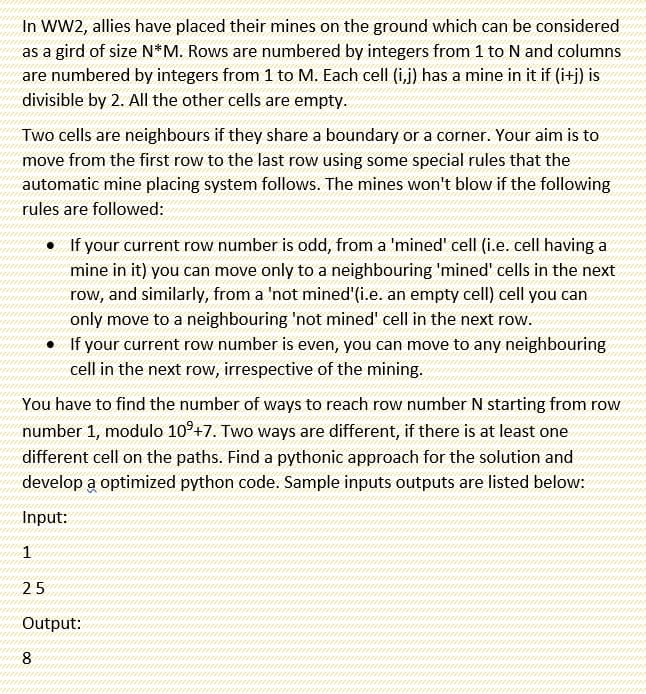
- You are given a grid having N rows and M columns. A grid square can either be blocked or empty. Blocked squares are represented by a '#' and empty squares are represented by '.'. Find the number of ways to tile the grid using L shaped bricks. A L brick has one side of length three units while other of length 2 units. All empty squares in the grid should be covered by exactly one of the L shaped tiles, and blocked squares should not be covered by any tile. The bricks can be used in any orientation (they can be rotated or flipped). Input Format The first line contains the number of test cases T. T test cases follow. Each test case contains N and M on the first line, followed by N lines describing each row of the grid. Constraints 1 <= T <= 501 <= N <= 201 <= M <= 8Each grid square will be either '.' or '#'. Output Format Output the number of ways to tile the grid. Output each answer modulo 1000000007. Sample Input 3 2 4 .... .... 3 3 ...…You are given a 2 by n grid, where the cell on row i column j contains a non-negative number ai,j . You can start at either cell in the lefttmost column, and your goal is to reach either cell in the rightmost column by a sequence of moves. You can move to an adjacent cell (if it exists) in each of the 4 cardinal directions (up,down, left and right). A path achieves a score equal to the sum of values in its cells. Note that a cell which is used twice in a path only counts its value once to the score of that path.Design an algorithm which runs in O(n) time and finds a path of minimum score from the leftmost column to the rightmost column.Simulated annealing is an extension of hill climbing, which uses randomness to avoid getting stuck in local maxima and plateaux. a) As defined in your textbook, simulated annealing returns the current state when the end of the annealing schedule is reached and if the annealing schedule is slow enough. Given that we know the value (measure of goodness) of each state we visit, is there anything smarter we could do? (b) Simulated annealing requires a very small amount of memory, just enough to store two states: the current state and the proposed next state. Suppose we had enough memory to hold two million states. Propose a modification to simulated annealing that makes productive use of the additional memory. In particular, suggest something that will likely perform better than just running simulated annealing a million times consecutively with random restarts. [Note: There are multiple correct answers here.] (c) Gradient ascent search is prone to local optima just like hill climbing.…
- A safe is locked by a combination of of four binary digits (that is, 0 or 1), but theowner has forgotten the combination. The safe is designed in such a way that nomatter how many digits have been pressed, if the correct combination of three digitsis pressed at any point, then the safe automatically opens (there is no ”enter” key).Our goal is to find the minimum number of digits that one needs to key in in order toguarantee that the safe opens. In other words, we wish to find the smallest possiblelength of a binary sequence containing every four-digit sequence in it.(a) Create a digraph whose vertex set consists of three-digit binary sequences. Fromeach vertex labelled xyz, there is one outgoing edge (labelled 0) leading to vertexyz0, and another outgoing edge (labelled 1) leading to vertex yz1.(b) Explain why every edge represents a four digit sequence and why an Euleriantour of this graph represents the desired sequence of keystrokes.(c) Find the minimum number of digits that one…Mastermind is a code-breaking game for two players. In the original real-world game, one player A selects 4 pegs out of 6 colors and puts them in a certain fixed order; multiples of colors are possible (for example, red-green red-green). His opponent B does not know the colors or order but has to find out the secret code. To do so, B makes a series of guesses, each evaluated by the first player. A guess consists of an ordered set of colors which B believes is the code. The first player A evaluates the guess and feeds back to B how many positions and colors are correct. A position is correct ("black") if the guess and the secret code have the same color. Additional colors are correct ("white"), if they are in the guess and the code, but not at the same location. For example1 2 3 4secret: red-green red greenguess: red blue green purpleresults in one correct position ("black = 1") for the red peg at position one and one additional correct color ("white=1") for the green peg in the guess.…Mastermind is a code-breaking game for two players. In the original real-world game, one player A selects 4 pegs out of 6 colors and puts them in a certain fixed order; multiples of colors are possible (for example, red-green red-green). His opponent B does not know the colors or order but has to find out the secret code. To do so, B makes a series of guesses, each evaluated by the first player. A guess consists of an ordered set of colors which B believes is the code. The first player A evaluates the guess and feeds back to B how many positions and colors are correct. A position is correct ("black") if the guess and the secret code have the same color. Additional colors are correct ("white"), if they are in the guess and the code, but not at the same location. For example1 2 3 4secret: red-green red greenguess: red blue green purpleresults in one correct position ("black = 1") for the red peg at position one and one additional correct color ("white=1") for the green peg in the guess.…
- Imagine there are N teams competing in a tournament, and that each team plays each of the other teams once. If a tournament were to take place, it should be demonstrated (using an example) that every team would lose to at least one other team in the tournament.Problem Alice was given a number line containing every positive integer, x, where 1<=x<=n. She was also given m line segments, each having a left endpoint, l (1<=l<=n), a right endpoint, r (1<=r<=n), and an integer weight, w. Her task is to cover all numbers on the given number line using a subset of the line segments, such that the maximum weight among all the line segments in the chosen subset is minimal. In other words, let S=(l1,r1,w1),(l2,r2,w2),....,(lk,rk,wk), represent a set of k line segments chosen by Alice, max(w1,w2,...,wk) should be minimized. All numbers 1,2,....n should be covered by at least one of k the chosen line segments. It is okay for the chosen line segments to overlap. You program should output the minimized maximum weight in the chosen subset that covers all the numbers on the number line, or -1 if it is not possible to cover the number line. Input format The first line of the input contains an integer, n - denoting the range of numbers…In computer science and mathematics, the Josephus Problem (or Josephus permutation) is a theoretical problem. Following is the problem statement: There are n people standing in a circle waiting to be executed. The counting out begins at some point (rear) in the circle and proceeds around the circle in a fixed direction. In each step, a certain number (k) of people are skipped and the next person is executed. The elimination proceeds around the circle (which is becoming smaller and smaller as the executed people are removed), until only the last person remains, who is given freedom. Given the total number of persons n and a number k which indicates that k-1 persons are skipped and kth person is killed in circle. The task is to choose the place in the initial circle so that you are the last one remaining and so survive. For example, if n = 5 and k = 2, then the safe position is 3. Firstly, the person at position 2 is killed, then person at position 4 is killed, then person at position 1…
- we consider a problem where we are given a set of coins andour task is to form a sum of money n using the coins. The values of the coins arecoins = {c1, c2,..., ck}, and each coin can be used as many times we want. Whatis the minimum number of coins needed?For example, if the coins are the euro coins (in cents){1,2,5,10,20,50,100,200}and n = 520, we need at least four coins. The optimal solution is to select coins200+200+100+20 whose sum is 520.A matrix is an array of numbers of size m by n (i.e., m x n). When we multiply 2 matrices, we multiply the matching numbers, then sum them up. Multiplying a matrix of size m x n with another matrix of size n x q will result in a matrix of size m x q. An example is shown in Figure 1: [ ? ? ? ? ? ? ] x [ ? ? ? ? ] = [ ?? +?? ?? + ?? ?? + ?? ?? + ?? ?? + ?? ?? + ?? ] Matrix 3 x 2 Matrix 2 x 2 Matrix 3 x 2 Figure 1: Multiplication of Matrix 3 x 2 and 2 x 2 Write a C++ program that multiplies 2 matrices and return the sum of the transposed matrix. Your program shall include the following: a) Define two 2 dimensional arrays, M and N that each represents a matrix of size 3 x 2 and a matrix of size 2 x 2. Request the user to enter the values for the 2 arrays using advanced pointer notations (refer to your slides for the list of array pointer notations). b) Create a function named multMatrix() that passes as arguments, the values of array M and N, multiplies them and store the results in a new…X-Kingdom has trapped n number of soldiers of their opponent. They want to execute them. They created a strategy so that the prisoners will kill each other and at the end one prisoner will be alive and eventually released. As part of the process, they assigned each trapped soldier a sequence number starting from 1 and ending at n. If n = 5 and k = 2, then the safe position is 3. Firstly, the person at position 2 is killed, then person at position 4 is killed, then person at position 1 is killed. Finally, the person at position 5 is killed. So, the person at position 3 survives. If n = 7 and k = 3, then the safe position is 4. The people at positions 3, 6, 2, 7, 5, 1 are killed in order, and the person at position 4 survives. Input:n and k Output:Print the list of prisoners in reverse order from n to 1Then reverse the list to print it in correct order from 1 to nDisplay the position number who will survive. You must have to use circular doubly linked list for your solution.

