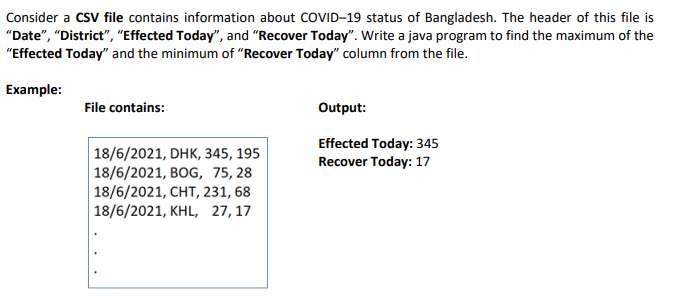
Consider a CSV file contains information about COVID-19 status of Bangladesh. The header of this file is "Date", "District", "Effected Today", and "Recover Today". Write a java program to find the maximum of the "Effected Today" and the minimum of "Recover Today" column from the file. Example: File contains: Output: Effected Today: 345 Recover Today: 17 18/6/2021, DHK, 345, 195 18/6/2021, BOG, 75, 28 18/6/2021, CHT, 231, 68 18/6/2021, KHL, 27,17
Q: Why do many systems have separate code and data caches, and how does the hardware identify whether…
A: Introduction: Set the camera up. Cache memory is a type of auxiliary memory that is closer to the…
Q: The Real-Time Operating System (RTOS) is crucial to the operation of the Internet of Things (IoT).
A: RTOS defines the real time task processing time, interrupt latency, and longer period reliability of…
Q: Is there anything in particular that can be achieved via the use of deep learning?
A: Answer: Deep learning is a subfield of machine learning (ML) that makes use of data that has a…
Q: Investigate the many applications to which information systems are put to use by a wide variety of…
A: Answer to the given question: The Six Most Popular Types of Information Systems and Their…
Q: What does it imply when someone talks about a 4G or 5G phone network?
A: Introduction: The usage of the terms 4G or 5G signifies that the phone connects via a 4G or 5G…
Q: What exactly do "software and hardware environment" and "software and hardware environment" mean?…
A: Introduction: A few examples of hardware include the chassis, central processing unit (CPU),…
Q: In the next part, we will discuss cookies in great length, covering at least four distinct types of…
A: Cookies are small pieces of code that websites save on the user's computer when a session is…
Q: The use of search engines on the internet raises a number of questions, including those pertaining…
A: Please find the detailed answer in the following steps.
Q: What are the most important advantages and disadvantages of keeping data on the cloud, and how do…
A: Cloud computing refers to the deployment of information technology services via the internet on an…
Q: What happens if you push Enter when the focus is on a Button control?
A: Introduction: This inquiry is about what happens if you push Enter when the emphasis is on a Button…
Q: Write a Java program that computes and prints out the sum of 1 + 2 + .. + 100 Note: Your output…
A: Algorithm: 1. Declare value of i,num and sum. 2. Until i is less than equal to num then keep the…
Q: Explain what you mean by the term "learning" in the context of neural networks and computer science.
A: Starting: In general, neural networks perform supervised learning tasks, which include generating…
Q: What is automated testing and how does it work?
A: Introduction: Automated testing is used to determine whether the software generated by the developer…
Q: What is the context of a process (definition and physical objects or information technology data…
A: Introduction: What is the context of a process (definition and physical objects or information…
Q: Note: Provide a copy of the code and screen shot for the output in the solutions’. Explain the…
A: The explanation is given below for the above-given question:
Q: Assembly language and machine language seem to have some kind of connection, but what exactly is it?
A: Assembly language is a low-level programming language designed for immediate communication with…
Q: check the picture and match each of the following points with the technology needed/used in the…
A: This question comes from Artificial intelligence which is a paper of Computer Science. Let's discuss…
Q: Is there any evidence that a distributed denial of service attack has ever been carried out with any…
A: Introduction: A denial-of-service (Dos) attack is a digital attack in which the perpetrator attempts…
Q: computer science - Explain why Bitcoin is regarded as a market disruptor in today's market.
A: Introduction: Bitcoin is regarded as a disruptive innovation in the current market because:
Q: To what degree is the Tag (the MAC) and encrypted data susceptible to being manipulated by an…
A: MAC: A message authentication code (MAC) is similar to a cryptographic hash, except it uses a secret…
Q: Make a contrast between a boot that is chilly and a boot that is warm.
A: Following are the important difference between Cold Booting and Warm Booting Sr. No. Key Cold…
Q: Explain the relevance (or lack thereof) of a TuringEquivalent machine/system or language.
A: Introduction: A Turing equivalent refers to the environment in which it is possible to create an…
Q: Main Street Bank is offering an annual interest rate discount based on the client’s credit score.…
A: // PaymentSchedule.java import java.util.Scanner; public class PaymentSchedule { public static void…
Q: Do breaches of data have the ability to affect how cloud security rules are implemented? What are…
A: Cloud computing security Cloud computing security is a collection of policies, processes, and…
Q: What exactly is SDLC? What are the different stages called?
A: SDLC: Evolution of systems The life cycle is a systematic strategy for delivering a quality system…
Q: What precautions can you take to defend your computer from power surges, and what other steps can…
A: Answer: Power surges are abrupt increases in the quantity of electricity supplied to common…
Q: 03/ Create five row vectors, the first A with 6 random integer numbers between 10 and 30, the second…
A: Find the required code in matlab given as below and output : As per company guidelines we are…
Q: What is the fundamental difference between assembly language and bytecode?
A: Given: Compare, Bytecode: Intermediate level. Not human-readable. Compiler and interpreter required.…
Q: Please provide an illustration of the differences between the client-server architecture and the…
A:
Q: There is a wide range of potential trouble caused by information systems that are not linked to one…
A: Answer: It is a well-known fact that systems generate a constant stream of worries and difficulties.…
Q: USING EMULATOR8086 APPLICATION CREATE THE FOLLOWING Create an assembly program that accepts 2…
A: mov a1, [num1] mov b1, [num2] sub a1, '0' sub b1, '0' add a1, b1 mov edx, 2 ;String length if single…
Q: 5. The following code has several errors. Find out and circle
A: Errors are circled below
Q: What exactly is SDLC, and what are the procedures involved?
A: SDLC: The Software Development Life Cycle (SDLC) is a well-defined procedure for producing…
Q: evel cach _1 memor erage acc =. What is
A:
Q: a. (100pts) Write a program to define a class Car according to the following UML. Please note that…
A: import java.util.Scanner; class Car{ private String name; private int mileage; private…
Q: What precautions can you take to ensure that your computer is safeguarded from extra dangers in…
A: Power Surges: Power surges are sudden increases in the amount of energy provided to typical…
Q: some of the most recent important aspects of Facebook?
A: Introduction : The first of many features is the ability to organize our newsfeed and contacts. If…
Q: When working with big volumes of data, you inevitably run into a number of problems. What are some…
A: Meaning: In an enterprise, big data refers to a large amount of data, which may be organised or…
Q: What are the distinctions between data centre IT security solutions on-premises and cloud security…
A: Introduction: When you use cloud security on a consistent basis, you do not need to make financial…
Q: It is important to investigate Access and Authentication in Information Security.
A: Introduction: Access control is a security method that controls who or what may see or utilise…
Q: Distinguish between the advantages and disadvantages of using concurrent programming. Interaction…
A: Processes and Scheduling: The process manager is responsible for the removal of a running process…
Q: Q:Find F.T for x(t) =- exp(-10|t|) and plot X(f) and Angle(f) ? 9:18 PM
A:
Q: One approach for accomplishing this goal is to make use of VLANs as a vehicle for propagating…
A: Introduction: Network administrators may use VLANs to restrict access to certain workstations to…
Q: Should we think about using many programmes on the computer at once? yes or no? justify your…
A: Given: Step describes whether or not a computer can multitask. Yes, a computer is capable of…
Q: How can you assess how successfully a training programme is being delivered while still ensuring…
A: Answer to the given question: Here are a few explicit tips and procedures to assist you with running…
Q: What exactly does it mean when a DNS refers to a "forward lookup zone," and what function does it…
A: Introduction: A big network server known as a DNS server stores a huge number of IP addresses…
Q: In what ways does the usage of a siloed information system cause problems and difficulties?
A: Introduction: Computer failure and loss are major computer difficulties that lead to excessively…
Q: When making hardware decisions, what three variables are considered?
A: Introduction: The term "hardware" refers to the physical component or device of a system that is…
Q: What is the purpose of learning about computer's personal and social consequences?
A: Introduction: Computers have been shown in studies to have a major influence on a child's…
Q: The effect that quantum computing will have on programming is not entirely understood.
A: Introduction: Quantum computing looks to open up new avenues for dealing with very difficult…
Step by step
Solved in 2 steps with 3 images

- Modify java code for Hw5 (stock,each csv file has headings: Date,Open,High,Low,Close, Adj Close,Volume) to count and print the number of days there is gain (increase from open to close price) of 2% or more of stock price. Also count and print the number of days the High is 30% bigger than Low. Also, find and print the average volume for the trading days where there is gain. Make sure each print occupies a single line, and all lines are lined up such that the label for each information requested is left aligned, and the decimal points are all aligned. import java.util.*; import java.io.*; public class StockData { public static double average(ArrayList<Double> prices) { double total = 0; double average; for (int i = 0; i < prices.size(); i++) { total = total + prices.get(i); } if (prices.size() > 0) { average = total / prices.size(); return average; } else { return 0; } } public static double min(ArrayList<Double>prices) { double min = prices.get(0); for (int i = 1; i…Write a program that receives a coded message file(Lab3ExtraCreditCT.txt) from your local espionage agent and decodes it into a file using standard English. The problem is your agent forgot to tell you the key used to decode the message. Fortunately, this is a simple substitution code consistently using 1 alphanumeric character to represent another, this is case sensitive. All other characters are not substituted, so a space will always be a space, a – will always be a –, a @ will always be a @, etcetera. You may use the following table to help you, it contains the most common letters used in the English language in descending order. E A R I O T N S L C U D P M H G B F Y W K V X Z J Q 0 5 3 2 4 6 8 1 9 7 Using the following key to convert plaintext to coded text: Plaintext = Now is the time for all good men to come to the aid of their country. Key = THEQUICKBROWNFXJMPSVLAZYDG The file your program outputs should look like this: Coded Text = Fxz bs vku vbnu ixp tww…Write a program in Python that reads student information from a text file, then creates a text file that records the course grades of the students and a final grade. Each row of the .txt file contains the Last Name, First Name, Midterm1 score, Midterm2 score, and the Final score of a student, each separated by a space. A sample of the student information is provided in StudentInfo.txt below. Assume the number of students is at least 1 and at most 20. The program performs the following tasks: • Read the file name of the .txt file from the user. • Open the .txt file and read the student information using readline() or readlines(). • Compute the average exam score of each student. • Assign a letter grade to each student based on the average exam score in the following scale: ◦ A: 90 =< x ◦ B: 80 =< x < 90 ◦ C: 70 =< x < 80 ◦ D: 60 =< x < 70 ◦ F: x < 60 • Output the first names, last names, exam scores, and letter grades of the students into a text file named…
- Write a program that reads words from a file (filename given as a string parameter) and prints the occurance of each word(case insensitive). And print the words in alphabetical order. For example, if the file contains text Love is free free is love then the function should print free:2 is:2 love:2 def count_word(filename): # YOUR CODE HERE raise NotImplementedError()Write a JAVA program that reads the student information from a tab separated values (tsv) file. The program then creates a text file that records the course grades of the students. Each row of the tsv file contains the Last Name, First Name, Midterm1 score, Midterm2 score, and the Final score of a student. A sample of the student information is provided in StudentInfo.tsv. Assume the number of students is at least 1 and at most 20. Assume also the last names and first names do not contain whitespaces. The program performs the following tasks: Read the file name of the tsv file from the user. Open the tsv file and read the student information. Compute the average exam score of each student. Assign a letter grade to each student based on the average exam score in the following scale: A: 90 =< x B: 80 =< x < 90 C: 70 =< x < 80 D: 60 =< x < 70 F: x < 60 Compute the average of each exam. Output the last names, first names, exam scores, and letter grades of the…Write a program that reads student information from a text file, then creates a text file that records the course grades of the students and a final grade. Each row of the .txt file contains the Last Name, First Name, Midterm1 score, Midterm2 score, and the Final score of a student, each separated by a space. A sample of the student information is provided in StudentInfo.txt below. Assume the number of students is at least 1 and at most 20. The program performs the following tasks: • Read the file name of the .txt file from the user. • Open the .txt file and read the student information using readline() or readlines(). • Compute the average exam score of each student. • Assign a letter grade to each student based on the average exam score in the following scale: ◦ A: 90 =< x ◦ B: 80 =< x < 90 ◦ C: 70 =< x < 80 ◦ D: 60 =< x < 70 ◦ F: x < 60 • Output the first names, last names, exam scores, and letter…
- Computer Science For each of the code snippet given below, identify the error and then write code after fixing the error. Given code is the simulation of grep -v command. -v prints all lines that do not match a specific pattern. void grep_inverse(char *filename, char *str) { FILE *fp; char buf[buff_size]; fp = fopen(filename, "r"); if(!fp) { perror(filename); } else { while (fgets(buf, buff_size, fp) != NULL) { if ((strstr (buf, str)) != NULL) printf("%s", buf); } } fclose(fp); }Write a C Program which reads the contents of the attached sequential file - customers.txt Print the surname of people who agreed to share their data. This is denoted by the final field in the file (1 for agree, 0 for not agreed). Print the average age of these people (age is the 4th column in the data) Print the average age for people who live in Dublin and have agreed to share their data. This is denoted by the first field in the file. customers.txt New York Dunne 865463389 21 1New York Milford 865438990 22 0New York Mowlds 876765443 24 1New York Wang 873456789 22 1New York Smith 875432234 25 1New York Henry 876654429 22 0New York Gupta 896765443 24 1Los Angeles Monahan 865432245 22 1Los Angeles Brunsdon 865678894 22 1Alabama Tyson 865434566 22 0Alabama Browne 865564766 20 1New York Dunne 890065443 27 1New…Write a java program to read from a text file called “CarList.txt”. The file includes carModel , carYear, and carPrice for an unknown number of Cars. The file uses a comma-separated file format, as the sample below. The program should write New cars only into an output file called “NewCars.txt”. A car is considered new if its year is above 2019. Finally, the program should print the number of new cars, the most expensive car, and the cheapest car at the end of the output file. The format of the output file should be similar to the given sample.
- I have a text file and I want to read it in C++. variables to use: fname, lname , Id nr, Gender and all third line which is an address The file is : Tommy James 23456731667 Streetname 45 , 154 23 Georgia John Andersson 3456723464 Streetname 12 , 231 32 Las Vegas Kim Larsson 3456312653 Streetnamn 15, 231 56 Florida If we Said the 8th digit in ID number is showing the Gender of the person. By %2== 0 it's Male The output should be: Lname Fname [F] address Is there possible to create a program in C++ with the previously output. lname , fname [F]Adress Without have a problem with Las Vegas word. I have a hard time to figure how I can do the third line in the file. They read to word Las and then the compiler shows terminate called after throwing an instance of ' std::invalid_ argument ' what (): stoi aborted so I figured that the problem I have in one line the city is two word.Three employees in a company are up for a special pay increase. You are given a file, say Ch3_Ex5Data.txt, with the following data:Miller Andrew 65789.87 5Green Sheila 75892.56 6Sethi Amit 74900.50 6.1 Each input line consists of an employee’s last name, first name, current salary, and percent pay increase. For example, in the first input line, the last name of the employee is Miller, the first name is Andrew, the current salary is 65789.87, and the pay increase is 5%. Write a program that reads data from the specified file and stores the output in the file Ch3_Ex5Output.dat. For each employee, the data must be output in the following form: firstName lastName updatedSalary. Format the output of decimal numbers to two decimal places.Write a JAVA program to read in a list of electric vehicles. Print out the vehicle with the longest range. Data is stored in the following format: <automobile name><newline><list price><space><range> Here is a sample datafile. File: cars.txt Ford Focus Electric 32103 185 Nissan Leaf S 36398 241 Tesla Model S 97600 536 Kia Soul EV 35895 179 The following is a sample run, user input is shown in bold underline: Enter the input filename: c:/temp/cars.txt Car with the longest range = Tesla Model S Price $97600.00 Range = 536

