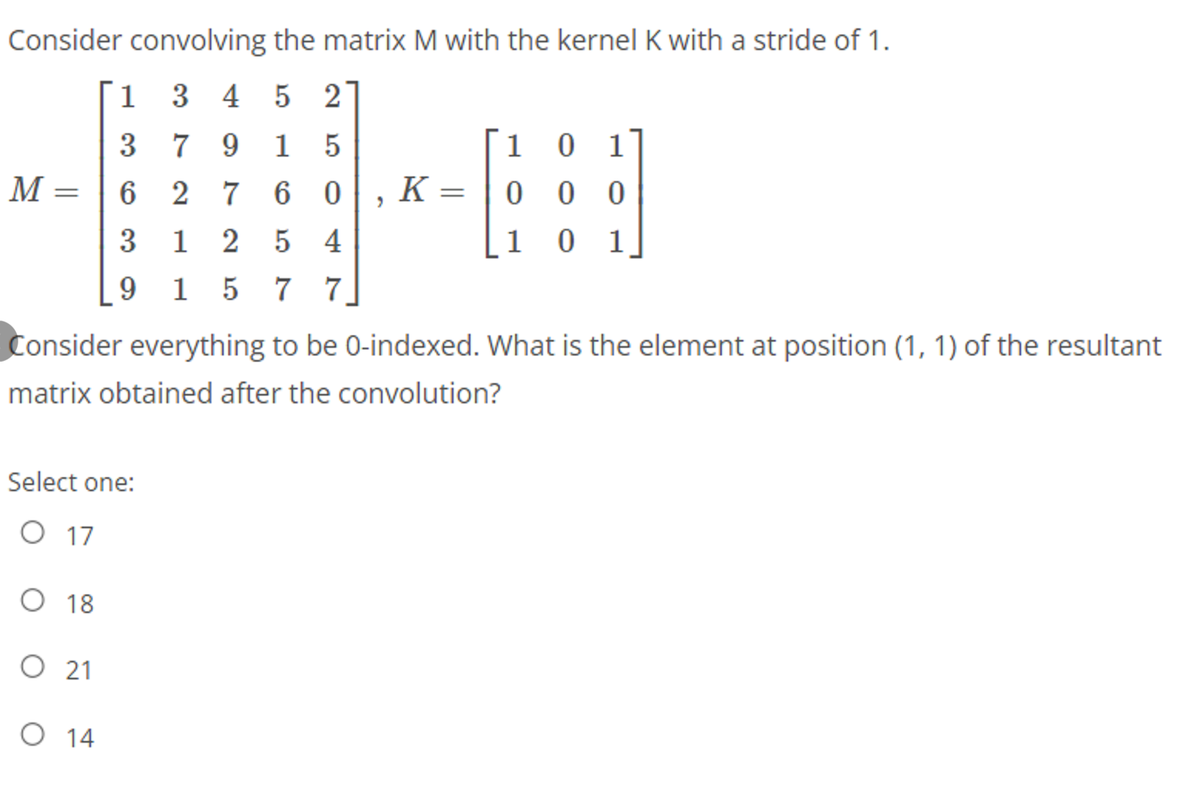
Consider convolving the matrix M with the kernel K with a stride of 1. 1 3 4 5 2] 1 0 1 K = | 0 0 0 3 7 9 1 5 M : 2 7 6 0 3 5 4 1 0 1 1 7 7] 2 5
Q: Which of the following can be used as an activation function in the output layer of a neural…
A: Option Softmax is correct for the above question. The softmax function is utilize as the activation…
Q: What prompted Cisco to switch from a standalone access control system to an IP networked solution? "
A: Foundation: Cisco Network Admission Control (NAC) is a network access control technology developed…
Q: What are case labels?
A: Introduction: A label identifies an individual as a specific type of person. Determining whether an…
Q: Is it possible to define what a digital signature is, and how does it work in practice? When it…
A: Definition: Digital signatures are digital "fingerprints" that securely connect a signer to a…
Q: Is there a computer hardware component that is definitely necessary in a personal computer?
A: The PC is also known as personal computer.
Q: What concerns does database use offer to people's privacy and civil liberties?
A: Start: The purpose of this inquiry is to draw attention to the dangers that databases pose to…
Q: A thorough description of the DNS's functioning, covering iterated and non-iterated queries,…
A: The DNS, often known as the domain name system, is the Internet's top telephone directory. The…
Q: a) What is context switching ? Why it occurs?
A: Only the first question is answerable as per the guidelines of Bartleby. Kindly repost the other…
Q: Computer science Where can I get the finest software deals?
A: Introduction: Computer science Where can I get the finest software deals?
Q: Why are thin clients preferred over desktop computers at a university computer lab, and how do they…
A: Why are thin clients preferred over desktop computers at a university computer lab, and how do they…
Q: Which of the following is the correct boolean expression to test for: int x being a value between,…
A: Boolean Expression: When a Java expression is evaluated, it produces a Boolean value: true or…
Q: When it comes to cloud security, what are the repercussions of a breach? Are there any…
A: Foundation: A data breach occurs when sensitive information is exposed to an unauthorised third…
Q: The following figure respectively shows (a) original image, (b) and (c) two gradient images of the…
A: Answer: An image gradient is a directional change in the force or variety in an image. The gradient…
Q: What's the difference between architecture and organization when it comes to computers?
A: Answer: The most noticeable distinction between computer architecture and computer organization. The…
Q: Explain in detail how and why distributed systems are beneficial.
A: Introduction: Modern computing would be impossible without distributed systems. They are required…
Q: Some individuals find cybercrime fascinating, while others find it repulsive.
A: Cybercrime is becoming more prevalent across all industries. Because these thefts take too much time…
Q: Why should users use health-care websites? In what ways are telesurgery and telemedicine different…
A: Answer The World Wide Web is abbreviated as the Web. The word is widely used on the internet. Anyone…
Q: When developing a new piece of software, how would you choose between ODBC/JBDC and an ORM…
A: JDBC stands for Java Database Connectivity and is an application programming interface that allows…
Q: Distinguish between the allocation schemes for indexed file space, linked allocation, and contiguous…
A: Allocation of Disk Space: Data in the operating system is allotted physical storage space through a…
Q: The camera matrix can be decomposed into a product of two matrices. What purpose does the following…
A: the camera matrix can be decomposed into product of two matrices, what purpose does the following…
Q: Explain how a file management system may provide access to many users to files for the purpose of…
A: GIVEN: Explain how a file management system may provide many users access to files for the purpose…
Q: QUESTION 12 Which of the following instructions will disable all of the interrupts? O a. SEI Ob.…
A: The question is to choose the correct option for the given questions.
Q: Which of the following are valid justifications for using CNNS?
A: which of the following are valid justifications for using CNN
Q: What is WiFi's function in the evolution of computers?
A: Given: Wi-Fi technology may link computers, tablets, cellphones, and other devices to the internet.…
Q: Which of the following is the truncation division operator in Python? A. / B. | C. //…
A: Here Correct answers is a option C) // Explain : // is the operator for truncation division. it is…
Q: Give an example of a protocol handled by that layer's equipment. d) A wireless network…
A: Information: Give an example of a protocol handled by that layer's equipment. d) A wireless…
Q: Find out how access control approaches are categorised. Compare and contrast the various sorts of…
A: Access control systems are categorized as Discretionary Access Control (DAC), Role-Based Access…
Q: Define and invoke the constructor for a HashSet variable named colors capable of holding strings.
A: Introduction: The Hashtable category allows you to organise knowledge using a user-defined key…
Q: What three variables are considered while making a hardware purchase?
A: let us see the answer:- Introduction:- When choosing computer hardware and software, the following…
Q: Compile a list of all the databases that have information about you. Each database's data collection…
A: Introduction A person's name, signature, home address, email address, telephone number, date of…
Q: Explain the sentence “Lower layer protocols encapsulate higher-layer data”
A: When data is moving in the OSI or TCP/IP model, encapsulation is the process of adding additional…
Q: Given a coding scheme. a:000 e:001 i:01 k:1100 0:1101 p:11110
A: Tree that represent coding scheme: The tree that represent the coding scheme can be draw by using…
Q: In descriptive analytics, OLAP plays a different function from OLAP in the data warehouse.
A: OLAP is also known as online analytical processing.
Q: 8.10 Write the exact output.
A: A piece of code is given:
Q: What are the benefits and drawbacks of building software with "good enough" quality?
A: Introduction: The benefits of building software with "good enough quality" are as follows.…
Q: If an LSTM had 82432 learnable parameters, how many learnable parameters would a GRU with the same…
A: Answer in step 2
Q: Distinguish between the functions of OLAP and descriptive analytics.
A: Although OLAP engines make it simple to conduct operations such as slicing, dicing, drill-down,…
Q: Describe the steps involved in creating the smallest transport-layer protocol.
A: The following technique details how to create the simplest possible transport-layer protocol:
Q: Evaluate the given Computer Expressions below: Suppose the value of A = 10; B = 15; C = 20.50; D =…
A: INTRODUCTION: Here we need to tell the answer of the given computer expression. According to…
Q: Computer science Distinguish between chain of evidence and chain of custody and provide instances of…
A: Introduction: Forensic science begins at the crime scene, where vital information may be gathered in…
Q: Which of the following is FALSE regarding a Disk-Oriented DBMS architecture?
A: which of the following is FALSE regarding a Disk oriented DBMS architechture
Q: How secure is your database? How can you safeguard your database in two ways?
A: Database security refers to the protection of sensitive data and the avoidance of database data…
Q: Why is it so vital for systems analysts to keep a record of the needs of end users?
A: Introduction: Understanding the user's requirements, as well as system design, is essential for the…
Q: A text box can be inserted into an image using a group of text correct Error O
A: Answer: A text box can be inserted into an image using a group of text correct A paragraph…
Q: What are the long-term consequences of a data breach on cloud security? What steps can be taken to…
A: Given: The most severe long-term impact of a data breach is the loss of customer trust. Customers…
Q: Is it possible that the optimum page replacement method will be affected by Belady's anomaly? Please…
A: Optimal Page Replacement: All algorithms seek to decrease the amount of page defects. In this…
Q: Data breaches may have serious consequences for cloud security, but many people don't realise it. If…
A: Compromise of Cloud Data: When secure/confidential information is purposefully or inadvertently…
Q: Explain the level of access in the context of records management concisely and with examples (based…
A: The level access to the record management
Q: Explain what happened in the data breach that was previously stated in your own words.
A: A data violation is a cyber attack that gains unauthorized access and reveals sensitive,…
Q: ry, that people and inform
A: If you have to, show that people and information: systems are the driving drivers behind mechanical…
29
Step by step
Solved in 2 steps with 2 images

- If there is a non-singular matrix P such as P-1AP=D, matrix A is called a diagonalizable matrix. A, n x n square matrix is diagonalizable if and only if matrix A has n linearly independent eigenvectors. In this case, the diagonal elements of the diagonal matrix D are the eigenvalues of the matrix A. A=({{1, -1, -1}, {1, 3, 1}, {-3, 1, -1}}) : 1 -1 -1 1 3 1 -3 1 -1 a)Write a program that calculates the eigenvalues and eigenvectors of matrix A using NumPy. b)Write the program that determines whether the D matrix is diagonal by calculating the D matrix, using NumPy. #UsePythonGiven the complement of a graph G is a graph G' which contains all the vertices of G, but for each unweighted edge that exists in G, it is not in G', and for each possible edge not in G, it is in G'. What logical operation and operand(s) can be applied to the adjacency matrix of G to produce G'? AND G's adjacency matrix with 0 to produce G' XOR G's adjacency matrix with 0 to produce G' XOR G's adjacency matrix with 1 to produce G' AND G's adjacency matrix with 1 to produce G'Consider the following pair of adjacency matrices.1. Draw the simple graphs associated with each of the above adjacency matrices.2. Check whether those two simple graphs are isomorphic. Show your work. 1 0 1 1 1 0 0 1 1 1 0 1 1 1 0 0 1 1
- Type in Latex **Problem**. Let $$A = \begin{bmatrix} .5 & .2 & .3 \\ .3 & .8 & .3 \\ .2 & 0 & .4 \end{bmatrix}.$$ This matrix is an example of a **stochastic matrix**: its column sums are all equal to 1. The vectors $$\mathbf{v}_1 = \begin{bmatrix} .3 \\ .6 \\ .1 \end{bmatrix}, \mathbf{v}_2 = \begin{bmatrix} 1 \\ -3 \\ 2 \end{bmatrix}, \mathbf{v}_3 = \begin{bmatrix} -1 \\ 0 \\ 1\end{bmatrix}$$ are all eigenvectors of $A$. * Compute $\left[\begin{array}{rrr} 1 & 1 & 1 \end{array}\right]\cdot\mathbf{x}_0$ and deduce that $c_1 = 1$.* Finally, let $\mathbf{x}_k = A^k \mathbf{x}_0$. Show that $\mathbf{x}_k \longrightarrow \mathbf{v}_1$ as $k$ goes to infinity. (The vector $\mathbf{v}_1$ is called a **steady-state vector** for $A.$) **Solution**. To prove that $c_1 = 1$, we first left-multiply both sides of the above equation by $[1 \, 1\, 1]$ and then simplify both sides:$$\begin{aligned}[1 \, 1\, 1]\mathbf{x}_0 &= [1 \, 1\, 1](c_1\mathbf{v}_1 +…The parts (a) and (b) of this problem are independentof each other.G1 G24 51 236sx yt u v(a) Prove that the graphs G1 and G2 are isomorphic byexhibiting an isomorphism from one to the other byconcrete arguments and verify it by using adjacencymatrices. Please take the ordering of the vertices as1, 2, 3, 4, 5, 6 while forming AG1, adjacency matrix ofG1.Warning: One must stick to the labelings ofthe vertices as they are given, if one changesthe labelings/orderings etc., the solution willnot be taken into account.(b) Consider the complete graph K13 with vertex setV13 = {u1, u2, u3, · · · , u13}.Let H = (V, E) be the simple graph obtained fromK13 by adding a new vertex u, i.e. V = V13 ∪ {u}and deleting the edges {u1, u2} and {u2, u3} andadding the edges {u1, u} and {u, u2} and keepingthe remaining edges same.Determine whether H has an Euler circuit or not,an Euler path or not. One must validate any conclusion by clear arguments.Given the adjacency matrix of an undirected simple graph G = (V, E) mapped in a natural fashion onto a mesh of size n2, in Θ(n) time a directed breadth-first spanning forest T = (V, A) can be created. As a byproduct, the undirected breadth first spanning forest edge set EA can also be created, where EA consists of the edges of A and the edges of A directed in the opposite direction.give proof of theorem.
- Consider now the interchange of 1 and 8, so that the new base will be[9, 8, 1, 10, 2, 12].We require the generators for ~(3)=G98. The orbit of 8 under G (2) =G 9 is{ 8,10,11,13,14,16,21 }, and so we calculate that' I A (3) I = 7. Initially,A= {1}, F= {2..7}, andT= {$3,S5,$6}.Choosing T = 2 from F givesg I = s7 = (1,2,3,4,6,5,7).Then 8 gl-t = 8, sog2 is the identity, and we add s7 to T. Thus,A = {1..7}, F= empty, and T= {s3,ss,s6, sT}.Since A has the correct size, we are finished.The new strong generating set is the same as the old. By checking not only S (/+2) but alsoS (/) for elements that fix 13j+1, we could have saved ourselves the trouble of duplicatingpermutations already in S. This simple improvement is used in implementations, We leave itas an exercise for the reader to make the necessary modifications to Algorithm 3.Analysis of Interchanging Base PointsLet G = (V, E) be a connected, undirected graph, and let s be a fixed vertex in G. Let TB be the spanning tree of G found by a bread first search starting from s, and similarly TD the spanning tree found by depth first search, also starting at s. (As in problem 1, these trees are just sets of edges; the order in which they were traversed by the respective algorithms is irrelevant.) Using facts, prove that TB = TD if and only if TB = TD = E, i.e., G is itself a tree.Algorithm for Normalizing GeneratorInput: a permutation group H with base B=[~I ,~2, -.-., 13k],strong generating set T, Schreier vectors v t~ , and basic orbits A (i) ;a permutation y normalizing H;Output: a base for K = <H,y> which may extend B;a sequence of elements [g 1 ,g 2 ..... gr] such that, for each j,(a) T L.) {gj,gj+l ..... gr } is a strong generating set of <H, gj,gj+l ..... gr >,(b) gj ~ <H, gj+l,gj§ ..... gr>,(c) gi normalizes <H,gj§ ,g/+2 ..... gr>, and(d) gp ~ <H, gj+l,gj+2 ..... gr>, for some prime pj;
- Let C be an (n, k) linear code over F such that the minimum weightof any nonzero code word is 2r + 1. Show that not every vector ofweight t + 1 in Fn can occur as a coset leader.Given the adjacency matrix of an undirected simple graph G = (V, E) mapped in a naturalfashion onto a mesh of size n2, in Θ(n) time a directed breadth-first spanning forest T = (V, A) can becreated. As a byproduct, the undirected breadth-first spanning forest edge set EA can also be created,where EA consists of the edges of A and the edges of A directed in the opposite direction.for G such that1. cq,0c2 ..... cx r e A, and2. G c~l,0h ..... ct, is the pointwise stabilizer of A in G.Applying the base change algorithm if necessary, we may assume a strong generating set S ofU relative to B is known.Let us return to the above example where G is the symmetries of the square acting on pairs ofpoints and A is A 1 , the set of edges of the square. The points (x I =1 and cz2=3 form a base forG, so G1,3 = G1,3,4,6 = < identity > (and s=0). Hence, ~1 =1 and ~2=2 form a base for imrThe stabiliser G 1 is generated by b• so {a,b,bxa} is a strong generating set of Grelative to the chosen base. Furthermore, the stabiliser of 1 in imr is generated by bxa=(2,3).Hence, the set of images { -d, b, bxa } = { (1,3,4,2), (1,2)(3,4), (2,3) } is a strong generatingset of im(p relative to the base [1,2]. The kernel of the homomorphism is the trivial subgroup,< identity > perform each of the basic tasks :











