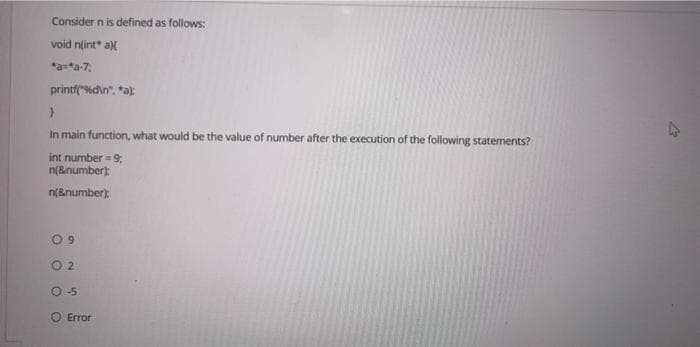
Consider n is defined as follows: void n(int* ax *a-*a-7; printf("%d\n", *a); } In main function, what would be the value of number after the execution of the following statements? int number = 9; n(&number); n(&number); 09 02 O-5 O Error
Q: In terms of network security, what does the term "firewall" signify and how is it used in network…
A: A firewall is a software or firmware that blocks unauthorized access to a network. Monitors incoming…
Q: How can one guarantee the evolution of old systems?
A: Reverse Engineering and Re-engineering ensure that legacy systems continue to develop in their…
Q: What does a firewall do, and how can it benefit your company?
A: In answer to your query, A firewall is a security system that prohibits unauthorized access. It…
Q: In C- I am creating a word jumble game and till now I have come up with a function that will jumble…
A: I am attaching the modified code in C in the next step:
Q: Q1/Design the program to calculate the value of (M) from the equation below: M=B+2 10³ sech A 1.x…
A: Answer has been explained below:-
Q: What is the length of the following string? string str="BulSU"; cout << str.length();
A: answer is
Q: What is the reason for limiting the number of iterations in the waterfall model?
A: Introduction In the waterfall approach, iterations are restricted. The waterfall model divides…
Q: rers, and note which brands receive better ratings overall, and how performance compares across…
A: Research memory producers, and note which PC brands get better appraisals by and large. Some memory…
Q: Applying the concept of Zeller's congruence discussed earlier, solve for the day of the week of…
A: Christian Zeller created the Zeller's congruence algorithm to determine the day of the week for any…
Q: 6.5 For each of the following write a. Create a list of the first 10 multiples of 13 (from 13 to…
A: Python program for list comprehension: # List comprehension of first 10 multiples of 13 multiples =…
Q: If a user phones the help desk and says, "My computer won't boot," a smart help desk technician…
A: My Computer Won't Boot: If your computer won't turn on, check sure it's connected in and that the…
Q: answer the following questions: 1: A dictionary is an unordered collection of key-value pairs. True…
A: answer along with output screenshot is given
Q: What are some instances of dynamic programming?
A: Dynamic programming: When it comes to dealing with design issues that include optimization, the most…
Q: Included should be a list of the five most prevalent types of network topologies. Which one do you…
A: Institution: 1) It performs better than Bus since signals aren't sent to all workstations. A message…
Q: Your manager believes that doing integration tests is a pointless use of time. Integration testing…
A: Introduction: Integration testing (sometimes known as integration and testing, or I&T) is a kind…
Q: Using Python: Write a loop that appends numbers to the list. The numbers should be the squares of…
A: NOTE - As per our guidelines, I have solved the first question. Please repost the other questions…
Q: Provide samples for each of the three most used file management methods.
A: Given: Give instances of each of the three main techniques to file management. Ordinary files,…
Q: To better understand the distinction between ethics in engineering and ethics in computing, please…
A: Start: Ethics is a collection of moral rules that regulate an individual's or a group's conduct. The…
Q: Should we link the CPU to the RAM via an asynchronous or synchronous bus? Please include an…
A: A bus is a standard communication connection that connects numerous subsystems via…
Q: What are the similarities and differences between the iterative and incremental approach and the…
A: Waterfall Model:- The waterfall model is one of the most common models used in software development.…
Q: w may a firewall be used to pro
A: Introduction: Below how a firewall be used to protect your data
Q: Provide an evaluation of whether Nestle is an open or a close system and how a change in one…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. A quality…
Q: Is there a particular reason why we need to have system engineering done? How can the engineering of…
A: Launch: Systems engineering is an interdisciplinary field of engineering and engineering management…
Q: When you switch on your computer, you are greeted with the whirring sound of the fans that are…
A: The system unit is part of the computer that houses the primary hardware devices to do critical…
Q: 2. Keep only the last three lines of a file and delete others. If there are less than three lines in…
A: Answer
Q: What actions does the attacker need to do in order for a sniffer attack to be successful? How may an…
A: Answer:
Q: What are the three components that a network absolutely has to have in order to function properly…
A: Performance, dependability, and security are the three most essential requirements for network…
Q: Matlab (or Python) must be used to do the computations in this project. Please refer to the Matlab…
A: Code: A=[6 -1 11;0 13 -16;0 8 -11]; B=[13.5;27.0;13.5]; C=[6.70 6.00 -7.20;-2.40 -4.10…
Q: One aspect of a simulated annealing cooling schedule is the temperature. i. Explain the effect of…
A: Answer
Q: What factors contribute to the evolution of an information system's overall scope?
A: let us see the answer:- Introduction:- (information systems for corporate management) has been and…
Q: When using Windows Server, what sort of firewall program do you have on your computer?
A: Firewall A Firewall is an network security gadget that screens and channels approaching and active…
Q: Compare and contrast the traditional Waterfall model with the more modern Rational Unified approach.
A: Waterfall Model is the oldest model used throughout the development life cycle to build a system in…
Q: Match the advantages of the Java Collection Framework to its respective description. a. Performance…
A: answers: a)Performance - The collection framework creates extremely effective and efficient data…
Q: What are the advantages and disadvantages of each successive generation of networking technology?
A: Generation of Networking Technology: Each Generation is characterized by a collection of telephone…
Q: What are the three basic components for a network to operate properly?
A: Network architecture components include hardware, software, transmission media, network topology and…
Q: Think about the concept of computational complexity that we discussed in class and explain what we…
A: The computational complexity or in simple words the complexity of an algorithm is the number of…
Q: In the waterfall approach, why is the number of iterations restricted? This begs the issue of why…
A: Answer:
Q: Which of the following statements is not valid in Python? subjects = ["Math", "Science", "English"]…
A: For option a): Python Program: subjects = ["Math", "Science", "English"] students = {1: "Joseph", 2:…
Q: Let P(x) denote "x + 225", find the truth values for the following compound propositions: a) P (1) V…
A:
Q: Binary Search Tree. Perform the following operations and instructions. a. Insert the following in…
A: Answer
Q: Which three requirements must be satisfied by a network in order for it to function in a manner that…
A: Introduction: Here we are required to explain three requirements that must be satisfied by a network…
Q: mts (not necessari 19. 12. 30
A: class Series { public static void main(String[] args) { for(int i=1;i<=30;i++){…
Q: Counter Update" button is clicked, the counter should be incremented by 1 and set in the…
A: Given:
Q: What are some possible causes that result in a video monitor not displaying any output?
A: Video monitor: A piece of hardware consisting of a display screen that is capable of displaying…
Q: Is there a specific role that WiFi plays in the advancement of computer technology?
A: Launch: Wi-Fi technology allows computers, tablets, telephones, and other devices to connect to the…
Q: What exactly is the purpose of a firewall, and how exactly does one get set up?
A: A firewall's functions include: Keep track of the user's activities. When a network user accesses…
Q: paper factory: which six instructions may be chained together to form the design.
A: Answer: Each processor in the chain will have its own implementation when it comes to processing a…
Q: Give the Adjacency Matrix and Adjacency List based on the graph below: 4 A B 5 D 1 10 2 E C 8
A:
Q: Discuss in some detail the three types of testing: unit testing, integration testing, and system…
A: A software development life cycle or SDLC is a process that defines different stages that are…
Q: What other types of firewalls are there than those that are based on a network?
A: Network: A network is a collection of computers, servers, mainframes, network devices, peripherals,…
Step by step
Solved in 3 steps with 1 images

- In C++ write a program that generates three random numbers and then find the min number among the generated values, using these three functions: void getrandnum(int &n1, int &n2, int &n3), int findMin(int n1, int n2, int n3), and void printResult(int n1, int n2, int n3, int min). Make the main function drive all these functions.int p =5 , q =6; void foo ( int b , int c ) { b = 2 * c ; p = p + c ; c = 1 + p ; q = q * 2; print ( b + c ); } main () { foo (p , q ); print p , q ; } Explain and print the output of the above code when the parameters to the foo function are passed by value. Explain and print the output of the above code when the parameters to the foo function are passed by reference. Explain and print the output of the above code when the parameters to the foo function are passed by value result. Explain and print the output of the above code when the parameters to the foo function are passed by name.Create a program that accepts an integer N, and pass it to the function generatePattern. generatePattern() function which has the following description: Return type - void Parameter - integer n This function prints a right triangular pattern of letter 'T' based on the value of n. The top of the triangle starts with 1 and increments by one down on the next line until the integer n. For each row of in printing the right triangle, print "T" for n times. In the main function, call the generatePattern() function. Input 1. One line containing an integer Output Enter N: 4 T TT TTT TTTT
- 1.Write a Java program to print 'Hello' on screen and then print your name on a separateline.Expected Output:HelloDonald Trump2. A school has following rules for grading system:a. Below 25 - Fb. 25 to 45 - Ec. 45 to 50 - Dd. 50 to 60 - Ce. 60 to 80 - Bf. Above 80 - AAsk user to enter marks and print the corresponding grade.3. Create a function that takes two numbers as arguments and returns the GCD of the twonumbers.Examplesgcd(3, 5) ➞ 1gcd(14, 28) ➞ 14gcd(4, 18) ➞ 24. Given an integer, create a function that returns the next prime. If the number is prime,return the number itself.ExamplesnextPrime(12) ➞ 13nextPrime(24) ➞ 29nextPrime(11) ➞ 11// 11 is a prime, so we return the number itself.5. Write a Java program that takes two numbers as input and display the product of twonumbers.Test Data:Input first number: 25Input second number: 5Expected Output:25 x 5 = 125 Page 2 of 4 6. Write a Java program to print the sum (addition), multiply, subtract, divide and remainderof two numbers.Test…Write a function(define) the_divisor(n, bound), that takes in two int values. N is the number you search for a divisor and bound will also be an integer. The function the_divisor should return the smallest divisor which is greater than bound. If no such integers exists, return -1. You cannot assume that the first argument will be larger than the second. In python >>> the_divisor(25,3) 5 >>>the_divisor(5,25) -1Write a function (define) the_divisor(n, bound), that takes in two int values. N is the number you search for a divisor and bound will also be an integer. The function the_divisor should return the smallest divisor which is greater than bound. If no such integers exists, return -1. You cannot assume that the first argument will be larger than the second. In python >>› the_divisor (25,3) 5 >>>the_divisor (5,25) -1 >>>the_divisor(25,5) 25
- code in python (A) please Solve the so-called "Birthday Problem". Write a program that takes an integer ?N and uses the function np.random.randint (low = 0, high = N) from numpy to generate a random sequence of integers between 00 and ?−1N−1. Run experiments to validate the hypothesis that the number of integers generated until the first repeated value is approximately ?∗?2⎯⎯⎯⎯⎯⎯⎯√π∗N2. a) Write a function birthday(N) that returns the number of values generated until a value is repeated as a function of the range of possible values ?N (from 00 to ?−1N−1); b) Write a function birthday_sim(N) that repeats birthday(N) a total of n_sim = 20000 times and returns the average of all the numbers generated; c) Show on one plot that as ?N increases (with a doubling experiment), from ?=2N=2 to ?=1000N=1000, the value of birthday_sim(N) approaches ?∗?2⎯⎯⎯⎯⎯⎯⎯√π∗N2.In Java: Develop a void function that takes two integers and prints whether the first number is divisible by the second. For example, with arguments 51 and 17, the function should print “51 is divisible by 17”. With arguments 17 and 8, the function should print “17 is not divisible by 8”. Call the function twice with different arguments to show each possible result. What happens when the second argument is greater than the first?Implement in C Programming 6.10.2: Pass by pointer. Write a function call to ConvertMoney() to store the number of quarters, nickels, and pennies within the integer variables numQuarters, numNickels, and numPennies, respectively. Ex: If the input is 133, then the output is: Quarters: 5 Nickels: 1 Pennies: 3 #include <stdio.h> void ConvertMoney(int totalPennies, int* numQuarters, int* numNickels, int* numPennies) { *numQuarters = totalPennies / 25; totalPennies = totalPennies % 25; *numNickels = totalPennies / 5; totalPennies = totalPennies % 5; *numPennies = totalPennies;} int main(void) { int totalPennies; int numQuarters; int numNickels; int numPennies; scanf("%d", &totalPennies); /* Your code goes here */ printf("Quarters: %d\n", numQuarters); printf("Nickels: %d\n", numNickels); printf("Pennies: %d\n", numPennies); return 0;}
- 1 - Nuclear Power Plant (python) The nuclear powerplant at Threeyedfish will automatically run a program to print a warning message when the reactor core becomes unstable. The warning message reads: NUCLEAR CORE UNSTABLE!!! Quarantine is in effect. Surrounding hamlets will be evacuated. Anti-radiationsuits and iodine pills are mandatory. Since the message contains crucial information, it should be printed three times. To do this, write a function that prints this message. This function has to be used three times.In java Develop a function that takes two integers and returns the sum of the values from the first to the second (the two inputs may be in any order). Call the function at least twice with different arguments Develop a void function PrintLineOfChar that accepts a single character and an integer. The function prints a single line of the character repeated the integer number of times. Call the function at least twice with different arguments.Consider the following function: double mystery(int x, double y, char ch){if (x > 0 && isupper(ch))return(sqrt(x * 1.0) + (static_cast<int>(ch) - 65));elsereturn(pow(y,3) + x + static_cast<int>(ch));}What is the output of the following C++ statements? (Assume that the output of decimal numbers is set to two decimal places.)a. cout << mystery(16, 2.0, 'A') << endl;b. cout << mystery(5, 3.0, '*') << endl;c. cout << mystery(-7, 2.5, 'T') << endl;

