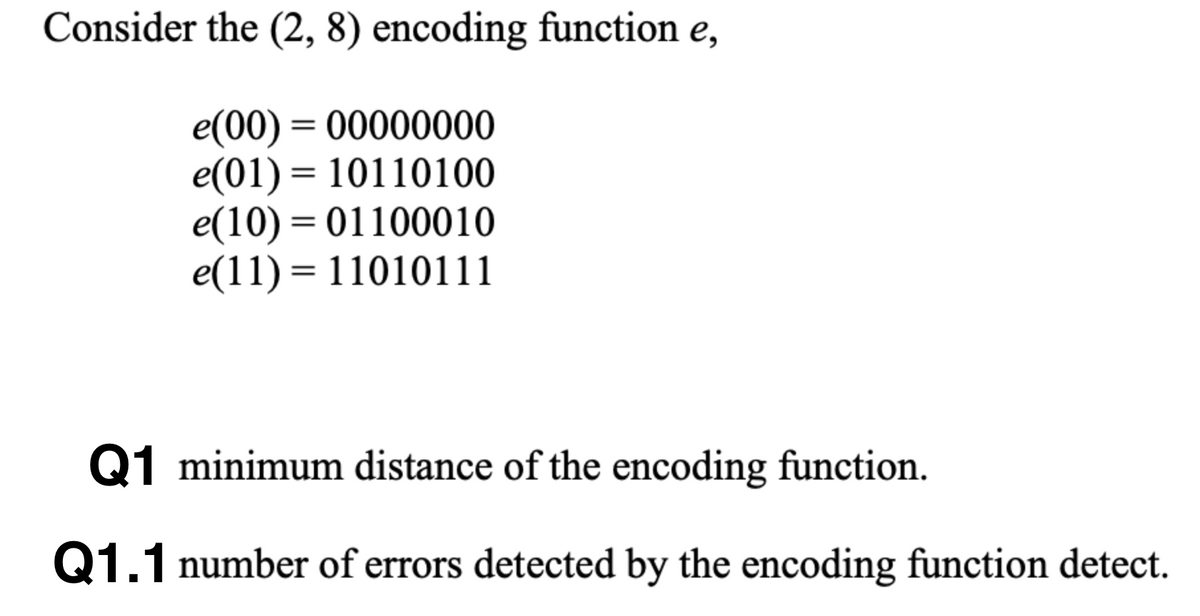
Consider the (2, 8) encoding function e, e(00) = 00000000 e(01) = 10110100 e(10) = 01100010 e(11) = 11010111 Q1 minimum distance of the encoding function. Q1.1 number of errors detected by the encoding function detect.
Q: int bof(char *str, int size) { char *buffer = (char *) malloc(size); strcpy(buffer, str); ...
A:
Q: Print the two strings, firstString and secondString, in alphabetical order. Assume the strings are l...
A: import java.util.Scanner;class OrderStrings { public static void main(String [] args) { Scann...
Q: Write a program that prompts the user to enter the month and year and displays the number of days in...
A: Introduction: Here we are required to make a C++ program that hat prompts the user to enter the mont...
Q: An 100 Mbps (mega-bit-per-second) is the most popular Ethernet standard. How many bits are in. trans...
A: Hey there, I am writing the required solution for the above metioned question. Please find the expla...
Q: A router receives a packet from another network for device in the local network that the router serv...
A: Solution:
Q: If expected value is not found as result of formula, which of the following error would appear? 1. ...
A: Let us see the answer:-
Q: Draw appropriate UML class diagram for Banking Management System. Banking Management System Class Di...
A: Actually, Unified Modeling Language (UML) is a general purpose modelling language. UML defines a sta...
Q: What are three ways you use computers and information systems in your daily life?
A: The solution for the above-given question is below:
Q: How do you set permissions in Linux using PuTTY for each shared directory so only the users and grou...
A: How do you set permissions in Linux using PuTTY for each shared directory so only the users and grou...
Q: What is the definition of a wireless network?
A: Introduction: A wireless network allows devices to stay connected to the network while roaming freel...
Q: A string is called a palindrome if it reads the same when reversed. That is, the string x1 x2 ... xn...
A: The solution for the above given question is given below:
Q: Write a python program that generates all the permutations of an ordered set that that do not have i...
A: Algorithm: Start Import permutations for itertools Initialize a list s with [1,2,3,4,5] Using permu...
Q: Design a complete GUI Application with as many components as combination of different layout Manager...
A: Given Laboratory 4 GUI (Graphical User Interface) in Java Cont... Activity 1: Design a complete GUI ...
Q: Let T1, T2 be 2-3-4 trees and let x be a key [in neither T1, T2], such that for each pair of keys x1...
A: Let T1, T2 be 2-3-4 trees and let x be a key [in neither T1, T2], such that for each pair of keys x1...
Q: Develop following C++ functions using doubly linked list (1) Find a key value from the user (2) Find...
A: Given:
Q: Problem 1 Write programs that ask to add a number entered by user. Ask the user to continue to add a...
A: In the above question, add two number entered by user and continue till user enter n.
Q: Students in a basic statistics class are allowed to take as much time as needed on their final exam....
A: Students in a basic statistics class are allowed to take as much time as needed on their final exam....
Q: What distinguishes wireless connections from their wired counterparts?
A: Introduction: We've discussed wireless connections and their wired equivalents, as well as how they ...
Q: Describe the functioning of a transparent latch.
A: Data storing is important when we want to store it permanantly.
Q: How can I take out data from the get request in JavaScript. Assume the get request has email and pas...
A: Required:- How can I take out data from the get request in JavaScript. Assume the get request has em...
Q: Problem 1 Write programs that ask to add a number entered by user. Ask the user to continue to add a...
A: The above question that is to write a pogram thata ask to add a number entered by user and ask the u...
Q: Essentially, if we want to trace the dependency and precedence paths of each input or calculation, a...
A: A node in a network has dependencies and paths. The precedence paths are those which have a dependen...
Q: What is the most affordable firewall?
A: Answer: There are many most affordable firewall has show in below:- 1. Fortinet 40F.
Q: te An SQL Query To Fetch “FIRST_NAME” From Worker Table Using The Alias Name As <WORKER_NA
A: Lets see the solution.
Q: ii) Write a JAVA program to input the elements of an integer array of size 10 and then print the sum...
A: Java Program: import java.util.*;class Numbers { public static void main(String[] args) { ...
Q: What distinguishes social engineering from other types of attacks?
A: Introduction: The skill of obtaining sensitive information from individuals is known as social engin...
Q: What is Cyber warfare attack? If two conties have conflicts, affects of Cyber warfare on the count...
A: The solution to the given problem is below.
Q: Implications of the study "An Examination of the Health Effects of Gadget Use"
A: Mobile phone use. Social media and the internet have altered people's perceptions of the world. Almo...
Q: Suppose that there are m students who want to take part in n projects. A student is allowed to join ...
A: In this m students wants to take part in n project only if they pass the criteria of the project. ...
Q: Find the power set of {apples, oranges}.
A: Here we have to find the power set of {apples, oranges}
Q: Addition of two characters in c programming
A: Introduction: There are several methods for concatenating characters as a String rather than interpr...
Q: ual testing?
A: given - What part does documentation play in manual testing?
Q: PARTITION(A, p,r) A[r] 2 i = p – 1 3 for j = p to r – 1 if A[j] < x i = i + 1 1 x = - 4 5 exchange A...
A: For better understanding, I have written the code. The main solution is in Step 2
Q: Program 1 - Translate the following C program to Pep/9 assembly language. #include int main() { int...
A: The Pep/9 computer is a 16-bit complex instruction set computer (CISC). It is designed to teach comp...
Q: write c++ program of 2d array Marks , average and names of 3 students in 3 subjects using if else.
A: #include <iostream> using namespace std; int main(){ char student[3][9] = { "Student1", "St...
Q: Write a ruby program to truncate a user taken string to the first n words and n should be taken from...
A: Let's see the solution in the next steps
Q: 3 ex+lo g(= sin(x+y)-
A: Public Class Form1 Private Sub Button1_Click(sender As Object, e As EventArgs) Handles Button1.Cl...
Q: Why is revision history an important feature to utilize during group activities? (Select all that ap...
A: Answer
Q: 3. Let A = {1, 2, 3} and B = {4,5}. %3D a) Find A x B b) Find B x A
A: A = {1, 2, 3} B = {4, 5} A*B = {1, 2, 3} * {4, 5} A*B = {(1, 4), (1,5), (2, 4), (2,5), (3, 4),(3, 5...
Q: In how many ways the data is represented and what are they?
A: Introduction: A name, a number, the colors in an image, or the notes in a musical composition are al...
Q: Why do we utilize defense mechanisms? What is its overall purpose?
A: Why do we utilize defense mechanisms: We utilize defensive mechanisms to defend ourselves from emoti...
Q: How can I take out data from the get request in JavaScript. Assume the get request has email and pas...
A: Required:- How can I take out data from the get request in JavaScript. Assume the get request has em...
Q: Which type of language contains commands like this? xor eax,eax A. Machine Code B. Interpreted Langu...
A: Answer : D. Low-level Language
Q: Consider sending real-time voice from Host A to Host B over a packet-switched network (VolP). Host A...
A: Here, I have to provide a solution to the above question.
Q: What is a release process, and how does it work? What is the significance of version control?
A: What is a release process, and how does it work? What is the significance of version control?
Q: Static random access memory (SRAM) is defined as follows
A: Introduction: SRAM (static RAM) is a kind of random-access memory (RAM) that holds data bits in its ...
Q: How can I calculate entropy, average code length and compression ratio in Python.
A: 1. Entropy def entropy(labels): """Computes entropy of 0-1 vector. """ n_labels = len(label...
Q: Designing stack structures, accumulator architectural designs, and general-purpose register architec...
A: On the basis of registration Possesses a pool of registers, each of which has a purpose (meaning the...
Q: Is aa distinguishable from the string a with respect to the set of strings over {a,b} that end with ...
A: 4) Strings w1 and w2 are distinguishable with respect to language L iff there exists some z in S*(se...
Step by step
Solved in 2 steps with 1 images

- Let be the discrete source on the alphabets {I, B, D, R, .} which defines a series of 5 possible characters. These characters occur with probabilities of: I= 0.3, B=0.25, D=0.2, R=0.15 and . = 0.1. c) Find the number of bits/symbol in this encoding technique. d) Show how your solution would be decoded.Let be the discrete source on the alphabets {L, F, G, A, .} which defines a series of 5 possible characters. These characters occur with probabilities of: L= 0.3, F=0.25, G=0.2, A=0.15 and . = 0.1. 1-Encode the Word “FLAG” using arithmetic coding compression. 2-Find the output Code Word.We compress the video with the pattern GoP (16 : 3) by using MPEG coding. Assume that the average compression ratios of frame I, frame P, and frame B are 1:5, 1:20, and 1:60, respectively. We put the compressed frames in 512 B packets and send them. The header size of each packet is 5% of the size of packet. Each packet contains information on one frame and its header, Each frame can be sent in multiple packets. Picture resolution is 196 × 144 for a video at 32 fps. (a)What is the compression ratio in this pattern? (b)What is the order of coding and transmitting frames in this pattern? (c)If frame 6 is lost while transmission, which frames will be faulty? (d)If frame 5 is lost while transmission, which frames will be faulty? (e)If frame 17 is lost while transmission, which frames will be faulty? (f)Find the size of uncompressed image frame? (g)In how many packets can an I-frame be transmitted on average? (h)In how many packets can an I-frame be transmitted on average? (i)In how many…
- #45.! Consider the following bit stream-a. 00000000 b. 11111111 c. 01010101 d. 00110011 Draw the graph of the i. Manchester using each of the given data streams, assuming that the last signal level has been positive. From thegraphs, guess the bandwidth for this scheme using the average number of changes in the signal level... .Consider the following bit stream-a. 00000000 b. 11111111 c. 01010101 d. 00110011 Draw the graph of the i. NRZ-Iusing each of the given data streams, assuming that the last signal level has been positive. From thegraphs, guess the bandwidth for this scheme using the average number of changes in the signal level.Use Huffman code to demonstrate that a variable length encoding scheme can be used to compress the following message: rammer_jammer_yellow_hammer_give_them_h_alabama How many bits were saved over a MINIMAL FIXED LENGTH encoding scheme?
- Given are the following codewords for an error control coding scheme data 000 011 100 codeword 00011000 00000111 10101000 . a.What is the minimum Hamming distance? b. What is the coding rate for this scheme? c. what raw data rate would be required if we need a throughput of 6 Mpbs? d. in a different situation, the number of data bits to transfer is 5, and the minimum hamming distance is dmin=5. find the maximum coding rate for this situationGiven the message “ACCBCAAB*”, in which the probabilities of symbols are P(A) = 0.4, P(B) = 0.3, P(C) = 0.2, and P(*) = 0.1, a. find the compressed data using arithmetic coding with a precision of 10 binary digits. b. find the compression ratio if we use 8 bits to represent a character in the message.Consider an encoding scheme where integer numbers from 1 to 26 are encoded as character 'A' ro 'Z'. for example , integer 1 encodes character 'A' integer 2 encodes character 'B' and so on last till integer number 26 which encodes character 'Z'. Using this encoding scheme, design a system to count all possible decodings for a given digit sequence. For example, for digit sequence "1524" there are three possible decodings. 1, 5, 2, 4 - AEBD 1, 5, 24 - AEX 15, 24 - OX
- Consider a SEC code that protects 8-bit words with 4 parity bits. If we read the value0xABC, is there an error? If so, correct the error.Note: 0xABC = 1010 1011 1100Hint: Decode the 12-bit encoded data and find if there is an error.Let be the discrete source on the alphabets {I, B, D, R, .} which defines a series of 5 possible characters. These characters occur with probabilities of: I= 0.3, B=0.25, D=0.2, R=0.15 and . = 0.1. a) Encode the Word “” using arithmetic coding compression. b) Find the output Code Word.Map the Hamming distance and maximum correctable bits to the following encodings (b = binary, h = hexadecimal). 1. Correctable errors from (00h→0b), (FFh→1b) answer: 1/2/3/4/5/6/7/8/9 2. Hamming distance from (00h→0b), (FFh→1b) answer: 1/2/3/4/5/6/7/8/9 3. Hamming distance from (00h→00b), (0Fh→01b), (F0h→10b), (FFh→11b) answer: 1/2/3/4/5/6/7/8/9 4. Correctable errors from (00h→00b), (0Fh→01b), (F0h→10b), (FFh→11b) answer: 1/2/3/4/5/6/7/8/9

