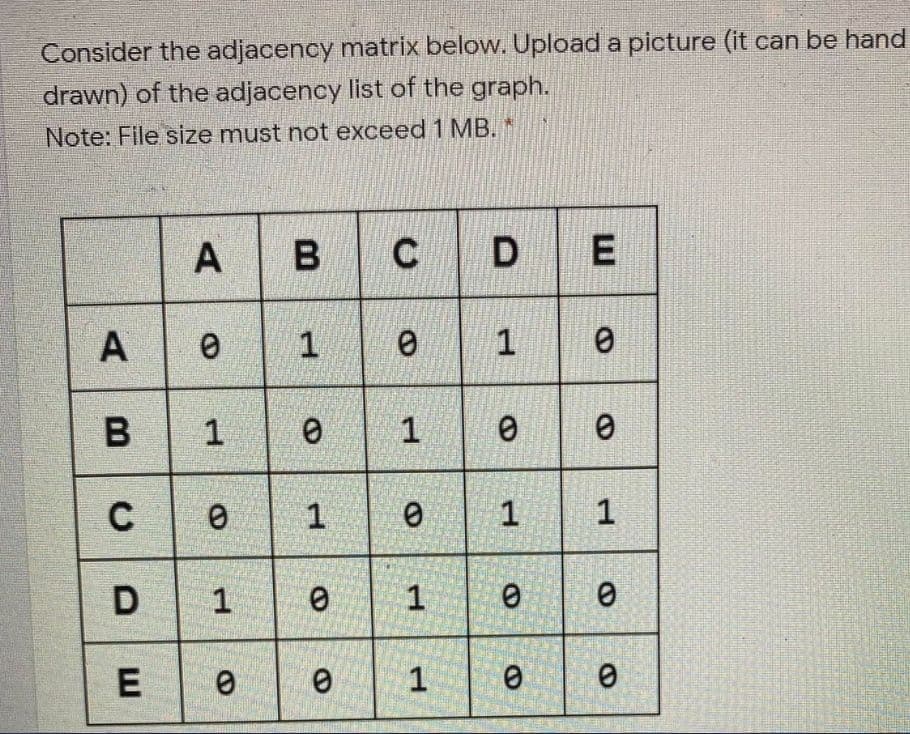
Consider the adjacency matrix below. Upload a picture (it can be hand drawn) of the adjacency list of the graph. Note: File size must not exceed 1 MB. * A B C A 1 B 1 C 1 1 1 1. 1. 1. 1.
Q: must be able to identify individual hosts (sUch as a computer, printer, router, etc.) and individual...
A: The answer is
Q: What is the ARM statement which correspond to the each following statement and find the value of R0?
A: The answer is
Q: A microprocessor is an electrical circuit that serves as the computer's central processing unit (CPU...
A: Introduction: A microprocessor is a computer processor that incorporates data processing logic and c...
Q: Host A sends a 1500-byte packet to Host B. What is the transmission delay (in ms) of the packet from...
A: The answer is
Q: Write a Python program to remove all the occurrences of the number 1 from the list given below and d...
A: Write a Python program to remove all the occurrences of the number 1 from the list given below and d...
Q: Write a php program to take the current room temperature from the user in degree celsius and try to ...
A: Answer: Approach:- 1. Take the current room temperature (in C) from the user using the readline m...
Q: To represent 65 unsigned decimal numbers, what is the smallest amount of binary bits required?
A: SUMMARY: -Hence, we discussed all the points.
Q: B. If Alice uses the same k to encrypt two messages M¡ and M2 as (12, 65) and (12, 64), what is the ...
A: The answer is
Q: Compare and contrast full mesh topology and dual-home implementation in Wide Area Network.
A: Mesh networks are very different from traditional network topologies such as the star, bus, and ring...
Q: Subject - Data Structure Please help me to debug my error. Thank you in advance! import java.ut...
A: I give the required error-free code along with output and code screenshot
Q: tips on how to stay safe and secure in the online environments.
A: Defined to stay safe and secure in the online environments
Q: ease don't copy Write a lisp function f4 that returns the maximum value of an integer list. Example:...
A: Given Please don't copy Write a lisp function f4 that returns the maximum value of an integer li...
Q: Relate the layers of TCP / IP Model with layers of OSI Model.
A: Let's understand both of hem separately: TCP/IP: TCP/IP is not a single networking protocol – it is ...
Q: What are the issues that can prevent a transaction processing system from scaling up linearly? In ea...
A: Answer: In a transaction processing system, there are issues to an increase in linear scale: Shared...
Q: Why may the Security tab be absent when viewing the Properties box for a folder?
A: Introduction: The level of security may be adjusted via the security tab. A folder's default securit...
Q: Input Format: First line will contain number of rows m of inmatrix The next m lines will contain t...
A: The current scenario here is to write the program to find the sum of row elements of the matrix and ...
Q: Q. You are playing an online game. In the game list of the N numbers are given. The player has to ar...
A: This is programming question and it is asking for a code to list odd even numbers.
Q: 3. What is the result of the following query? 2 select name, dept_name from Instructor where name li...
A:
Q: Cloud storage is a limited form of Software as a Service (SaaS)
A: cloud based service like pay as you go for service like storage , networking is IaaS ( Infrastructur...
Q: Write a program in java eclipse ide Input from console 2 integer numbers, save them in variables vx...
A: Write a program in java eclipse ide: Part1:-Input from console 2 integer numbers, save them in varia...
Q: How to systematically improve a Linux computer's security.
A: Solution :: There are lots of Linux servers out there - (good or well enough) many that it's impos...
Q: PYTHON: Write a program (without using built-in functions from scipy, etc) to find the roots of the ...
A:
Q: What is the cost of switching contexts between processes and threads in Distributed Computing?
A: the answer is
Q: Why is understanding the users Visual System so important to the design process? Give an example.
A: what users are thinking and feeling As a result, you must always present them the proper things in t...
Q: 2а. Show that 7n? – 9n + 56 is O(n³). b Show that 100n? is not O(n).
A: We know that : O(g(n)) = { f(n): there exist positive constants c and n0 such that 0 ≤ f(...
Q: You have successfully followed the cabling procedures for a new network connection at a primary scho...
A: Given :- You have successfully followed the cabling procedures for a new networkconnection at a prim...
Q: Why do we utilise MATLAB to solve difficulties in Computational Geometry?
A: Introduction: In business and academia, MATLAB is used by millions of engineers and scientists for d...
Q: Complete the following code for a method that returns the number of elements in an array of objects ...
A: PROGRAM CODE: Following is the complete program code that represents the demonstration of the given...
Q: in java eclipse ide Write a program: Input from console 2 integer numbers, save them in variab...
A: I give the code in java eclipse and also provide the output and code screenshot
Q: What is the purpose of a test management review, and why is it necessary?
A: Introduction: The action of managing a testing process is frequently referred to as test management....
Q: Why is the completion of one entire pattern referred to as a Cycle?
A: Introduction: A cycle is the completion of a complete pattern.
Q: Enter an integer number from console. Save it in variable vw. Check if this number is divisible by 7...
A: Use a Scanner class to read input from console and also use modulus operator to check the remainder ...
Q: When do you use description? When do you use definition?
A: Intro When do you use description? When do you use definition?
Q: Write a JAVASCRIPT program to add a new element 'J' at the beginning and a new element 'T' at the en...
A: Write a JAVASCRIPT program to add a new element 'J' at the beginning and a new element 'T' at the en...
Q: e) Find the moment of inertia of a hollow cylinder about the axis of the cylinder using a JAVA in wh...
A: Introduction: Find the moment of inertia of a hollow cylinder about the axis of the cylinder using ...
Q: Design a 3-bit comparator and write Verilog code using gate level modeling. Write a Verilog test ben...
A:
Q: hipping mistake we are completely MemeForFree to get yours for fre ity
A: Given the scenario, we want to find strings that are read in reverse order same as the original orde...
Q: Given x = [245-10 8 369-414], write a code using For loop to find the largest and the smallest value...
A: numbers = [2, 4, 5, -10, 8, 3, 6, 9, -4, 1, 4] max = Nonemin = None for num in numbers: if (max i...
Q: Question 4 While connecting the inputs and the outputs of a circuit in a stick diagram, which type o...
A: A stick diagram is a diagram which is used to plan the layout of a transistor cell. Sticks or lines ...
Q: Find the median of the two arrays given below when the arrays are merged into a single array. int nu...
A: Algorithm: Include header files and namespace std Create a function named findMedian(int num1[], in...
Q: What is the definition of an inline function
A: Introduction: An inline function is one for which the compiler transfers the code from the function...
Q: Write a JAVA program in which the user enters the initial velocity u, time of travel t, and the acce...
A: Take the initial velocity u, time of travel t, and the acceleration a of an object from the user usi...
Q: Describe the whole process of developing and deploying a database.
A: Intro: Describe the whole process of developing and deploying a database.
Q: When does it make sense to break down large computer processes and programs into smaller subsystems?...
A: Intro When does it make sense to break down large computer processes and programs into smaller sub...
Q: _A CPU typically contains a control unit, an arithmetic logic unit, registers, and a program counter...
A: Given, The answer is given below
Q: Find out the following information about your personal system. Write the answers to the information ...
A: We need to provide information regarding computer system.
Q: must be able to identify individual hosts (such as a computer, printer, router, etc.) and individual...
A: The answer is
Q: Complete the following code for sorting an array of objects of the described ??????? class. The meth...
A: Updated Java Code for sorting the name in lexicographic ordering public void sort(student[] aArray...
Q: How does the Multi-level Feedback Queue scheduler ensure that interactive jobs are completed as rapi...
A: INTRODUCTION: This scheduling is similar to Multilevel Queue(MLQ) scheduling, except that you can m...
Q: Q3. How would you get a confidence score (i.e., a score indicating how confident the model is in its...
A: Let's see the solution in the next steps
Step by step
Solved in 3 steps with 2 images

- Write a Python script that implements the CHF (the Casual Hash Function.) The input data should be split into blocks of 32 bits. If the last block is smaller than 32 bits, the remaining bits should be filled with 1 followed by as many zeros as required. A and B are 2 buffers with specific values (see below). Each block in the message should be combined as shown in the image below. All resulting blocks (i.e. FBI) should be combined with "&" to produce the digest. The size of the digest is 64 bits. Calculate the digest for the string: "Alright, but apart from the sanitation, the medicine, education, wine, public order, irrigation, roads, the fresh-water system, and public health, what have the Romans ever done for us?"Suppose we are building a B-Tree. Pages are 4008 bytes. A key value takes 8 bytes, and a pointer to a tree node or a record takes 8 bytes. a) What is the maximum number of keys in each node? b) Calculate the maximum number of pages N, which can be indexed with anindex file with height, h=2 and m keys (m is calculated in part a)? c) How many I/O operations are required for searching through N pages using a sorted file (N is calculated in part b)?.implement a python code that is a filesystem using a tree data structure. If the specific path does not exist, disregard that file using the code template given in this pastebin link: https://pastebin.com/NuPaPAFT The input format is as follows, the first line is the name of the root directory second line is the number of subdirectories that follows For the next files that follows, the format is: Filename-root node,next path,next path,... Please note the output format. Sample input 1: C12Users-CWindows-CProgramFiles-CAdobe-C,ProgramFilesSteam-C,ProgramFilesferdie-C,Usersjohn-C,Usersguest-C,UsersFirmware-C,WindowsSystem-C,WindowsDocuments-C,Users,ferdieDownloads-C,Users,ferdie Output: C Users ferdie Documents Downloads john guest Windows Firmware System ProgramFiles Adobe Steam
- Assume we wish to resize an existing hash table because the current hash table is becoming too small for the application. Without writing code briefly describe the process of resizing a hash table by "copying" the old data to the new hash table. What is the expected complexity of your process using Big-O notation. Justify your complexity measure. An example of a hash table before resizing is given.Consider an extensible hash table that uses 4-bit hash keys and stores two recordsper bucket. Simulate the insertion, into an initially empty hash table, of records with(hash values of) keys 1111, 1110, 1101,..., 0001, 0000, in that order. Simulate all 16insertions, indicating what happens after each insertion. Start with i=0 bit.Suppose we have a table: Doctor (DOCNO INT, DocName INT, Specialization VARCHAR(10), Salary Float) and it has an extendible hashing index. The hash function h (k) uses two rightmost bits of binary value of the number k and global depth of the directory structure is 2. The bucket size is four records ie it can store upto 4 records. Insert the elements 13, 22, 4, 2, 19, 6, 14, 16, 26, 28, 8, 7, 23,24 using extendible hashing technique.
- you need to design, analyze, and implement algorithms to read in a sequence of characters from standard input and maintain the characters in a linked list with no duplicates. When you read in a previously unseen character, insert it at the front of the list. When you read in a duplicate character, delete it from the list and reinsert it at the beginning. The program implements the well-known move-to-front strategy which is useful for caching, data compression, and many other applications where items that have been recently accessed are more likely to be re-accessed. Requirements: The program should read a sequence of characters. The program should insert unseen character at the front of the list. The program should check if the character is not in the list to be inserted at the front of the list. The program should delete a duplicate character and delete it from the list and insert it at the beginning of the list. The program should check if the character is already in the list and…Suppose that the virtual page reference stream contains repetitions of long sequences of page references followed occasionally by a random page reference. For example, the sequence: 0, 1, ... , 511, 431, 0, 1, ... , 511, 332, 0, 1, ... consists of repetitions of the sequence 0, 1, ... , 511 followed by a random reference to pages 431 and 332. (a) Why will the standard replacement algorithms (LRU, FIFO, clock) not be effective in handling this workload for a page allocation that is less than the sequence length? (b) If this program were allocated 500 page frames, describe a page replacement approach that would perform much better than the LRU, FIFO, or clock algorithms.demonstrate one way to use a hash table for just such a use—a computer terms glossary. The program works by first reading in a set of terms and definitions from a text file. This process is coded in the BuildGlossary subroutine. The structure of the text file is: word,definition, with the comma being the delimiter between a word and the definition. Each word in this glossary is a single word, but the glossary could easily work with phrases instead. That’s why a comma is used as the delimiter, rather than a space. Also, this structure allows us to use the word as the key, which is the proper way to build this hash table. Another subroutine, DisplayWords, displays the words in a list box so the user can pick one to get a definition. Since the words are the keys, we can usethe Keys method to return just the words from the hash table. The user can then see which words have definitions.To retrieve a definition, the user simply clicks on a word in the list box. The definition is retrieved…
- Suppose you have a hash table with seven entries (indexed 0 through 6). This table uses open addressing with the hash function that maps each letter to its alphabet code (a = A = 0, etc.) modulo 7. Rehashing is accomplished using linear-probing with a jump of 1. Describe the state of the table after each of the letters D, a, d, H, a, and h are added to the table.Implement a blog server in C 1. Implement get of all posts (GET /posts), and individual post (GET /post/1) 2. Implement creation of post (POST /posts). Allow the user to enter their name, but check that they are a valid user in db. Do error checking! The user should not specify the post id; that should come from the database. 3. Write three html files to test this; serve them with the blog server: index.html shows the list of posts with a link to each. post.html shows a post. publish.html allows the creation of a new post. Link these together as a user would expect!Matlab: How do I plot semilogx() multiple times? The program reads an uploaded file and then plots column 1 on the log axis and column 3 on the linear axis, but only when it sees "Day= " data.csv: Bacterial Data Day= 1 1e-16 14.32 99.23 90.323e-19 9.23 89.23 9.454e-21 12.45 9.74 1.22 Bacterial Data Day= 2 2e-17 19.32 29.23 3.325e-18 56.23 9.23 7.453e-21 92.45 19.74 14.45 Bacterial Data Day= 3 1.5e-15 89.23 90.31 89.122.e-19 14.55 17.89 78.133.9e-21 2.33 11.23 9.32



