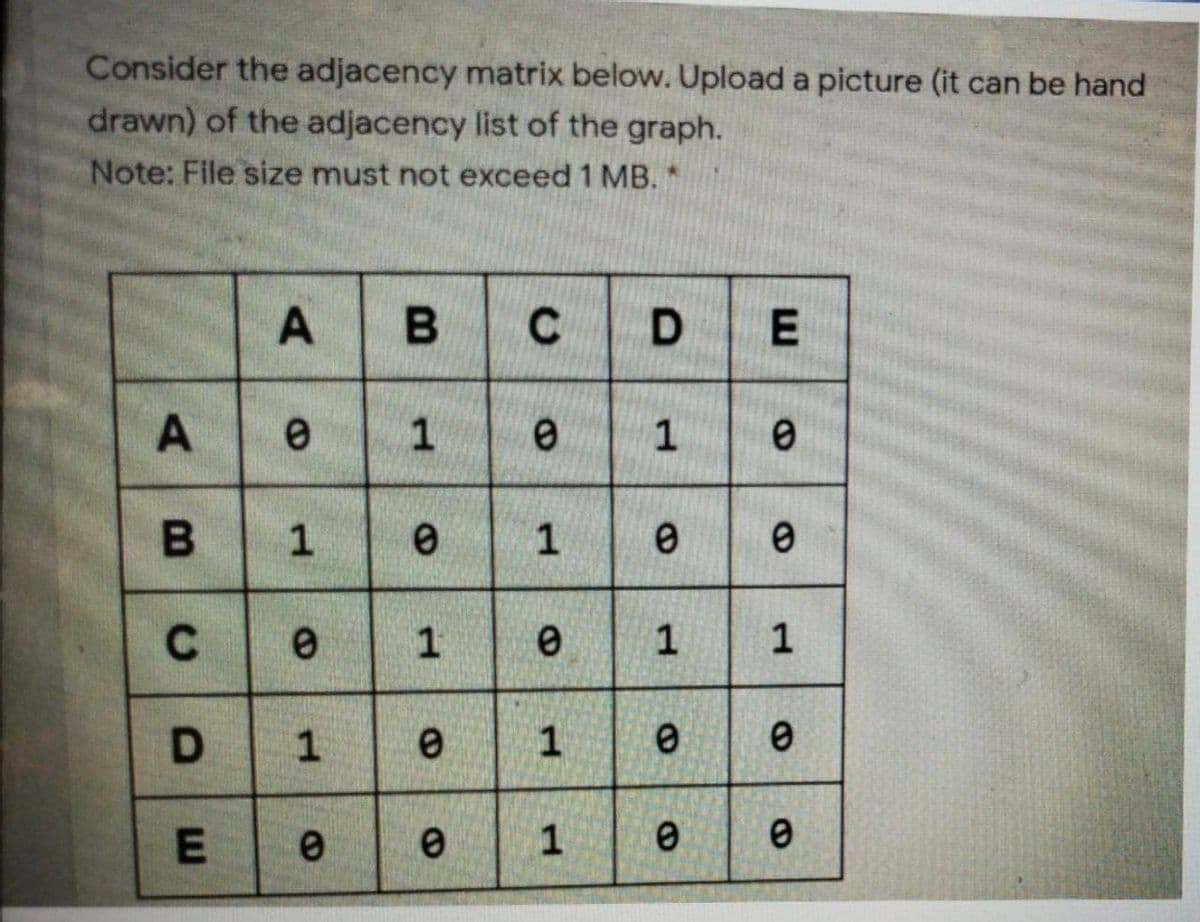
Consider the adjacency matrix below. Upload a picture (it can be hand drawn) of the adjacency list of the graph. Note: File size must not exceed 1 MB. * C 1 C 1 1 1 1 1 D. 1. 1. E
Q: Suppose the register %rax contains 0x100, and the register %rbx contains 0x10. What value is stored ...
A: The correct answer is given below:-
Q: Complete the following Python code. #main.py import area1 def main(): =area1.carea print('Area:', _(...
A: main.py : #main.py import area1 def main(): ______________ = area1.carea print('Area:'...
Q: 1. How do I detect visual problems without video feedback?
A: The answer is given below;-
Q: Using the types of entities found in the Colonial Adventure Tours database (trips, guides, clients, ...
A: The Set of entities provided for Colonial Adventure Tours Database includes Trips, Guides, Clients a...
Q: Please answer it in python Write a ReadListInteger function without arguments that reads positive o...
A: As all the questions are not related to each other. As per the rules of Bartleby I can only solve 1 ...
Q: class. The StackUnderflowException class extends the Java Answer:
A: Ans: The StackUnderFlowException class extends the java class that is called the RuntimeException.
Q: Find the angular velocity from velocity and radius in python
A: Required:- Find the angular velocity from velocity and radius in python Approach:- Take the velocity...
Q: Things saved in a computer's memory may be divided into three broad groups.
A: Intro A computer's memory is storage place where data is stored in form of binary bits physically.
Q: Write a Java program StringProg which creates a Scanner and then does the following: 1. Ask the user...
A: As per the answering policy i can only answer upto 3 question max at a time, so I'm answering first ...
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in ...
A: Given : To write a php program to convert temperature in Fahrenheit from the degree celsius.
Q: cache sel Coapuy is ur o Ti ue ssesa sa the bio The lewng nce ef scenes te memary blocks 0, 12, 256,...
A: We need to find number of conflict misses.
Q: 13) What does the total number of pixels in the region defines? a) Perimeter b) Area c) Intensity d)...
A: The correct answer is given below:-
Q: Which of the three buses connects the core processing unit to the remainder of the computer system?
A: Introduction: In computer architecture, a bus (short for omnibus and traditionally referred to as da...
Q: provided below as well as samples in the text as guides. Save the WBS in list form as a Word file. ...
A: Please check the step 2 for solution
Q: Say you are given a hash function that produces a 224-bit digest, along with a message digest d. Usi...
A: In both math and cryptography, given a capacity H from set A to set B, and a component b in B, a pre...
Q: Write a python program to find the median of two lists when the lists are merged into a single list....
A: Required:- Write a python program to find the median of two lists when the lists are merged into a s...
Q: Write a MATLAB program to plot the discrete signal given below, y = [4, 12, -3, 0, -8, 6, 2, 1, 11...
A: Write a MATLAB program to plot the discrete signal given below, y = [4, 12, -3, 0, -8, 6, 2, 1, 11,...
Q: Which kind of parallelism (data or control) is optimal for SIMD? What kind of parallelism does MIMD ...
A: SIMD stands for Single Instruction Multiple Data, and SIMD is a form of parallel processing in Flynn...
Q: Design NFA accepting string with a's and b's such that string containing two consecutive a's or two ...
A: NFA: The full form of NFA is non-deterministic finite automata, it is defined similar to DFA but it ...
Q: en the MPU et vector rrupt vector neral purpose reg
A: When the MPU starts up for the first time it goes to the and begins executing.Reset vector Interrup...
Q: Designing what you're going to build happens in which phase of CRISP-DM? Business understanding Data...
A: In CRISP-DM designing phase is built in Data preparation i.e. option c.
Q: Construct a dfa that accepts strings on {0,1} if and only if the value of the string, interpreted as...
A:
Q: hen did the analog computer first com
A: Lets see the solution.
Q: Mathletes Game! With the introduction of loops, we now know enough about programming to begin creati...
A: Please check the below c++ code
Q: uppose you have a certain amount of money in a savings account that earns compound monthly interest...
A: According to the information given:- We have to follow the instruction to get desired outcome.
Q: 1) What techniques can managers use to make performance analysis more understandable and comparable?...
A: Intro 1) What techniques can managers use to make performance analysis more understandable and compa...
Q: Consider the adjacency matrix below. Upload a picture (it can be hand drawn) of the adjacency list o...
A: Dear student, We valued your time but as per guidelines, I can answer the only first question. Pleas...
Q: (a) Show that the following grammar is ambiguo- ::= | [ ::= 0 | 1 | 2 | 3|4|5|6|7|8 |9 (b) Find...
A:
Q: Write a sorting class that sorts elements of an array of type Long in ascending order. note: Arra...
A: Step 1 : Start Step 2 : Define and initialize an array of type long. Step 3 : Print the array before...
Q: What is the signal function's relevance, and how does it change?
A: Introduction: A signal is a function in signal processing that transmits information about an item. ...
Q: Use C sharp language and code must get compiled in visual studio. ---------------------------------...
A: Here are some points to note exceptions can be caught by using try and catch block try block is u...
Q: What exactly is disc storage, and why is it so important?
A: Introduction: Computer Devices: In computer science, various devices are used to enter and output d...
Q: It's critical to understand what a computer's operating system is capable of.
A: Introduction: The application's principal job is to manage computer resources on a computer system, ...
Q: How many days, years did quitting employees work in their past jobs. Name Null? Туре NUMBER (6) EMPL...
A: Here is the query for the the time span of the employees work
Q: is an optional clause available for the Case Structure when no match is found in any of the Case sta...
A: We are asked a question on programming logic in case structure.
Q: Vhen the MPU starts up for the first time it goes to the and begins executing. Reset vector Interrup...
A: Lets see the solution in the next steps
Q: Write a complete program that consists of the main function that will call 4 user-defined functions....
A: logic:- To repeat users calculation, use while(1) loop and in one of choice put break. Use two fun...
Q: Create the following tables in your database with the following schema: Table: Employee +- | Column ...
A: Here are all the queries asked in above:
Q: Describe five of the records and information manager's responsibilities.
A: Introduction: Here we are asked to list the duties of the records and information manager.
Q: AVING count(*) = 34 SELECT a, sum(c) FROM xyz GROUP BY b HAVING sum(c) < 0 SELECT c, min(a), max(b...
A: Assuming all tables and columns exist, in which of the following SQL can the HAVING clause be writte...
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in ...
A: For this script, we will be creating a POST form that submits to the same PHP page in which it is. T...
Q: Machine learning/deeplearning in additive manufacturing how to find projects or examples to learn t...
A: Lets see the solution.
Q: Using the MATLAB platform, Write a program to plot the given signal array [4,8,12,7,-2,6,4,5,0,-1,1,...
A: Required:- Using the MATLAB platform, Write a program to plot the given signal array = [4,8,12,7,-2,...
Q: Back in what decade did the term "computer literacy" come into use?
A: In the above question that is the term "computer literacy" come into use is answered below
Q: Briefly describe the workflow and control hand
A: given - Briefly describe the workflow and control handoffs used to execute a system call.
Q: How do I find these four red marks on the Group Policy Management. In other words, how do you disabl...
A: Hold down the Windows Key and press “R” to bring up the Run command box. Type “gpedit.msc“, then pre...
Q: QUESTION 1 Write a complete program that consists of the main function that will call 4 user-defined...
A: logic:- To repeat users calculation, use while(1) loop and in one of choice put break. Use two fun...
Q: Develop a program to add two numbers of 8 byte lon whose result is more than 8 byte. The first numbe...
A: In this question, we are asked to write a assembly program which store the numbers from 8501 to 8508...
Q: Write a python program to find the potential energy using the total energy & kinetic energy. All the...
A: The solution to the given problem is below.
Q: Write a JAVA program to find the unique element which is present only once in the given array. All t...
A: Write a JAVA program to find the unique element which is present only once in the given array. All t...
Step by step
Solved in 2 steps with 1 images

- you need to design, analyze, and implement algorithms to read in a sequence of characters from standard input and maintain the characters in a linked list with no duplicates. When you read in a previously unseen character, insert it at the front of the list. When you read in a duplicate character, delete it from the list and reinsert it at the beginning. The program implements the well-known move-to-front strategy which is useful for caching, data compression, and many other applications where items that have been recently accessed are more likely to be re-accessed. Requirements: The program should read a sequence of characters. The program should insert unseen character at the front of the list. The program should check if the character is not in the list to be inserted at the front of the list. The program should delete a duplicate character and delete it from the list and insert it at the beginning of the list. The program should check if the character is already in the list and…Write a Python script that implements the CHF (the Casual Hash Function.) The input data should be split into blocks of 32 bits. If the last block is smaller than 32 bits, the remaining bits should be filled with 1 followed by as many zeros as required. A and B are 2 buffers with specific values (see below). Each block in the message should be combined as shown in the image below. All resulting blocks (i.e. FBI) should be combined with "&" to produce the digest. The size of the digest is 64 bits. Calculate the digest for the string: "Alright, but apart from the sanitation, the medicine, education, wine, public order, irrigation, roads, the fresh-water system, and public health, what have the Romans ever done for us?" steps on how are in the attached picturesWrite a Python script that implements the CHF (the Casual Hash Function.) The input data should be split into blocks of 32 bits. If the last block is smaller than 32 bits, the remaining bits should be filled with 1 followed by as many zeros as required. A and B are 2 buffers with specific values (see below). Each block in the message should be combined as shown in the image below. All resulting blocks (i.e. FBI) should be combined with "&" to produce the digest. The size of the digest is 64 bits. Calculate the digest for the string: "Alright, but apart from the sanitation, the medicine, education, wine, public order, irrigation, roads, the fresh-water system, and public health, what have the Romans ever done for us?"
- Suppose we are building a B-Tree. Pages are 4008 bytes. A key value takes 8 bytes, and a pointer to a tree node or a record takes 8 bytes. a) What is the maximum number of keys in each node? b) Calculate the maximum number of pages N, which can be indexed with anindex file with height, h=2 and m keys (m is calculated in part a)? c) How many I/O operations are required for searching through N pages using a sorted file (N is calculated in part b)?.Correct answer will be upvoted else downvoted. Computer science. You have an arrangement a with n components 1,2,3,… ,k−1,k,k−1,k−2,… ,k−(n−k) (k≤n<2k). How about we call as reversal in a couple of files i<j to such an extent that a[i]>a[j]. Assume, you have some change p of size k and you assemble an arrangement b of size n in the accompanying way: b[i]=p[a[i]]. You will probably find such change p that the absolute number of reversals in b doesn't surpass the all out number of reversals in a, and b is lexicographically greatest. Little update: the grouping of k integers is known as a stage in the event that it contains all integers from 1 to k precisely once. Another little update: a grouping s is lexicographically more modest than another succession t, if either s is a prefix of t, or for the primary I to such an extent that si≠ti, si<ti holds (in the principal position that these arrangements are unique, s has more modest number than t). Input…Assume we wish to resize an existing hash table because the current hash table is becoming too small for the application. Without writing code briefly describe the process of resizing a hash table by "copying" the old data to the new hash table. What is the expected complexity of your process using Big-O notation. Justify your complexity measure. An example of a hash table before resizing is given.
- Computer Science For the following values, explain whether we can efficiently get the value from a default (standard) inverted index postings file. By efficiently we mean with one lookup--not scanning the entire index. Symbol Value |d| total number of terms in a given doc |d|u number of unique terms in a given doc df(w) number of documents term w appears in c(w, C) number of times term w occurs in corpus C c(w, d) number of times term w occurs in document d p(w, d) probability of term w occurring in document d a. p(w,d) b. |d|u c. |d| d. df(w) e. c(w,C) f. c(w,d)Suppose that a disk drive has 6,000 cylinders, numbered 0 to 5999. The drive is currently serving a request at cylinder 2225, and the previous request was at cylinder 5195 (Hint: this indicates the reading head’s moving direction). The queue of pending requests, in FIFO order, is: 5962,2876,5452,1369,3594,5046,866,3269,409,1744 Starting from the current head position, what is the total distance (in cylinders) that the disk arm moves to satisfy all the pending requests for each of the following disk-scheduling algorithms? a. FCFS SSTF SCAN LOOK C-SCAN C-LOOKSuppose we have a table: Doctor (DOCNO INT, DocName INT, Specialization VARCHAR(10), Salary Float) and it has an extendible hashing index. The hash function h (k) uses two rightmost bits of binary value of the number k and global depth of the directory structure is 2. The bucket size is four records ie it can store upto 4 records. Insert the elements 13, 22, 4, 2, 19, 6, 14, 16, 26, 28, 8, 7, 23,24 using extendible hashing technique.
- code in python attached please Define a hash table with an associated hash function ℎ(?)h(k) mapping keys ?k to their associated hash value. b) In simple uniform hashing, each key is assumed to have equal probability to map to any of the hashes in a given table of size m. Given an open-address table of size 500500 and 22 random keys, what is the probability that they hash to the same value? What is the probability that they hash to different values?Consider an extensible hash table that uses 4-bit hash keys and stores two recordsper bucket. Simulate the insertion, into an initially empty hash table, of records with(hash values of) keys 1111, 1110, 1101,..., 0001, 0000, in that order. Simulate all 16insertions, indicating what happens after each insertion. Start with i=0 bit.Assume you have a text file containing 10,000 words and you want to count the frequency of each word in the file. What is the time complexity of this operation using a hash table?



