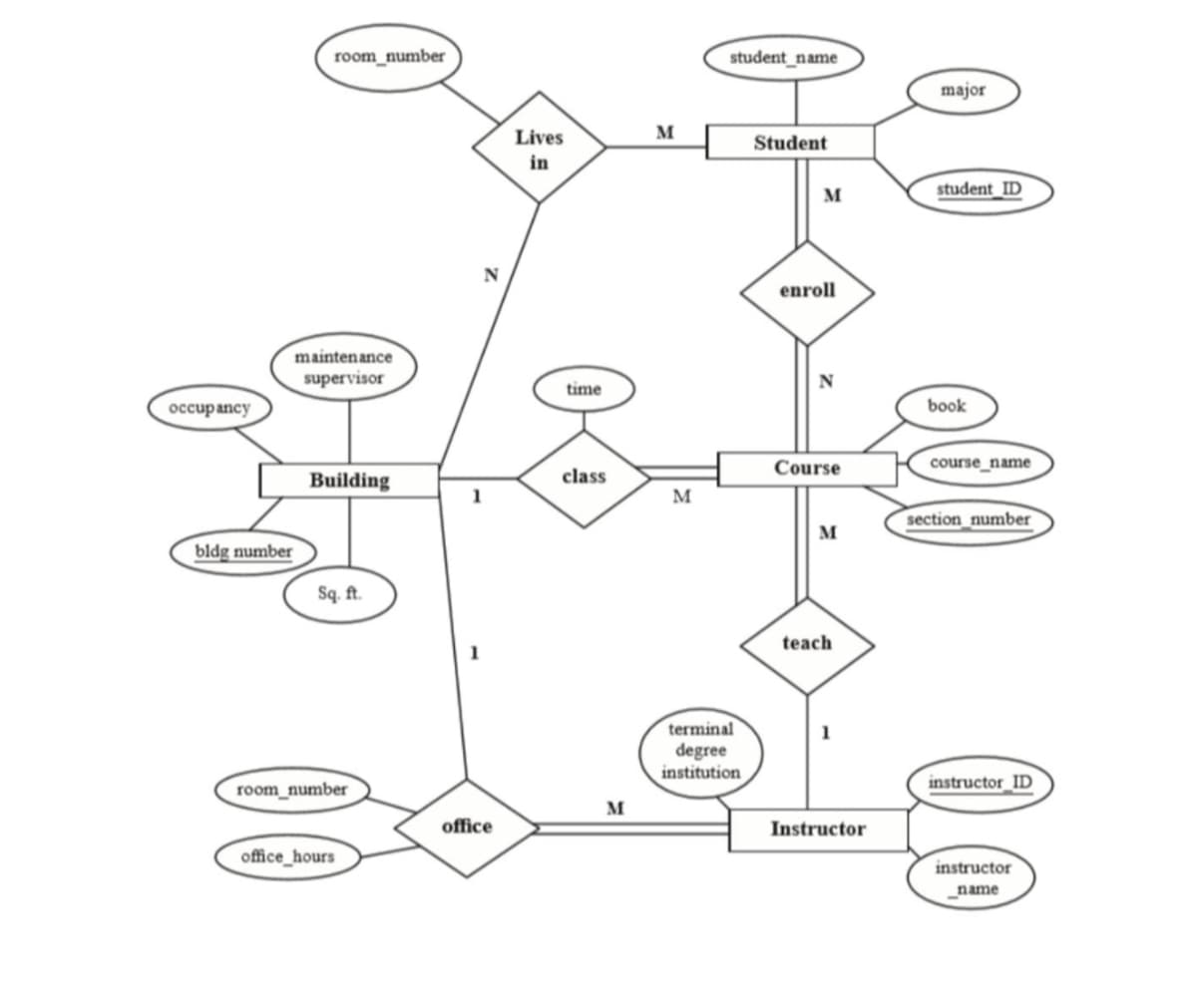
Consider the ER diagram presented in the figure bellow. Given the ER schema, draw an instance diagram using three courses that you are taking this semester. Draw instances of each entity type involved and relationships as they exist in reality.
Consider the ER diagram presented in the figure bellow. Given the ER schema, draw an instance diagram using three courses that you are taking this semester. Draw instances of each entity type involved and relationships as they exist in reality.
Chapter7: Developing An Excel Application
Section: Chapter Questions
Problem 3RA
Related questions
Question
Consider the ER diagram presented in the figure bellow. Given the ER schema, draw an instance diagram using three courses that you are taking this semester. Draw instances of each entity type involved and relationships as they exist in reality.
Transcribed Image Text:occupancy
bldg number
room_number
maintenance
supervisor
Building
Sq. ft.
room_number
office_hours
office
Lives
in
time
class
M
M
M
student_name
terminal
degree
institution
Student
M
enroll
N
Course
M
teach
Instructor
major
student ID
book
course_name
section_number
instructor ID
instructor
name
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage