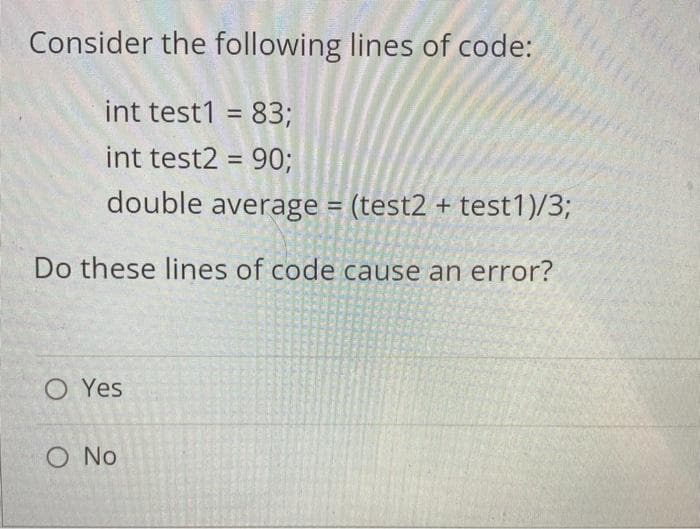
Consider the following lines of code: int test1 = 83; int test2 = 90; double average = (test2 + test1)/3; Do these lines of code cause an error? O Yes O No
Q: Explain how an organization's information systems employ databases. Give an example.
A: Given: We have to discuss Explain how an organization's information systems employ databases. Give…
Q: Is there a drawback to billing software that can be identified?
A: An software is a collection of programs or set of programs given to the system.
Q: For most of us. the Internet is a tool we use for email, news, entertainment, socializing, and…
A: let us see the answer:- Introduction:- Cyberwarfare is the use of digital attacks, such as computer…
Q: Why does this return an empty array and not 'G','H','I','J','K','B' x =…
A: Solution: Using slice object we can select the range where to start and where to end. It is does…
Q: What are you referring to when you talk about the aims of the authentication process? What are the…
A: Authentication is the process of identifying an individual process or entity that is attempting to…
Q: In the following protocol A → S : A,B S-A: (Ts.L, КАВ. В, (Ts. L, КАв- А)кклS A → B : {Ts. L, KAB.…
A: Cryptography: Cryptography is technique of securing information and communications through use of…
Q: What security risks does your computer face? How may these hazards be reduced? Describe the…
A: Given: In order to protect themselves, clients can make sure they understand the terms of their…
Q: Think about a bank robbery scenario that may occur. What safeguards does the bank have in place to…
A: Introduction: An NIDS is a must-have for network security since it allows you to identify and react…
Q: What are the goals of authentication, and how do you define them? Compare and contrast the benefits…
A: Answer the above question are as follows
Q: Examine the factors that a web designer must consider while creating a website.
A: Web design is extremely important for any business.
Q: Describe the significance of web application security and provide examples from the industry. What…
A: Describe the significance of web application security and provide examples from the industry. What…
Q: Why is it vital for you to understand and be able to generate a virus as a penetration tester?
A: According to the information given:- we have to define generate a virus as a penetration tester.
Q: Define what the term "UNIX" means. What are the top five UNIX features, and how would you describe…
A: Unix and Unix-like operating systems are a group of computer operating systems descended from Bell…
Q: Use the extended Euclidean Algorithm to compute the inverse of 5 mod 241.
A:
Q: Assume your disc volume's boot record is corrupted. A backup copy of the boot record may be made…
A: When it comes to partitioned computer mass storage devices such as fixed discs or detachable drives,…
Q: System development methodology is defined in this section.
A: A system development methodology is a methodology for systematically organizing the best ways to…
Q: Find a complex design with a bug, and provide enough evidence to confirm that the bug cannot be…
A: The solution is in below step.
Q: Distributed denial-of-service attacks come in a variety of formats.
A: Both DDoS and Denial of Service (DDoS) assaults are identical except for the fact that in DoS…
Q: Why is it required for a computer to have a cooling system? What are the different cooling methods?
A: The main reason for the cooling system Computer cooling is required to remove the waste heat…
Q: What is the purpose of memory? RAM stands for Random Access Memory. Why is memory referred to as…
A: RAM: The random disk is a short-term memory used by computers to store and manage all of their…
Q: the use of electronic data How does the event viewer log organise events on the server?
A: Electronic data Interchange is the electronic interchange of business information using a…
Q: Implement a Python script that uses the multiprocessing module to print its PID. Upload both the…
A: Program Plan/Algorithm: Import the modules Create a function to print the process of module 1…
Q: A "distributed denial of service attack" is what it's known as, and it can be carried out by a…
A: Given: We have to discuss A "distributed denial of service attack" is what it's known as, and it…
Q: Discussion: 1. Convert the gray code 01011001 to decimal number and show your work. de 00101191 to…
A: According to the Bartleby guideline we are suppose to answer only one question at a time. Kindly…
Q: Write a brief description of the UNIX operating system? Identify and describe six UNIX tools for…
A: Could you please write a brief comment about the UNIX operating system? Identify and describe six…
Q: 1 1 Contagion (a) Write a function printmat : bool array array -> unit = that given a bool matrix…
A: Ans A- I'm doing a task wherever i would like to possess a perform printmat : bool array array ->…
Q: use a toast that provides simple feedback to the user regarding the website that he/she already…
A: Below is the complete solution with explanation in detail for the given question using Android…
Q: Production Semantic Rules S.val = A.val; SA Sign A.sign = Sign.sign; %3D print(A.val); Sign.sign=1…
A:
Q: Explain this code detail by detail like putting comments
A: As per question statement, Comments is required which explains the code.
Q: Fill in the blanks below. Assume user supplies the value of n. Line Code 1 2 do { 3. print x 4 X=x+1…
A:
Q: Assume X = {3,4,6,9,8,7,16,15,20,19} is an array representation of a binary heap can i have help…
A: Binary Heap is a Complete Binary Tree. It is typically represented as an array. The root element…
Q: Explain how a company's information systems utilize databases, using any company as an example.
A: Database: An organised collection of structured data, or "data," is kept electronically in a…
Q: If you want the computer to look for operating system boot files on the CD-ROM before checking the…
A: Boot Sequence : Booting is the process during which the computer hardware check for all the…
Q: A distributed denial-of-service attack cannot be orchestrated by a single individual, but what…
A: A distributed denial-of-service -(DDoS) attack occurs when multiple machines work together to attack…
Q: What steps can you take to keep your data safe?
A: The physical data model is a representation of the data that will be used to create the database.…
Q: What is the goal of authentication? Discuss the benefits and drawbacks of different authentication…
A:
Q: Fill in the blanks to create a proper mutator method for the cart attribute in the code below. All…
A: Let us see the mutator method details below.
Q: What security flaws may your PC have? What can be done to reduce the risks? Distinguish the tactics…
A: 1 Types of security vulnerabilities include the following: The flaws are among the most serious…
Q: How can I draw (class diagram) for language translation app?
A: The class diagram for language translation app is as follows.
Q: Consider a weighted graph where all the edges have weight=10. If we want to determine the shortest…
A: A weighted graph is a graph where each edge is associated with a value called weight. There are many…
Q: To what end would a virus writer intentionally design a payload that may ruin a computer system? It…
A: This malware's payload is as follows: A payload is malware that the threat actor aims to deliver to…
Q: It's important to show how data flows between the different parts of a website.
A: The following are the components of a Web application that will be explained: The internet connects…
Q: Explain several goals and objectives of HCI focusing on achieving usability.
A: Please upvote. i am providing you the correct answer below. Please please please.
Q: How do you create a temperature monitoring system?
A: Lets see the solution in the next steps
Q: Before scanning your hard drive for operating system files, you'll need to make sure the computer is…
A: Start: CD ROM, or Compact Disc Read-Only Memory, is a kind of data storage that can carry up to 1 GB…
Q: What is RAID 5? What kind of situation would necessitate the deployment of RAID 5 rather than one of…
A: Introduction: Here we are required to explain what is RAID 5, also we need to explain what kind of…
Q: ou hoping to achie
A: Authentication is the demonstration of demonstrating an affirmation, like the character of a…
Q: Examine the factors that a web designer must consider while creating a website.
A: Web Designer: Designing a company's website is all about making it easy for customers to find what…
Q: What are the many kinds of Virtual Private Networks (VPNS) and what are their advantages?
A: Kind of virtual private network:
Q: Examine the two schools of thinking when it comes to the definition of "information technology."…
A: Data:- An information system is a collection of interconnected components that gather, store, and…
3 DO NOT COPY FROM OTHER WEBSITES
Upvote guarenteed for a correct and detailed answer. Thank you!!!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Write an application that allows a user to enter any number of student quiz scores, as integers, until the user enters 99. If the score entered is less than 0 or more than 10, display Score must be between 10 and 0 and do not use the score. After all the scores have been entered, display the number of valid scores entered, the highest score, the lowest score, and the arithmetic average.Determine the distance between point (x1, y1) and point (x2, y2), and assign the result to pointsDistance. The calculation is:Distance = SquareRootOf( (x2 - x1)2 + (y2 - y1)2 ) #include <stdio.h>#include <math.h> int main(void) { double x1; double y1; double x2; double y2; double xDist; double yDist; double pointsDistance; xDist = 0.0; yDist = 0.0; pointsDistance = 0.0; scanf("%lf", &x1); scanf("%lf", &y1); scanf("%lf", &x2); scanf("%lf", &y2); /* Your solution goes here */ printf("%lf\n", pointsDistance); return 0;Write an application that allows you to enter nine(and only nine, no more no less) integers and displays the values, their mean, and their median. (Java)
- By default, which one of the following types of values will be thrown when the below function is executed?def abstractAdd(a,b,c):print(a+b+c) Choose an answer A None B bool C str D intA cashier distributes change using the maximum number of five dollar bills, followed by one dollar bills. For example, 19 yields 3 fives and 4 ones. Write a single statement that assigns the number of one dollar bills to variable numOnes, given amountToChange. Hint: Use the % operator. #include <stdio.h> int main(void) { int amountToChange; int numFives; int numOnes; scanf("%d", &amountToChange); numFives = amountToChange / 5; /* Your solution goes here */ printf("numFives: %d\n", numFives); printf("numOnes: %d\n", numOnes); return 0;A magic date is one when written in the following format, the month times the date equals the year e.g. 6/10/60. Write code that figures out if a user entered date is a magic date. The dates must be between 1 - 31, inclusive and the months between 1 - 12, inclusive. Let the user know whether they entered a magic date. If the input parameters are not valid, return false. examples: magicDate(6, 10, 60) -> truemagicDate(50, 12, 600) -> false
- You can declare a void method as follow; public void int calculateSalary() { int num1=89; int num 2= 71; int sum= num1+num2; return sum; } a) True b) FalseAsk the user for a name and for a list of test scores. Show the number of tests taken and the average. Allow the user to enter any number of scores and make the program end when a negative value is entered. Write in java and use test case examples as a result.What is the sentinel value in the following code snippet?int main(){int score = 0;int sum_of_scores = 0;int end = 1;cout << "Enter an score (-1 to end): ";cin >> score;while (score != -1){sum_of_scores = sum_of_scores + score;cout << "Enter an score (-1 to end): ";cin >> score;}cout << "Sum of scores " << sum_of_scores;return 0;}
- Find the output of the code below :void main( ) { int NoOfGirls = 4; int NoOfBoys = 10 ; if ( NoOfBoys = 8 && NoOfGirls <= NoOfBoys ) cout<<”Great achievement”; else cout<<”Greater achievement”; }Assume that int a[ 2 ][ 2 ] = { { 1, 2 }, { 3, 4 } }; the value of a[ 1, 1 ] = ______;for (int value=3; pow (2, value) <=100; value++) cout << pow (2, value) << ": ";



