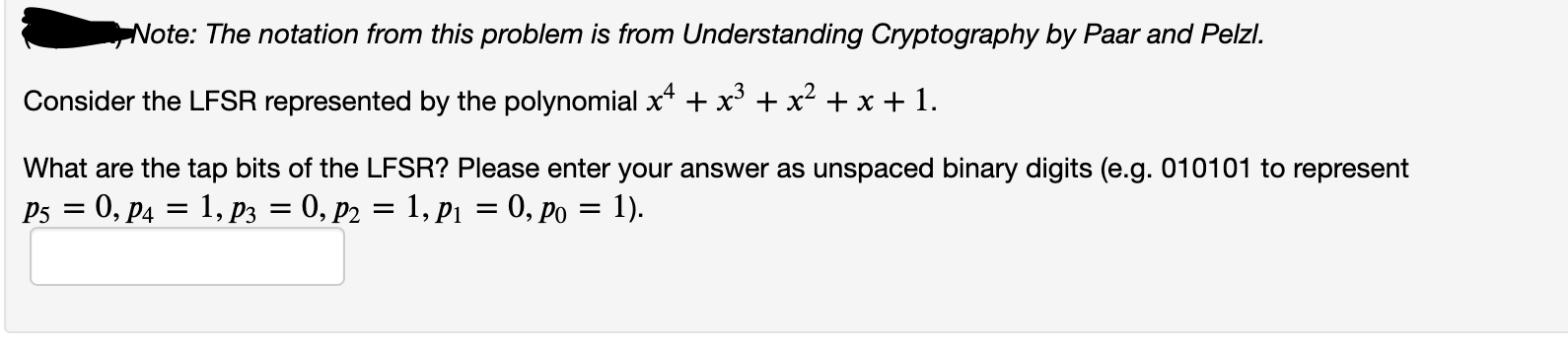
Consider the LFSR represented by the polynomial x* + x* + x² + x + 1. What are the tap bits of the LFSR? Please enter your answer as unspaced binary digits (e.g. 010101 to represent P5 = 0, P4 = 1, p3 = 0, p2 = 1, p1 = 0, po = 1).
Q: Consider the plaintext PLAINCIPHERTEST, arrange it to 3*5 matrix and rearrange R1 to R3, R2 to R3,…
A: Given plain text is, PLAINCIPHERTEST Arranged in 3*5 matrix Then rearrange R1 to R3, R2 to R3, C1 to…
Q: Suppose that you share a new (unused) random key of 128-bits with a recipient. You are considering…
A: For an n-bit block size are 2n possible different plaintext blocks and 2n possible different…
Q: Given the below conditional CMP r0,r1 ADDEQ r2,r0,r1 SUBGT r2,r0,r1 RSBLT r2,r0,r1
A: The correct is questions in Option("r2=15,N=1")
Q: 25)=3.54,p.01 c. t(.8128) = 7.0, p = α, tobt = 4.25 d. t(10), tcrit > 5.3, p < α
A: Solution As we know An APA format scenario contains the df,t value,p value compared with alpha and…
Q: padding Question 11 Suppose we have a block cipher with block size 8-bytes (64-bits) and we will use…
A: PKCS#5 padding is defined for 8-byte block sizes ECB should not be used if encrypting more than…
Q: Q1 Consider the following four addresses: 172.16.22.224/20 172.16.53.10/20 172.16.48.225/20…
A: 2
Q: The state of a feedback shift register of length L is a bit string of length L. true / O false…
A: Given:
Q: Suppose we have a code consisting of 5 ternary codewords, with codeword lengths (1, 1, 2, 2, 3). How…
A: the answer is given below:-
Q: Client host Server host 2 3 5 ...
A: Solution:
Q: Suppose N people want to communicate with each of N – 1 other people using symmetric key encryption.…
A: Actually, Encryption is the conversion of data into a form, called a ciphertext, that cannot be…
Q: The Internet Protocol (IP) address of a computer acts as its unique identifier. How do mnemonic…
A: To discuss IP addresses as well as mnemonic addresses: Determine the maximum number of computers…
Q: How many bit strings with length not exceeding n, where n is a positive integer, consist entirely of…
A:
Q: Can you tell whether the datagram is carrying UDP, TCP, or ICMP data? How? What is the SPI for this…
A: The User Datagram Protocol, or UDP, is a bit different from what you might expect from a transport…
Q: Consider the PPP byte stuffing method. What are the contents of the following received sequence of…
A: PPP is a character oriented version of HDLC Flag is 0x7E (01111110) Control Escape 0x7D…
Q: For a given byte-oriented protocol, we have two special patternsFLAG (10101010) and ESC (01010101).…
A: Byte-oriented protocol is the protocol used for communication which uses its full bytes as control…
Q: Using the two rules of IPv6 compression, edit each IPv6 address until it is in the shortest form…
A: IPV6 compression Rule: Totally is there three rules. Rule-1: When a field contains just 0 (zero),…
Q: What is the URL of a private network? Is it feasible for a datagram addressed to a private network…
A: Private Network URL Address: First let's know about understand what is a private network. A private…
Q: In a communication system, all message signals and their frequency values are given in the table…
A: Huffman Coding Huffman coding provides codes to characters where length is proportional to the…
Q: Note: The notation from this problem is from Understanding Cryptography by Paar and Pelzi. Suppose…
A: LFSR:- A linear feedback shift register (LFSR) is a shift register that takes a linear function of a…
Q: Assume we have a code composed of 5 ternary codewords of varying lengths (1, 1, 2, 2, 3). How many…
A: Intro Assume we have a code composed of 5 ternary codewords of varying lengths (1, 1, 2, 2, 3). How…
Q: 1. It is a protocol for encapsulating data packets that use one routing protocol inside the packets…
A: GRE stands for Generic Routing Encapsulation, and it's a mechanism for encapsulating data packets…
Q: Suppose a message is 5000 bits long. If it is to be encrypted using a block cipher of 64 bits, find…
A: BLOCKS: A block cipher takes a block of plaintext bits and generates a block of ciphertext bits,…
Q: 19 Using the compression rules, write either the compressed IPV6 address or the full IPV6 address.…
A: Hey, thank you for your question. There are multiple parts submitted in your question. As per our…
Q: CIS269 Packet Translation Lab Break down the following IP datagram into its individual…
A: Break down the following IP datagram into its individual fields, listing the value of each. Hint:…
Q: 3. Consider the following forwarding table (that uses longest prefix matching). Rewrite this…
A: the forwarding table using the a.b.c.d/x notation is given below
Q: Consider the SSL protocol, all the data frames in the record protocol have to be 59111 O encrypted O…
A: We are asked a question on SSL protocol. Secure socket Layer protocol is used to provide the data…
Q: If the IP fragment offset is equal to 40, and sequence number of start byte of payload is 500 then…
A:
Q: Let's start by defining an Internet Protocol (IP) address. What use do mnemonic addresses serve? Is…
A: An IP address is a number that uniquely identifies a device on the Internet or a private network.
Q: Consider sending a 2000-byte datagram into a link with a MTU of 980 bytes. Suppose the original…
A: The Answer is in Below Steps
Q: Derive K1, the first-round subkey. b. Derive L0, R0. c. Expand R0 to get E[R0], where E[ # ] is the…
A: 1. M = 0000 0001 0010 0011 0100 0101 0110 0111 1000 1001 1010 1011 1100 1101 1110 1111 As you have…
Q: b) Suppose a bank organization MyBank has designed a system in which a symmetric session key is…
A: According to the guidelines we are allowed to answer only the first question. - The question wants…
Q: Q5. DHKE protocol Use these toy parameters to demonstrate how DHKE (Diffie-Hellman Key Exchange)…
A:
Q: In the following problems, check suitable rule (Sum, Subtraction or Product) and compute the total…
A: To do: check suitable rule for given
Q: Sort DNS records according to their kind. Provide a short explanation of each with examples and…
A: Introduction: Translating IP addresses into human-readable domain names is the goal of the Domain…
Q: Suppose the information content of a packet is the bit pattern 1110 0110 1001 1101 and an even…
A: Given: Bit pattern:1110 0110 1001 1101 Solution: Firstly the given bit pattern is represented as…
Q: Breakdown each part of the following rules and tell what each segment does iptables -t…
A: iptables : is a line command interface used to set up and maintain the tables for the netfilter…
Q: A large number of consecutive IP address are available starting at 192.16.0.0. Suppose that four…
A: 1) For 7000 addresses => 7000/256=28 hence Hence Address range is 192.16.0.0 to 192.16.27.255/19…
Q: Write down of shorter form the following IPv6 addresses: 0000:0000:0000:0000:0000:0000:0000:0001,…
A: Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: Consider the LFSR represented by the polynomial x4 + x² + x + 1. What are the tap bits of the LFSR?…
A: LFSR is a Linear Feedback Shift Register. Its input bits are usually driven by the XOR gates. In…
Q: What relationship is needed between sequence number size and window size to avoid problem in…
A:
Q: Find the odd man out. JNS, JL, JAL, BL a) JNS b) BL c) JAL d) Л
A: given : Find the odd man out. JNS, JL, JAL, BL a) JNS b) BL c) JAL d) Л
Q: Consider the LFSR represented by the polynomial x^4+x^3+1 What are the tap bits of the LFSR? Please…
A: The bits in the LFSR state that influence the input are called taps.
Q: Note: The notation from this problem is from Understanding Cryptography by Paar and Pelzl. Suppose…
A: Answer seed (S5,S4,S3,S2,S1,S0) = (1,0,0,1,1,0) tap bits (P5,P4,P3,P2,P1,P0) = (0,1,1,1,1,1)…
Q: i Consider sending a 2000-byte datagram into a link with a MTU of 980 bytes. Suppose the original…
A: Find:- fragments =? fragment size=? idetification no.=? fragment offset=? fragment flag=?
Q: Answer the following questions based on the concept of Addressing Valid / If invalid, give S# IPV6…
A: valid…
Q: r1, 0(r5) LW r2, 4(r5) Add r3,r1,r7 Add r4
A: Draw out how the following code is run step-by-step with forwarding. What is the CPI? LW r1, 0(r5)…
Q: Exam2: Problem 6 Previous Problem Problem List Next Problem Consider the following two methods for…
A: The answer provided below has been developed in a clear step by step manner. First Step | All Steps…
Q: Sort DNS records according to their kind. Give a short description of each with examples, as well as…
A: DNS records (acronym zone files) are instructions that reside on authoritative DNS servers and offer…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Msg3. B→A : B, N1, Ks, Message2, h(B, N1, Message2) Whereas: h(m) represents the digest of the message (m). {m}{K} represents the encryption of message (m) using the key (K) PK is public key N1 is a random number. 1. What are the main problems in Msg3?Suppose N people want to communicate with each of N – 1 other people using symmetric key encryption. All communication between any two people, i and j, is visible to all other people in this group of N, and no other person in this group should be able to decode their communication. How many keys are required in the system as a whole? Now suppose that public key encryption is used. How many keys are required in this case?Assume you are using any correct plaintext padding method, such as those described in lecture, with a 128-bit (16-byte) block cipher. If you are sending a message that is 184 bytes long, how many padding bytes would you need to add? Justify your answer. For the remaining questions, consider a 4-bit block cipher, described in hexadecimal by the following table: Plaintext Ciphertext Plaintext Ciphertext 0 a 8 e 1 c 9 d 2 f a 0 3 6 b 7 4 3 c 5 5 8 d b 6 4 e 9 7 2 f 1 You can think of this as a simple substitution cipher for hexadecimal digits. There is no “key” other than the table itself.
- a. Compute CBC-MAC for a message of 16 bits, “8642” (in Hexa). Assume a block size of 8 bits with an IV=F1 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be B4 (in Hexa). (Hint: Divide the message into blocks of 8 bits each; XOR each block with the previous cipher output; then encrypt this with the key. For the first block, XOR it with IV. Details in pages 325-326 Ch.12 of the textbook) b. Suppose Alice computes the Secret prefix MAC (page 322: secret prefix MAC(x) = h(key || x)) for the message ”AM” (in ASCII) with key “G” (in ASCII) that both Alice and Bob know. The hash function that is used is h(x1x2x3)= g(g(x1 XOR x2) XOR x3 ) where each xi is a character represented as 8 bits, and g(x) is a 8-bit string that is equal to the complement of bits in x. For example, g(10110011) = 01001100. The MAC is 8 bits. (8-bit ASCII representation of the characters is given below.) What is the Secret prefix MAC…Assume we have a code composed of 5 ternary codewords of varying lengths (1, 1, 2, 2, 3). How many unique messages comprised of two message symbols result in a series of four code symbols after encoding?Give encryption or decryption of these hexadecimal messages using the one-time pad algorithm, giving the result in hexadecimal also. You may wish to convert to binary first. a. m = 0xdeadbeef, K = 0x4ea04002, c = ? b. c = 0x84848484, K = 0xffffffff, m = ? c. c = 0x104557ce, K = 0xdabbad00, m = ?
- Suppose we will use Advanced Encryption Standard (AES) to encrypt a block of plaintext and the known round key for round 7 is: B5 8D BA D2 31 2B F5 60 7F 8D 29 2F EA D2 73 21 What is the third word (i.e. the third 4 bytes) of the round key for round 8?Compute CBC-MAC for a message of 16 bits, “ABCD” (in Hexa). Assume a block size of 8 bits with an IV=C9 (in hexa). For simplicity, assume the encryption to be a simple XOR of the key with the plaintext. Let the encryption key be D8 (in Hexa). (Hint: Divide the message into blocks of 8 bits each; XOR each block with the previous cipher output; then encrypt this with the key. For the first block, XOR it with IV.Let's start by defining an Internet Protocol (IP) address. What use do mnemonic addresses serve? Is the number of domains that a 32-bit representation can store finite? Is there a limit to how many machines a domain may hold?
- Computer Science Can you tell whether the datagram is carrying UDP, TCP, or ICMP data? How? What is the SPI for this SA from your Ubuntu to DVWA-Ubuntu? What is the SPI for this SA from DVWA-Ubuntu to Ubuntu? How are the sequence numbers changing in each of the SAs? In your own words, describe in what cases is manual keying feasible and in what cases it is not.What does it signify when a computer has an IP address? What is the function of mnemonic addresses? How many domains can a 32-bit representation carry, if any? In that case, what's the maximum number of machines that may be part of a single domain?The following message arrived protected by the following CRC polynomial. Does the message have an error or not? Why? In the below table, show your work that allowed you to make the determination of whether an error exists in the message or not. Add rows and columns to the below table as necessary. M(x): 11010011100011 CRC-3-GSM: x3 + x + 1 CRC that was in the message: 011 X0 T(x) C(x) Remainder

