Consider the relations Courses1, Courses2, _Enrollment and Students. Courses cid ename Al Calculus A2 Algebra L2 A5 English L3 Location LI Student(sid, sname, age, level) Courses2 cid AS Bl B2 Classroom L3 L4 Computing LS b) Courses 1-Courses2 name English History (1) Give the results of the following relational _algebra expressions: a) Teid ( name='History' OR 'Computing (Courses2)) c) Courses Courses2 d) Courses1 Enrollment Enrollment sid cid 101 Al 102 A5 103 BI 102 Al 102 A2 e) Enrollment / Teid (Courses1)
Consider the relations Courses1, Courses2, _Enrollment and Students. Courses cid ename Al Calculus A2 Algebra L2 A5 English L3 Location LI Student(sid, sname, age, level) Courses2 cid AS Bl B2 Classroom L3 L4 Computing LS b) Courses 1-Courses2 name English History (1) Give the results of the following relational _algebra expressions: a) Teid ( name='History' OR 'Computing (Courses2)) c) Courses Courses2 d) Courses1 Enrollment Enrollment sid cid 101 Al 102 A5 103 BI 102 Al 102 A2 e) Enrollment / Teid (Courses1)
Principles of Information Systems (MindTap Course List)
12th Edition
ISBN:9781285867168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter5: Database Systems And Applications
Section: Chapter Questions
Problem 4PSE: Using a graphics program, develop an entity-relationship diagram for a database application for an...
Related questions
Question
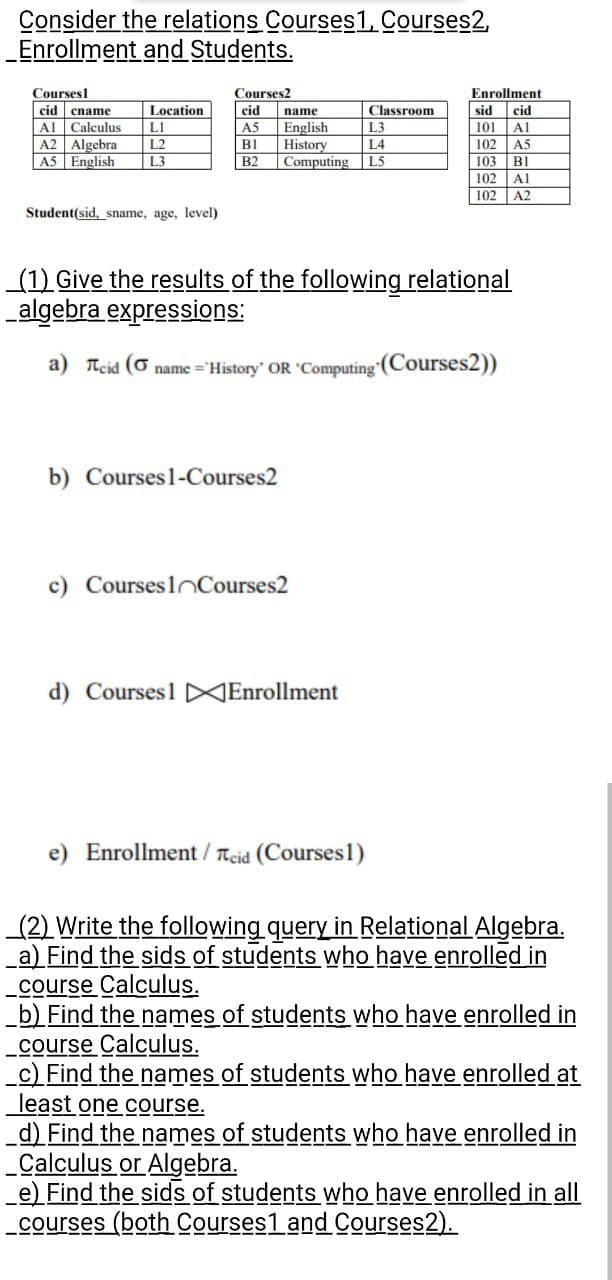
Transcribed Image Text:Consider the relations Courses1, Courses2,
_Enrollment
and Students.
Coursesl
cid ename
Al Calculus
Location
L1
A2 Algebra L2
A5 English
L3
Student(sid, sname, age, level)
Courses2
cid
A5
B1
B2
b) Courses 1-Courses2
name
English
L3
History
L4
Computing L5
(1) Give the results of the following relational
algebra expressions:
a) Teid ( name="History' OR 'Computing (Courses2))
c) Courses Courses2
Classroom
d) Courses1 Enrollment
e) Enrollment / Teid (Courses1)
Enrollment
sid cid
101
Al
102
A5
103 Bl
102
Al
102
A2
(2) Write the following query in Relational Algebra.
a) Find the sids of students who have enrolled in
course Calculus.
b) Find the names of students who have enrolled in
course Calculus.
_c) Find the names of students who have enrolled at
least one course.
d) Find the names of students who have enrolled in
_Calculus or Algebra.
e) Find the sids of students who have enrolled in all
courses (both Courses1 and Courses2).
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning