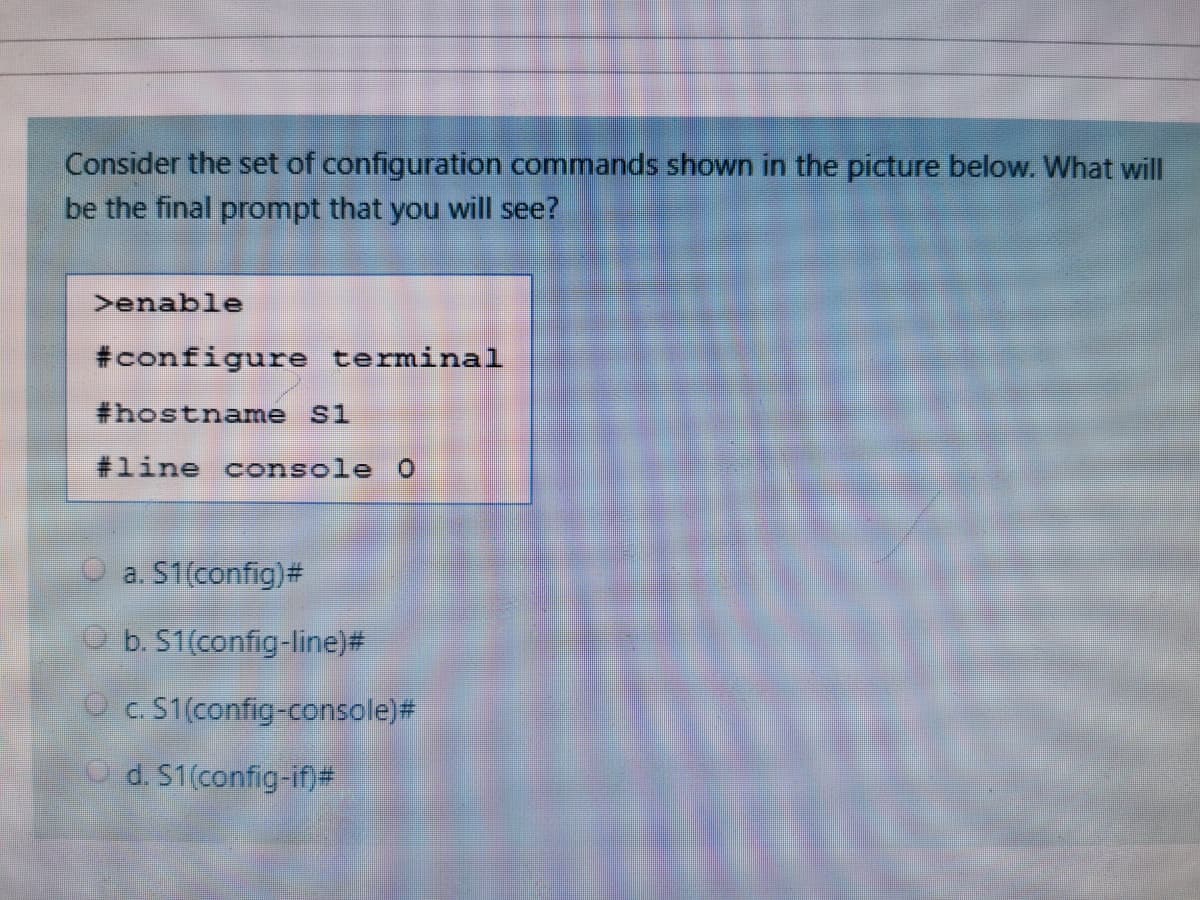
Consider the set of configuration commands shown in the picture below. What will be the final prompt that you will see? >enable #configure terminal #hostname si #line console 0
Q: What allows for a single configuration to be set and then deployed to many or all users? a. Snap-In…
A: Please find the answer below :
Q: which of the following commands is used to run a following command as a privileged user ? a) runas…
A: To run a command as a privileged user means that a command that cannot be used by a normal user can…
Q: Digit 2,4,1 of HTTP status code represents : O Success, Clienterror, Informational Success,…
A: Answer: Correct option is sucess, clienterror, informational according to 2 4 1 code.
Q: nction of Command history, workspace window, Current Folder and Command Windo
A: Matlab Command history: The Command History is a window that lists the most recently executed Matlab…
Q: Q3. Take a screen shot of the screen in command prompt using at least any 5 of various network…
A: Networking commands are utilized at the command brief to get network data like the IP address of the…
Q: Which is the correct order and complete syntax for UNIX commands? Group of answer choices Options…
A: - We need to choose right options for the commands.
Q: Which command will display the number of hops between your computer and the other?
A: HOP counts refer to the number of devices, usually routers, that a piece of data travels through.
Q: Write a simple PowerShell Script as follow:. Create a scheduled task using PowerShell. Create a…
A: In this question we have to write a PowerShell script program to execute three scripts : 1. To…
Q: How do you execute (run) a shell script? (The following script is used in questions 2 and 3)…
A: To run a bash script type the following command in terminal ./<filename> But to do so we…
Q: How can you bypass the wait function and send a user process to the background?a. This cannot happen…
A: Bypassing the wait function The wait function is used to suspend execution of the calling thread.…
Q: Daemon processes must be viewed using the -e option in conjunction with the ps command because they…
A: Daemon processes: A daemon is a long-running background process that responds to service requests.…
Q: Set up a name server (ns1) for the domain happy.lab and its reverse zone on server. How would I…
A: ->Navigate to DNS> Zones to view a list of all DNS zones associated with your account.…
Q: What will be the value in W after the following sequence of commands? CLRW BCF STATUS, 0 MOVLW 17…
A: CLRW BCF STATUS, O MOVLW 17 SUBLW 10 MOVWF PORTB INCF PORTB, 1 RRF PORTB, 0 ADDLW 5
Q: Linux 7. Use the "uniq -c" command to sort and summarize the total occurrences of sudo access by…
A: Here i write code for linux find the number of sudo access in the given datafile1(assume). i…
Q: We want to create a user who has all permissions to manage the server. | Login Properties - usert…
A: As per the given question, we need to identify out of the given options, the correct role for a user…
Q: Q4. Install the RHEL system roles package and create a playbook called timesync.yml that: - Runs on…
A: The YAML code and command as follows:
Q: Which command is used to delete a user account?a. usermod –d usernameb. del usernamec. userdel…
A: To delete a user account, the correct option is c. userdel username Explanation: usermod –d…
Q: does the following command do? cat vuln e
A: Vulnerability commands will allow executing unauthorized command in our operating system . These…
Q: Which one of the following is a symlink to the root path as seen by the process? i. /proc/[PID]/root…
A: Question. Which one of the following is a symlink to the root path as seen by the process? i.…
Q: QUESTION 25 Typically, the daemons are not responsible for: Create user account, Run scheduled…
A: Typically the daemons are not responsible for Answer: Monitor systems such as hardware storage…
Q: The user credentials in the following screenshot is for GLOBAL Setingu Port Sata Aporithn Setings…
A: correct option A
Q: ____________allows for a single configuration to be set and then deployed to many or all users. a.…
A: Given question is multiple choice question.and it's related to windows _____________allows for a…
Q: You wish to configure the runlevels that a particular upstart daemon is started in. Whatshould you…
A: /etc/init is the directory that contains configuration files used by upstart to start, stop, reload,…
Q: What folder contains group policy templates, logon/logoff scripts, and DFS synchronization data?…
A: “System Volume (SYSVOL)” folder contains group policy templates, logon scripts, and Distributed File…
Q: 1- Which of the following constructor create a server socket with the specified port, listen…
A: Answer :- 1. This class executes server sockets. A server attachment trusts that solicitations…
Q: To apply the same configuration in multiple switch interfaces, which one of the following keywords…
A:
Q: When you run the ps command, how are daemon processes recognized?a. The terminal is listed as…
A: A daemon process is a system process that is started during system startup. The daemon process is…
Q: What will be stored into cx after executing the following commands? x1 DW 13 DUP(?),5,4,8 mov cx,…
A: In Registers -> There are processor register which are divided into general register, control…
Q: Recall that only Standard Output can be sent across a pipe to another command. Usingthe information…
A: The 3 standard files are: Stdin: It is used to get keyboard input from the user. Stdout: It is used…
Q: The line that configures the host name for the computer at boot time can be found in /etc/hostname.…
A: Solution: The path etc/hostname contains information about the machine such as machine…
Q: Write the purpose of given command line statements. [root@localhost -]# grep redhat /etc/gshadow…
A: The file /etc/gshadow is a readable file & can be accessed only by the root user. It contains…
Q: Create a server side script using inbuilt modules from Node.js(OS, Path, File system and HTTP).You…
A: Code: const fs = require("fs"); const path = require("path"); //To store the paths of all jpg…
Q: Because daemon processes are not connected with terminals, they must be seen using the –e option in…
A: Introduction: Daemons are frequently initiated when a system is booted up and only stop when the…
Q: Complete the following command so that it displays the output indicated below. Solution PS C:>…
A: There is no single command to get this output. You need to try various commands. Here are following…
Q: Write the command that will configure a Linux system to have the hostname of "Engineering"
A: hostname is the command used to see the current hostname $ hostname prints the hostname
Q: Which command is a UNIX command? Group of answer choices route ipconfig nbtstat ifconfig
A: Unix command are: route ifconfig
Q: Which of the following commands can be used to start a UNIX SysV daemon called lalain runlevels 1,…
A: “chkconfig” command can be used to start a particular daemon in the required run levels. “chkconfig…
Q: out the Operating system version?
A: given - Which of the folling commands can be used to obtain information about the Operating system…
Q: Create a new user on your pfsense system a. User: Remote Password: Remote1 b. Full name: Remote User…
A: To add new user in pfsense system Navigate to system -> User management Click on Add There will…
Q: You are required to write a Spring Boot + SpringMVC based application that handles a sample request…
A: Building: You will build an application that has a static home page and that will also accept HTTP…
Q: Write the purpose of given command line statements. [root@localhost -1# gpasswd -A u6,u4 redhat…
A: 1. gpasswd -A u6,u4 redhat -A, –administrators : Set the list of administrative users. The gpasswd…
Q: As daemon processes are not associated with terminals, you must use the –e switchwith the ps command…
A: Daemon processes Daemon processes runs as background processes. It is not under the direct control…
Q: The NET command has many usages, including the following:
A: NET Command: The Microsoft NET command is a must know for administrators. It adds or delete the…
Q: Because daemon processes are not linked to a terminal, the ps command must be used in combination…
A: The question is to find the the given statement is true or false.
Q: Which two environment variables must you set for the script to complete successfully
A: The two environment variables that we must set up for the script to complete successfully are :…
Step by step
Solved in 3 steps with 1 images

- What will be stored into cx after executing the following commands? x1 DW 13 DUP(?),5,4,8 mov cx, LENGTH x1 a.4 b.16 c.32 d.13Penetration programming Modify the script so that it also works interactively. Specifically, if no hostname is given on the command line, the program should interactively ask for a hostname, starting port, and ending port with three separate prompts, and carry out its scan using those values. After scanning finishes, the program should loop to receive another set of values, stopping only when the user enters a blank host name. If this feature is implemented properly, it will also allow you to run the script in ’batch’ mode, by “piping in” a plain text file with the hostname on the first line, start port on the second, stop port on the third, and repeating for as many hosts as you wish to scan. For example, if a file named hosts_to_scan.txt contains a list of hosts and ports in the proper format, the program should now work as follows: cat hosts_to_scan.txt | ./portscanner.sh The timeout argument should still work in this case as well: cat hosts_to_scan.txt | ./portscanner.sh -t 3…What is reported on VA page 30 if a command is not carried out? Software-managed TLBs outperform hardware-managed ones in the following usage cases:
- Recall that only Standard Output can be sent across a pipe to another command. Usingthe information presented in this chapter, how could you send Standard Error across thepipe in the following command?ls /etc/hosts /etc/h | tr h HWrite a simple PowerShell Script as follow:. Create a scheduled task using PowerShell. Create a schedule task which restarts a service of your choice. Add a write-host command with a name called "zack".Write a script to create a group called ”Eng1” and create 10 users with user name ”student1”-”student10” in ”Eng1” group. For each user, create a script that prints out ”Hello ${username}, welcome to "Eng1” and put the script in user’s home directory. Show command that were used with screenshots Linux, centOS7, VirtualBox
- The netstat programme, available for Linux and Windows, provides a list of active network connections. Describe how to use this command to identify whether a web page is not terminating connections or, if connection pooling is being used, is not returning connections to the pool. You may do this by looking at whether or not the connection is being returned to the pool. There is a possibility that connection pooling will not immediately terminate the connection.Set up a name server (ns1) for the domain happy.lab and its reverse zone on server. How would I go about doing this on a linux machine running Centos 7Can you run two client programs on a same host? Try it out, and explain how the server differentiate the two different processes (both running the same client code)? from socket import * serverName = 'localhost' serverPort = 12000 clientSocket = socket(AF_INET, SOCK_STREAM) clientSocket.connect((serverName,serverPort)) sentence = input('Input lowercase sentence:') byteToSend = str.encode (sentence) clientSocket.send(byteToSend) modifiedSentence = clientSocket.recv(1024) print('From Server:', modifiedSentence) clientSocket.close() from socket import * serverPort = 12000 serverSocket = socket(AF_INET,SOCK_STREAM) serverSocket.bind(('',serverPort)) serverSocket.listen(1) print ('The server is ready to receive') while 1: connectionSocket, addr = serverSocket.accept() sentence = connectionSocket.recv(1024) capitalizedSentence = sentence.upper() connectionSocket.send(capitalizedSentence) connectionSocket.close() from socket import * serverName =…
- Create a server side script using inbuilt modules from Node.js(OS, Path, File system and HTTP).You need to display the total number of JPG files in the current directory or you can choose a particular directory. Please make sure all sub-directories are included in the search for the jpg file. Please send me the Solution in Javascript using Node js Server (Consider the subdirectory condition as well) Thanks in advance1. Which of the following is not usually implemented in the server-side code? a. Routing Code b. All of these are usually implemented in Server-Side Code c. Authentication Logic Code d. User Interface Code 2. True or False. The fetch method can only be used to make GET requests. a. True b. False 3. True or False. Node.js is a asynchronous event-driven framework. This means it can only handle one event at a time a.True b. False 4. When using the router level middleware in express, what must match for the Handler Method to be executed? a. None of these b. Path and URL c. Request and Response d. Method and Pathpenetration programming Modify the .sh script so that it also works interactively. Specifically, if no hostname is given on the command line, the program should interactively ask for a hostname, starting port, and ending port with three separate prompts, and carry out its scan using those values. After scanning finishes, the program should loop to receive another set of values, stopping only when the user enters a blank host name. If this feature is implemented properly, it will also allow you to run the script in ’batch’ mode, by “piping in” a plain text file with the hostname on the first line, start port on the second, stop port on the third, and repeating for as many hosts as you wish to scan. For example, if a file named hosts_to_scan.txt contains a list of hosts and ports in the proper format, the program should now work as follows: cat hosts_to_scan.txt | ./portscanner.sh The timeout argument should still work in this case as well: cat hosts_to_scan.txt | ./portscanner.sh -t 3…

