Complete the following command so that it displays the output indicated below. Solution PS C:> -ComputerName hypervisor-1 PS C:\> $sessionHypervisorl -ClassName SMBIOSBIOSVersion : P92 Manufacturer: HP Name: P92 SerialNumber : 2M251604B4 Version : HP – PSComputerName : hypervisor-1
Q: A list is sorted in ascending order if it is empty or each item except the last one is less than or…
A: CODE IN PYTHON: def isSorted(inputList): if len(inputList) < 2: return True for i in…
Q: Table size is reduced by deleting columns that meet particular criteria in a relational database.…
A: The select procedure simply searches the table for data and acquires or retrieves entries depending…
Q: Is increasing the amount of duplication in a message beneficial or detrimental?
A: Any record in your marketing database that inadvertently shares data with another record is…
Q: The data fields for the inner class Node for a single linked list class contains : reference to the…
A:
Q: Build a C program that will input 10 values and arranged it from highest to lowest.
A: The answer of this question is as follows:
Q: What happens if the sender receives an acknowledgment before the window size in Go back N arq…
A: GO-BACK-N ARQ utilizes the protocol pipelining thought, in which numerous edges can be conveyed…
Q: What is the correct order for converting the source code into an executable file?
A: Source code the program code which is in high level language and this is in reader format. The…
Q: An application programming interface (API) is referred to as a "programming language" in computers.…
A: Introduction: API stands for application programming interface (API) several software intermediaries…
Q: When a block is being returned to main memory from the write buffer, what should happen if a…
A: Introduction: Data is updated to cache and memory at the same time in write-through. This method is…
Q: Based on the output, create a C++ program that will consider the variables as your declaration…
A: This program is basically asking to print the address of each variable named as num,count,…
Q: šiven the weighted graph below: ) Find the Minimum Spanning Tree (MST), using Prim's algorithm.…
A: a. find minimum spanning tree using prims algorithm. b. Now show the tree with minimum weight and…
Q: Which compiler phase would give you an error notice if you attempted to add an integer to a…
A: Introduction: Compiler: It is a translator that converts programs written in a high-level language…
Q: Compare and contrast the application protocols SMTP and HTTP. What is HTTP and how it works? What…
A: The HTTP and SMTP both are application layer protocol. HTTP stand for Hyper Text Transfer Protocol,…
Q: Describe how a keyboard can be considered a switch encoder.
A: keyboard is the one of most used computer input devices. A keyboard is like an electric…
Q: 17. The bit pattern 11011 is stored in a 5-bit shift-register. Assume that the shift- register has…
A:
Q: In order to create a comprehensive operations handbook, one must first figure out how to get the…
A: Introduction: The operations handbook is a document that guides persons unfamiliar with the firm,…
Q: Write the correct statement to store value of “vb programming” to label button 5 Select one: a.…
A: In this question we have to answer the two question. One is the regarding VB programming Second is…
Q: The Positive Ones There are different kinds of numbers, but among them all, the most commonly used…
A: As given, we need to write a C++ program that takes four numbers as input and count all the positive…
Q: need a simple html restraunt website code with JavaScript and important features of html such as…
A: Put the index.html and style.css files in one folder and run the index.html file in a browser like…
Q: If you had to choose, would you prefer to write an application in assembly code?
A: Introduction If you had to choose, would you prefer to write an application in assembly code?
Q: Write a C program language. Define a recursive function that will return the sum of all ODD…
A:
Q: puter Science Show the runtime stack and activations for the following recursive function. by…
A: Given : public static void printCharsReverse(String str) { if (str == null || str.equals(""))…
Q: Use DEV-C++ to develop a well-documented C++ program that: 1) Prompts the user to enter from the…
A: Code: #include <iostream>using namespace std;int main() { int n; //Iterating through the…
Q: Create a Form Using JavaScript to make sure all the data are entered correctly in your form. Send…
A: Code: create table using below CREATE TABLE `employee_data`.`employee` (`emp_name` VARCHAR( 30 ) NOT…
Q: Which of the following should replace so that the code segment works as intended? FOR EACH vote IN…
A: The answer is discussed in next step with explanation
Q: What is the output of the given program below if the inputted value is 2 #include #include void…
A: Code : Output :
Q: Make the "Happy Birthday Program". Must work in Linux and needs to use C++ and x86 assembly.
A: Solution: Given,
Q: a suitable datapath design (multiplexers, registers, ALU operations biocks, buses, signals..etc)…
A:
Q: what is core, peripheries, and semi-peripheral states? explain simply
A: Given To know about the core, peripheries, and semi-peripheral states.
Q: Using VBA: Write a guessing game where the user has to guess a secret number. After every guess the…
A: Guessing game where the user has to guess a secret number. After every guess the program tells the…
Q: The concepts of virtual memory and virtual machines should be compared. To what extent do the…
A: Introduction: Virtual memory is a memory management approach that allows secondary memory to be…
Q: w does computer help you on your daily activities and what is the advantage and disadvantage of…
A: Below the advantage and disadvantage of computer to us on our daily lives
Q: the F/C pin is placed at a logic 1 level, the crystal oscillator is disabled. Where is the timing…
A:
Q: Demonstrate the output of the given code below int x=0,ctr=1; do { ctr++; x++; printf(“%d…
A: Demonstrate the output of the given code below: Output:
Q: Write a code that will loop by inputting any integer and displays whether the integer is “POSITIVE”…
A: As no programming language is mentioned, it is solved using basic C++
Q: can a deadlock occur when you only have one process running on the system (in other words, can a…
A: Answer
Q: Recall the selection sort algorithm from class. Given the following list, what would be the state of…
A:
Q: Create the K-maps and then simplify for the following functions: I) F(x,y,z) = x′y′z′ + x′yz′ +…
A: F(x,y,z) = x′y′z′ + x′yz′ + xy′z′ + xyz′ x'y'z' -0 x'yz' - 2 xy'z' - 4 xyz' - 6
Q: Consider what would happen if you modified your system's default runleveltarget to something ike…
A: Introduction: On Unix-like systems, like Linux, the current operating state of the operating system…
Q: Write an executable program that reads the current system date and write it in your language in…
A: According to the information given:- We have to Write an executable program that reads the current…
Q: 2. Refer to the statement below, #include void main(){ int ij: for(i=0;i<5;i++) { for(j=0;j<5;j++){…
A: I modify your code as per the output and provide the code ,output and their screenshot
Q: Use an example to demonstrate data manipulation, forgeries, and web jacking.
A: Introduction: When it comes to data manipulation, changing or altering data to make it more readable…
Q: How does emerging technologies associated with Human-Computer Interaction (HCI)?
A: Human–Computer Interaction is the analysis of how computer technology influences human labour and…
Q: What exactly is deductive proof?
A: Intro A deductive proof is made up of a series of assertions that begin with a hypothesis and end…
Q: How did Ubuntu get its start as a branch of another Linux distribution?
A: Introduction: He came up with the idea for of the Ubuntu Foundation in 2004. He was born in South…
Q: Explain the differences between an SSD and a magnetic disc.
A: Introduction SSD: The full form of SSD is Solid-State Drive. It is nothing but a huge storage…
Q: For system development, what does it take to be a successful team member? How do you ensure…
A: The solution to the given question is: Introduction Creating new software from concept to completion…
Q: Explain what is configuration management. What would be the benefits of configuration management ?
A: answer is
Q: Why do we employ MATLAB to tackle challenges in Computational Geometry?
A: Introduction: MATLAB is a high-performance computer language for engineers. It has a user-friendly…
Q: Find the complexity of the following blocks of code or algorithm’s description your answer must…
A:
May you please assist with this hypervisor powershell fill in the blank
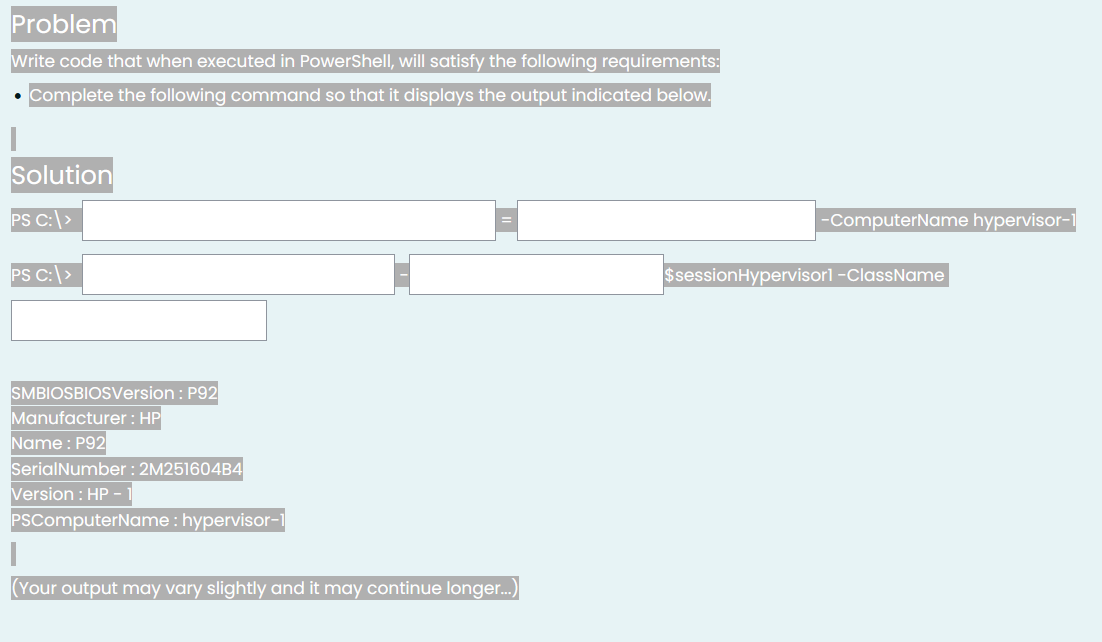
Step by step
Solved in 2 steps

- Please answer properly with output screenshot must Where is the error in this code? from telethon.sync import TelegramClientfrom telethon.tl.functions.messages import GetDialogsRequestfrom telethon.tl.types import InputPeerEmptyimport os, sysimport configparserimport csvimport time re="\033[1;31m"gr="\033[1;32m"cy="\033[1;36m" def banner():os.system('clear')print("ok") cpass = configparser.RawConfigParser()cpass.read('config.data') try: api_id = cpass['cred']['id'] api_hash = cpass['cred']['hash'] phone = cpass['cred']['phone'] client = TelegramClient(phone, api_id, api_hash)except KeyError: os.system('clear') banner() print(re+"[!] run python3 setup.py first !!\n") sys.exit(1) client.connect()if not client.is_user_authorized(): client.send_code_request(phone) os.system('clear') banner() client.sign_in(phone, input(gr+'[+] Enter the code: '+re))os.system('clear')banner()chats = []last_date = Nonechunk_size = 200groups=[]result =…Below is cache.py. Make sure the code works properly and is plagarism free. Make sure to show the screenshot of the output with the screenshot of the code being tested as plagarism free. cache.py import socketimport sys def handle_client(client_socket): while True: command = client_socket.recv(1024).decode() if not command: break if command == 'quit': break elif command == 'put': receive_file(client_socket) elif command == 'get': send_file(client_socket) else: print("Invalid command.") break client_socket.close() def receive_file(client_socket): pass def send_file(client_socket): pass def main(): if len(sys.argv) != 4: print("Usage: cache.py <port> <server_ip> <server_port> <transport_protocol>") return port, server_ip, server_port, transport_protocol = int(sys.argv[1]), sys.argv[2], int(sys.argv[3]), sys.argv[4]…The Cupid matchmaking Service maintains two files - one for the male clients and another for female clients. Each file contains a client ID, last name, first name, and address. Each file is in client ID order. Use the provided pseudocode to write a C++ application that merges the two files into one file containing a list of all clients, maintaining ID member order. // Pseudocode Project8// Start// Declarations// InputFile inFile1;// InputFile inFile2;// OutputFile outFile1;// num mClientNumber, fClientNumber// string mClientName, fClientName// bool atLeastOneFileNotAtEnd = true// bool inFile1Written = false// bool inFile2Written = false// output "File merge processing starting"// open inFile1 "MaleClients.rtf"// open inFile2 "FemaleClients.rtf"// open outFile1 "MergedClients.rtf"// read mClientNumber and mClientName from inFile1// read fClientNumber and fClientName from inFile2// while ( atLeastOneFileNotAtEnd == true )// if (inFile1 is EOF)// if (inFile2Written == false)// output…
- This exercise is will require you to write a C program that is able to run Linux commands from theprogram when executed. The program should be able to perform the following operations:1. Take a Linux command as an input from the user using scanf in C.2. This command should be a valid Linux command3. The program should use execvp(char *command, char *params[]) function to run this Linux commandand produce and output on the console.4. The screenshot below shows the expected output of the program:Instructions:• Write the C program in any editor of your choice. • Use execvp(char *command, char *params[]) function to run the commandsa) Create a system call int sys_wolfie(void *buf, uint size), which copies an ASCII art image of Wolfie to a user-supplied buffer, provided that the buffer is large enough. You are welcome to use an ASCII art generator, or draw your own by hand. If the buffer is too small, or not valid, return a negative value. If the call succeeds, return the number of bytes copied. B) Write a user-level application, called wolfietest.c, that gets the Wolfie image from the kernel, and prints it to the console. When the OS runs, your program's binary should be included in fs.img and listed if someone runs ls at the xv6 shell's command prompt. Language in CBelow is server.py. Make sure the code works properly and is plagarism free. Make sure to show the screenshot of the output with the screenshot of the code being tested as plagarism free. server.py import socketimport sys def handle_client(client_socket): while True: command = client_socket.recv(1024).decode() if not command: break if command == 'quit': break elif command == 'put': receive_file(client_socket) elif command == 'get': send_file(client_socket) else: print("Invalid command.") break client_socket.close() def receive_file(client_socket): pass def send_file(client_socket): pass def main(): if len(sys.argv) != 3: print("Usage: server.py <port> <transport_protocol>") return try: port, transport_protocol = int(sys.argv[1]), sys.argv[2] except ValueError: print("Invalid port number.") return…
- if the user click on create account or on login with empty text info (without entering the desired info like name and DOB before clicking on create account for example ) the program crashes, can you figure out why and fix it import tkinter as tkfrom datetime import datetime, timedeltaclass ATM: def __init__(self): self.accounts = {} def create_account(self): # Get user inputs first_name = first_name_entry.get() last_name = last_name_entry.get() dob = dob_entry.get() address = address_entry.get() debit_card = debit_card_entry.get() while len(debit_card) != 16 or not debit_card.isdigit(): debit_card = input("Invalid debit card number. Enter debit card number (16 digits): ") pin = pin_entry.get() while len(pin) != 4 or not pin.isdigit(): pin = input("Invalid pin. Enter 4-digit pin: ") # Create account and update GUI self.accounts[debit_card] = {"first_name":…Below is a sequence of shell commands that we typed into a bash terminal window on a Linux machine and some of the output that was produced. Your job is to write the output produced by the commands in the sequence. The commands are executed consecutively and changes made by one command may affect the output produced by later commands. First Create a Directory and Rename as Name_AridNo like (Ali_18-Arid-102) and then execute the following commands and show output. Shell > pwd /home/me/test > ls -F hw1 hw1.bak tmp/ > bash > touch it > cd tmp > ls –F justme.txt > echo “Dear Ali” > diary > cat ‘Name_AridNo’ /etc/hosts > pwdIn Chapter 11, you created the most recent version of the MarshallsRevenue program, which prompts the user for customer data for scheduled mural painting. Now, save all the entered data to a file that is closed when data entry is complete and then reopened and read in, allowing the user to view lists of customer orders for mural types.
- I have a code (class Server). I need help to fix error in another class. These are 2 seperated files. import socketimport pandas as pdimport sqlite3class Server:def __init__(self, portnumber):self.port = portnumberself.s = socket.socket()self.host = socket.gethostname()self.s.bind((self.host, self.port))self.s.listen(5)print('Server listening....')def __enter__(self):return selfdef __exit__(self, exc_type, exc_val, exc_tb):self.close()def serve(self):while True:conn, addr = self.s.accept()print('Got connection from', addr)query = conn.recv(1024).decode()print('Server received query:', query)# Process the SQL query and retrieve datadata = self.process_query(query)# Send the data back to the clientconn.sendall(data.to_msgpack())print('Sent data:', data)conn.close()def process_query(self, query):# Connect to the SQLDatabase and execute the queryconnection = sqlite3.connect('data.db')data = pd.read_sql_query(query, connection)connection.close()return datadef close(self):self.s.close()# Run…Please identify the correct statement(s) for the following code snippet from the script: while inst_iter.hasNext() and not monitor.isCancelled(): ins = inst_iter.next() addr = ins.getAddress() pcodeList = ins.getPcode() for pcode in pcodeList: if pcode.getOpcode() == PcodeOp.FLOAT_DIV or pcode.getOpcode() == PcodeOp.INT_DIV: print("Address: {}, Inst: {}, Pcode: {}".format(addr, ins, pcode)) addrSet.add(addr) Question 1 options: It saves the address of the disassembled instruction that introduces division. This snippet uses refined/high p-code. This snippet uses raw p-code. It uses p-code opcode to identify the division operator. It uses the mnemonic string of a disassembled instruction to identify the division operator. It saves the sequence number of the p-code instruction that introduces division.Please write the program and explain-line-by-line. Thank you! A shell interface gives the user a prompt, after which the next command is entered. The example below illustrates the prompt osh> and the user's next command: cat prog.c. (This command displays the file prog.c on the terminal using the UNIX cat command.) osh>cat prog.c One technique for implementing a shell interface is to have the parent process first read what the user enters on the command line (in this case, cat prog.c) and then create a separate child process that performs the command. Unless otherwise specified, the parent process waits for the child to exit before continuing. This is similar in functionality to the new process creation illustrated in Figure 3.9. However, UNIX shells typically also allow the child process to run in the background, or concurrently. To accomplish this, we add an ampersand (&) at the end of the command. Thus, if we rewrite the above command as osh>cat prog.c & the…





