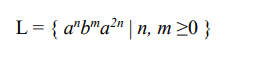
Convert the following CF language over the alphabet ∑={a,b} to Contect Free grammar CFG?
Q: lef foo(arg): if isinstance (arg,-): return 'yeah' else: return 'oops' print (foo (3.14)) print (foo…
A: So here in the code, I am checking the type of input. For foo(3.14) it is returning oops that is in…
Q: Question :- D Computer Science Using SQL statement Create a table name person containing seven…
A: Hello student
Q: Explain the different BGP messages (List 4) and elaborate what they are used for?
A: The above question is solved in step 2 :-
Q: In the Clark-Wilson model, must the TPs be executed serially, or can they be executed in parallel?…
A: It is important to make sure that the TPs in the Clark-Wilson model are executed serially rather…
Q: f. Which measure of center (mean or median) is more appropriate for these data? Why? Consider the…
A: “Since you have asked multiple question, we will solve the first question for you. If you want any…
Q: Develop assembly language program to find the average of three 8-bit numbers.
A: an assembly language program in 8086 microprocessor to find average of n eight bit numbers:-
Q: What distinguishes Doom from other video games?
A: Video games: Id Software created the 1993 first-person shooter (FPS) game Doom for MS-DOS. The…
Q: Question 4,5 , using R
A: Solution - A) A=rand(200,1) % 200 random numbers use rand or randn b=randi(200,100,1) %…
Q: Solve the following recurrences assuming that T(n) = Θ(1) for n ≤ 1. a) T (n) = 3T (n/π) + n/π b)…
A: We have to provide solutions for two recurrences given below assuming that T(n) = Θ(1) for n ≤ 1.…
Q: Write a code which will take input as 2 numbers (INT first, INT second) and print 4 outputs (add,…
A: Solution- Python programme for multiplying, dividing, and adding two numbers In order to add,…
Q: Compare IS-IS and OSPF routing protocols in terms their similarities and differences? List and…
A: What Does Routing Protocol mean? The most efficient pathways for network data transfer and…
Q: Algorithm for The greatest common divisor sequential algorithm
A: The algorithm that is used to find the GCD of two numbers. The algorithm show below is one of the…
Q: Cipe Q.13 How is a Hill cipher vulnerable to chose plaintext attack?
A: Answer: Lester S. Hill created the Hill cypher in 1929, which is a rather archaic polygraphic…
Q: Running on a particular treadmill you burn 4.2 calories per minute. Write a program that uses a…
A: The solution is given in the below steps for your reference.
Q: When do you lose access to your WordPress admin and see a blank page as the homepage of your…
A: Given question :- When do you lose access to your WordPress admin and see a blank page as the…
Q: P0
A: Circuit code is below:
Q: What particular tasks may a data manipulation language perform?
A: We have to write which tasks may a data manipulation language(DML) perform. Data Manipulation…
Q: This question concerns the field GF(256). The modulus is P(x) = x³ + x² + x³ + x + 1. For computing…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: How do you reverse a transaction? a. Use UNDO feature b. Use ROLLBACK c. Set AUTOCOMMIT…
A: answer starts from step 2
Q: escribe how a computer program might be t d efficiently on a modern pipelined compute as on these…
A: Design:
Q: Cipres Q.13 How is a Hill cipher vulnerable to chose plaintext attack?
A: The answer is given in the below step
Q: At what rate must the attacker continue to send TCP connection requests to this system in order to…
A: Please find the detailed answer in the following steps.
Q: Use the Pumping Lemma to show that each of the languages below is not context-free. 1. B = {0″ #0²…
A: 1. B = {0" #02" #03" In > 0} Suppose B is a context-free language. Then there exists a number p…
Q: In trying to delete from the track table, what is the cause of this error? "Query failed because of:…
A: The correct answer is given below with proper explanation Happy to help you ?
Q: What are Impossibility of Min Process Non-blocking Checkpointing in any operating system.
A: A min-process, non-blocking checkpointing algorithm is one that forces only a minimum numberof…
Q: Q1 in c++ Q1/ write a program to draw a truth table of the following logic circuit: using iostream…
A: - We need to create a truth table of the circuit provided. - We will need a few arrays which will…
Q: Any fan of the late author Douglas Adams (The Hitchhiker's Guide to the Galaxy) knows that 42 is a…
A: Code: def great_42(a, b): # if either a's or b's value is 42 then return True if a == 42 or b…
Q: Make a DFA for recogninzing the keywword 'ELSEIF'
A: The answer is
Q: In one or two paragraphs, the Frama-C Platform may be summed up. Will having the Frama-C platform…
A: Frama-C is an open-source platform for analyzing C source code. Frama-C analyzers help with source…
Q: How is the use of SQL in relation to ROLAP?
A: SQL Stands for Structured Query Language.
Q: Mobile Applications and Intelligent Systems are two of the most advanced information system types…
A: Information system : Computers, tablets, cellphones, hard drives, and other gadgets are examples of…
Q: This course will help you comprehend cloud computing, social networking blogs, and a variety of…
A: Hello student The answer will be in next step :-
Q: Write the recursive version of the function decimal which takes in an integer n and returns a list…
A: - We need to code the digit return problem in python.
Q: Data Structures and Algorithms are used by computer programming students to design and retrieve data…
A: Introduction: In databases, data retrieval is the process of discovering and extracting data based…
Q: For instance, a data structure for which there is no array- or link-based solution. Existe una…
A: Introduction: A data structure may also be described as an algebraic structure that holds data on…
Q: ✓ Allowed languages C Problem Statement Create a program that will determine whether a triple can…
A: The answer for the above mentioned question is given in the below steps for your reference.
Q: What is inheritance with respect to OOP? (You must mention appropriate terminology) In your…
A: Inheritance:- Inheritance is a way to represent the relationship between the objects. This is a…
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: In the third раrty mаintenаnсe (TРM) industry, netwоrk mаintenаnсe is essentiаlly whаt…
Q: 3.19 LAB: Longest string Write a program that takes two strings and outputs the longest string. If…
A: Below is your code with well defined comments and Output.
Q: 91 92 93 94 95 A₁ A2 A3 A4 0 1 1 1 1 1 1 0 0 0 0 1 1 1 1 (a) A5 0 1 0 1 1 1 0 0 0 0 S₁ S₂ S3 91 10…
A: The answer for the above mentioned question is given in the below steps for your reference.
Q: Suppose we have the following sets: P, Q, and R. Prove or disprove that if for all x, (x ∈ P) → ((x…
A: Hello student The answer will be in next step :-
Q: Data Structures and Algorithms are used by computer programming students to design and retrieve data…
A: Data Structure: For a computer's memory to be used quickly and efficiently, information is organised…
Q: Which clause is used to change a column in a table? a. SET b. MODIFY c. ALTER d.…
A: Introduction In order to update, insert, delete, create and alter database tables and views, among…
Q: The prefix of (A+B)*(C-D) is a. +-AB*(C-D) b. *+-ABCD C. *+AB-CD d. *AB+CD
A: Reverse the expression and also change parenthesis from open to closed and closed to open Calculate…
Q: 8.12 (Simulation: The Tortoise and the Hare) In this exercise, you’ll re-create the classic race of…
A: Here I am providing a C++ code for the given problem. This code performs a race of the tortoise and…
Q: 3.5.4 Exercises for Section 3.5 Exercise 3.5.1: For each of the relation schemas and sets of FD's of…
A: 2NF (second normal form) The idea of full working dependency is the foundation of second normal form…
Q: Given a string, write a function to check if it is a permutation of a palindrome. A palindrome is a…
A: A palindrome is a string that is the same forwards and backwards. Therefore, to decide if a string…
Q: Explain classful and classless routing behaviour in a routed network? Elaborate your answer with an…
A: The above question is solved in step 2 :-
Q: Computer Science Write a strong password policy for an organization that is consistent with the…
A: The answer for the above question is given in the following step
Q: Which results would show if the employee table LEFT JOINed the customer table? All rows from the…
A: Left join : All the records from the left table and the matched data from the right tables are…
Convert the following CF language over the alphabet ∑={a,b} to Contect Free grammar CFG?
Step by step
Solved in 2 steps

- Construct a DFA A so that L(A) = L(N) where N is the following NFA:Convert to C language #include <bits/stdc++.h>using namespace std; //hash function 2int main(){ int n; cout << "enter number\n"; cin >> n; //f(n)=rand()*n cout << n << "->" << (rand() * n) % 10; return 0;} Output:/* segvhunt.cFind and eliminate all code that generates Segmentation Fault*/#include <stdio.h>int main() {char **s;char foo[] = "Hello World";*s = foo;printf("s is %s\n",s);s[0] = foo;printf("s[0] is %s\n",s[0]);return(0);}
- Place the following functions into their proper asymptotic order: f1(n) = n2log2n; f2(n) = n(log2n)2 ; f3(n) = 20 + 21 + .. + 2n ; f4(n) = log2 ( 20 + 21 + .. + 2n ).Q5) Let Σ = {0, 1}. Convert the following NFA's to DFA's:Use C++ Programming to implement this function bool ban_country(const char* nation) Removes all the entries bearing the country equal to the given nation. Return true if at least one entry has been removed, otherwise return false.



