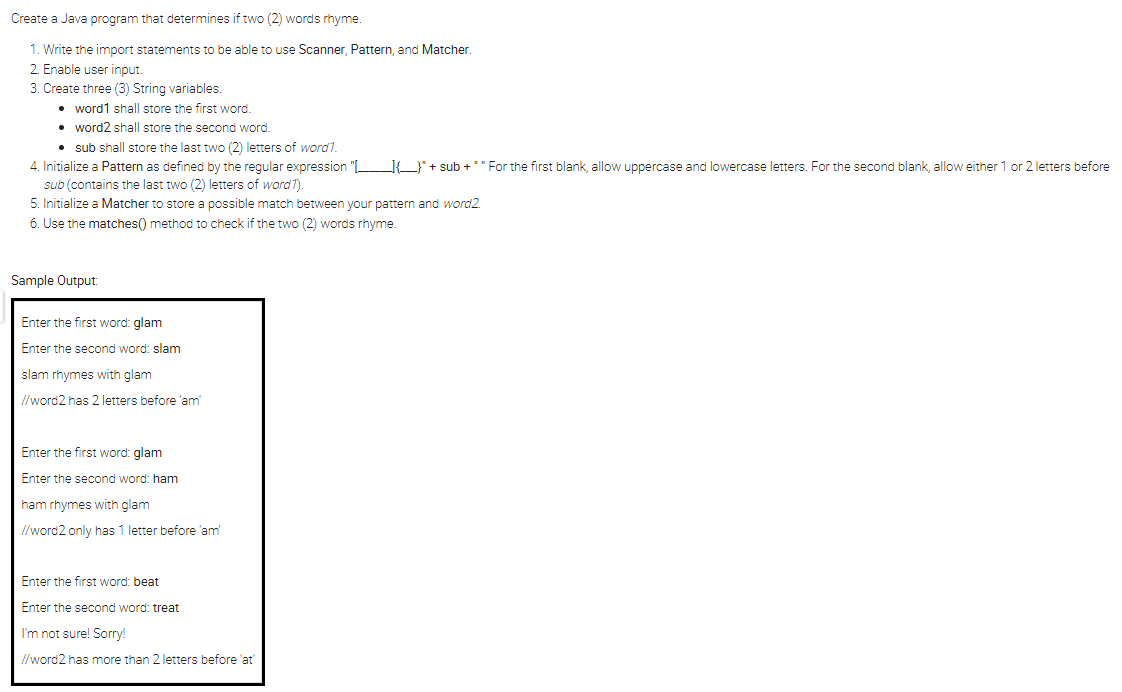
Create a Java program that determines if two (2) words rhyme.
Q: Write a C++ program to read two one dimensional array and exchange between them
A: Your C++ program is given below as you required with an output.
Q: What are the finest [authentication and access control] security tools?
A: Intro control: establish measures to address identified threats/weaknesses.As a defensive measure,…
Q: In what ways is cyber crime important?
A: Cyber Crime: Cybercrime, often known as computer crime, is the use of a computer for criminal…
Q: I am doing a word guessing game where I have created a function that shuffles a word randomly.…
A: Jumbled word is given to player, player has to rearrange the characters of…
Q: When accepting electronic payments online, what are the best security practises?
A: Introduction: Best security techniques are as follows:
Q: Cloud computing vs grid computing: what's the difference, and how do you decide?
A: Introduction Cloud Computing Cloud computing employs a client-server architecture to distribute…
Q: The gadget that generates hardcopy graphics is referred to as a "plotter" informally. why?
A: Plotter: A plotter is a printer that uses one or more automated pens to create line drawings on…
Q: In the next sections, we will go further deeper into application layer protocols and network…
A: Intro A network application is any software that runs on a single host and communicates with another…
Q: display
A: Given : Store a positive integer in variable N and display the Nth term in the arithmetic sequence,…
Q: How does the application software return to its regular mode of operation after the interrupt…
A: Operating system: Operating system offers interaction between application programme and CPU.…
Q: Why is the implementation of a Software-Defined Network (SDN) in educational institutions so…
A: Justification: The user may do operations at extremely specified time intervals by using the time…
Q: As a member of a bank's information system staff, you are required to do system maintenance tasks in…
A: Given: As a member of the staff of an information system in a banking system, one of your…
Q: Describe how Application Programming Interfaces (APIs) may be utilised to aid in the integration of…
A: Intro A computer and its associated hardware that has become obsolete but is still in operation…
Q: When looking for a printer firmware update, what should you look for?
A: Checks the firmware on the touch screen of the printerView the firmware version number currently…
Q: What are the advantages of using a relational database management system, as well as its…
A: Your answer is given below. Introduction :- This sort of database management system stores data in…
Q: What perspectives should be considered while developing models of software-intensive systems?
A: A software-intensive system is, by definition, any framework where programming impacts a huge…
Q: Define the phrase "queue head structure."
A: Introduction: A queue is a data structure that uses the FIFO method, which means that the elements…
Q: Provide an explanation of the goal, and then go on to detail how your proposed code solution would…
A: INITIATION: In coding, you instruct the computer to examine conditions by writing limiting…
Q: What is dynamic memory allocation and how does it work? What are the advantages of employing this…
A: Dynamic Memory Allocation: When a running application requests a block of main memory from the OS,…
Q: When it comes to documentation for Visual Studio, where can you get it? What kind of tools does the…
A: Introduction: The MSDN Library includes essential programming materials for creating online services…
Q: Which of the following is the most significant role that a firewall plays? How should one go about…
A: Introduction: A firewall is a security apparatus, PC equipment, or programming, that can assist with…
Q: Explain how any business analytics classes you took had an impact on the group projects and/or tasks…
A: Given: Experiential Learning gives students with firsthand experience, allowing them to integrate…
Q: Why is the implementation of software-defined networking (SDN) in educational institutions so…
A: What is the SDN? Software-defined networks are abbreviated as SDN. As its name indicates, it is a…
Q: etworks" is exactly what it sounds like. Do routers fall under this category? What does the…
A: Over layers of network: A logical PC network that is built on top of one more physical network is…
Q: Starting with the most critical, below are the factors that affect the Big-O performance of a hash…
A: The following is a list of the crucial factors that determine how well a hash table performs…
Q: Compilers struggle to implement either the VLW or superscalar architectures. Which architecture is…
A: Intro A superscalar processor may carry out many instructions in a single clock cycle. They…
Q: capabilities of a desktop operating system?
A: Operating System: An operating system connects people to their computers. It enables the effective…
Q: Which of the following is the most significant role that a firewall plays? How should one go about…
A: Firewall system: A Firewall is a network security device that monitors and filters incoming and…
Q: In the code editor, you are provided with an initial code which has main() function. In the main(),…
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT…
Q: There are two different types of problems that may be tackled with the help of simulation models.
A: Simulation models: The act of generating and studying a digital prototype of a physical model in…
Q: Compare the results of abstraction using computer science examples. Software engineering is an…
A: Intro Our goal is to investigate both the notion of abstraction and the significance of abstraction…
Q: Use diagrams to tell the difference between a scalar and a superscalar processor. Compared to scalar…
A: Encryption: There are many varieties of computer processor hardware, including scalar and…
Q: The X oints is the name of the model used when designing databases.
A:
Q: Which firewall architecture is now the most widely used by businesses? Why? Explain.
A: Start: An internet firewall is a device that performs cybersecurity duties by filtering traffic on a…
Q: The importance of continuous event simulation, together with four arguments in support of it
A: Please find the detailed answer in the following steps.
Q: What is the distinction between cloud and grid computing?
A: Cloud computing : It uses a client-server architecture to deliver computing resources such as…
Q: On the other hand, the majority of computer systems use a lower number of layers than what is…
A: The OSI layer model is known as (Open Systems Interconnection Model). The OSI model is a conceptual…
Q: What exactly is the role of the central processing unit, and what exactly does it do? What are your…
A: A computer system includes hardware and software. CPU, memory, I/O, and storage are included.…
Q: Search the Internet for information security materials that are available to the general public. We…
A: Intro What does information security entail?The act of securing information through reducing…
Q: What sort of layout for a website's domain would be most suited for a social networking platform?
A: Start: People are increasingly using social networking sites (SNSs) as a place to congregate online.…
Q: What are the OSI model's flaws and how do they work?
A: Intro MAC addressing failures, duplex faults, collisions, CRC frame mistakes, and spanning-tree…
Q: del-View-Controller fit into the overall fram of the ways that using an MVC design migl
A: MVC sorts out web applications. MVC design's benefits Answer: MVC sorts out web applications. MVC…
Q: Investigate the problem with the graph's coloring. Examine both greedy and backtracking algorithms…
A: Introduction:
Q: What are some of the reasons why you believe that the quality of the data is one of the most…
A: Here i am discussing about data quality in data warehouse:…
Q: Hello, I've attached the prompt for this assignment. I need help creating code to delete and update…
A: The code is given below. import java.util.*; public class ContactService { //Start with an…
Q: Is the external bus in the von Neumann design exclusively for data memory
A: Introduction Program and instruction data are stored in the same memory in the von Neumann…
Q: Which two types of technology are found in the vast majority of wireless systems?
A: Which two technologies are the most prevalent in wireless systems? Therefore, we must identify and…
Q: The data tablet consumes a far lower amount of computer time than the light pen does, and it…
A: The data tablet consumes a far lower amount of computer time than the light pen does, and it…
Q: What is the difference between the terms World Wide Web and Internet?
A: Institution: The terms "World Wide Web" and "Internet" may apply to a wide range of topics,…
Q: When learning about binary search trees in C++, what are some examples of the real-world…
A: Introduction The binary tree is like a tree with hierarchies of nodes. Where the topmost node is…
Create a Java program that determines if two (2) words rhyme.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Create a Java program that declares and initializes a string variable "dayOfWeek" with a value of your choice (e.g., "Monday", "Tuesday", etc.). Use a "switch" statement to check the value of "dayOfWeek" and output a message to the console indicating the corresponding day of the week. For example, if "dayOfWeek" is "Monday", output a message saying "Today is Monday". Use "default" to output a message for any invalid value of "dayOfWeek".Please help me comment these lines of code. Please not these are just some lines of code that have been taken from the java program I am creating which is a coin toss program. I do not need you to create one. Just comment what the lines of code below private static String sideUp; } public void toss() { Random in = new Random(); int x = in.nextInt(); if (x % 2 == 0) sideUp = "Heads"; else sideUp = "Tails"; } public static void main(String[] args) { int tail = 0, head = 0; System.out.println("\nTossing coin 20 times:-"); for (int i = 1; i <= 20; i++) { coin.toss(); if (coin.getFace().equals("tails")) tail++; else head++;Create a Java program that determines if two (2) words rhyme. Write the import statements to be able to use Scanner, Pattern, and Matcher.Enable user input.Create three (3) String variables.word1 shall store the first word.word2 shall store the second word.sub shall store the last two (2) letters of word1.Initialize a Pattern as defined by the regular expression "[______]{___}" + sub + " " For the first blank, allow uppercase and lowercase letters. For the second blank, allow either 1 or 2 letters before sub (contains the last two (2) letters of word1).Initialize a Matcher to store a possible match between your pattern and word2.Use the matches() method to check if the two (2) words rhyme. Sample Output: Enter the first word: glam Enter the second word: slam slam rhymes with glam //word2 has 2 letters before 'am' Enter the first word: glam Enter the second word: ham ham rhymes with glam //word2 only has 1 letter before 'am' Enter the first word: beat Enter the second word: treat…
- Write a complete Java program that does the following: Asks the user to enter his / her name, age, student ID, and GPA. Stores the entered information in adequate variables. Prints the student’s name, age, Student ID, and GPA using "printf" method. All information should be printed in one line separated by tap space. Note: The class name of your Java program must be your first name followed by (_) and your student ID. Your answer should have the code as text as well as the screenshot of the program output (using your own student ID) as a part of your answer. Otherwise, zero marks will be awarded.1. Write a program that will input a password and test if the password is correct and display the message “Password Accepted” otherwise, display “Invalid Password”. Use Java programmingWrite an Java application that determines whether a phrase entered by the user is a palindrome. A palindrome is a phrase that reads the same backward and forward without regarding capitalization or punctuation. For example, “Dot saw I was Tod”, “Was it a car or a cat I saw?”, and “Madam, I’m Adam” are palindromes. Display the appropriate feedback: You entered a palindrome or You did not enter a palindrome. import java.util.*; public class Palindrome { public static void main(String[] args) { // Write your code here } }
- Write a Java program that prompts the user to enter a password that matches a specific pattern **USING A SINGLE REGEX STATEMENT** as covered in your textbook. Your program must approve the user's entry.. Here is the pattern, in this order: 1 or more upper case letters two lower case letters 1 or 2 digits zero or 1 upper case letters any two of this group @#$%^& If password is not correct user must be prompted to enter a new password until conditions are metCreate a JAVA program Write a program that reads total marks of 5 students and give their grades according to the following table. (Can we use switch?) Total mark Grade Equal or above 90 A Between 80 and less than 90 B Between 70 and less than 80 C Between 60 and less than 70 D Less than 60 FWrite a program that will calculate car insurance premium using Java!!! Steps to write a program: First things first, your program should ask customer to provide a name, so display a message: "Enter your name". Then ask user about ownership of US driver license. Display message: "Do you have a US driver license?". If user doesn't have a US driver license - display warning message: "Invalid data!" and stop the program (_use System.exit(0) after displaying warning message to stop the program_). Then ask user to provide a zip code. If zip code equals to 20910 or 20740, add $60 to the premium (an amount to be paid for an insurance policy). If zip code equals to 22102 or 22102 , add $30 to the premium. Otherwise add $50 to the premium. Then ask user about car ownership. Display message: "Is this vehicle Owned, Financed, or Leased?". If car is owned, add $10 to the premium, otherwise add $20 to the premium. Then ask user about car usage. Display message: **"How is this vehicle primarily…
- create a java program that the user will input a String. check the inputed string if its a palindrome display to the user wether the inputed string is palindrome or notWrite a Java program that will ask the user to enter an integer number and then reverses the number. Then check whether the input number and the reversed number are same. If it is display the message that they are same else displays the message that they are not same. Name the program Lab8.java Use a one-line comment before each block to describe what you are doing – don’t describe the code syntax, but rather the purpose of the code. These comments should effectively describe the steps in your “algorithm.” Sample run: Please enter a number: 39193 The reversed number is: 39193 The given number and reversed number are same.Write a complete Java program that prints out the following information: Ask the user to enter the last three numbers of the student ID. Read the input and store it in a suitable variable. Find and print the Square root of the inputted number, using a Math function. The class name should be your Name. Note: Your answer should have the code as text, as well as a screenshot of the code with the output. The inputted number should be the last three digits of your Student ID number. Name is Rabab ID is 190058401

