Create a Python GUI program that will search, add, save and delete student information stored in a textfile. it should have abuttonSearch , buttonNew , buttonSave and buttonDelete.
Create a Python GUI program that will search, add, save and delete student information stored in a textfile. it should have abuttonSearch , buttonNew , buttonSave and buttonDelete.
Principles of Information Systems (MindTap Course List)
13th Edition
ISBN:9781305971776
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter4: Software And Mobile Applications
Section: Chapter Questions
Problem 2SAT
Related questions
Question
Create a Python GUI
it should have abuttonSearch , buttonNew , buttonSave and buttonDelete.
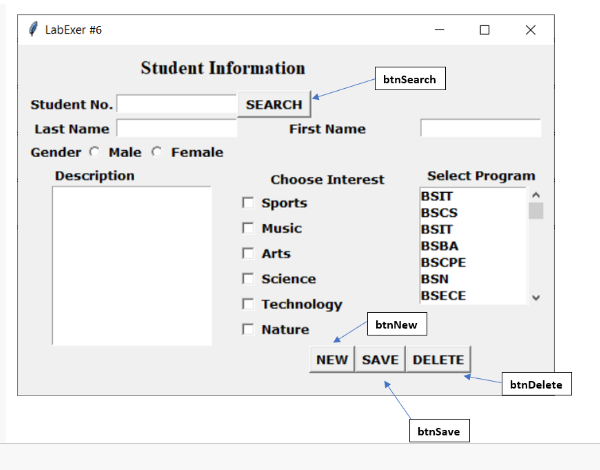
Transcribed Image Text:LabExer #6
Student No.
Last Name
Gender Male Female
Description
Student Information
SEARCH
X
Select Program
BSIT
BSCS
BSIT
BSBA
BSCPE
BSN
BSECE
btnNew
NEW SAVE DELETE
btnSave
btnSearch
0
First Name
Choose Interest
Sports
Γ Music
Arts
Science
Technology
Nature
btnDelete
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning