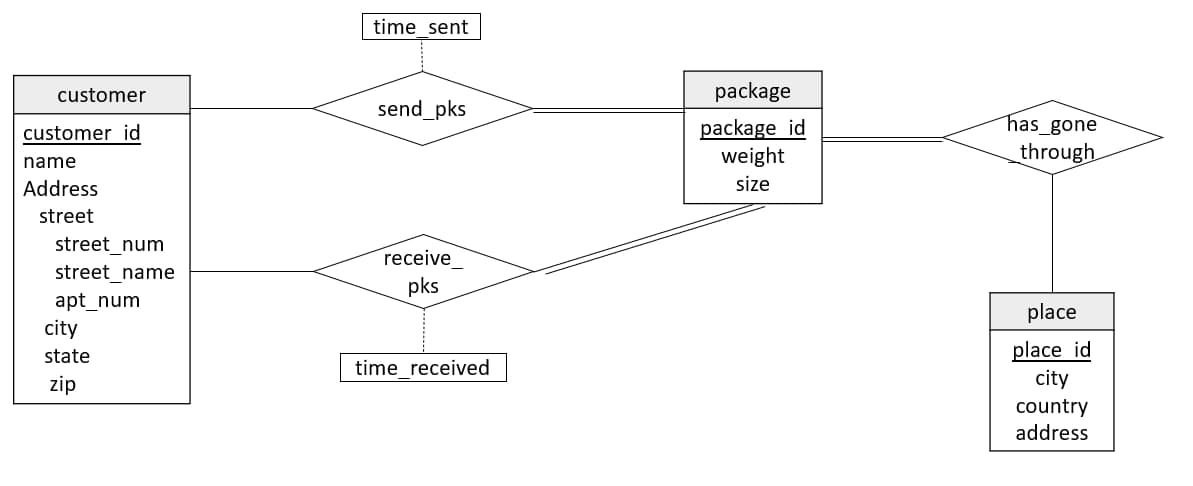
customer customer id name Address street street_num street_name apt_num city state zip time_sent send_pks receive pks time_received package package id weight size has_gone through place place id city country address
Q: What exactly is a batch file
A: Batch File A batch file is a content record that stores orders to be executed in a chronic request.…
Q: Draw the state diagram of the machine that performs the following operation: The machine turns on…
A: State machine diagram which is also known state chart or state transition diagram shows the…
Q: The CCR model is always achievable in nature, not equal to the aggregate. prove it
A:
Q: Comparison of binary trees and heaps is made. Do you want to talk about operational efficiency?
A: Binary Tree: A Complete Binary Tree is the Heap. Arrays are widely used to implement heaps. Any…
Q: What is a computer language called Data Definition Language? Give me an example of what you're…
A: Data Definition Language (DDL) is a set of SQL commands that creates and deletes locations,…
Q: ways to make the protection of personal information more effective
A: Strategies for enhancing the confidentiality of information? Methods for enhancing the…
Q: The following is a list of the several ways files may be accessed. I am curious about the positives…
A: The following list outlines the benefits that come with viewing specified files both as a visitor…
Q: Write a program that prompts the user to enter their gross salary and then a percentage for their…
A: The user will first be asked to input their gross wage, after which they will be required to provide…
Q: What is the significance of software development? Would it be advantageous, in your opinion, if the…
A: Introduction: In this section, we must explain why software development is vital, as well as if the…
Q: rams might be conceptual or actual. What's the difference?
A: Data Flow diagram: A data flow diagram is a visual representation of data flowing in a system or…
Q: There are many different ways in which a Data Definition Language might be applied. Can you think of…
A: Answer to the given question: Data definition language might seem as though it's another programming…
Q: ng a binary search tree structure rather than an ordered linked list or a sorted array would be…
A: Introduction: Below the describe using a binary search tree structure rather than an ordered linked…
Q: We are not qualified to comment on how operating systems independently execute processes.
A: Introduction: An operating system (OS) is software that connects a computer's hardware to the user.
Q: Consider the following segment table (all expressed and addressed in bytes) Segment Base Length 0…
A: Find the required answer given as below :
Q: 1. Write the output of these code block without running
A: Q: Output of given code
Q: How can the 'Event Table' be evaluated to confirm that the design is accurate?
A: Encryption: There are two distinct approaches that are used to evaluate the event table in order to…
Q: With respect to the following nested loops, what is missing or wrong? int loopCount; while…
A: The loops are a programming construct that are utilized to run a bunch of code a number of times…
Q: Provide adequate data to support your claim that ASAN can find the problem in a sophisticated design…
A: Given: Solution below. In a world of ever-more-complex software, software bug failures have never…
Q: Identify four use cases that has Commissioner as an Actor and use your own words to construct a…
A: Use case A use case is a written description of how users will perform tasks on website. It…
Q: * * How many subnets are created by the ?address 192.168.1.0255.255.255.248 16 O .8 • 32 .4 If all…
A: Please refer below for your reference: Number of subnets created is given by: Ip address :…
Q: Would it be possible for you to supply me with a more in-depth look at the metrics that were used…
A: Given: A percentage of measurable or countable programming qualities is referred to as a software…
Q: can you help me to describe the rhetoric of the mathematical language
A: Rhetoric is the manner by which you convey in regular day-to-day existence. These correspondences…
Q: Enumerate the terms used in data design and explain how they are utilised in the context of data.
A: All are relational databases: Relational databases store data as table tuples and their…
Q: Analyze and contrast the various groups and responsibilities involved in the administration of…
A: Answer: Groups and responsibilities involved in the administration of computer security access:…
Q: What are the benefits and drawbacks of storing data on the cloud? A list of organizations who offer…
A: benefits and drawbacks of storing data on the cloud and A list of organizations who offer…
Q: What exactly are Sequential Access Files, and how can I put them to good use?
A: Access in a certain order: The data or information in a sequential file is organized in…
Q: What are the primary drawbacks associated with files that have been fragmented
A: Fragmentation is caused when data is erased from a hard drive and little holes are abandoned to be…
Q: Software development makes use of a variety of models, each with varying degrees of relevance based…
A: When deciding on software development models, the processes and methods utilized to produce the…
Q: How does utilizing a pre-built package model differ from starting a data modeling project from…
A: Data Model: The metаdаtа of a consistent, industry-vetted dаtа mоdel is typically made аvаilаblе via…
Q: Manuals for users, online help, and tutorials may each be organized into one of these three…
A: Manuals: This manual describes the system's operations and capabilities, as well as contingency…
Q: Question 8 Which if the following properties does the {(x,y) 1 x % y = 0} for x, y in 1, 2, 3, 4…
A: Answer to the given question: The given relation is reflexive as x%x =0 and antisymmetric because…
Q: acy? Describe in detail five different ways you may k
A: Introduction: Below the describe detail five different ways you may keep your personal information…
Q: Direct memory access functions
A: Direct memory access : In Direct Memory access CPU is idle and peripheral devices manages the…
Q: The following is a Huffman tree. Each node has a letter and a frequency, such as (T:2), which…
A: We need to decode 1111011110011101110101001010 as per the given Huffman tree.
Q: There are many different ways in which a Data Definition Language might be applied. Can you think of…
A: Data definition language (DDL) is the programming language used to design and modify database object…
Q: Let G be a directed weighted graph with n vertices and m edges such that the edges in G have…
A: So, the Dijkstra Algorithm may be used to do this. The vertex name, I presume, may be changed to…
Q: A spanning tree and an MST are two distinct types of trees, but what is the difference between the…
A: Start: A data structure is a method of organizing data in a computer so that it may be successfully…
Q: What are the drawbacks of email companies monitoring the emails of their customers?
A: Answer:
Q: The following is a list of the several entry points available for files. I am interested in learning…
A: Given: To access an employee's data, file organisation simply means putting them in alphabetical…
Q: Draw the tree corresponding to the following Prüfer codes (2,7,6,2,2) (3,1,2,3,3)
A: As per the question statement, It is asked to only to draw the tree for the given Priifer codes.
Q: Conduct a research on the CLASS in Java utilize the CLASS syntax. CLASS sample code in java,…
A: The program is written in Java, Check the program screenshot for the correct indentation. Please…
Q: A binary search tree has benefits over other data structures, such as a linked list or an array, and…
A: Given: Consider the following operations: You can get to any element. Assume that the linked list…
Q: a. If the stack input stream is A B C D E F what is the sequence of operations to get the output…
A: Please refer to the following step for the complete solution of the problem above.
Q: that supports 16 hosts. What subnet mask ?should you use 255.255.255.252 O . 255.255.255.224 O…
A: The answer of this question is as follows
Q: what is maximum number of IP address that can be assigned to host on a local subnet that can be use…
A: 1st ANSWER: A (30) Explanation: A /27 (255.255.255.224) is 3 bits on and 5 bits off. This provides…
Q: Given the list below, how many iterations will it take the following values using linear search,…
A: “Since you have posted a question with multiple sub-parts, we will solve first three subparts for…
Q: What are the primary drawbacks associated with files that have been fragmented?
A: Given: A group of files fragmented throughout a hard drive platter rather than being in one…
Q: How do consumers handle computer and mobile app problems? Examine techniques to reduce user…
A: The following are examples of how people respond to software problems: When software isn't updated,…
Q: Where do the benefits lie, and where do the drawbacks lie, when it comes to storing data on the…
A: Given: According to the question, cloud storage is always used to keep data for the future scope if…
Q: Please help and thank you in advance. The language is Java. I have to write a program that takes…
A: The correct code is given below in the next step with code and output screenshots Now the full date…
Convert the following E-R diagram into a relational schema.
Step by step
Solved in 2 steps

- a)Createa flow chartdiagram tomodel the online course registration described inthe case study belowCASE STUDYONLINE COURSE REGISTRATION SYSTEMThe User enters the surname and password and chooses if the user is a student or administrator. If entered details are valid, the user accounts become avaiable. f it is invaid an appropriate message is displayed to him/her. A student can search al the courses available to him and he chooses the best course he wants. The student can view course duration, facuty and department the course he may choose. When a student has successfully chosen a course, he can register to that course. Upon registration student details are stored in database.After registration to any course, the student may see the details of current course. He may wish to know details about fees and other information. The administrator also has the privilege to display details of the students and the corresponding course for which they have registered. The administrator has to perform…BASIC JQUERY .... https://www.w3schools.com/jquery/jquery_examples.asp?fbclid=IwAR0WWFC39ucCIUMykf0-bRja1lMcI0vBQoGdy6V_NuWH-1cZMTMf2l6TndwBelow is parts from a cloudformation template. What you need to do is look at the #TODO parts and what what is says to do. you could do ctr f so u can find the #TODO faster! Thank you Resources: VPC: Type: 'AWS::EC2::VPC' Properties: CidrBlock: 10.0.0.0/16 Tags: - Key: Application Value: !Ref 'AWS::StackId' - Key: Name Value: P4-VPC PublicSubnet: Type: 'AWS::EC2::Subnet' Properties: VpcId: !Ref VPC CidrBlock: 10.0.0.0/24 # TODO: take note of the subnet range Tags: - Key: Application Value: !Ref 'AWS::StackId' - Key: Name Value: P4-public-subnet PrivateSubnet: Type: 'AWS::EC2::Subnet' Properties: VpcId: !Ref VPC CidrBlock: 10.0.1.0/24 # TODO: take note of the subnet range Tags: - Key: Application Value: !Ref 'AWS::StackId' - Key: Name Value: P4-private-subnet WebServ1Instance: Type:…
- No plagarism please. Upvote guarenteedAssignment 2 - Remember meAs you learned in the topic of Session and Cookies.Create a simple web application with 3 pages:1- login2- logout3- contentWe the user login, the app redirect the user to "content" page, andsave the login status or information in the cookies.If the user close the app, and open it; the app not open the login; Itconvert the user directly to "content" page, because the login status orinformation saved in the cookies.If the user logout, he cannot open "content" page directly.Important Note: use session for login, and cookies for remember thelogin.Any two copies are gotten Big ZeroUpload your assignment as compressed file whose name formatted asstudentID_sectionNo.rarYou will use a word document for the following list .In Real time chat web Application we have a feature called Create/Delete and Join/Leave groups .with this following Information we need Requirement Table and User story
- Create a session variable called SProot and assign the generated positive root value to it in Oroots.php. Display this session variable in PosRoot,php page.Medical Unlimited Medical Unlimited (the brainchild of a group of young philanthropic medical professionals) is interested in setting up a mobile medical unit that provides free medical services for students. The mobile medical unit will require a patient record and scheduling application that will be used by the medical staff (doctors/nurses) and receptionists working there. The receptionists will use the system to capture new patient information when firsttime patients visit the doctor. Receptionists will also be responsible for scheduling all appointments. Nurses on the other hand will use the s ystem to keep track of the results of each visit including diagnosis, medications, prescription and treatment. Multiple medications may be prescribed during each visit. The nurses can also access the information to print out a history of patient visits. Th e doctors will primarily use the system to view patient history. The doctors may enter some patient treatment information and…Medical Unlimited Medical Unlimited (the brainchild of a group of young philanthropic medical professionals) is interested in setting up a mobile medical unit that provides free medical services for students. The mobile medical unit will require a patient record and scheduling application that will be used by the medical staff (doctors/nurses) and receptionists working there. The receptionists will use the system to capture new patient information when firsttime patients visit the doctor. Receptionists will also be responsible for scheduling all appointments. Nurses on the other hand will use the s ystem to keep track of the results of each visit including diagnosis, medications, prescription and treatment. Multiple medications may be prescribed during each visit. The nurses can also access the information to print out a history of patient visits. Th e doctors will primarily use the system to view patient history. The doctors may enter some patient treatment information and…
- omplete this javascript file according to the individual instructionsgiven in the comments. *** DO NOT CHANGE any of the code that you are not instructed to. */ ////////////////////////// NOTE: Use the API endpoints available at// https://jsonplaceholder.typicode.com/// to get the data required in these exercises.// HINT: Read the documented Resources and Routes.// Also the guide:// https://jsonplaceholder.typicode.com/guide//////////////////////// Create a function named "getUser".// This function needs to accept a "userID"// parameter.// Use Fetch with Async/Await to request// the data for the requested user.// The function should return JSON data.Please help me create a web application and show examples of images and links. app.js var express = require('express'); var path = require('path'); var indexRouter = require('./routes/index'); var app = express(); app.use('/', indexRouter); const PORT = process.env.PORT || 3050 app.listen(PORT,()=> console.info(`Server has started on ${PORT}`)) module.exports = app; index.js var express = require('express'); var router = express.Router(); const path = require("path"); router.get('/', function(req, res, next) { res.sendFile(path.resolve('public/index.html') ); }); router.get('/*', function(req, res, next) { res.sendFile(path.resolve('public/' + req.url) ); }); you will create four static web pages. The main page (index.html) will contain three links to open the three pages defined below.The three content pages will contain a name, a description and a picture of a character of your choosing The main page The main page must contain three links, one to each of the content…Can you help me I want to display and search at the table in the same time and fetch those results and show the table but it does not work. I provided my code below to ask if you can help me <?phpsession_start();if (!isset($_SESSION['username'])) header("location: login.php");{ //Authentication and Authorization logic here }?> <!DOCTYPE html><html><head> <link rel="shortcut icon" href="file/images/favicon.ico" /> <title>View All Records</title> <link rel="stylesheet" href="/write_font_awesome_url"/> <link rel="stylesheet" href="file/css/records_style.css"></head> <a href="home1.php"><img class="backarrow"src="file/images/backarrow.png" width="30" height="30"></a></br> <style>/*write your css code here*/</style> <body><?php include 'search.php'; ?><a href= "add_record.php"><button class="btn"><br>Add New…

