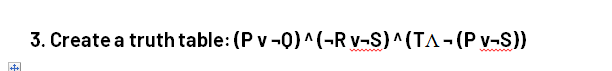
Create a truth table: (P v ¬Q) ^ (¬R v¬S) ^ (TɅ ¬ (P v¬S))
Q: What does "interrupt" mean? Can an enumeration of the numerous varieties of hardware disruption…
A: An "interrupt" in processor regulation refers to a suggestion sent by hardware or software to the…
Q: Phishing emails may attempt to convince you that your personal or financial data has been…
A: Phishing emails may attempt to convince you that your personal or financial data has been…
Q: Why does computer science appeal to individuals of various ages and backgrounds?
A: Computer science is the study of computers and computational systems which includes their design,…
Q: How do we envision AI aiding us? Please expand on each main point and provide at least two examples…
A: Artificial Intelligence (AI) has the potential to aid us in numerous ways, revolutionizing various…
Q: All types of virtualization are discussed, including language, operating system, and hardware.
A: Virtualization be a technique with the intention of enables the reproduction of a Physical object in…
Q: How significant are the various specifications of a portable computer?
A: The performance and capabilities of a portable computer, such a laptop or tablet, are significantly…
Q: What three alternatives are available for restoring a database? In a summary, what is the purpose of…
A: 1. Complete Backup Restoration: This is the most straightforward method to restore the entire…
Q: Outline the primary distinctions between traditional forms of intellectual property larceny and…
A: Intellectual Acreage larceny, often identified as IP theft, relates to the illegal use of another's…
Q: Multitasking enables application switching. Is it possible to transfer operating systems on a…
A: Yes, it is possible to transfer operating systems to a computer. The process of transferring an…
Q: Multitasking enables application switching. Is it possible to transfer operating systems on a
A: Answer is explained below in detail
Q: Explain the necessity of regular wireless audits and how to conduct one.
A: Regular wireless audits are crucial for maintaining the security and integrity of wireless networks.…
Q: The communication system in your college is using a phase modulation of 8 PSK having symbol rate of…
A: In the field of telecommunications and networking, the bit rate refers to the rate at which bits are…
Q: 1. Display the entire dataset. 2. Display all countries from Asia. 3. What is the population of…
A: 1. To display the entire dataset in SAS, you can use the PROC PRINT procedure. Assuming your dataset…
Q: Because the CIA's "holy trinity" of secrecy, trust, and vigilance does not appear to be operational…
A: CIA's "holy trinity" of secrecy:The Central Intelligence Agency (CIA), which gathers, analyzes, and…
Q: What are the greatest alternatives for constructing on existing infrastructure? When would it be…
A: The answer for above question is in next step.
Q: In addition to Cisco, Oracle, and Microsoft's websites, examine two others of your choosing (see…
A: Before delving into where one can obtain the required information, it's crucial to consider the…
Q: 1. The number of iterations for the for loop below is: for a in b c d e; do echo $a; done; (a) 1…
A: The correct answer is (d) 4. The for loop iterates over the elements "b", "c", "d", and "e".NOT…
Q: How do various network topologies, including LANs and WANs, influence the design of a distributed…
A: Network topologies define how PCs, printers, and other symbols are tied within a network. These…
Q: What types of modifications can be made to the networks connecting the computers to prevent viruses…
A: There are several sorts of adjustments that may be put into place to stop viruses from infecting…
Q: Suppose that value of x in a byte register is 0x87. Fill in the following blanks indicating the byte…
A: In computer programming and computer architecture, shifting refers to the operation of moving the…
Q: What are the top four advantages of continuous event simulation?
A: Continuous event simulation is a powerful technique used in various fields to model and analyze…
Q: The rate at which data is transferred over an Ethernet Connection.
A: Ethernet is a ever-present networking typical that may be used for numerous poles apart things and…
Q: How does CPU Scheduling enhance operating system performance?
A: CPU scheduling is a crucial component of an operating system that determines how tasks or processes…
Q: Defragmenting hard drives: a system speed booster? Why? Yes, why not?
A: Defragmenting hard drives used to be a common practice to improve system speed and performance in…
Q: Why are operating systems significant? One paragraph is dedicated to describing the batch operating…
A: Operating systems are a crucial component of modern computing, providing a vital layer of software…
Q: Discuss the advantages and disadvantages of cloud storage versus client software for data storage.
A: In the evolving technical landscape, organization grapple with decision on where to store their…
Q: A router has the following four active flows, and each flow has packets to transmit. Given FQ is…
A: Given, A router has the following four active flows, and each flow has packets to transmit. Given FQ…
Q: The issue for IT professionals: Is email encryption moral?
A: Email encryption is a practice that involves securing the content of emails through the use of…
Q: What does the term "optimising compiler" imply, and how does one function? In terms of programming,…
A: An optimizing compiler refers to a compiler that attempts to minimize or maximize some estates of an…
Q: It is prudent to utilise asymmetric encryption techniques, such as those found in public-key…
A: It is prudent to utilise asymmetric encryption techniques, such as those found in public-key…
Q: Is there any advantage to making a phone call as opposed to submitting an email?
A: There are several compensation to creation a phone call instead of submit an email, Depending on the…
Q: For connecting and chaining FIQ interrupt procedures, an Interrupt Vector Table (IVT) offset is…
A: For connecting and chaining Fast Interrupt Request (FIQ) interrupt procedures, an Interrupt Vector…
Q: There are two ways in which the expanding trend of resource virtualization could affect operating…
A: Resource virtualization refers to the process of abstracting and pooling physical resources, such as…
Q: What is the single most essential consideration when administering complex real-time systems,
A: The single most essential consideration when administering complex real-time systems is ensuring…
Q: Why is the transmission of data over fibre optic cables more efficient than over copper connections?
A: Copper cable, also known as twisted-pair cable, is a type of cable made up of pairs of copper wires…
Q: Given the following attached main function: Write the following functions based on the criteria…
A: The provided code is a C++ program that performs calculations related to an employee's pay. It…
Q: Who are the compiler's closest relatives? Could you provide a summary of each?
A: Compilers are computer programs that are used to convert Programming language Translated from a…
Q: How conventional or iterative is the cascade structure of your project? How might this be resolved?
A: Cascade structure refers to a design or implementation approach where changes or actions propagate…
Q: What is the utmost velocity of data transmission within an Ethernet LAN
A: The utmost velocity of data transmission within an Ethernet LAN (Local Area Network) is determined…
Q: Describe in detail the Domain Name System (DNS), including iterated and non-iterated queries,…
A: The Domain Name System (DNS) is a fundamental protocol of the internet that translates…
Q: Write a java code for finding the probability of doing anything from the user entered probability of…
A: Step-1: StartStep-2: Declre variable probabilityNotDoingAnything and take input from user between 0…
Q: In what ways do particular specifications for a portable computer matter?
A: Each specification of a portable computer directly impacts its performance and usability. The…
Q: The cloud computing resources that are available should be enumerated. What are some examples of…
A: Cloud computing has revolutionized the way businesses operate by providing on-demand access to a…
Q: Which network architecture would you employ if your company had to connect forty internal PCs to the…
A: Some things to consider before setting a network architecture in office like expense , support and…
Q: How can one maintain their privacy when using shared printers and computers?
A: In today's digital age, privacy has become a significant concern, especially when using shared…
Q: What sort of Internet connection is preferred to provide guaranteed uptime to customers? Full…
A: To provide guaranteed uptime to customers, a reliable and stable internet connection is crucial. The…
Q: Why not experiment with user and kernel threading on Sun Solaris? Solaris' approach to threading:…
A: User-level threads are managed without kernel intervention. This means they are more efficient than…
Q: What are your thoughts on email? How is information transmitted from one location to another? Record…
A: Email, abbreviation "automated mail," is a system for catching, throwing, and storing mail online.…
Q: The concentration of a database programmer on information distinguishes them from other programmers.…
A: Non like other kinds of computer programmer, database computer programmer focus on planning,…
Q: Calls are made and taken using mobile modems. Who ensures that the modem is adequately equipped? Is…
A: Using communication methods to set up and keep links with other devices, smart modems are used to…
Create a truth table: (P v ¬Q) ^ (¬R v¬S) ^ (TɅ ¬ (P v¬S))
Step by step
Solved in 3 steps

- (C Language) The Fibonacci sequence begins with 0 and then 1 follows. All subsequent values are the sum of the previous two, for example: 0, 1, 1, 2, 3, 5, 8, 13. Complete the Fibonacci() function, which takes in an index, n, and returns the nth value in the sequence. Any negative index values should return -1.Describe each of the following sets by listing its elements:a. {x | x ∈ N and x2 − 5x + 6 = 0}b. {x | x ∈ R and x2 = 19}c. {x | x ∈ N and x2 − 2x − 8 = 0}}d. {x | x ∈ Z and x ∗ x = 4}6.Code for an array of meeting time intervals consisting ofstart and end times [[s1,e1],[s2,e2],...] (si < ei),determine if a person could attend all meetings. For example,Given [[0, 30],[5, 10],[15, 20]],return false.""".
- Transcribed Image Text DNA is sequence of bases A, G, T, C. Let DNA [ab] be the subsequence of DNA starting from index a finishing in b inclusive, and DNA[a.] be the subsequence of DNA starting from index a to the end. We could perform the following ops on DNAS: cross operation - they take DNA1 and DNA2 and numbers kl and k2. Then two new DNAS are created: DNA3 = DNA1[1,,k1]+DNA2[k2+1.] and DNA4 = DNA2[1.k2]+DNA1[k1+1.].mutate operation - they take a DNA, number k and one of the bases. Then they replace the base in position k in DNA with that base. also, they need to know certain characteristics of those DNAS. So, they can perform count operation - they take DNA and numbers k1 and k2 (k1 <= k2). This operation should return the number of A, G, T, C bases in DNA[k1,,k2].The initial DNAS are numbered from 1 to n, where n is the amount of those DNAS. The new DNAS the first line of input file contains number n - the number of initial DNAS. Each of the following n lines containsextern "C" int f(int *,int,int); int a[2][2] = {{11,12},{21,22}}; void setup(){ Serial.begin(115200); while(!Serial); delay(500); int *arr = (int*)a; Serial.println(f(arr,2,2)); } void loop(){ } .global f f: ldr r3,[r0] // get first element mov r2,#0add r2,r3 mov r1, #3 lp: add r0,#4 // add next elementldr r3,[r0]add r2,r3sub r1,#1 bgt lp mov r0,r2 bx lr Describe what operation is being performed in this codeQuestion 15 ka R Programming - 1) Without using the dplyr package explain the various ways of subsetting rows and columns in a data frame in base R. 2) Write a for loop with: - if else conditions in it. - assign function - which makes use of empty vector or empty lists Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
- 8.26 LAB: Word frequencies (dictionaries) Implement the build_dictionary() function to build a word frequency dictionary from a list of words. Ex: If the words list is: ["hey", "hi", "Mark", "hi", "mark"] the dictionary returned from calling build_dictionary(words) is: {'hey': 1, 'hi': 2, 'Mark': 1, 'mark': 1} Ex: If the words list is: ["zyBooks", "now", "zyBooks", "later", "zyBooks", "forever"] the dictionary returned from calling build_dictionary(words) is: {'zyBooks': 3, 'now': 1, 'later': 1, 'forever': 1} The main code builds the word list from an input string, calls build_dictionary() to build the dictionary, and displays the dictionary sorted by key value. Ex: If the input is: hey hi Mark hi mark the output is: Mark: 1 hey: 1 hi: 2 mark: 1 Use Python, please.def find_root4(x, epsilon): ''' IN PYTHON Assume: x, epsilon are floating point numbers and epsilon > 0 Use bisection search to find the following root of x such that If x >=0, return y such that x - epsilon <= y ** 2 <= x + epsilon Else, return y such that x - epsilon <= y ** 7 <= x + epsilon Note: You must use bisection search to implement the function. ''' pass9. Write function getMoveRow to do the following a. Return type integer b. Parameter list i. 1-d character array (i.e. move), size 3 c. Convert the row portion of the player’s move to the associated integer index for the board array d. Example: i. move = ‘b2’ ii. 2 is the row iii. 2 is index 1 in the board array e. Return the row array index that corresponds to the player’s move f. Return a -1 if the row is not valid (i.e. INVALID) 10. Write function getMoveCol to do the following a. Return type integer b. Parameter list i. 1-d character array (i.e. move), size 3 c. Convert the column portion of the player’s move to the associated integer index for the board array d. Example: i. move = ‘b2’ ii. b is the column iii. b is index 1 in the board array e. Return the column array index that corresponds to the player’s move f. Return a -1 if the column is not valid (i.e. INVALID) I am getting an error when entering the code at the very end. please fix it. This is the code in C int…
- 4. b. If A is an array of integers with width = 4; Please translate withthree-address statement, the following expression: x = a[i] + 2;5(b) Give the two arrays that will be merged by the final step of mergesort on [8, 2, 1, 4, 5, 3, 7, 9].int a[10] = {0,1,2,3,4,5,6,7,8,9};int *m = &a[0];int *p = &a[5];int *q = &a[1]; p = (int) m + (int) p - (int) q; what is the value of of *p

