C Language) The Fibonacci sequence begins with 0 and then 1 follows. All subsequent values are the sum of the previous two, for example: 0, 1, 1, 2, 3, 5, 8, 13. Complete the Fibonacci() function, which takes in an index, n, and returns the nth value in the sequence. Any negative index values should return -1.
C Language) The Fibonacci sequence begins with 0 and then 1 follows. All subsequent values are the sum of the previous two, for example: 0, 1, 1, 2, 3, 5, 8, 13. Complete the Fibonacci() function, which takes in an index, n, and returns the nth value in the sequence. Any negative index values should return -1.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter5: Repetition Statements
Section5.5: A Closer Look: Loop Programming Techniques
Problem 12E: (Program) Write a program that tests the effectiveness of the rand() library function. Start by...
Related questions
Question
(C Language) The Fibonacci sequence begins with 0 and then 1 follows. All subsequent values are the sum of the previous two, for example: 0, 1, 1, 2, 3, 5, 8, 13. Complete the Fibonacci() function, which takes in an index, n, and returns the nth value in the sequence. Any negative index values should return -1.
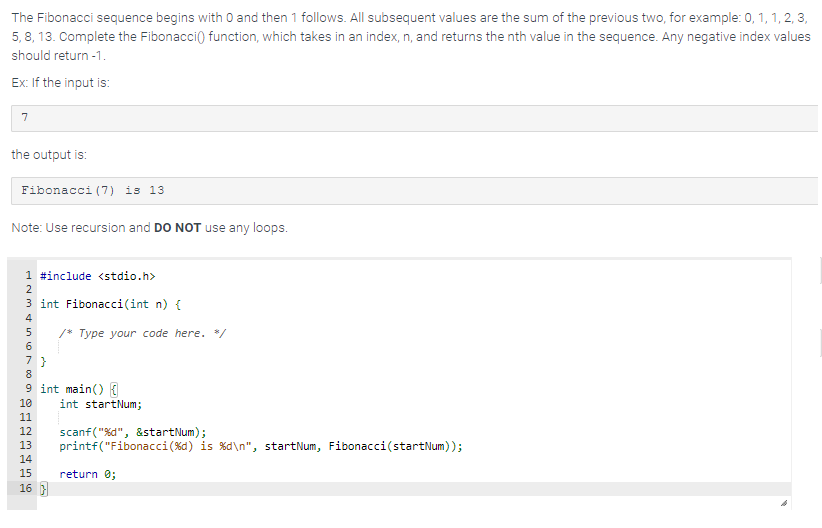
Transcribed Image Text:The Fibonacci sequence begins with 0 and then 1 follows. All subsequent values are the sum of the previous two, for example: 0, 1, 1, 2, 3,
5,8, 13. Complete the Fibonacci() function, which takes in an index, n, and returns the nth value in the sequence. Any negative index values
should return -1.
Ex: If the input is:
7
the output is:
Fibonacci (7) is 13.
Note: Use recursion and DO NOT use any loops.
1 #include <stdio.h>
2
3 int Fibonacci(int n) {
4
56789BEG
7}
9 int main() {
10
11
12
13
14
15
/* Type your code here. */
16}
int startNum;
scanf("%d", &startNum);
printf("Fibonacci ( %d) is %d\n", startNum, Fibonacci(startNum));
return 0;
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr