Create a Use Case Diagram of Bank Management Sytem, using this scenario (see attached photo) Do not take a shortcut on use cases, you must understand the flow of the scenario
Create a Use Case Diagram of Bank Management Sytem, using this scenario (see attached photo) Do not take a shortcut on use cases, you must understand the flow of the scenario
Database System Concepts
7th Edition
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Chapter1: Introduction
Section: Chapter Questions
Problem 1PE
Related questions
Question
Create a Use Case Diagram of Bank Management Sytem, using this scenario (see attached photo)
Do not take a shortcut on use cases, you must understand the flow of the scenario
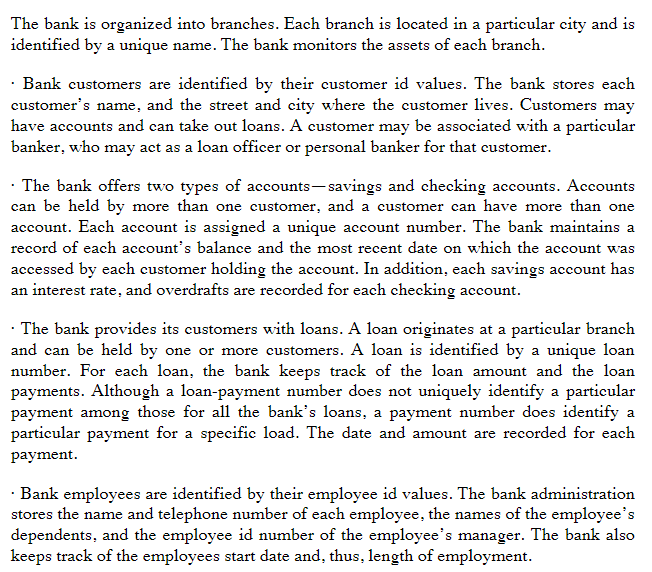
Transcribed Image Text:The bank is organized into branches. Each branch is located in a particular city and is
identified by a unique name. The bank monitors the assets of each branch.
Bank customers are identified by their customer id values. The bank stores each
customer's name, and the street and city where the customer lives. Customers may
have accounts and can take out loans. A customer may be associated with a particular
banker, who may act as a loan officer or personal banker for that customer.
The bank offers two types of accounts-savings and checking accounts. Accounts
can be held by more than one customer, and a customer can have more than one
account. Each account is assigned a unique account number. The bank maintains a
record of each account's balance and the most recent date on which the account was
accessed by each customer holding the account. In addition, each savings account has
an interest rate, and overdrafts are recorded for each checking account.
. The bank provides its customers with loans. A loan originates at a particular branch
and can be held by one or more customers. A loan is identified by a unique loan
number. For each loan, the bank keeps track of the loan amount and the loan
payments. Although a loan-payment number does not uniquely identify a particular
payment among those for all the bank's loans, a payment number does identify a
particular payment for a specific load. The date and amount are recorded for each
payment.
Bank employees are identified by their employee id values. The bank administration
stores the name and telephone number of each employee, the names of the employee's
dependents, and the employee id number of the employee's manager. The bank also
keeps track of the employees start date and, thus, length of employment.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:
9780133976892
Author:
Paul J. Deitel, Harvey Deitel
Publisher:
PEARSON

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781337627900
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:
9780073373843
Author:
Frank D. Petruzella
Publisher:
McGraw-Hill Education