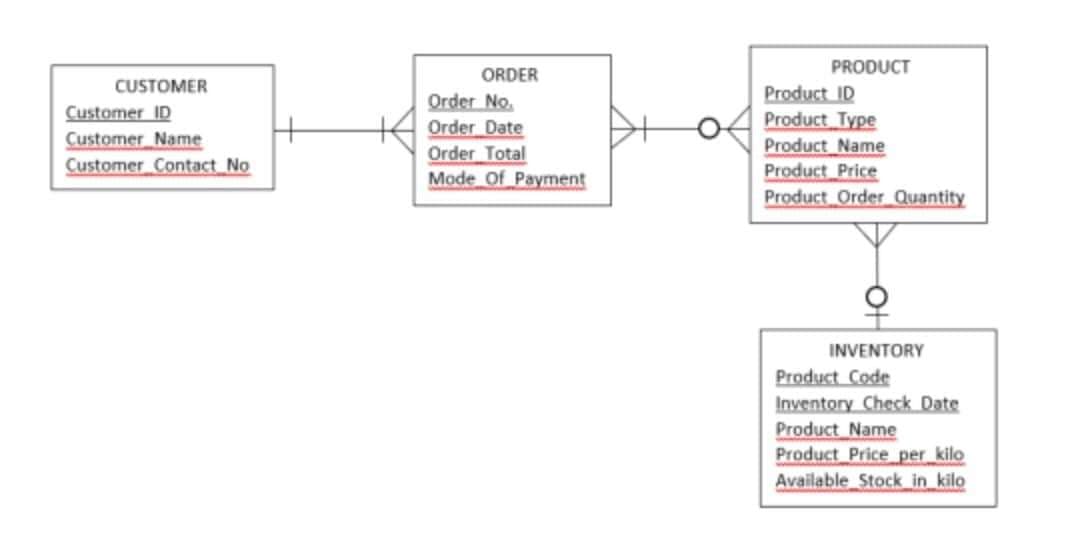
CUSTOMER Customer ID Customer Name Customer Contact No ORDER Order No Order Date Order Total Mode Of Payment PRODUCT Product ID Product Type Product Name Product Price Product Order Quantity INVENTORY Product Code Inventory Check Date Product Name Product Price per kilo Available Stock in kilo
Q: Why did you choose Microsoft Excel above the other options available to you?
A: Microsoft Excel: Excel formats, organises, and calculates spreadsheet data. Data analysts and other…
Q: Write a C program to count the number of occurrences of any two vowels in succession in a line of…
A: The five letters A , E , I , O and U are called vowels. All other alphabets except these 5 vowels…
Q: Create a simple payroll program that applies object-oriented concepts. For PC users, create a…
A: The solution to the given question is: STUDENT RECORD WINDOWS FORM APPLICATION using System;…
Q: Please give an overview of the technologies that are being used more and more with nonvolatile…
A: Given: Memory that is not volatile and is composed of solid-state components. Memory that is…
Q: What differentiates today's mobile devices from and from desktop computers?
A: Introduction: The tasks that are typically completed on a personal computer can also be carried out…
Q: describe at least two operating systems, which provide command line interface, for working on…
A: Command-line interfaces are also called…
Q: Why did you choose Microsoft Excel above the other options available to you?
A: Programming accounting pages in Microsoft Excel has become a standard component of the majority of…
Q: A symmetric block cipher's hardware components may be summarised as follows: Explain each of the two…
A: Utilizing a single key, symmetric encryption scrambles (encodes) and unscrambles (interprets)…
Q: In 2022 country A will have a population of 25 million inhabitants and country B of 18.9 millions.…
A: Find the required code with answer and output given as below :
Q: In other words, what does the phrase "Internet 2" really imply and how does it operate exactly?
A: Worldwide correspondence is simple presently on account of a complicatedly connected overall PC…
Q: What's the distinction between data and information?
A: Introduction: On a day-to-day basis, an individual thinks of data and information as being the same…
Q: Explain the difference between the following with simple example 1. plot and plot3. 2. H1 line and…
A: 1) plot :- Creates a 2-D line plot of the data in Y versus the corresponding values in X. plot3…
Q: Are there any steps you can take to guarantee that the source-control system is properly entered…
A: Source control system: A vital system, known as a source control system, makes it feasible for…
Q: Explain briefly how the weighted approach may be used to convert decimal to ternary in a ternary…
A: Intro To the above-mentioned query. Please find the answer below. I'm writing the answer to this…
Q: Examples of two-tier and three-tier application architectures should be provided to demonstrate…
A: explains the differences between a two-tier and three-tier application architecture Database…
Q: Assume there is only one seat available in a class for which two students are registering. What…
A: Database system: Database systems, usually referred to as DBMS, are pieces of software that gather…
Q: What is a firewall's primary function? What distinguishes it from the rest? What is the purpose of a…
A: Firewall's primary function: A firewall, at its most basic, is a barrier that lies between a private…
Q: Write a java program that will compare the contains of 2 files and count the total number of common…
A: The JAVA code is given below with code and output screenshots 2 sample files are taken: File1.txt…
Q: Q1/Write a function that calculates the mean of the input vector?
A: I have solved using matlab Please check the step 2 & 3 for solution
Q: 1. a) Convert the following equations into corresponding C statement: 7.7b (xy + a)/c - 0.8 +2b A =…
A: The C statement to calculate A is as follows: A = (((7.7 * b) * ( x * y + a )) / c - 0.8 + 2*b )/((…
Q: Given the variable: double num=35.4689; Write a printf statement that will print the variable num in…
A: Answer:
Q: which of the following can be determined from Turnitin's Index? a) How much plagiarism was committed…
A: Turnitin is an authentic testing and anti-cheating service that checks your writing for quote errors…
Q: To what extent do logical and linear address relate to one another?
A: Introduction What exactly are logical address and linear address, and how are the two related to one…
Q: The educational technology consists of three sections that work in harmony with one another. They…
A: Three main parts. Education technology comprises three parts: Educational system administration…
Q: Can you write it more in a proof format, thank you.
A: Suppose there are 'k' number of persons in the celebration. Each person handshake with some number…
Q: Is it more harder to design Graphical User Interfaces (GUI) with pixel coordinates?
A: Intro Graphical User Interfaces (GUI) A graphical user interface (GUI) is a user interface that…
Q: Does the latest security breach involving access control and authentication that made news seem to…
A: A data/security breach happens when private or protected information is exposed. A data breach might…
Q: use java to ; a. request for only name and rank to be entered into the system b. display results…
A: As per the question statement, We need to write JAVA program.
Q: Give examples to show at least two different ways to select subset of columns from a dataframe data…
A: As per the question statement, We need to provide two different ways to select subset of columns…
Q: B) Use "solve" function to solve the following equations and "double" function to put the results in…
A: As per the question statement, We need to write matlab code.
Q: Learning influences a person's physical and cultural development.
A: Answer in step 2
Q: What's the connection between the MAR and MDR? Is there a similarity in the Little Man Computer
A: Introduction There are two distinct registers linked to memory, MAR and MDR, and the reasons for…
Q: Write a PHP program which iterates the integers from 1 to 10. You will need to create and declare a…
A: Answer: Algorithm Step1: first we have initialized i with 1 and run the while loop up to 10 Stpe2:…
Q: As you go through the various Microsoft software, explain how they may be used for various purposes.
A: The question is to write various purposes of Microsoft software.
Q: What are the most up-to-date methods for securing LANs? Identify four categories and explain each…
A: Introduction: Network security measuresThese are the security controls you add to your networks…
Q: What exactly is booting?
A: Introduction: When a computer is first turned on, it goes through a predetermined sequence of tasks…
Q: If harmful software has a global influence, what variables are responsible for its creation?
A: Harmful software also known as malicious software. Any program or file that purposefully harms a…
Q: You need a way to prevent class fields from being corrupted by mistake.
A: Keeping files from being corrupt Use the same software across the board. Files may be damaged when…
Q: Write a java programs that will show the total number of Composites between 2 numbers given by the…
A: code in below
Q: wrong answer
A: Start Create a class named Ship with name and year as its attributes. Implement constructor to…
Q: Attacks on a cypher are more difficult for a short message since they are more difficult to break.
A: A cypher is a computation: For encoding and decoding information in cryptology. Symmetric key…
Q: You talk about the aims of the authentication process, but when you talk about the end result, what…
A: Authentication is the procedure that servers employ when they need to know who is accessing their…
Q: Write a pseudo-code on how to import global COVID cases data. Assume you have a CSV file containing…
A: code: # import require libraries import pandas as pd import numpy as np import matplotlib.pyplot…
Q: What exactly do you mean by "network security"? It's important to explain how the industry-standard…
A: Network Protection: A security hazard is any unfortunate occurrence that might result in undesirable…
Q: Windows Defender and another free anti-malware application are compared to demonstrate differences.
A: Taking into consideration the inquiry: The following are the primary distinctions between the two…
Q: . If a five-digit number is input through the keyboard, write a progra ew number by adding one to…
A: solution in below step
Q: An example of a real-world SQL database, as well as an explanation of the database, should be…
A: The question is to give an example of a real-world SQL database, as well as an explanation of the…
Q: Why is primary and cache memory divided into blocks ?
A: Below is the answer to above question. I hope this will be helpful for you...
Q: Q. what are the tyoes of code cloning in software cloning?
A: Code cloning:- Code cloning in software cloning is making use of pre- written code. Code cloning is…
Q: Evaluate the following action taken by the team during the validation. For each scenario, identify…
A:
Step by step
Solved in 2 steps with 1 images

- Write a SQL statement that will add the below row to the Task table.TaskID Description Duration StartDate TeamMemberID4 Implementemailnotifications2{ String str = tf5.getInt("ID"); Class.forName("com.microsoft.sqlserver.jdbc.SQLServerDriver"); Connection con = DriverManager.getConnection("jdbc:sqlserver://NOMBUSO1806:1433;databaseName= Employee ATM", "NOMBUSO1806", "mysql1234"); // write your database username and password PreparedStatement st = con.prepareStatement("select * from Employees where ID=?"); // Search with ATM ID st.setString(1, str); ResultSet rs = st.executeQuery(); // Excuting Query if (rs.next()) { String s = rs.getString(1); String s1 = rs.getString(2); String s2 = rs.getString(3); // Sets Records in TextFields. tf1.setText(s); tf2.setText(s1); tf3.setText(s2); my getInt() is throwing an error that the method is not found. what should i do?Create the search/select(Add to shopping cart)/check out (purchase) abstract use cases for customer and use them to create corresponding business use cases.
- The screen shown is used to enter the sales of the products into the sales and salesdetails tables. It utilizes the four depicted files ProductDAO.java, Product.java, PosDAO.java and Pos.java. The schema for the database is also depicted. The java code utilizes a jconnector to retrieve data from the database. When a product code is entered and then a quantity is entered, on the enter key pressed, the product code is sent to the getProduct(String ID) of a ProductDAO object and that function connects to the database and retrieves the data, placing it into a Product object and return this as Product object so that it can be placed into the Jtable of the PosGUI screen. Write the code for the getProduct(String ID) function located in the ProductDAO file. The code is equivalent to the prodid.A __________ consist of a set of dependencies and rules.Single choice. CHOOSE OPTION: makefile Option 2 complier static libraries macrosIn Senior Project Website, the user requests the website to search for previous senior projects, the website displays the search web form, the user inputs the keywords to be used for the search process, the user submits the search criteria to the website, and the website requests a remote database to search for senior projects that fulfill the requested criteria (keywords). The remote database returns back a Boolean value (indicating if the search is successful or not) and a list of found senior projects (the list is empty if not successful), If the search is successful, the website displays the list of received senior projects, else, the website displays error dialog box indicating that no projects were found. Q2. For Senior Project Website System described above, students are required to conduct the following task: a) Design the Sequence Diagram of Senior Project Website System described above.
- You are required to write a Product Management Android application for a small business as described below. The user of the application is the Purchase Manager. The Purchase Manager requires functionality for decision support on making purchases and updating stock quantities when stocks are received. Viewing of updated stock quantities and stock prices is required. Create a TopLevel View as follows: This view is the first page of your application. It presents to the Purchase Manager two options, one for Receiving Stocks, and one for Ordering Stocks.A controller action can be used to: Question 24 options: a) Return a view b) Return a simple content c) return a 404 error code d) All the answers are correctYou are required to write a Product Management Android application for a small business as described below. The user of the application is the Purchase Manager. The Purchase Manager requires functionality for decision support on making purchases and updating stock quantities when stocks are received. Viewing of updated stock quantities and stock prices is required. Using Andriod programming Create View 1 as follows: This view is the “Receiving Stocks” view. It must show a list of Product Names, a field for entering the quantity received, and a button, “Update Stocks”. The Purchase Manager will select the relevant Product Name, enter an integer, and click on the button. The button should add the quantity entered above to the StockOnHand field for the specified Product Name, as well as, subtract the quantity entered from the StockInTransit field. The “Output View” must then be updated. See below. Create View 2 as follows: This view is the “Ordering Stocks” view. It shows a list of…

