d. What is the greatest magnitude negative number one can represent in n-bit 2's complement code?
Q: Currently working with python and I have imported an excel file into my code. I have a Header with…
A: You can use the pandas library in Python to import the excel file and count the number of rows where…
Q: What use does a Master file that mostly contains historical information serve?
A: A collection of records belonging to one of the primary issues of an information system, such as…
Q: Write a program to read a text file line by line and display each word separated by '#'
A: Since , specific programming language was not mentioned. So, I have chosen Python Programming…
Q: The stock data of your favorite publicly traded company may have irregularities; what types of…
A: The stock market prices of the various financial institutions continue to shift or alter very…
Q: Help for Everyone Place 35H in the accumulator's input, and the result will be sent to the B…
A: Writing an assembly language programme is required to transport data 35H into the accumulator, then…
Q: Do security holes exist in WPA? What should be done to fix this if it turns out to be true?
A: Yes, security holes do exist in WPA. The best way to fix this is to use WPA2, which is a newer…
Q: What characteristics set apart domain-specific software architecture?
A: Introduction Any piece of software should be compelling to find true success. It should be equipped…
Q: Are SSL and TLS the same thing, or are there distinctions between them? The two terms seem to be…
A: Introduction : A secure Sockets Layer (SSL) is a cryptographic protocol that provides communications…
Q: Assume you are working with base 26 and the available symbols for this number system are A, B, C, D,…
A: Introduction Base 10 numbers are denoted in the form of 10xn, where x is the digit, and n is the…
Q: With data visualization, data storage is one of the most important aspects of data management.…
A: Let's think about data storage and data visualisation for the distributed warehouse and business…
Q: Read six names from input and print out only the unique names.
A: The question does not specify any particular programming language for the solution. We have done the…
Q: To learn RAID 5, we must first define it. When should RAID 5 be used instead of an other data…
A: Data protection method: Data encryption is a data protection method that is used to protect data by…
Q: Why, despite its seeming lack of complexity, is a file so useful?
A: complexity:- Complexity is a measure of the amount of time, resources, and effort required to solve…
Q: The numerous methods of data concealment provide unique difficulties for law enforcement, thus it's…
A: Introduction: Data concealment is the process of obscuring or hiding data or information in order to…
Q: Do you believe that NAD therapy will be effective in preventing and treating hangovers? Explain?
A: As an non drinker, I do not have personal beliefs or opinions. However, there is currently no…
Q: What kind of inputs does the DumpMem method accept?
A: What kind of inputs does the DumpMem method accept answer in below step.
Q: To improve their business processes, a growing number of organizations are looking to big data. Can…
A: Big Data encompasses all procedures and instruments for using and managing massive data collections.…
Q: A growing number of businesses are adopting big data strategies. Explain its function and importance…
A: Big data refers to the large volume of data – both structured and unstructured – that inundates a…
Q: cprogram to o identify the corners of the polyomino and store them in an array. This array is called…
A: The corners of the polyomino must first be located and stored in an array. Below, we refer to this…
Q: How does Random Forest work? Why is it better than a single decision tree?
A: Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: The difference between a data repository and a data dictionary and what each term means.
A: Ans Compare Repository and Data Dictionary definition. A key area of the ABAP workbench is the…
Q: What can you do today to protect your MIS against the many cyber dangers that might affect it in the…
A: Malware is the most widespread security concern, so let's start there. Since the internet's…
Q: Do you really need a Master file, given how much information it stores for so long?
A: Long-term data storage refers to the practise of storing post-project information in a way that is…
Q: At what step of the process (the build or the run) would you like an error to be discovered?
A: Compile time errors: The problems identified by the compiler during compilation are known as…
Q: HELP ME SPEED I NEED FINAL ANSWER In ________, contained class exist even if main class is…
A: Here is your solution step by step -
Q: To what two factors do the inherent limitations of binary digital computers and floating-point…
A: Floating-point computation: Floating-point arithmetic is the technique of adding two scientifically…
Q: When used, how does incremental development work? Please explain.
A: Incremental Development In computer code engineering, incremental development could be a process…
Q: Regarding these three features, where does TCP vary from UDP?
A: TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are two of the most commonly…
Q: In order to fix your basic network, what network commands would you use? For a more extensive…
A: A network is defined as the connection of two or more computers to exchange information and…
Q: With data visualization, data storage is one of the most important Provide examples of how you may…
A: There are several Business Intelligence (BI) tools that can be used in a decentralized data…
Q: Assignment Write a program that displays a menu with shape options, for example: 1-) Triangle 2-)…
A: Answer: Algorithms: Step1: we have print the menu for the finding the area Step2: then we have ask…
Q: Henry is given the responsibility to install a smart indoor lighting system in his organization,…
A: A motion detector sensor detects the presence of movement in its field of view, which can be used to…
Q: python What isthe code syntax for Converting your target variable in the dataset into a binary…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: 8. Which HTML tag is used to define an internal style sheet? A) B) (C)
A: The <style> tag is used in HTML to define a section for internal CSS styles. CSS (Cascading…
Q: It's more efficient to divide large-scale computing tasks and applications into more manageable…
A: Breaking down large-scale computing tasks and applications into smaller, more manageable chunks is…
Q: Please elaborate about RAID 5's operation. Is there ever a time when RAID 5 would be preferable to…
A: RAID 5: RAID is a storage virtualization solution that combines several physical disc drive…
Q: To add NEW DATA as the first entry to a singly linked list T, create a pseudo-code process.
A: Here is your solution -
Q: What are the three distinct categories of major database events that have the potential to kick off…
A: Hey, we'll respond to the first question as there are numerous questions submitted. If you just have…
Q: But why exactly is the concept of a file so potent?
A: INTRODUCTION: Individual file organization and accessibility are becoming more crucial in data…
Q: Please written by computer source Locate the CHI Policy document set you have been given. Using a…
A: To create a PDF document, we can use a variety of tools and methods, depending on your needs. If you…
Q: The numerous methods of data concealment provide unique difficulties for law enforcement, thus it's…
A: Answer:
Q: Task 1: Implement and Test a Sorting Algorithm 1. Create a Java project and implement your own…
A: Algorithm: The code implements two algorithms: selection sort and binary search. Selection sort…
Q: The Problem: You are coding a graphics filter that process each of an image through a filter. Each…
A: Like floating point, fixed point arithmetic enables calculations using real values. The decimal…
Q: Flash drives should be inserted into this slot. How were the drives mapped in the operating system?
A: Operating system An operating system is a product that fills in as a mediator between end-client and…
Q: Please provide some concrete examples of how to rearrange cells in Excel.
A: Please provide some methods for rearranging the cells in Excel. In Excel, we may reorder cells by…
Q: How may the NIST CyberSecurity Framework be utilized to lessen cybercrime, and what are its three…
A: The following are the NIST Cyber Security Framework's primary elements: To write the NIST Cyber…
Q: 3 3 3 3 def change_maker (my_coins, my_money): output = [] i = 0 j = len(my_coins) while i < j: div…
A: Introduction Big O notation: Big O notation is a mathematical notation used to describe the upper…
Q: 2. Given three different sorting algorithms to solve a sorting problem and their runtimes are…
A: - We have to determine the sorting algorithm to be used based on the symbols and complexity…
Q: what are the key learnings of the article” Machine Learning-Based Analysis of Cryptocurrency Market…
A: Introduction One of the most well-known monetary institutions in existence at the time,…
Q: Can Arduino projects be written in Python? If that's the case, please explain your reasoning.
A: Python may be used to write programmes for Arduino: When it comes to open source hardware…
Can someone help me with 4d please
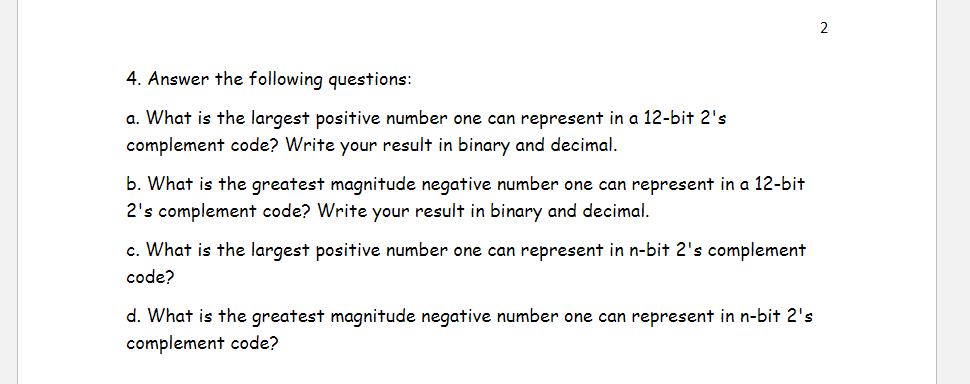
The solution is given below for the above-given question:
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- dont use others answers 3 a) Represent the decimal number -89 in binary using 8-bit: i.Signed magnitude: ____________________________ ii.One's complement: ____________________________ iii.Two's complement: ___________________________ b) What decimal value does the 8-bit binary number 10011110 have if: i.it is interpreted as an unsigned number? ___________________________ ii.it is on a computer using signed-magnitude representation? _______________________ iii.it is on a computer using one’s complement representation? _______________________ iv.it is on a computer using two’s complement representation? _______________________Kindly answer the following questions. j. The one thing that causes the most trouble with 2's complement numbers is the special case of the negative number which consists of a 1 followed by all 0's (1000 ... 000). If this number is n bits long, what number does it represent and why? (It is not negative zero.) a. Represent 187 in BCD code, excess-3 code, 6-3-1-1 code, and 2-out-of-5 code.Are you able to differentiate between the least significant bit and the most significant bit in a given set of data?
- Kindly answer the following questions. d. If the word length is n = 4 bits (including sign), what decimal number does 10002 represent in sign and magnitude? In 2's complement? In 1's complement? e. Given a negative number represented in 2's complement, how do you find its magnitude? Given a negative number represented in 1's complement, how do you find its magnitude?Assume that we have two different computers. One has a word length of 6 bits and the other has a word length of 15 bits. A) What is the range of numbers that can be stored in these computers assuming that the stored data is unsigned (without the sign bit)? B) What is the range of numbers that can be stored in these computers assuming 1’s complement is used to store data? C) What is the range of numbers that can be stored in these computers assuming 2’s complement is used to store data?1. Suppose (27.625 base 10) is represented using a 16-bit Floating Point Format where 1 bit is for the sign bit, 5 bits is for exponent and 10 bits is for mantissa. What is the exponent? Do not involve a space character when you type your answer. 2. Suppose (-27.625 base 10) is represented using a 16-bit Floating Point Format where 1 bit is for the sign bit, 5 bits is for exponent and 10 bits is for mantissa. What is the the result? Do not involve a space character when you type your answer.
- You need to show detail work on how you get the answer. Dont use answers from other websites please! Please type your answer not picture What decimal value does the 8-bit binary number 10011010 have if: a) it is on a computer using signed-magnitude representation? b) it is on a computer using two’s complement representation? c) it is on a computer using excess-M representation?9. Answer the following questions about IEEE 754 32-bit single precision numbers. a. Draw a diagram of the number format. b. What’s the range of numbers that can be represented? c. What’s meant by normalization? d. What’s the implied bit? e. What’s meant by exponent overflow and underflow? f. What’s meant by significand overflow and underflow? g. How’s + ∞ represented? h. How would he following numbers be represented? i. 1.6328125 x 2^-20 ii. 1.6328125 x 2^20 iii. -1.6328125 x 2^-20 iv. -1.6328125 x 2^201) Assume we have 16-bit (2 bytes) 2's complement system with a 2-bit fractional. Find a decimal representation of 2's complements number 1111 1111 1110 0111.11 (The quiz is expecting a numeric entry. It will automatically suppress leading and trailing zeros. It will display your answer with commas every third digit.) 2) Assume we have 8 bit (1 byte) 2's complement system with a 3-bit fractional. Find a decimal representation of 2's complements binary number 1010 0111.101 (The quiz is expecting a numeric entry. It will automatically suppress leading and trailing zeros. It will display your answer with commas every third digit.)
- You need to show detail work on how you get the answer. Dont use answers from other websites please! Please type your answer not picture 2. Represent the decimal number -66 in 8-bit binary number using the following representation methods: a) Two’s complement b) Signed-magnitude 3. What decimal value does the 8-bit binary number 10010110 have if: a) it is on a computer using signed-magnitude representation? b) it is on a computer using two’s complement representation? c) it is on a computer using excess-M representation?This question concerns the DES S-boxes. Please enter all answers in decimal. Consider the two 6-bit numbers x1=101101 and x2=000101. What is S1(x1)? (in decimal) What is S1(x2)? (in decimal) What is S1(x1⊕x2)? (in decimal) What is S1(x1)⊕S1(x2)? (in decimal) This shows that S1 is non-linear with respect to x1 and x2.1) For a sytem of 10-digit unsigned base 2 numbers, how many numbers can be represented? 2) For a (n-1) digit 2's complement binary number (n>2), what is the number of negative integers? 3) For a 10 digit 2's complement number, what is the difference between the most positive number and the most negative number?

