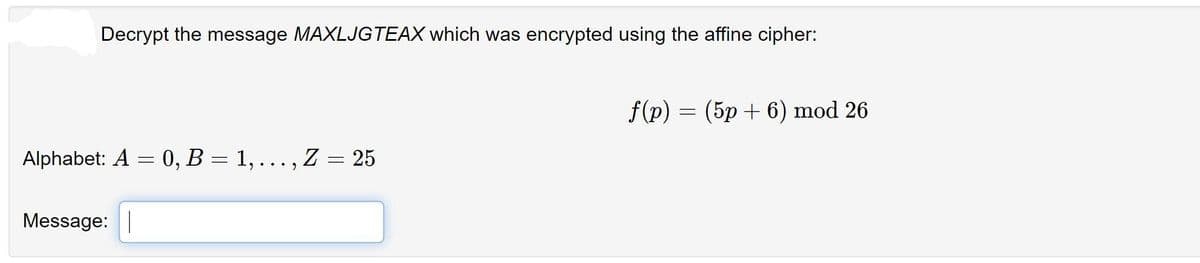
Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher:
Q: Your job is to decrypt the intercepted message CQNTNHRBDWMNACQNVJC, which is believed to reveal the…
A: letter=[chr(x) for x in range(65,91)] cipher="cqnthnrbdwnacqnvjc" cipher=cipher.upper() for key in…
Q: Assume that you intercept the following ciphertext and you know that it was encrypted using an…
A: Given data, Assume that you intercept the following ciphertext and you know that it was encrypted…
Q: Given is the following string of ciphertext which was encrypted with substitution cipher. asvphgyt…
A: Answer : WORLDCUP here cipher text is asvphgyt; the encryption rule is C=(M+k)Mod 26 here the 1st…
Q: Multiple choice The ciphertext of the message " ILOVEMYUNIVERSITYVERYMUCH" after encryption by…
A: Columnar Transposition involves writing the plaintext out in rows, and then reading the ciphertext…
Q: For efficiency reasons it is often useful to keep fixed parameter values for many users of a…
A: For efficiency reasons it is often useful to keep fixed parameter values for many users of a…
Q: Question 5: a. Using the key LARGES following the Playfair Cipher encrypts the message: NEED TO SEE…
A: a. Given that, Keyword = LARGES Plain text message= NEED TO SEE YOU IMPORTANT BEFORE SUNSET Play…
Q: Use the Vigenère cipher to DECRYPT the following ciphertext: “OGTJQPPB” knowing that the keyword…
A: The Answer is
Q: Which Cipher is used to resolve the issue with Mono alphabetic Cipher NOTE: Answer the above…
A: Monoalphabetic ciphers: Monoalphabetic cipher its is a substitution cipher and each plain alphabet…
Q: Q16: if the following message "paperx" is encrypted by using Hill cipher and converted into cipher…
A: The matrix used for encryption is the cipher key, and it should be chosen randomly from the set of…
Q: The ciphertext of the message " ILOVEMYUNIVERSITYVERYMUCH" after encryption by using Transposition…
A: Given: The ciphertext of the message " ILOVEMYUNIVERSITYVERYMUCH" after encryption by using…
Q: Dexter wants to set up his own public keys. He chooses p = 23 and q = 37 with e = 17. Answer the…
A: Given: Dexter wants to set up his own public keys. He chooses p = 23 and q = 37 with e = 17. Answer…
Q: I know how the Playfair cipher works. I would like to know how to find the keyword of the Playfair…
A:
Q: Question 1 Study the scenario and complete the question(s) that follow: Ceasar Cipher The Caesar…
A:
Q: Q3. Encrypt the Message "Spring Semester" by using polyalphabetic cipher of period 3 is being used,…
A: I can show you the procedure for making the table encrypt using a Key in Monoalphabetic Ciphers.…
Q: Ex/ if the following message “paperx” is encrypted by using Hill cipher and converted into…
A: The cipher key is the matrix used for encryption, and it should be selected at random from a…
Q: 1. Suppose that we use a substitution cipher to encrypt an English word, from which we obtain the…
A: Hey, since multiple questions posted, we will answer first question according to our policy. If you…
Q: The ciphertext of the message " ILOVEMYUNIVERSITYVERYMUCH" after encryption by using Transposition…
A: Given:
Q: Find the key
A: Plain Text : " SUCCESS IS NOT FINAL FAILURE IS NOT FATAL" Cipher Text:…
Q: By using playfair cipher find key if the length of key 7 and plaintext =wh yd on ty ou , and the…
A: Plaintext-= wh yd on ty ou
Q: Consider the following plaintext message. P = Follow the instructions What is the corresponding…
A: According to the information given:- We have to follow the instruction to perform the ciphertext…
Q: Q) Encrypt the message " MEET ME IN NET LAB " using Ceaser Cipher method and Key = 7. Verify the…
A: Caesar Cipher is a type of substitution cipher, in which each letter in the plain text is replaced…
Q: Which one of the following is a correct cipher for "too hard to be hard" if encrypted using Caesar…
A: Conversion of text "too hard to be hard" using Caesar cipher is in step2.
Q: uppose we are told that the plaintext breathtaking when ecrypted, the ciphertext becomes:…
A: The Answer is as follows.
Q: Which of the following statements is FALSE regarding cryptography? a. Asymmetric ciphers use the…
A: Answer: DES algorithm is an example of block cipher. Hence choice c. DES algorithm is an example of…
Q: w given two large primes, p and q, a cryptographic hash function H(x). a) DESCRIBE the RSA…
A: Q. RSA (Rivest–Shamir–Adleman) and AES (Advanced Encryption Standard) are two different types of…
Q: Assume that a Vigen'ere cipher is used to encrypt a lengthy string of text, and that the same string…
A: The vigenere cipher is an algorithm that is used to encrypting and decrypting the text. The vigenere…
Q: decrypt the following cipher: (CXDKOAXC) Using Playfair Cipher, Keyword = expressions %3D Select…
A: The answer is
Q: If "shifting by 4" is used in the Caesar cipher, the ciphertext of "FOUR" is O JSYV FRUH JMZI none…
A:
Q: Encrypt the message WATCH YOUR STEP by translating the letters into numbers, applying the given…
A: 1) We have message WATCH YOUR STEPS 2) We need to encrypt this message using formula f(p) =…
Q: Write the code to decrypt ( tfdvsjuz) A- using Caesar cipher when the key = 25? ? find the plaintext…
A: Ceasar cipher is one of the simplest encryption technique in which each character in plain text is…
Q: The ciphertext of the message " ILOVEMYUNIVERSITYVERYMUCH " after encryption by using Transposition…
A: Answer: VNSEC OURVU LYEYM IMVTYY Cipher text ILOVEMYUNIVERSITYVERY MUCH KEY: 54321 Filling the text…
Q: 1. Using the ABBA key, decrypt the word PKWDLDTB, if the Playfair cipher was used. Select ciphertext…
A: The Playfair cipher is a written code or symmetric encryption technique that was the first…
Q: The ciphertext of the message " SUNRISE" after encryption by using Simple Substitution cipher and…
A: Message - SUNRISE Key- SULTAN Using simple substitution cipher
Q: The following is a message encrypted using keyword cipher and you know the keyword is CYBERSECURITY…
A: Required: The following is a message encrypted using keyword cipher and you know the keyword is…
Q: 2. What is the correct decryption of "imontbgetagigoera" which is encrypted using rail fence cipher…
A: The rail fence cipher is a simple transposition cipher. It is also known as a zigzag cipher. The…
Q: The following ciphertext: ASNEFOELBCVYNAWEEEOONASRNUTIYIEIDMT was produced using a transposition…
A: total 35 characters are there, including spaces and special character so it will be 5x7
Q: A) Decrypt the following message with Transposition cipher to be understandable using the follo…
A: A) cipher text: jaalin eumtpt elpee pscaal yreiff 5 2 4 1 3 y e p j e r u s a l e m c a p…
Q: No plagarism please! Correct and detailed answer will be Upvoted else downvoted. Thank you!…
A: In this answer I will be discussing about polygram substitution ciphers.
Q: The ciphertext of the message " SUNDRY" after encryption by using Simple Substitution cipher and the…
A: Cryptography: In cryptography encryption is the concept in which information is encrypted into…
Q: Encrypt the Message “Spring Semester” by using polyalphabetic cipher of period 3 is being used,…
A: Encrypt the Message “Spring Semester” by using polyalphabetic cipher of period 3 is being used,…
Q: Q The cipher text C=10 sent to user whose public key is e=7, n=91. What is the plaintext M? Back…
A: RSA Algorithm: Step1: Choose 2 prime numbers p and q Step2: Calculate n=p×q Step3: Select a public…
Q: how to do this; Given an RSA public and private key of (note that not all of the private key is…
A: RSA (Rivest–Shamir–Adleman) algorithm is a public-key cryptography algorithm where public and…
Q: DECRYPT the following Cipher Text – ‘EBAPALMUQIEJKPBLYQ ’ with the Key ‘SHINAS’ using VIGENERE…
A: Required: DECRYPT the following Cipher Text – ‘EBAPALMUQIEJKPBLYQ ’ with the Key ‘SHINAS’ using…
Q: Encrypt the message WATCH YOUR STEP by translating the letters into numbers, applying the encryption…
A: First we have to assign a number to each letter: A=0; B=1; C=2 ;D=3; E=4; F=5; G=6; H=7;…
Q: Use the Vigenère cipher to DECRYPT the following ciphertext: "OGTJQPPB" knowing that the keyword…
A: The Answer is
Q: 3. Encrypt the following Plain text "What do you like the most" using Play Fair Cipher (Keyword is…
A: The Playfair Cipher Encryption Algorithm:The Algorithm consistes of 2 steps: Generate the key…
Q: Decrypt the message and show all your work
A: This is a very simple problem. Here are the steps to solve this transposition cipher. Keyword =…
Q: The following ciphertext was encrypted using a Vigen`ere cipher. 1 Guess the period of the key.…
A: Answer: I have given answered in the handwritten format in brief.
dont answer strict warning if you dont hae 100% sure else sure downvote and compliant
Step by step
Solved in 2 steps

- The affine cipher (transformation) C≡3P+24 (mod26) was used to encrypt a message. The resulting ciphertext is RTOLKTOIK. Decrypt this message. A=0,B=1,C=2,...,Y=24,Z=25Decrypt "FYDQAIRR" if it is known to have been encrypted with the affine cipher and c→M and k→C are knownThe affine cipher f(p) = (9p + 10) mod 26 is used to obtain the encrypted message F EMV Z,where p is the two digit representation (00-25) of each character in the original message. What is the original message?
- Perform the Encryption and then the Decryption for the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".Perform the Encryption using the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the messagewith the code 15 and 19
- Decrypt "RXJFKZYH" if it is known to have been encrypted with the affine cipher and c→J and k→N are knownThe following was encrypted using the Hill Cipher with a 2 x 2 matrix as the key. Determine both the decryption key as well as the message itself. AUGRRXULTRFUQGBNULYTAGPONPBVPBSUMOFFYVYGLYGT MCOICEESXFPBUHKCYUIDKRGJEOHDXNHQPBMYBEHYYUNLWhat is the formula used for encryption of data using affine cipher(a,b are constants and x is the numerical equivalent of a letter to be encrypted)? 1. ax+b 2. (ax+b)%26 3. a(x^2) +bx 4. (a(x^2) +bx)%26
- The ciphertext text “GEZXDS” was encrypted by a Hill cipher with a 2 × 2 matrix. The plaintext is “solved”. Find the encryption matrix M.Decrypt the following transposition cipher. YREEOESXUAOYAWMZ What is the plain text? How many columns and rows were there?Q17. Use the values below to decrypt the numerical ciphertext c = 133 , using the cryptoscheme: Encryption (m + k) mod N = c Decryption (c - k) mod N = m N = 50 k = 42

