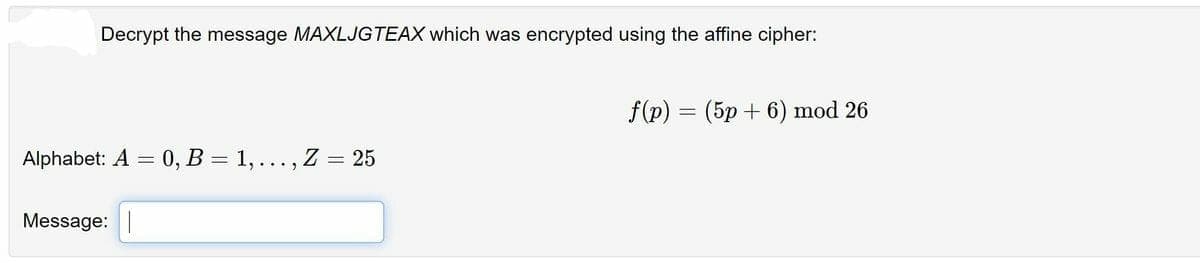
Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: f(p) (5p+6) mod 26 = Alphabet: A = 0, B = 1, ... , Z = 25 Message:
Q: 1. What is Failover-Clustering and why do you think it is so widely used?
A: To define Failover-Clustering.
Q: #include using namespace std; void main() { // Fill in the code to declare the printSum…
A:
Q: What are the advantages of using a compiled language over an interpreted language? In which…
A: Compilers translate compiled languages into machine code that can be executed by the processor. As a…
Q: 1. Insertion Sort 46 2. Selection Sort 46 Merge Sort 38 38 46 38 52 52 52 39 39 39 14 14 14
A: Insertion sort algorithm: Spilt a list in two parts - sorted and unsorted. Iterate from arr[1] to…
Q: Question 3 In a perfect binary tree if the height of the tree is 4, then the total number of nodes…
A: A binary tree is a special type of tree which contains at most two children nodes. Contrary to a…
Q: Learn to tell the difference between neural networks that employ recurrent and non-recurrent…
A: 1. The assignment is to write the distinction between the Neural network employing recurrent data…
Q: In order to attain a termination of recursion, list three different forms of recursion along with a…
A: Recursion is a process in which a function calls itself directly or indirectly. Different types of…
Q: o create a matrix that has mul ows, separate the rows with
A:
Q: The command eye (2) is result in: O [1 0;01] O [0 1; 10] O [11; 11] O [0 0; 1 1]
A: In matlab eye(2) Represents Identity matrix of 2x2 I.e., [1 0;0 1]
Q: Which of the following is a tuple in Python? O A(a,b,c) OB. [{a,b,c}] OC. [a,b,c] OD.{a,b,c}
A: The tuple is (a, b, c) (option A) Explanation:- In python, the tuple are declared with round bracket…
Q: What are some of the characteristics that set a computer apart from other electronic devices
A: Answer:
Q: The ADT Set stores elements in any order without duplications. It has the following two methods:…
A: Answer in step 2
Q: Which statement is false for Java? A private member of a class cannot be accessed from its derived…
A: In Java programming language, A public member of a class can be accessed in all packages. That means…
Q: So, what is artificial intelligence, exactly? Please include at least one example. a) What are the…
A: Artificial intelligence (AI) consists of the following components: Artificial intelligence (AI) is…
Q: This particular computer uses an instruction cache, a data cache, an operand fetch unit, and an…
A: The answer is
Q: The way risks are managed might be affected by the database management system that is being…
A: DBMS: A database management system is a collection of programs that manages the database structure…
Q: Which of the following statements displays a dialog box that prompts the user for the name of a…
A: The answer is strCity = InputBox (“Enter the city name”,,”City”) (option b) Explanation:- In visual…
Q: Write a loop to display the powers of 2 exactly as shown below: 1 2 4 8 16 32 64 128
A: Note*- In the above question, language is not mentioned .So i will solve your query in C++ language.…
Q: Write a loop to display the powers of 2 exactly as shown below: 1 2 4 8 16 32 64 128
A: As per answering guidelines since no language mentioned using c++ language.
Q: The density of an object is 2 g/cm3. To convert this to kg/m3, we need to divide it by 1000 to…
A: 1000g(100cm)3 = 1 kg1m3 Using the above formula to convert g/cm3 to kg/m3 we will first devide the…
Q: Is a microprocessor an output or an input device? Explain.
A: In this question, we have to discuss whether microprocessor is an output or an input device. Let's…
Q: What are the recommended procedures for assuring a local area network's resilience and availability?
A: What are the recommended procedures for assuring a local area network's resilience and availability?
Q: Why do Chrome OS machines demand less internal storage space than other desktop operating systems?
A: OS is the term for the software that serves as the interface between hardware and the user.OS…
Q: What exactly is meant by the term "cloud-based data storage," and what are some of the most…
A: Answer: Cloud storage is a cloud processing model that stores data on the Internet through a cloud…
Q: Write a program in python to get the lossing probability after taking the winning probability from…
A: User will enter the winning probability. As we know that the total probability is 1 which is equals…
Q: A(1,3) is an element of first column row and third row. От OF
A: Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: What exactly does it mean to say that something is a microprocessor?
A: Given: What exactly does it mean to say that something is a microprocessor?
Q: The function reshape(A,r,c) is used to: In matllab
A: In reshape function reshape(A,r,c) changes the A to new matrix of r rows and c columns.
Q: The following are the components of the methodology developed to provide efficient access to…
A: Microfilm definition: (Entry 1 of 2): a film containing a photographic record of the printed or…
Q: To create a matrix that h separate the rows with
A: Lets see the solution.
Q: Parallel Programming in Java Give one Example and discussion of parallel programming code using the…
A: With the advent of multicore CPUs in recent years, parallel programming is the way to take full…
Q: In terms of solving corporate data storage concerns, discuss the advantages and disadvantages of…
A: Attached storage: Attached storage is storage that is directly connected to a computer. It is not…
Q: How would you characterize the process of supervised learning in neural networks from a mathematical…
A: Neural networks refer to systems of neurons , either organic or artificial in nature.
Q: ✓ Details Create a class called Flower. Add one member variables color. Add only one getter function…
A: Your C++ program is given below as you required with an output.
Q: WHO ARE THE PEOPLE INVOLVED IN THE PHASES OF WATERFALL MODEL
A: There are a lot of people involved when a team is working on development of a product under he…
Q: If p is a Boolean variable, which of the following logical expression has the value false? a. p…
A: Only d is the answer. Logical and operation gives if any one of value false in this d option. P and…
Q: If z=[7 8 9 3 4], then length(z)= *
A: I have provided Answer with brief explanation---------------- For more understanding , I have…
Q: Interfaces are better than abstract classes in terms of benefits.
A: Answer: An abstract class permits you to make usefulness that subclasses can execute or supersede.…
Q: write this program with c++ in (opp) Write program for a Pharmaceutical store; where attributes…
A: Answer in step 2
Q: Write a JAVA program in which the user enters the initial velocity u, time of travel t, and the…
A: I give the code in Java along with output and code screenshot
Q: Consider probable flaws in the network's infrastructure. The proper security procedures should be…
A: Network vulnerabilities include: Malware, short for harmful software, includes Trojans, viruses, and…
Q: Why do we utilise MATLAB to solve difficulties in Computational Geometry?
A: Introduction: In business and academia, MATLAB is used by millions of engineers and scientists for…
Q: - The step function u (t) is integral of * with respect to time t. O Sinusoidal function O Ramp…
A: ANSWER:
Q: A 3 8 00 F 3 D 5 сл 3 3 G 1 E 3 B 3 C 5. -For the given graph, perform Dijkstra algorithm for…
A: In the given graph, it contains 7 vertices that are {A, B, C, D, E, F, G} and between these vertices…
Q: How to identify the need of mobile app? | • Give in example exact match Retrieval used | • Give an…
A: "As mention by you, we will do Question 3. If you need solution of other parts, please do post again…
Q: A*B is valid if A's number of column are not equals B's number of rows От O F
A: The horizontal and vertical lines of entries in a matrix are called rows and columns, respectively.…
Q: * The correct choice to draw the Arc between points (320,210) and (420,210) is 420,210 320,210…
A: Answer: we have to identified the correct option to draw the arc between the two point . so we will…
Q: * If A = [1 2 3; 4 5 6; 7 8 9;0 0 0], then size(A)= O 44 34 O 33 O 43 Other:
A: In the given question If A =[1 2 3; 4 5 6; 7 8 9;0 0 0], then size(A)=other
Q: Could you please explain why interrupts are so important in microprocessors?
A: let us see the answer:- Introduction:- An interrupt (sometimes known as a trap) is a request to the…
Q: Exp (3) Binary Addition Exercise 1- Explain how can you implement the half and full adder without…
A: According to answering policy We can answer only 1st question. For remaining question please…
Need correct answer with explanation must and should
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 3 images

- The affine cipher (transformation) C≡3P+24 (mod26) was used to encrypt a message. The resulting ciphertext is RTOLKTOIK. Decrypt this message. A=0,B=1,C=2,...,Y=24,Z=25Decrypt "FYDQAIRR" if it is known to have been encrypted with the affine cipher and c→M and k→C are knownPerform the Encryption and then the Decryption for the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".
- The ciphertext text “GEZXDS” was encrypted by a Hill cipher with a 2 × 2 matrix. The plaintext is “solved”. Find the encryption matrix M.Decrypt "RXJFKZYH" if it is known to have been encrypted with the affine cipher and c→J and k→N are knownFind the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the messagewith the code 15 and 19
- Perform the Encryption using the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".The affine cipher f(p) = (9p + 10) mod 26 is used to obtain the encrypted message F EMV Z,where p is the two digit representation (00-25) of each character in the original message. What is the original message?Decrypt the word RWLSR if it was encrypted using an alphabetic Caesar shift cipher that starts with shift 9 (mapping A to J), and shifts one additional space after each character is encrypted.
- Encrypt the plaintext “CAT” using the following RSA model if A uses P = 11 and Q = 19 whereas B uses P = 13 and Q = 17. Then Decrypt the cipher to get back the plaintext.Q17. Use the values below to decrypt the numerical ciphertext c = 133 , using the cryptoscheme: Encryption (m + k) mod N = c Decryption (c - k) mod N = m N = 50 k = 42The following cipher text was encrypted using a shift cipher AOPZTLZZHNLPZHMHRL Find the plain text and the key K

