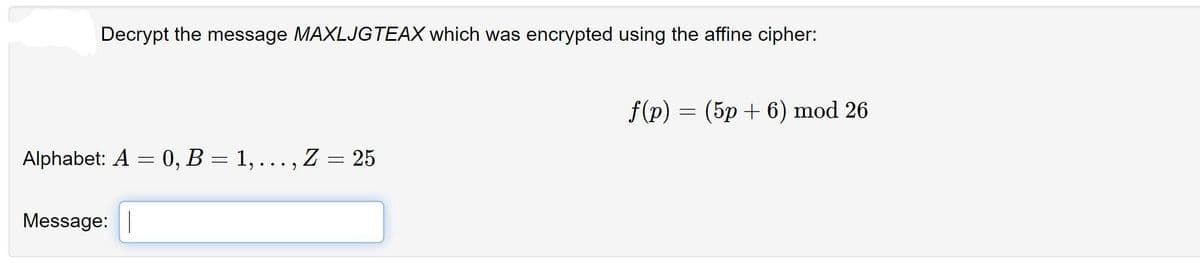
Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher:
Q: Cryptanalyze the single alphabetic substitution cipher and enter the substitution key in the format:…
A: Substitution cipher: In substitution cipher, each letter of the plaintext is replaced by other…
Q: Explain how a monoalphabetic substitution cipher works. Illustrate your explana- tion by using the…
A: In questions with many questions we must answer the first one.
Q: Your job is to decrypt the intercepted message CQNTNHRBDWMNACQNVJC, which is believed to reveal the…
A: letter=[chr(x) for x in range(65,91)] cipher="cqnthnrbdwnacqnvjc" cipher=cipher.upper() for key in…
Q: Decrypt the following plaintext "LNZM" using Atbash cipher. You have to generate the Atbash…
A: Atbash cipher is a substitution cipher with just one specific key where all the letters are reversed…
Q: What is the formula used for decoding the ciphered text using affine cipher(a,b are constants and x…
A: Question. What is the formula used for decoding the ciphered text using affine cipher(a,b are…
Q: Attacks on a cipher that use letter frequency can be made more difficult by assigning multiple codes…
A: Homophonic substitution cipher it is much more complicated varient of substitution cipher so…
Q: Decrypt this message DHAJOFVBYZALW encrypted using the shift cipher f(x)=(p+7) mod 26. o…
A: Decryption of Above text is done by Rotate back each character by 7 position .such that in rotating…
Q: Using the affine cipher, encrypt the string “TABLE” using the keys a = 3 and b = 2. Given the…
A: Plaintext = TABLE Value of x is taken based on alphabetical order, with A = 0, B = 1, C = 2 and so…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: f(p) (5p+6) mod 26 =…
A: The Answer is
Q: following ciphertext: 25292168 which was encrypted for a user with public key 27219809. n =
A: Key generation Generate two very large prime numbers, p and q, which satisfies the conditionp ≠ q →…
Q: Please Encrypt the following text by using Scytale cipher where the Key length is 6 Palintext: This…
A: Scytale Cipher is an encryption mechanism that was used as early as 400BC for secret communication…
Q: Decrypt the message TEA ONS EAS TCN AND TRH THE TEE if it was encrypted using a tabular…
A: The solution is given below for the above given question:
Q: Compare the given types of cryptanalytic attacks and identify the one which are the hardest for a…
A: In Known-plaintext attack, the plaintext of some part of the ciphertext is known by the attacker ,…
Q: The following cipher text was encrypted using a shift cipher AOPZTLZZHNLPZHMHRL Find the plain…
A:
Q: A Caesar cipher is a simple substitution cipher based on the idea of shifting each letter of the…
A: def caesar_cipher_encode(string, n): ans = '' for i in string: # traversing string if not…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: f(p : (5p+ 6) mod 26 %3D…
A: Affine decrypt MAXLJGTEAX (C ++ code )
Q: The affine cipher f(p) = (9p + 10) mod 26 is used to obtain the encrypted message F EMV Z, where p…
A: The answer to the above-mentioned question is given below with an explanation.
Q: Decrypt the affine cipher with ciphertext 'LBBKL BJMKB OLTQW TXIKT WKIBJ AABN'
A: Given ciphertext is: LBBKL BJMKB OLTQW TXIKT WKIBJ AABN Affine cipher is a type of monolithic…
Q: Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the message with the…
A: Required: Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the…
Q: Encrypt the plaintext “CAT” using the following RSA model if A uses P = 11 and Q = 19 whereas B uses…
A: RSA algorithm is public-key encryption or asymmetric cryptography algorithm. It uses two separate…
Q: Encrypt this plaintext with the Caesar/Rail Fence Cipher
A: the encrypted message:(5,12,3,7,9,6,4,14,1,13,10,8,15,2,11,16) explanation: Suppose your plaintext…
Q: Q2) Encrypt the following text "got" using one-time pad cipher with key=xyz
A: A one-time pad cypher is a Vignere cypher with the following characteristics: It's an impenetrable…
Q: Explain why attacks on a cipher are more difficult for a short message.
A: In cryptology, the discipline worried about the investigation of cryptographic calculations, a…
Q: Use the Caesar cipher to decrypt the message SRUTXH BR WH DPR PDV
A: The Message is SRUTXH BR WH DPR PDV The Cipher used for Encryption is Caesar Cipher. We need to…
Q: How is the Caesar Cipher more secure than the mono-alphabetic cypher?
A: Introduction: we will look at how a mono-alphabetic encryption is more secure than a Caesar cypher.
Q: Decrypt the cipher text using Transposition cipher and a key: 541362. Find the original message…
A:
Q: Using the modulo operator and key = 7, decrypt the cipher text "OHWWF ULD FLHY"
A: Your question is about Using the modulo operator and key = 7, decrypt the cipher text "OHWWF ULD…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: Alphabet: A = 0, B = 1,…
A: ENCRYPTION E(x) = (ax+b) mod m here, a = 5 and b = 6 [key of the cipher] m = 26 [size of…
Q: Use the modified Caesar cipher described in the assignment instructions to decrypt the following:…
A: Modified Caesar Cipher 1. Simple Substitution Technique 2. Key (K) range: 1-25 3. Working -…
Q: The ciphertext of the message " SUNRISE" after encryption by using Simple Substitution cipher and…
A: Message - SUNRISE Key- SULTAN Using simple substitution cipher
Q: Encrypt the following ciphertext "KLE" using Caesar cipher. O a. NHO O b. NOH O. OHN O d. HON
A: We know that we can encrypt any ciphertext by shifting it to 3 letters.
Q: The following ciphertext message was encrypted using the RSA algorithm and public key (2021,97).
A: Here, N = 16 Then possible φ(n) = 1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13, 14, 15 But the No. of…
Q: Cryptanalyze the single alphabetic substitution cipher and enter the substitution key in the format:…
A: In a Substitution cipher, any character of plain text from the given fixed set of characters is…
Q: Use the mixed alphabet cipher to encrypt the following message alphabet: ABCDEFGHIJKLMNOPQRSTUVWXYZ…
A: MIXED ALPHABET CIPHER: The mixed alphabet cipher is basically a cryptographic approach that is used…
Q: Decrypt the ciphertext.
A: ANSWER: Symmentic cipher: Cryptographic and Network Security:
Q: Encrypt SILLIMANLOVE using: a. Shift Cipher, key of 8 b. Affine Cipher, K(3,1)…
A: Shift cipher (Caesar Cipher ) , key Of 8 Affine cipher , k(3,1) Vigenere Cipher
Q: Use One Time Pad cipher with a key “peace be on the chosenP” to encrypt “Corona Virus on the Air “
A: Plain Text Given, Corona Virus on the Air Key to encrypt the plain text, peace be on the chosenP
Q: Decrypt the following transposition cipher. YREEOESXUAOYAWMZ What is the plain text? How many…
A: Given transposition cipher as:YREEOESXUAOYAWMZ
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: f(p) = (5p + 6) mod 26…
A: Answer: Given message is: MAXLJGTEAX Alphabet: A = 0, B=1,C =2, D = 3, E = 4, ........Z= 25. The…
Q: Decrypt "RJBZFTJDTNPJVXXWJR" cipher text which encrypted using One Time Pad cipher with a key "peace…
A: Given Decrypt "RJBZFTJDTNPJVXXWJR" cipher text which encrypted using One Time Pad cipher with a key…
Q: Decrypt the message CURRHYAKZVCA which was encrypted using the affine cipher:
A: Affine cipher is a combination of Additive cipher and Multiplicative cipher. Given formula, f(x) =…
Q: Decrypt the following plaintext "LNZM using Atbash cipher. You have to genereate the Atbash…
A: Answer: Our guide is answer first there question in details from first question. This is question…
Q: DECRYPT the following Cipher Text – ‘EBAPALMUQIEJKPBLYQ ’ with the Key ‘SHINAS’ using VIGENERE…
A: Required: DECRYPT the following Cipher Text – ‘EBAPALMUQIEJKPBLYQ ’ with the Key ‘SHINAS’ using…
Q: Playfair Cipher is a classical encryption technique, which encrypts plaintext according to four…
A: In cryptography encryption is the concept in which information is encrypted into secret codes so…
Q: What are the encryptio and decryption formula for Caesar Cipher?
A: Caesar Cipher is a cryptography technique also known as a shift cipher. This process uses the…
Q: Q3) Use Vigenere cipher with keyword "apples" to encrypt the message "Life is full of surprises"
A: The Vigenere cipher uses a 26×26 table with A to Z as the row heading and column heading This table…
Q: Using Columnar transposition encrypt the message “TODAY IS MIDTERM EXAM OF INTRODUCTION TO SECURITY…
A: First we need to write key in one row and in second row add alphabetic order number to the alphabets…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: f(p) = (5p+6) mod 26
A: The answer is
Q: The following ciphertext was encrypted using a Vigen`ere cipher. 1 Guess the period of the key.…
A: Answer: I have given answered in the handwritten format in brief.
dont dont post copied one strict warning
Step by step
Solved in 2 steps

- The affine cipher (transformation) C≡3P+24 (mod26) was used to encrypt a message. The resulting ciphertext is RTOLKTOIK. Decrypt this message. A=0,B=1,C=2,...,Y=24,Z=25Decrypt "FYDQAIRR" if it is known to have been encrypted with the affine cipher and c→M and k→C are knownThe affine cipher f(p) = (9p + 10) mod 26 is used to obtain the encrypted message F EMV Z,where p is the two digit representation (00-25) of each character in the original message. What is the original message?
- Perform the Encryption and then the Decryption for the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".Perform the Encryption using the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the messagewith the code 15 and 19
- Decrypt "RXJFKZYH" if it is known to have been encrypted with the affine cipher and c→J and k→N are knownThe following was encrypted using the Hill Cipher with a 2 x 2 matrix as the key. Determine both the decryption key as well as the message itself. AUGRRXULTRFUQGBNULYTAGPONPBVPBSUMOFFYVYGLYGT MCOICEESXFPBUHKCYUIDKRGJEOHDXNHQPBMYBEHYYUNLWhat is the formula used for encryption of data using affine cipher(a,b are constants and x is the numerical equivalent of a letter to be encrypted)? 1. ax+b 2. (ax+b)%26 3. a(x^2) +bx 4. (a(x^2) +bx)%26
- The ciphertext text “GEZXDS” was encrypted by a Hill cipher with a 2 × 2 matrix. The plaintext is “solved”. Find the encryption matrix M.Decrypt the following transposition cipher. YREEOESXUAOYAWMZ What is the plain text? How many columns and rows were there?Q17. Use the values below to decrypt the numerical ciphertext c = 133 , using the cryptoscheme: Encryption (m + k) mod N = c Decryption (c - k) mod N = m N = 50 k = 42

