DES 1. You are a junior IT executive at your department dealing with the DES encryption key. From the random key generator, you are given the secret key (E0E0E0E0F1F1F1F1)hex to encrypt a message. a)What is the output of the key after it is applied with the parity bit drop process box in Figure 1? At this point, is it a strong or weak key? Please state your reason. b)Using the key-permutation compression 2 from Figure 2, decide whether this is a strong or weak key. Justify your answer. DO NOT COPY AND PASTE!
DES 1. You are a junior IT executive at your department dealing with the DES encryption key. From the random key generator, you are given the secret key (E0E0E0E0F1F1F1F1)hex to encrypt a message. a)What is the output of the key after it is applied with the parity bit drop process box in Figure 1? At this point, is it a strong or weak key? Please state your reason. b)Using the key-permutation compression 2 from Figure 2, decide whether this is a strong or weak key. Justify your answer. DO NOT COPY AND PASTE!
Chapter6: System Integration And Performance
Section: Chapter Questions
Problem 20VE
Related questions
Question
DES
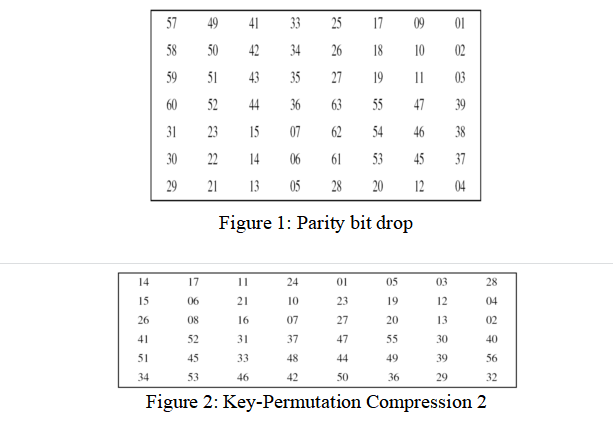
1. You are a junior IT executive at your department dealing with the DES encryption key. From the random key generator, you are given the secret key (E0E0E0E0F1F1F1F1)hex to encrypt a message.
a)What is the output of the key after it is applied with the parity bit drop process box in Figure 1? At this point, is it a strong or weak key? Please state your reason.
b)Using the key-permutation compression 2 from Figure 2, decide whether this is a strong or weak key. Justify your answer.
DO NOT COPY AND PASTE!
Transcribed Image Text:57
49
41
33
25
17
09
01
58
50
42
34
26
18
10
02
59
51
43
35
27
03
60
52
44
36
63
55
47
39
31
23
15
07
62
54
46
38
30
22
14
06
61
53
45
37
29
21
13
05
28
20
12
04
Figure 1: Parity bit drop
14
17
24
01
05
03
28
15
06
21
10
23
19
12
04
26
08
16
07
27
20
13
02
41
52
31
37
47
55
30
40
51
45
33
48
44
49
39
56
34
53
46
42
50
36
29
32
Figure 2: Key-Permutation Compression 2
19
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning


Enhanced Discovering Computers 2017 (Shelly Cashm…
Computer Science
ISBN:
9781305657458
Author:
Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning


Enhanced Discovering Computers 2017 (Shelly Cashm…
Computer Science
ISBN:
9781305657458
Author:
Misty E. Vermaat, Susan L. Sebok, Steven M. Freund, Mark Frydenberg, Jennifer T. Campbell
Publisher:
Cengage Learning