Describe the advantages and disadvantages of the College networks, with particular attention to cyber security
Describe the advantages and disadvantages of the College networks, with particular attention to cyber security
COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
1st Edition
ISBN:9780357392676
Author:FREUND, Steven
Publisher:FREUND, Steven
Chapter8: Working With Trendlines, Pivottables, Pivotcharts, And Slicers
Section: Chapter Questions
Problem 11EYW
Related questions
Question
100%
Describe the advantages and disadvantages of the College
networks, with particular attention to cyber security
Transcribed Image Text:Chrome File Edit View History Bookmarks Profiles Tab Window Help
Paraphrasing Tool | Quil X Sw Speedwrite - Fas
citethisforme.com
с
Ad
2 MILLION
STUDENTS
CAN'T BE
WRONG
Join Over 2M Students
BOOK
BY
6TH JUNE ¹22
Sandals
LEARN MORE
Севи
The Open University
III
YOUR BIBLIOGRAPHY
Add New Reference
Add Reference
Citation successfully created!
i Your bibliography will expire in
Your bibliogra
ANON
In-text: (n.d.)
Your Bibliography: n.d. [
<https://www.ncsc.gov.
ready/mobile-device-m
Copy bibliography citat
ANON
In-text: (2022)
Your Bibliography: Npcc→→
du
MAY 1
EXTR
24
000
000
8
Email - Tafa ×
Network Sec X
Assignment × smartphone x
Search resu X
ucbirmingham.instructure.com/courses/28986/files/1517334?module_item_id=510382
21-22_AHECOMF... › Files > Network Security ...
2021/22 - FE- Academic Year
Home
Announcements
Assignments
Discussions
Grades
People
Pages
Files
Syllabus
Quizzes
Modules
Collaborations
Chat
Office 365
Google Drive
Evasys Student
Surveys
Panopto Video
+
What are the X
t
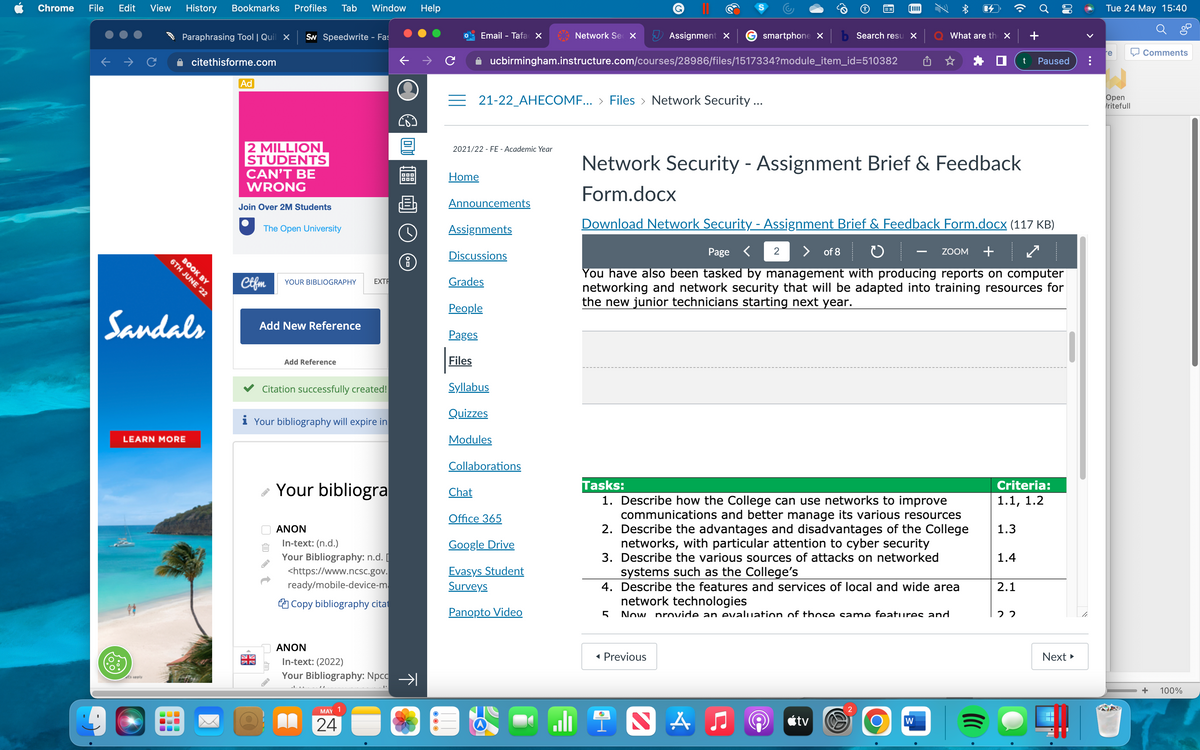
Network Security - Assignment Brief & Feedback
Form.docx
Download Network Security - Assignment Brief & Feedback Form.docx (117 KB)
Page < 2
of 8
ZOOM +
You have also been tasked by management with producing reports on computer
networking and network security that will be adapted into training resources for
the new junior technicians starting next year.
Tasks:
Criteria:
1.1, 1.2
1. Describe how the College can use networks to improve
communications and better manage its various resources
1.3
2. Describe the advantages and disadvantages of the College
networks, with particular attention to cyber security
1.4
3. Describe the various sources of attacks on networked
systems such as the College's
2.1
4. Describe the features and services of local and wide area
network technologies
5 Now provide an evaluation of those same features and
22
◄ Previous
2
INA ♫
tv
W
O
Paused
Next ►
Tue 24 May 15:40
re
Comments
Open
/ritefull
+
100%
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

New Perspectives on HTML5, CSS3, and JavaScript
Computer Science
ISBN:
9781305503922
Author:
Patrick M. Carey
Publisher:
Cengage Learning

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

New Perspectives on HTML5, CSS3, and JavaScript
Computer Science
ISBN:
9781305503922
Author:
Patrick M. Carey
Publisher:
Cengage Learning