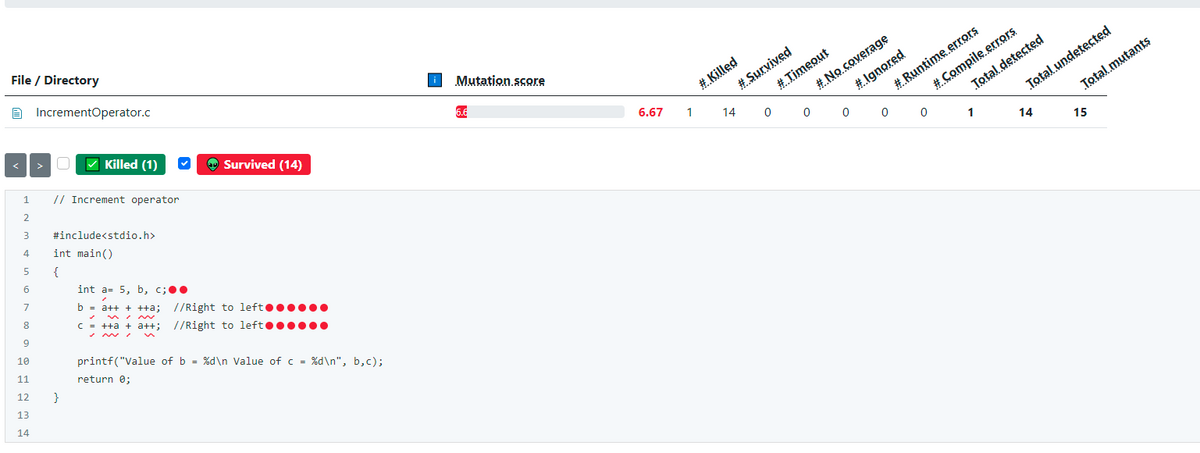
please Find equivalent mutant and paste the code segment here please
Q: How do the advantages of cloud computing stack up when compared to one another? Cloud computing…
A: Given: Almost twenty years have passed since cloud computing was first made accessible. In spite of…
Q: Mr. Armstrong Please create a C-programming code to check whether a number is an Armstrong number or…
A: Code: #include <stdio.h> void main(){ //declaring required fields int…
Q: The CPU is linked to a number of I/O devices, any of which might produce an interrupt at any moment.…
A: Introduction: Cypher block chaining is the technique used by DES (Data Encryption Standard). In…
Q: What are the advantages and disadvantages of storing data on the cloud? Please provide a list of…
A: Service companies and all other branded businesses on the path to progress are accountable for…
Q: What are some of the reasons that have led to the development of computer security into the…
A: The following elements have been essential contributors to the development of computer security into…
Q: Describe in detail the computing models of SaaS, PaaS, and IaaS Cloud. Consider three things when it…
A: Consider the following three essential cloud computing models: IaaS, PaaS, and SaaS. IaaS…
Q: I have a tiny network, and I was wondering what some typical troubleshooting methods and network…
A: Introduction: A network is defined as two or more computers are connected in the network for…
Q: 7. When running the depth first search, which of the following are possible for the ending time of…
A: Here about DFS:…
Q: What happens if you run an error-prone programme?
A: Introduction What does "error-prone programming" mean? Error-Prone is a Java static analysis tool…
Q: Find out how mobile devices and cloud computing are connected, and who the largest companies are in…
A: The answer is as follows: DEFINITION What Should You Do: Cloud computing is something I want to…
Q: List five disadvantages of GIF files.
A: According to the question, GIF is the very small size of images that makes the webpages attractive…
Q: What are we trying to accomplish with artificial intelligence in the end? Please provide a synopsis…
A: Artificial intelligence is everywhere in our lives today. Whether it’s our favorite Instagram…
Q: What procedure does the critical error handler follow when it encounters an error?
A: By default, .NET provides some templates i.e., NET application performance monitoring templates…
Q: Which strategies does the department use in order to ensure that users can always have access to the…
A: Introduction: In point of fact, there are certain solutions that may be used in switched and routed…
Q: What is Linux distribution life-cycle management and what does it do?
A: Other operating systems, such as Microsoft's Windows, combine all the code into one package. One of…
Q: How can I diagnose and solve issues with my network by utilizing the CLI troubleshooting commands…
A: Introduction: Timeouts, heavy buffering, poor internet call quality, and other difficulties are…
Q: Define a struct menuItemType with two components: menuItem of type string and menuPrice of type…
A: editable source code: #include <iostream> #include <string> using namespace std;…
Q: Implement the following methods, that accept an array of double and return the sum, average, and…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: What is the purpose of watchdog timers in many embedded systems?
A: Introduction: The significance of a watchdog timer in embedded systems:
Q: Explore the concept of hosted software as it relates to corporate software and analyze the key…
A: Introduction: Electronic connectivity is the most important factor in ensuring the success of the…
Q: hat role will Artificial Intelligence play in the future? Do you have any Artificial Intelligence…
A: In the future, what function will Artificial Intelligence play? Machines can learn from their…
Q: How will developments in artificial intelligence affect the path that the future will take? What…
A: Given: AI's future impact What software uses AI? AI scary?AI simulates human intellect on a…
Q: Develop a radix-3 DIT FFT algorithm to evaluate the 9-point DFT. Draw the flow graph of the radix-3…
A: Develop a radix-3 DIT FFT algorithm to evaluate the 9-point DFT. Draw the flow graph of the radix-3…
Q: The term "teacher" refers to curriculumists. How do you plan to make information and communications…
A: Bringing technology into their classrooms: The ability of teaching staff to frame learning in novel…
Q: Please explain what is meant by the phrases "critical infrastructure difficulty" and "attribution…
A: Inspection: Protecting public safety, which encompasses persons, the economy, and organizations, is…
Q: What additional types of organizations might profit from this innovation in terms of IT expense…
A: Other types of businesses could benefit from this invention by lowering their IT expenditures.…
Q: What role does the Model-View-Controller architecture (also known as MVC) play in the development of…
A: Definition: MVC stands for Model-View-Controller and is considered one of the most significant…
Q: Wireless networks are quicker than wired networks, but the combination of the two is the quickest.…
A: Intro Wireless networks: Wired connections transmit more data than Wi-Fi connections. When your PC…
Q: What are some of the reasons that have led to the development of computer security into the…
A: These elements have led to the transformation of computer security into modern information security.…
Q: Explain the concept of read uncommitted isolation level. Give an example of how it is used.
A: The lowest isolation level is Read Uncommitted. At this level, one transaction may read…
Q: List process-related responsibilities of a multi-user, time-sharing OS.
A: Introduction: Listing High-level process steps:
Q: Given k sorted lists and the total number of elements in all lists is n, please design an algorithm…
A:
Q: In Microsoft Access, how do you add reports? What about adding controls to a report?
A: Add reports in Microsoft access: Reports offer a way to view, format, and summarize the information…
Q: Technology based on information What results may be expected in the event that a bug is introduced…
A: Introduction: There are two sorts of mistakes that occur the bulk of the time.
Q: Which strategies does the department use in order to ensure that users can always have access to the…
A: Which strategies does the department use in order to ensure that users can always have access to the…
Q: How does the department guarantee that there is always access to the network while using switched…
A: A staggering amount of decisions based on table data must be taken in order to move even a single…
Q: What are some of the goals that the authentication process is trying to accomplish? Compare and…
A: The answer to the following question:-
Q: Exactly what are some of the goals of the authentication process? Analyze how various methods of…
A: Let us look at the solution. The act of identifying an individual process or entity trying to log in…
Q: Given the following matrices: 2 3 0\ 0 1 -1 A = -5 4 7 and B = 2 3 6 0 1 3 -8 1 1 Write a program in…
A: Start Accept matrix A elements Accept matrix B elements Assign matrix C with 2times of A matrix…
Q: Computer Science: Identify the OSPF autonomous system area (OSPF AS).
A: Given: The purpose of this inquiry is to provide light on the significance of the term "Area" in the…
Q: What is the overall goal of the data processing process step?
A:
Q: Write Java a program that will record the purchases made at a store. For each purchase, read from…
A: import java.io.FileWriter; import java.util.Scanner; public class Main{ public static void…
Q: Explore the concept of hosted software as it relates to corporate software and analyze the key…
A: Definition: Electronic connectivity is the most important factor in promoting team growth. Teams…
Q: c++, Print out all composite numbers from 2 to 50 using a loop. Within the loop, you must call a…
A: The asked C++ program is coded in the next step with explanatory comments.
Q: As a network security administrator, you should be aware of and take precautions against malicious…
A: Start: Because they hold sensitive data and trade secrets or earn money, servers, particularly web…
Q: What are the key differences between authenticating a distant user and authenticating a local user?…
A: What is the difference between remote and local user authentication? Which one was the most…
Q: How does the department guarantee that users have access to the network when using a system that is…
A: Beginning: A staggering amount of decisions based on table data must be taken in order to move even…
Q: How many item/key comparisons will the standard merge function (from merge sort) take to merge the…
A:
Q: How to make heart shape pattern with name in the middle
A: Explanation: // let's first including all the required libraries as #include <stdio.h>…
Q: In order to achieve improved application resilience, availability, and performance, how could the…
A: In this section, we have discussed a few key ways in which regions and availability zones contribute…
3
please Find equivalent mutant and paste the code segment here please
Step by step
Solved in 3 steps with 2 images

- This class prints the first several lines of a file. The default is to print 5 lines, but the -n flag can specify a different number. If no file is specified on the command line, read from standard input. The code bekoow is to help get started. #include <stdio.h> #include <stdlib.h> // You may assume that lines are no longer than 1024 bytes #define LINELEN 1024 static void usage (void); int main (int argc, char *argv[]) { return EXIT_SUCCESS; } static void usage (void) { printf ("head, prints the first few lines of a file\n"); printf ("usage: head [FLAG] FILE\n"); printf ("FLAG can be:\n"); printf (" -n N show the first N lines (default 5)\n"); printf ("If no FILE specified, read from STDIN\n"); }Write a void function that will merge the contents of two text files containing the chemical elements into a single binary file. The function's parameters will be three file pointers; each text file will contain an integer atomic number followed by the element name, chemical symbol and atomic weight. Here are two sample lines: 11 Sodium Na 22.9920 Calcium Ca 40.08 The function can assume that one file does not two copies of the same elements and that the binary output file should have the same property. IN C PLEASEThis file has syntax and/or logical errors. Determine the problem and fix the program. // Employee's salary should not be negative // Include stack trace when exception occurs using System; using static System.Console; class FDebugEleven03 { static void Main() { Employee emp = new Employee(); try { emp.IdNum = 234; emp.Salary = -12; } catch (NegativeSalaryException e) { WriteLine(e.Message); WriteLine(e.StackTrace); } } } public class NegativeSalaryException : { private static string msg = "Employee salary is negative."; public NegativeSalaryException() : base(msg) { } } public class Employee { private int idNum; private double salary; public int IdNum { get return idNum; set idNum = value; } public double Salary { get {…
- USING C++ PLEASE CREATE THREE FILES! IntCollection.h (or IntCollection.hpp): class definition IntCollection.cpp: class implementation main.cpp, including sample output and your answer to question 6 at the bottom. : main program to run the code The following code creates an IntCollection object named ‘c’. It adds seven integers to ‘c’, then uses a for loop to display the seven integers: int main() { IntCollection c; c.add(45); c.add(-210); c.add(77); c.add(2); c.add(-21); c.add(42); c.add(7); for (int i = 0; i < c.getSize(); i++) { cout << c.get(i) << endl; } } For this assignment you will add a copy constructor, a destructor, and three overloaded operators to the IntCollection class. In the design diagram below, the black member functions represent code that has already been implemented. You will be implementing the green items. Each item that you will be adding to the class is described below the diagram. private: int size // the number of ints currently stored in…JAVA PROGRAM ASAP Please CREATE A program ASAP BECAUSE IT IS LAB ASSIGNMENT #2 so it passes all the test cases. The program must pass the test case when uploaded to Hypergrade. Chapter 9. PC #16. Morse Code Translator (modified *** Read carefully ***) Morse code is a code where each letter of the English alphabet, each digit, and various punctuation characters are represented by a series of dots and dashes. Write a program that asks the user to enter a file name containing morse code, and then converts that code to text and prints it on the screen. The Morse code table is given in a text file morse.txt. When printing resulting text, display one sentence on each line. There should be no extra spaces at the beginning and at the end of the output. Mose.txt 0 -----1 .----2 ..---3 ...--4 ....-5 .....6 -....7 --...8 ---..9 ----., --..--. .-.-.-? ..--..A .-B -...C -.-.D -..E .F ..-.G --.H ....I ..J .---K -.-L…void writeEmpToFile(Employee *emp, FILE *f) { fwrite(&emp->salary, sizeof(emp->salary), 1, f); fwrite(&emp->yearBorn, sizeof(emp->yearBorn), 1, f); fwrite(emp->ssn, sizeof(char), SSN_SIZE, f); int len = strlen(emp->name) + 1; fwrite(&len, sizeof(int), 1, f); fwrite(emp->name, sizeof(char), len, f); } If you don't want to look at all the code then please help me get the other section done from this code that I will put right here directly in the post if you need context on what this code needs to work with you can click on the link below https://onlinegdb.com/nWSAIx8hCn
- void writeEmpToFile(Employee *emp, FILE *f) { fwrite(&emp->salary, sizeof(emp->salary), 1, f); fwrite(&emp->yearBorn, sizeof(emp->yearBorn), 1, f); fwrite(emp->ssn, sizeof(char), SSN_SIZE, f); int len = strlen(emp->name) + 1; fwrite(&len, sizeof(int), 1, f); fwrite(emp->name, sizeof(char), len, f); } Below is the work I have done so far that is required from the image but I have not been able to finish it and I need assistance with making the final changes that I have missed from the image that I have provided If you want to see the full code that this chunk of code is supposed to function with it is in the link below https://onlinegdb.com/nWSAIx8hCnpublic getFuelLevel():double retrieves fuel level in gallons Precondition: fuel level is initialized Postcondition: no change in state Return: fuel level in gallons with decimal valuespublic getFuelTankSize():double retrieves fuel level in gallons Precondition: fuel level is initialized Postcondition: no change is state Return: fuel level in gallons with decimal valuespublic setUpTrip(double, double): void Car's state is set to hold the speed of travel and distance to travel at that speed Precondition: none Postcondition: Car's state holds information on distance to travel and speed to travel Parameters: Average Speed to be driven, Distance to driveDevelop and use an algorithm that calculates the amount of fuel used and the actual distance driven in the drive() method. The algorithm must use a formula or multiple formulas ( as a piecewise function) that gives proportionately poorer mileage when the Car is driven faster or slower than its optimal speed. When a new Car object…In Java C++Write a code assessing a txt file consisting of id numbers. It should asses the given id numbers if its valid. An ID number can be considered valid given below. The following numbers are (imagine that the numbers are in a txt file)12034562120238471204562312067282120371891293042812047281129374911283920112013818It must be divisible by 11 given the formula below.The output will be the number of valid and invalid numbers. 11191031 = 1*8 + 1*7 + 1*6 + 9*5 + 1*4 + 0*3 + 3*2 + 1*1 = 77sum of the products must be divisible by 11 for it to be valid.
- Create a new C++ project in Visual Studio (or an IDE of your choice). Add the files listed below to your project: BinaryTree.h Download BinaryTree.h BinarySearchTree.h Download BinarySearchTree.h main.cpp Download main.cpp Build and run your project. The program should compile without any errors. Note that function main() creates a new BST of int and inserts the nodes 12, 38, 25, 5, 15, 8, 55 (in that order) and displays them using pre-order traversal. Verify that the insertions are done correctly. You may verify it manually or use the visualization tool at https://www.cs.usfca.edu/~galles/visualization/BST.html. (Links to an external site.) Do the following: 1. add code to test the deleteNode and search member functions. Save screenshot of your test program run. 2. add code to implement the nodeCount member function of class BinaryTree. Test it and save screenshot of your test program run. 3. add code to implement the leafCount member function of class BinaryTree. Test it and…PLEASE COMMENT CODE In a python program, create a new file and call it “ tracking”. Write to it four lines each contains information about an order like this: 1-00654-021 Dell charger Toronto-WEST 99-49-ZAD011-76540-022 ASUS battery Milton-EAST 34-56-CBH561-09239-026 HP HD Scarborough-NORTH 12-98-AZC451-12349-029 Mac FD North York-LAWRENCE 34-49-ZWL01Add the file two more lines: 1-34567-055 Lenovo SSD Milton-ON 34-09-MT04 1-90432-091 Lenovo battery Oakville-ON 78-KL98 Define a function that searches for a brand (e.g. Dell, ASUS, etc.). Test the function in your program.For this assignment, you will write a program that reads employee work data from a text file, and then calculates payroll information based on this file. The text file will contain one line of text for eachemployee. Each line consists of the following data (delimited by spaces or tabs):1) employee’s id2) employee’s hourly wage rate3) hours worked Monday4) hours worked Tuesday5) hours worked Wednesday6) hours worked Thursday7) hours worked Friday ex) txt file attached Your program should first prompt the user to get the location of the input file. Then it will read the data from the file, put it in appropriate arrays (as described below), and output to the screen the following information: (1) the employee ID, total number of hours worked, regular pay, overtime hours, overtime pay, and total paid to each employee (2) the total hours worked by all employees throughout the week; (3) the total amount paid out to all employees for the week; (4) the employee who received the highest pay for…









