Describe the below expression of the following regular expression R.E. = (ba*c (a*aa)* b*a*c*)*c
Q: In JAVA, how do you create a program that checks if a matrix is transitive or not
A: Code is given below public static boolean CheckTransitive(int array[][]) { boolean…
Q: Define the characteristics that are required for test-driven development. In the event that you…
A: INTRODUCTION: A software development approach called test-driven development keeps track of all…
Q: Considering System Sequence Diagram(SSD) given in the questiondevelop design sequence diagrams (DSD)…
A: All four sequence diagram are given below 1)makeNewSale 2) enterItem 3)endSale 4) makePayment
Q: Suppose three algorithms A, B, and C, can be implemented to perform a task. The algorithms have the…
A: Algorithms are judged upon their run time. Algorithms can be constant runtime, linear, logarithmic,…
Q: Write a java code to get the number of electrons passing through a heater wire in one minute, if it…
A: Program Plan: Initialize and declare the values of current and time. Initialize chargedParticles.…
Q: Project 2: You have to create a program in C language in which the user enters the mass M and length…
A: Coded using C language.
Q: 4. Create two column vectors x and y of 100 elements with random values between 10 and 10. To create…
A: We need to write a Python code for the given scenario.
Q: is it possible to pass object as an argument in a constructors
A: Yes, you can pass objects as arguments in a constructors Consider the following example: Here we…
Q: x86 Assembly Language Programming What will be the final value in EDX after this code executes? mov…
A: please check the step 2 for solution
Q: Write a complete C++ program that takes 10 integers from the user and stores them in an array b for…
A: Please consider the following program:
Q: Suppose Alice and Bob are sending packets to each other over a computer network. Suppose Trudy…
A: Given: There is a transfer of packets taking place between two clients present in a network, i.e.,…
Q: Create a function that takes two "sorted" arrays of numbers and returns an array of numbers which…
A: In this problem, we need to create a new method with that takes two "sorted" arrays of numbers and…
Q: Solve problem by using PYTHON Program to remove the ith occurrence of the given word in ist where…
A: It is defined as a simple, general purpose, high level, and object-oriented programming language. It…
Q: Write a loop to display the powers of 2 exactly as shown below: 1 12400 4 8 16 32 64 128
A: Code #include<iostream> #include<math.h> using namespace std; int main() { double…
Q: A. Write an Assembly program to load the register E with the value 12 and the register H with the…
A: The question is to write the assembly language code for the given problem.
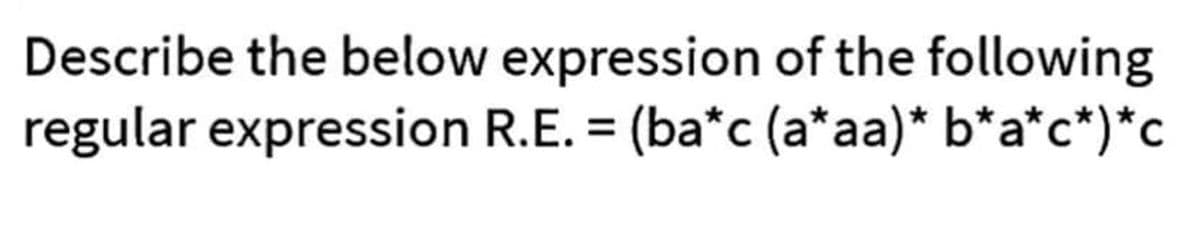
Q: describe
A:
Q: P20. Suppose you can access the caches in the local DNS servers of your department. Can you propose…
A:
Q: Describe the various VPN types, as well as the technology, protocols, and services that are utilized…
A: The term VPN refers to a virtual private network. Vpn stands for virtual private network, and it…
Q: Explain aurora DB in AWS.
A: The above question is solved in step 2 :-
Q: What is mean by digital envelope.Explain its working.
A: Digital Envelope :- A digital envelope is a secure electronic data container used to encrypt and…
Q: What does the presence of hashtags in an Excel column mean?
A: Introduction: There are few reasons are there for the presence of hashtag in Excel spreadsheet. We…
Q: How does a data breach effect cloud security? What are some possible countermeasures?
A: A data breach occurs when confidential, sensitive, or protected information is exposed to an…
Q: ould be the config of a computer (A support a 32-bit word computer sys
A:
Q: Given a letter, created a function which returns the nearest vowel to the letter. If two vowels are…
A: In this problem we need to design the JAVA Script program. Input - String Output - Boolean Logic…
Q: what use Linux may have in any element of rocket technology.
A: Linux is used extensively in rocket technology. It is used in the development and deployment of…
Q: Seker B 14 Use Gauss-Jordan elimination to solve the following linear system -3x+4y=-6 Sk-y-10 ⒸA.…
A: Here in this question we have given some linear equations and with using gauss jordan elimination…
Q: Please convert following figure into a relational schema. In each table, the primary key and foreign…
A: Here the BankBranch entity is a weak entity and therefore we need to include the primary key of Bank…
Q: Current Situation of Computing Department Knowledge Management System (KMS)
A: An knowledge management system (KMS) is a stage that assists you with getting the right information…
Q: The word protocol is often used to describe diplomatic relations. How does Wikipedia describe…
A:
Q: // For an input string of words, find the most frequently occuring word. In case of ties, report any…
A: According to the information given:- We have to follow the instruction in order to get desired…
Q: Assume you need to store book data in a structured manner. Either more books should be added, or…
A: The answer is given in the below step
Q: Write an SQL query to fetch the different projects available from the EmployeeSalary table.
A: Here we will use distinct clause in order to get the unique values of the product. Here we are…
Q: 14 Use Gauss-Jordan elimination to solve the following linear system: -3x+4y=-6 5x-y=10 OA (2.0)…
A: According to the information given:- We have to solve and find out the correct option.
Q: How can a client determine whether or not a server request will be fulfilled?
A: There are two scenarios when a server request will not be fulfilled. When the error arises from the…
Q: Apply your knowledge about arrays and functions and write a program, which takes a positive integer…
A: Algorithm: Read the value of n Run loop for i to n+1 and print the upper row element Run for loop…
Q: Q1 Multiple Choice Given a flow network G = (V, E) and any flow between s and t, let (A,B) be a…
A: The network graph visualization supports the undirected graph and directed graph structures. Network…
Q: Obtain the cipher text for the plain text "mosque" using playfair cipher. All steps should be…
A: We need to encrypt 'mosque' using playfair cipher.
Q: Runtime Original proportional to input size 1,000 logn nlogn n³ N 20 Original Runtime in ms 4 4…
A: I have answered below:
Q: Solve problem by using PYTHON Program to remove the ith occurrence of the given word in list where…
A: Introduction: In this question, we are asked to write a python code to remove word as given in the…
Q: Where does Windows store deleted files when you use File Explorer or Windows Explorer to remove them…
A: The answer to the question is given below with an explanation
Q: Using Divide and Conquer technique, sort the given number using quick soft 9,1,35264
A: ANswer is given below:
Q: Sequence diagram for uber eats
A: - We have to give the sequence diagram for uber eats.
Q: What is the Current IT infrastructure and systems in place of Computing Department Knowledge…
A: Answer - Knowledge Management System (KMS), basically stores and manage the data of an organization…
Q: Write an SQL query to fetch the count of employees working in project ‘P1’.
A: The query along with the output screenshot is given below
Q: The odd numbers are the numbers in the sequence 1,3,5,7,9,.... Define the sequence of S-numbers as…
A: Below is the answer to above question. I hope this will be helpful for you..
Q: Convert the decimal signed number -7 into 8-bit signed binary number. The signed binary number is…
A: Here in this question we have given a decimal number (-7) and we have asked to convert it into…
Q: Recall that TCP can be enhanced with SSL to provide process-to-process security services. including…
A:
Q: PYTHON!! Solve problem by using PYTHON Program to remove the ith occurrence of the given word in…
A: Python program steps to remove the ith occurrence of the given word list: To make it possible for…
Q: need help creating this program including the appropriate functions listed below Create a class…
A: // File Name: SavingsAccount.h #ifndef H_SAVINGSACCOUNT#define H_SAVINGSACCOUNT #include…
Q: Typically, a BUS consists of multiple communication paths or lines. Each line is capable of…
A: Introduction to Bus A bus is a subsystem that links computer parts and allows data to be…
I need the answer as soon as possible
Step by step
Solved in 2 steps

- Write a program to check the divisibility of two numbers. Use the concept of default argument here. If the number is not divisible, check whether the first number is a prime or not, using the previously defined divisibility check function.Rewrite the following statements using combined assignment operators: length = length / 2;Modify question 2 from Lab 2 such that if the value for Celsius is 100 or more, also display “Above or equalBoiling point of Water”Otherwise, display “BelowBoiling point of Water” python coding
- (Numerical) Write a program that tests the effectiveness of the rand() library function. Start by initializing 10 counters to 0, and then generate a large number of pseudorandom integers between 0 and 9. Each time a 0 occurs, increment the variable you have designated as the zero counter; when a 1 occurs, increment the counter variable that’s keeping count of the 1s that occur; and so on. Finally, display the number of 0s, 1s, 2s, and so on that occurred and the percentage of the time they occurred.(Practice) For the following correct algebraic expressions and corresponding incorrect C++ expressions, find the errors and write corrected C++ expressions: Algebra C++ Expression a.(2)(3)+(4)(5)(2)(3)+(4)(5) b. 6+1826+18/2 c. 4.512.23.1S4.5/12.23.1 d. 4.6(3.0+14.9)4.6(3.0+14.9) e. (12.1+18.9)(15.33.8)(12.1+18.9)(15.33.8)Identify the standard form of the following argument. p → q q → r ... p → r



